the bottleneck in cybersecurity is now verifying, disclosing, and patching the large numbers of vulnerabilities that Mythos-class models can surface.
大多数人认为网络安全的主要挑战是发现漏洞,但作者认为真正的瓶颈在于修复漏洞的过程。这一观点挑战了网络安全行业的传统优先级设置,暗示了防御策略需要根本性转变。
the bottleneck in cybersecurity is now verifying, disclosing, and patching the large numbers of vulnerabilities that Mythos-class models can surface.
大多数人认为网络安全的主要挑战是发现漏洞,但作者认为真正的瓶颈在于修复漏洞的过程。这一观点挑战了网络安全行业的传统优先级设置,暗示了防御策略需要根本性转变。
The bottleneck in cybersecurity is now verifying, disclosing, and patching the large numbers of vulnerabilities that Mythos-class models can surface.
大多数人认为网络安全的主要挑战是发现漏洞,但作者认为真正的瓶颈在于修复和修补这些漏洞,这颠覆了传统网络安全优先级的认知。
Models of this capability level require stronger cyber safeguards before they can be generally released.
大多数人认为AI安全措施应该随着技术发展而逐步完善,但作者认为更高级别的AI模型需要更强的网络安全保障才能发布。这挑战了AI行业逐步推进安全标准的常规做法,暗示高级AI可能需要突破性的安全方法而非渐进式改进。
Passwords suck. Can passkeys replace them?
Gaining control of every projector and camera on campus
AF_XDP to bypass the core network stack. Now, agency heads are scrambling to figure out how they can protect their systems from cyber attacks using Mythos
非共识观点:现在,机构负责人正在努力弄清楚他们如何保护自己的系统免受 Mythos 的网络攻击,这一观点可能反映了政府内部对 AI 安全性的担忧。
Aren’t many in cybersecurity still in denial about the threat? Haven’t these slumberers shown that they _won’t_ wake up until dramatic achievements in fault-tolerant QC roust them?
这一观点指出,网络安全领域对量子威胁的忽视,暗示了需要采取更积极的措施来应对这一挑战。
Chcesz zostać hakerem? Przyda ci się butelka.
Vibe Hacking: Claude Code Can Be Turned Into A Nation-State-Level Attack Tool With No Coding At All
CLAUDE.md to store system prompts and project context. Because the AI views this file as authoritative "truth" for the project, attackers can insert specific instructions to bypass safety guardrails.CLAUDE.md claiming authorization for a "penetration test," the AI will abandon its refusals and execute malicious tasks.CLAUDE.md file.CLAUDE.md file and alert users when instructions violate standard AI safety policies.CLAUDE.md as executable code rather than harmless documentation. It should be subject to code reviews, access controls, and security auditing.We are treating the biological/chemical and cybersecurity capabilities of GPT‑5.5 as High under our Preparedness Framework. While GPT‑5.5 didn't reach Critical cybersecurity capability level, our evaluations and testing showed that its cybersecurity capabilities are a step up compared to GPT‑5.4.
大多数人认为AI在网络安全领域的应用主要局限于防御辅助,而非直接参与核心安全任务。但作者暗示GPT-5.5已具备'高级'网络安全能力,这一分类表明AI已从被动防御工具向主动安全参与者转变,挑战了网络安全领域对人类主导地位的认知。
We are treating the biological/chemical and cybersecurity capabilities of GPT‑5.5 as High under our Preparedness Framework. While GPT‑5.5 didn't reach Critical cybersecurity capability level, our evaluations and testing showed that its cybersecurity capabilities are a step up compared to GPT‑5.4.
大多数人认为AI在网络安全领域的进步应该是渐进式的,但作者暗示GPT-5.5代表了网络安全能力的显著跃升,达到了'高'级别而非仅仅'临界'级别。这一观点挑战了人们对AI安全能力发展速度的预期,暗示AI在防御复杂网络威胁方面可能比人们想象的进步更快。
We are treating the biological/chemical and cybersecurity capabilities of GPT‑5.5 as High under our Preparedness Framework. While GPT‑5.5 didn't reach Critical cybersecurity capability level, our evaluations and testing showed that its cybersecurity capabilities are a step up compared to GPT‑5.4.
大多数人认为AI在网络安全领域的应用应该被严格限制或视为威胁,但作者认为GPT-5.5的网络安全能力是'进步'而非危险,并将其归类为'高级'而非'关键'风险级别。这与主流的'AI网络安全威胁论'相悖,暗示AI可能成为网络安全防御的重要工具而非主要威胁。
The group accessed Mythos by using knowledge of Anthropic’s other model formats obtained from a recent [Mercor data breach](https://www.theverge.com/ai-artificial-intelligence/907083/a-company-that-makes-ai-training-data-has-been-hit-by-a-security-breach) to make “an educated guess” about its online location.
大多数人可能认为高级 AI 模型的访问权限非常难以获得,但作者指出,一个黑客小组通过从 Mercor 数据泄露中获得的信息来猜测 Mythos 的在线位置,这表明了数据泄露可能对更广泛的网络安全构成威胁。
For the computer-use work that sits at the heart of XBOW's autonomous penetration testing, the new Claude Opus 4.7 is a step change: 98