Author response:
The following is the authors’ response to the original reviews.
Public Reviews:
Reviewer #1 (Public review):
Summary:
This fundamental study identifies a new mechanism that involves a mycobacterial nucleomodulin manipulation of the host histone methyltransferase COMPASS complex to promote infection. Although other intracellular pathogens are known to manipulate histone methylation, this is the first report demonstrating the specific targeting of the COMPASS complex by a pathogen. The rigorous experimental design using state-of-the art bioinformatic analysis, protein modeling, molecular and cellular interaction, and functional approaches, culminating with in vivo infection modeling, provides convincing, unequivocal evidence that supports the authors' claims. This work will be of particular interest to cellular microbiologists working on microbial virulence mechanisms and effectors, specifically nucleomodulins, and cell/cancer biologists that examine COMPASS dysfunction in cancer biology.
Strengths:
(1) The strengths of this study include the rigorous and comprehensive experimental design that involved numerous state-of-the-art approaches to identify potential nucleomodulins, define molecular nucleomodulin-host interactions, cellular nucleomodulin localization, intracellular survival, and inflammatory gene transcriptional responses, and confirmation of the inflammatory and infection phenotype in a small animal model.
(2) The use of bioinformatic, cellular, and in vivo modeling that are consistent and support the overall conclusions is a strength of the study. In addition, the rigorous experimental design and data analysis, including the supplemental data provided, further strengthen the evidence supporting the conclusions.
Weaknesses:
(1) This work could be stronger if the MgdE-COMPASS subunit interactions that negatively impact COMPASS complex function were better defined. Since the COMPASS complex consists of many enzymes, examining the functional impact on each of the components would be interesting.
We thank the reviewer for this insightful comment. A biochemistry assays could be helpful to interpret the functional impact on each of the components by MgdE interaction. However, the purification of the COMPASS complex could be a hard task itself due to the complexity of the full COMPASS complex along with its dynamic structural properties and limited solubility.
(2) Examining the impact of WDR5 inhibitors on histone methylation, gene transcription, and mycobacterial infection could provide additional rigor and provide useful information related to the mechanisms and specific role of WDR5 inhibition on mycobacterial infection.
We thank the reviewer for the comment. A previous study showed that WIN-site inhibitors, such as compound C6, can displace WDR5 from chromatin, leading to a reduction in global H3K4me3 levels and suppression of immune-related gene expression (Hung et al., Nucleic Acids Res, 2018; Bryan et al., Nucleic Acids Res, 2020). These results closely mirror the functional effects we observed for MgdE, suggesting that MgdE may act as a functional mimic of WDR5 inhibition. This supports our proposed model in which MgdE disrupts COMPASS activity by targeting WDR5, thereby dampening host pro-inflammatory responses.
(3) The interaction between MgdE and COMPASS complex subunit ASH2L is relatively undefined, and studies to understand the relationship between WDR5 and ASH2L in COMPASS complex function during infection could provide interesting molecular details that are undefined in this study.
We thank the reviewer for the comment. In this study, we constructed single and multiple point mutants of MgdE at residues S<sup>80</sup>, D<sup>244</sup>, and H<sup>247</sup> to identify key amino acids involved in its interaction with ASH2L (Figure 5A and B; New Figure S4C). However, these mutations did not interrupt the interaction with MgdE, suggesting that more residues are involved in the interaction.
ASH2L and WDR5 function cooperatively within the WRAD module to stabilize the SET domain and promote H3K4 methyltransferase activity with physiological conditions (Couture and Skiniotis, Epigenetics, 2013; Qu et al., Cell, 2018; Rahman et al., Proc Natl Acad Sci U S A, 2022). ASH2L interacts with RbBP5 via its SPRY domain, whereas WDR5 bridges MLL1 and RbBP5 through the WIN and WBM motifs (Chen et al., Cell Res, 2012; Park et al., Nat Commun, 2019). The interaction status between ASH2L and WDR5 during mycobacterial infection could not be determined in our current study.
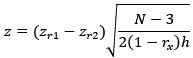
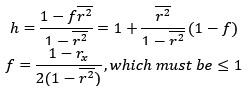
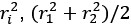
(4) The AlphaFold prediction results for all the nuclear proteins examined could be useful. Since the interaction predictions with COMPASS subunits range from 0.77 for WDR5 and 0.47 for ASH2L, it is not clear how the focus on COMPASS complex over other nuclear proteins was determined.
We thank the reviewer for the comment. We employed AlphaFold to predict the interactions between MgdE and the major nuclear proteins. This screen identified several subunits of the SET1/COMPASS complex as high-confidence candidates for interaction with MgdE (Figure S4A). This result is consistent with a proteomic study by Penn et al. which reported potential interactions between MgdE and components of the human SET1/COMPASS complex based on affinity purification-mass spectrometry analysis (Penn et al., Mol Cell, 2018).
Reviewer #2 (Public review):
Summary:
The manuscript by Chen et al addresses an important aspect of pathogenesis for mycobacterial pathogens, seeking to understand how bacterial effector proteins disrupt the host immune response. To address this question, the authors sought to identify bacterial effectors from M. tuberculosis (Mtb) that localize to the host nucleus and disrupt host gene expression as a means of impairing host immune function.
Strengths:
The researchers conducted a rigorous bioinformatic analysis to identify secreted effectors containing mammalian nuclear localization signal (NLS) sequences, which formed the basis of quantitative microscopy analysis to identify bacterial proteins that had nuclear targeting within human cells. The study used two complementary methods to detect protein-protein interaction: yeast two-hybrid assays and reciprocal immunoprecipitation (IP). The combined use of these techniques provides strong evidence of interactions between MgdE and SET1 components and suggests that the interactions are, in fact, direct. The authors also carried out a rigorous analysis of changes in gene expression in macrophages infected with the mgdE mutant BCG. They found strong and consistent effects on key cytokines such as IL6 and CSF1/2, suggesting that nuclear-localized MgdE does, in fact, alter gene expression during infection of macrophages.
Weaknesses:
There are some drawbacks in this study that limit the application of the findings to M. tuberculosis (Mtb) pathogenesis. The first concern is that much of the study relies on ectopic overexpression of proteins either in transfected non-immune cells (HEK293T) or in yeast, using 2-hybrid approaches. Some of their data in 293T cells is hard to interpret, and it is unclear if the protein-protein interactions they identify occur during natural infection with mycobacteria. The second major concern is that pathogenesis is studied using the BCG vaccine strain rather than virulent Mtb. However, overall, the key findings of the paper - that MgdE interacts with SET1 and alters gene expression are well-supported.
We thank the reviewer for the comment. We agree that the ectopic overexpression could not completely reflect a natural status, although these approaches were adopted in many similar experiments (Drerup et al., Molecular plant, 2013; Chen et al., Cell host & microbe, 2018; Ge et al., Autophagy, 2021). Further, the MgdE localization experiment using Mtb infected macrophages will be performed to increase the evidence in the natural infection.
We agree with the reviewer that BCG strain could not fully recapitulate the pathogenicity or immunological complexity of M. tuberculosis infection. We employed BCG as a biosafe surrogate model since it was acceptable in many related studies (Wang et al., Nat Immunol, 2025; Wang et al., Nat Commun, 2017; Péan et al., Nat Commun, 2017; Li et al., J Biol Chem, 2020).
Reviewer #3 (Public review):
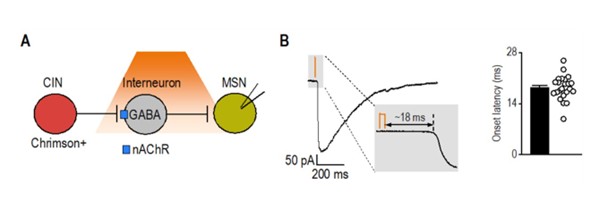
In this study, Chen L et al. systematically analyzed the mycobacterial nucleomodulins and identified MgdE as a key nucleomodulin in pathogenesis. They found that MgdE enters into host cell nucleus through two nuclear localization signals, KRIR<sup>108-111</sup> and RLRRPR<sup>300-305</sup>, and then interacts with COMPASS complex subunits ASH2L and WDR5 to suppress H3K4 methylation-mediated transcription of pro-inflammatory cytokines, thereby promoting mycobacterial survival. This study is potentially interesting, but there are several critical issues that need to be addressed to support the conclusions of the manuscript.
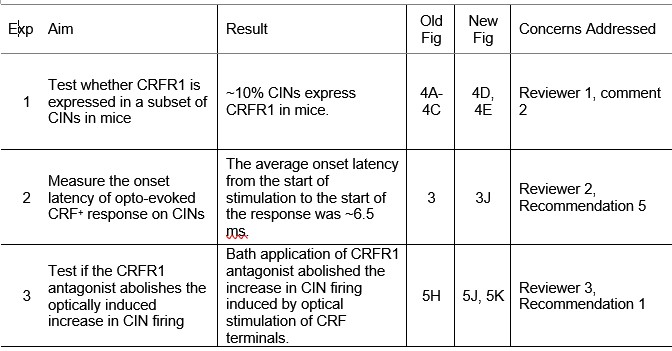
(1) Figure 2: The study identified MgdE as a nucleomodulin in mycobacteria and demonstrated its nuclear translocation via dual NLS motifs. The authors examined MgdE nuclear translocation through ectopic expression in HEK293T cells, which may not reflect physiological conditions. Nuclear-cytoplasmic fractionation experiments under mycobacterial infection should be performed to determine MgdE localization.
We thank the reviewer for this insightful comment. In the revised manuscript, we addressed this concern by performing nuclear-cytoplasmic fractionation experiments using M. bovis BCG-infected macrophages to assess the subcellular localization of MgdE (New Figure 2F) (Lines 146–155). Nuclear-cytoplasmic fractionation experiments showed that WT MgdE and the NLS single mutants (MgdE<sup>ΔNLS1</sup> and MgdE<sup>ΔNLS2</sup>) could be detected both in the cytoplasm and in the nucleus, while the double mutant MgdE<sup>ΔNLS1-2</sup> was detectable only in the cytoplasm. These findings strongly indicate that MgdE is capable of translocating into the host cell nucleus during BCG infection, and that this nuclear localization relies on the dual NLS motifs.
(2) Figure 2F: The authors detected MgdE-EGFP using an anti-GFP antibody, but EGFP as a control was not detected in its lane. The authors should address this technical issue.
We thank the reviewer for this question. In the revised manuscript, we have included the uncropped immunoblot images, which clearly show the EGFP band in the corresponding lane. These have been provided in the New Figure 2E.
(3) Figure 3C-3H: The data showing that the expression of all detected genes in 24 h is comparable to that in 4 h (but not 0 h) during WT BCG infection is beyond comprehension. The issue is also present in Figure 7C, Figure 7D, and Figure S7. Moreover, since Il6, Il1β (pro-inflammatory), and Il10 (anti-inflammatory) were all upregulated upon MgdE deletion, how do the authors explain the phenomenon that MgdE deletion simultaneously enhanced these gene expressions?
We thank the reviewer for the comment. A relative quantification method was used in our qPCR experiments to normalize the WT expression levels in Figure 3C–3H, Figure 7C, 7D, and New Figure S6.
The concurrent induction of both types of cytokines likely represents a dynamic host strategy to fine-tune immune responses during infection. This interpretation is supported by previous studies (Podleśny-Drabiniok et al., Cell Rep, 2025; Cicchese et al., Immunological Reviews, 2018).
(4) Figure 5: The authors confirmed the interactions between MgdE and WDR5/ASH2L. How does the interaction between MgdE and WDR5 inhibit COMPASS-dependent methyltransferase activity? Additionally, the precise MgdE-ASH2L binding interface and its functional impact on COMPASS assembly or activity require clarification.
We thank the reviewer for this insightful comment. We cautiously speculate that the MgdE interaction inhibits COMPASS-dependent methyltransferase activity by interfering with the integrity and stability of the COMPASS complex. Accordingly, we have incorporated the following discussion into the revised manuscript (Lines 303-315):
“The COMPASS complex facilitates H3K4 methylation through a conserved assembly mechanism involving multiple core subunits. WDR5, a central scaffolding component, interacts with RbBP5 and ASH2L to promote complex assembly and enzymatic activity (Qu et al., 2018; Wysocka et al., 2005). It also recognizes the WIN motif of methyltransferases such as MLL1, thereby anchoring them to the complex and stabilizing the ASH2L-RbBP5 dimer (Hsu et al., Cell, 2018). ASH2L further contributes to COMPASS activation by interacting with both RbBP5 and DPY30 and by stabilizing the SET domain, which is essential for efficient substrate recognition and catalysis (Qu et al., Cell, 2018; Park et al., Nat Commun, 2019). Our work shows that MgdE binds both WDR5 and ASH2L and inhibits the methyltransferase activity of the COMPASS complex. Site-directed mutagenesis revealed that residues D<sup>224</sup> and H<sup>247</sup> of MgdE are critical for WDR5 binding, as the double mutant MgdE-D<sup>224</sup>A/H<sup>247</sup>A fails to interact with WDR5 and shows diminished suppression of H3K4me3 levels (Figure 5D).”
Regarding the precise MgdE-ASH2L binding interface, we attempted to identify the key interaction site by introducing point mutations into ASH2L. However, these mutations did not disrupt the interaction (Figure 5A and B; New Figure S4C), suggesting that more residues are involved in the interaction.
(5) Figure 6: The authors proposed that the MgdE-regulated COMPASS complex-H3K4me3 axis suppresses pro-inflammatory responses, but the presented data do not sufficiently support this claim. H3K4me3 inhibitor should be employed to verify cytokine production during infection.
We thank the reviewer for the comment. We have now revised the description in lines 220-221 and lines 867-868 "MgdE suppresses host inflammatory responses probably by inhibition of COMPASS complex-mediated H3K4 methylation."
(6) There appears to be a discrepancy between the results shown in Figure S7 and its accompanying legend. The data related to inflammatory responses seem to be missing, and the data on bacterial colonization are confusing (bacterial DNA expression or CFU assay?).
We thank the reviewer for the comment. New Figure S6 specifically addresses the effect of MgdE on bacterial colonization in the spleens of infected mice, which was assessed by quantitative PCR rather than by CFU assay.
We have now revised the legend of New Figure S6 as below (Lines 986-991):
“MgdE facilitates bacterial colonization in the spleens of infected mice. Bacterial colonization was assessed in splenic homogenates from infected mice (as described in Figure 7A) by quantifying bacterial DNA using quantitative PCR at 2, 14, 21, 28, and 56 days post-infection.”
(7) Line 112-116: Please provide the original experimental data demonstrating nuclear localization of the 56 proteins harboring putative NLS motifs.
We thank the reviewer for the comment. We will provide this data in the New Table S3.
Recommendations for the authors:
Reviewer #2 (Recommendations for the authors):
There are a few concerns about specific experiments:
Major Comments:
(1) Questions about the exact constructs used in their microscopy studies and the behavior of their controls. GFP is used as a negative control, but in the data they provide, the GFP signal is actually nuclear-localized (for example, Figure 1c, Figure 2a). Later figures do show other constructs with clear cytoplasmic localization, such as the delta-NLS-MgdE-GFP in Figure 2D. This raises significant questions about how the microscopy images were analyzed and clouds the interpretation of these findings. It is also not clear if their microscopy studies use the mature MdgE, lacking the TAT signal peptide after signal peptidase cleavage (the form that would be delivered into the host cell) or if they are transfecting the pro-protein that still has the TAT signal peptide (a form that would present in the bacterial cell but that would not be found in the host cell). This should be clarified, and if their construct still has the TAT peptide, then key findings such as nuclear localization and NLS function should be confirmed with the mature protein lacking the signal peptide.
We thank the reviewer for this question. EGFP protein can passively diffuse through nuclear pores due to its smaller size (Petrovic et al., Science, 2022; Yaseen et al., Nat Commun, 2015; Bhat et al., Nucleic Acids Res, 2015). However, upon transfection with EGFP-tagged wild-type MdgE and its NLS deletion mutants (MdgE<sup>ΔNLS1</sup>, MdgE<sup>ΔNLS2</sup>, and MdgE<sup>ΔNLS1-2</sup>), we observed significantly stronger nuclear fluorescence in cells expressing wild-type MdgE compared to the EGFP protein. Notably, the MdgE<sup>ΔNLS1-2</sup>-EGFP mutant showed almost no detectable nuclear fluorescence (Figure 2C, D, and E). These results indicate that (i) MdgE-EGFP fusion protein could not enter the nucleus by passive diffusion, and (ii) EGFP does not interfere with the nuclear targeting ability of MdgE.
We did not construct a signal peptide-deleted MgdE for transfection assays. Instead, we performed an infection experiment using recombinant M. bovis BCG strains expressing Flag-tagged wild-type MgdE. The mature MgdE protein (signal peptide cleaved) can be detected in the nucleus fractionation (New Figure 2F), suggesting that the signal peptide does not play a role for the nuclear localization of MgdE.
(2) The localization of MdgE is not shown during actual infection. The study would be greatly strengthened by an analysis of the BCG strain expressing their MdgE-FLAG construct.
We thank the reviewer for the comment. In the revised manuscript, we constructed M. bovis BCG strains expressing FLAG-tagged wild-type MdgE as well as NLS deletion mutants (MdgE<sup>ΔNLS1</sup>, MdgE<sup>ΔNLS2</sup>, and MdgE<sup>ΔNLS1-2</sup>). These strains were used to infect THP-1 cells, and nuclear-cytoplasmic fractionation was performed 24 hours post-infection.
Nuclear-cytoplasmic fractionation experiments showed that WT MgdE and the NLS single mutants could be detected both in the cytoplasm and in the nucleus by immunoblotting, while the double mutant MgdE<sup>ΔNLS1-2</sup> was detectable only in the cytoplasm (New Figure 2F) (Lines 146–155). These findings indicate that MdgE is capable of entering the host cell nucleus during BCG infection, and that this nuclear localization depends on the presence of both its N-terminal and C-terminal NLS motifs.
(3) Their pathogenesis studies suggesting a role for MdgE would be greatly strengthened by studying MdgE in virulent Mtb rather than the BCG vaccine strain. If this is not possible because of technical limitations (such as lack of a BSL3 facility), then at least a thorough discussion of studies that examined Rv1075c/MdgE in Mtb is important. This would include a discussion of the phenotype observed in a previously published study examining the Mtb Rv1075c mutant that showed a minimal phenotype in mice (PMID: 31001637) and would also include a discussion of whether Rv1075c was identified in any of the several in vivo Tn-Seq studies done on Mtb.
We thank the reviewer for this insightful comment. In the revised manuscript, we have incorporated a more thorough discussion of prior studies that examined Rv1075c/MgdE in Mtb, including the reported minimal phenotype of an Mtb MgdE mutant in mice (PMID: 31001637) (Lines 288–294).
In the latest TnSeq studies in M. tuberculosis, Rv1075c/MgdE was not classified as essential for in vivo survival or virulence (James et al., NPJ Vaccines, 2025; Zhang et al., Cell, 2013). However, this absence should not be interpreted as evidence of dispensability since these datasets also failed to identify some well characterized virulence factors including Rv2067c (Singh et al., Nat Commun, 2023), PtpA (Qiang et al., Nat Commun, 2023), and PtpB (Chai et al., Science, 2022) which were demonstrated to be required for the virulence of Mtb.
Minor Comments:
(1) Multiple figures with axes with multiple discontinuities used when either using log-scale or multiple graphs is more appropriate, including 3B, 7A.
We sincerely thank the reviewer for pointing this out. In the revised manuscript, we have updated Figure 3B and Figure 7A.
(2) Figure 1C - Analysis of only nuclear MFI can be very misleading because it is affected by the total expression of each construct. Ratios of nuclear to cytoplasmic MFI are a more rigorous analysis.
We thank the reviewer for this comment. We agree that analyzing the ratio of nuclear to cytoplasmic mean fluorescence intensity (MFI) provides a more rigorous quantification of nuclear localization, particularly when comparing constructs with different expression levels. However, the analysis presented in Figure 1C was intended as a preliminary qualitative screen to identify Tat/SPI-associated proteins with potential nuclear localization, rather than a detailed quantitative assessment.
(3) Figure 5C - Controls missing and unclear interpretation of their mutant phenotype. There is no mock or empty-vector control transfection, and their immunoblot shows a massive increase in total cellular H3K4me3 signal in the bulk population, although their prior transfection data show only a small fraction of cells are expressing MdgE. They also see a massive increase in methylation in cells transfected with the inactive mutant, but the reason for this is unclear. Together, these data raise questions about the specificity of the increasing methylation they observe. An empty vector control should be included, and the phenotype of the mutant explained.
We thank the reviewer for this comment. In the revised manuscript, we transfected HEK293T cells with an empty EGFP vector and performed a quantitative analysis of H3K4me3 levels. The results demonstrated that, at the same time point, cells expressing MdgE showed significantly lower levels of H3K4me3 compared to both the EGFP control and the catalytically inactive mutant MdgE (D<sup>244</sup>A/H<sup>247</sup>A) (New Figure 5D) (Lines 213–216). These findings support the conclusion that MdgE specifically suppresses H3K4me3 levels in cells.
(4) Figure S1A - The secretion assay is lacking a critical control of immunoblotting a cytoplasmic bacterial protein to demonstrate that autolysis is not releasing proteins into the culture filtrate non-specifically - a common problem with secretion assays in mycobacteria.
We thank the reviewer for this comment. To address the concerns, we examined FLAG-tagged MgdE and the secreted antigen Ag85B in the culture supernatants by monitoring the cytoplasmic protein GlpX. The absence of GlpX in the supernatant confirmed that there was no autolysis in the experiment. We could detect MgdE-Flag in the culture supernatant (New Figure S2A), indicating that MgdE is a secreted protein.
(5) The volcano plot of their data shows that the proteins with the smallest p-values have the smallest fold-changes. This is unusual for a transcriptomic dataset and should be explained.
We thank the reviewer for this comment. We are not sure whether the p-value is correlated with fold-change in the transcriptomic dataset. This is probably case by case.
Reviewer #3 (Recommendations for the authors):
There are several minor comments:
(1) Line 104-109: The number of proteins harboring NLS motifs and candidate proteins assigned to the four distinct pathways does not match the data presented in Table S2. Please recheck the details. Figure 1A and B, as well as Figure S1A and B, should also be corrected accordingly.
We thank the reviewer for the comment. We have carefully checked the details and the numbers were confirmed and updated.
(2) Please add the scale bar in all image figures, including Figure 1C, Figure 2D, Figure 5C, Figure 7B, and Figure S2.
We thank the reviewer for this suggestion. We have now added scale bars to all relevant image figures in the revised manuscript, including Figure 1C, New Figure 2C, Figure 5C, Figure 7B, and New Figure S2B.
(3) Please add the molecular marker in all immunoblotting figures, including Figure 2C, Figure 2F, Figure 4B, Figure 4C, Figure 5B, Figure 5D, and Figure S5.
We thank the reviewer for this suggestion. We have now added the molecular marker in all immunoblotting figures in the revised manuscript, including New Figure 2E–F, Figure 4B–C, Figure 5B and D, Figure S2A, New Figure S2E and New Figure S4C.
References
Bryan AF, Wang J, Howard GC, Guarnaccia AD, Woodley CM, Aho ER, Rellinger EJ, Matlock BK, Flaherty DK, Lorey SL, Chung DH, Fesik SW, Liu Q, Weissmiller AM, Tansey WP (2020) WDR5 is a conserved regulator of protein synthesis gene expression Nucleic Acids Res 48:2924-2941.
Chai Q, Yu S, Zhong Y, Lu Z, Qiu C, Yu Y, Zhang X, Zhang Y, Lei Z, Qiang L, Li BX, Pang Y, Qiu XB, Wang J, Liu CH (2022) A bacterial phospholipid phosphatase inhibits host pyroptosis by hijacking ubiquitin Science 378(6616):eabq0132.
Chen C, Nguyen BN, Mitchell G, Margolis SR, Ma D, Portnoy DA (2018) The listeriolysin O PEST-like sequence co-opts AP-2-mediated endocytosis to prevent plasma membrane damage during Listeria infection Cell host & microbe 23: 786-795.
Chen Y, Cao F, Wan B, Dou Y, Lei M (2012) Structure of the SPRY domain of human Ash2L and its interactions with RbBP5 and DPY30 Cell Res 22:598–602.
Cicchese JM, Evans S, Hult C, Joslyn LR, Wessler T, Millar JA, Marino S, Cilfone NA, Mattila JT, Linderman JJ, Kirschner DE (2018) Dynamic balance of pro‐ and anti‐inflammatory signals controls disease and limits pathology Immunological Reviews 285: 147–167.
Couture JF, Skiniotis G (2013) Assembling a COMPASS Epigenetics 8:349-54
Drerup MM, Schlücking K, Hashimoto K, Manishankar P, Steinhorst L, Kuchitsu K, Kudla J (2013) The calcineurin B-like calcium sensors CBL1 and CBL9 together with their interacting protein kinase CIPK26 regulate the Arabidopsis NADPH oxidase RBOHF Molecular plant 6: 559-569.
Ge P, Lei Z, Yu Y, Lu Z, Qiang L, Chai Q, Zhang Y, Zhao D, Li B, Pang Y, Liu C, Wang J (2021) M. tuberculosis PknG Manipulates Host Autophagy Flux to Promote Pathogen Intracellular Survival Autophagy 18: 576–94.
Hung KH, Woo YH, Lin IY, Liu CH, Wang LC, Chen HY, Chiang BL, Lin KI (2018) The KDM4A/KDM4C/NF-κB and WDR5 epigenetic cascade regulates the activation of B cells Nucleic Acids Res 46:5547–5560.
James KS, Jain N, Witzl K, Cicchetti N, Fortune SM, Ioerger TR, Martinot AJ, Carey AF (2025) TnSeq identifies genetic requirements of Mycobacterium tuberculosis for survival under vaccine-induced immunity NPJ Vaccines 10:103.
Li X, Chen L, Liao J, Hui J, Li W, He ZG (2020) A novel stress-inducible CmtR-ESX3-Zn²⁺ regulatory pathway essential for survival of Mycobacterium bovis under oxidative stress J Biol Chem 295:17083–17099.
Park SH, Ayoub A, Lee YT, Xu J, Kim H, Zheng W, Zhang B, Sha L, An S, Zhang Y, Cianfrocco MA, Su M, Dou Y, Cho US (2019) Cryo-EM structure of the human MLL1 core complex bound to the nucleosome Nat Commun 10:5540.
Penn BH, Netter Z, Johnson JR, Von Dollen J, Jang GM, Johnson T, Ohol YM, Maher C, Bell SL, Geiger K (2018) An Mtb-human protein-protein interaction map identifies a switch between host antiviral and antibacterial responses Mol Cell 71:637-648.e5.
Petrovic S, Samanta D, Perriches T, Bley CJ, Thierbach K, Brown B, Nie S, Mobbs GW, Stevens TA, Liu X, Tomaleri GP, Schaus L, Hoelz A (2022) Architecture of the linker-scaffold in the nuclear pore Science 376: eabm9798.
Podleśny-Drabiniok A, Romero-Molina C, Patel T, See WY, Liu Y, Marcora E, Goate AM (2025) Cytokine-induced reprogramming of human macrophages toward Alzheimer's disease-relevant molecular and cellular phenotypes in vitro Cell Rep 44:115909.
Qiang L, Zhang Y, Lei Z, Lu Z, Tan S, Ge P, Chai Q, Zhao M, Zhang X, Li B, Pang Y, Zhang L, Liu CH, Wang J (2023) A mycobacterial effector promotes ferroptosis-dependent pathogenicity and dissemination Nat Commun 14:1430.
Qu Q, Takahashi YH, Yang Y, Hu H, Zhang Y, Brunzelle JS, Couture JF, Shilatifard A, Skiniotis G (2018) Structure and Conformational Dynamics of a COMPASS Histone H3K4 Methyltransferase Complex Cell 174:1117-1126.e12.
Rahman S, Hoffmann NA, Worden EJ, Smith ML, Namitz KEW, Knutson BA, Cosgrove MS, Wolberger C (2022) Multistate structures of the MLL1-WRAD complex bound to H2B-ubiquitinated nucleosome Proc Natl Acad Sci U S A 119:e2205691119.
Sharma G, Upadhyay S, Srilalitha M, Nandicoori VK, Khosla S 2015 The interaction of mycobacterial protein Rv2966c with host chromatin is mediated through non-CpG methylation and histone H3/H4 binding Nucleic Acids Res 43:3922-37.
Singh PR, Dadireddy V, Udupa S, Kalladi SM, Shee S, Khosla S, Rajmani RS, Singh A, Ramakumar S, Nagaraja V (2023) The Mycobacterium tuberculosis methyltransferase Rv2067c manipulates host epigenetic programming to promote its own survival Nat Commun 14:8497.
Wang J, Ge P, Qiang L, Tian F, Zhao D, Chai Q, Zhu M, Zhou R, Meng G, Iwakura Y, Gao GF, Liu CH (2017) The mycobacterial phosphatase PtpA regulates the expression of host genes and promotes cell proliferation Nat Commun 8:244.
Wang J, Li BX, Ge PP, Li J, Wang Q, Gao GF, Qiu XB, Liu CH (2015) Mycobacterium tuberculosis suppresses innate immunity by coopting the host ubiquitin system Nat Immunol 16:237–245
Wysocka J, Swigut T, Milne TA, Dou Y, Zhang X, Burlingame AL, Roeder RG, Brivanlou AH, Allis CD (2005) WDR5 associates with histone H3 methylated at K4 and is essential for H3 K4 methylation and vertebrate development Cell 121:859-72.
Yaseen I, Kaur P, Nandicoori VK, Khosla S (2015) Mycobacteria modulate host epigenetic machinery by Rv1988 methylation of a non-tail arginine of histone H3 Nat Commun 6:8922.
Zhang L, Kent JE, Whitaker M, Young DC, Herrmann D, Aleshin AE, Ko YH, Cingolani G, Saad JS, Moody DB, Marassi FM, Ehrt S, Niederweis M (2022) A periplasmic cinched protein is required for siderophore secretion and virulence of Mycobacterium tuberculosis Nat Commun 13:2255.
Zhang YJ, Reddy MC, Ioerger TR, Rothchild AC, Dartois V, Schuster BM, Trauner A, Wallis D, Galaviz S, Huttenhower C, Sacchettini JC, Behar SM, Rubin EJ (2013) Tryptophan biosynthesis protects mycobacteria from CD4 T-cell-mediated killing Cell 155:1296-308.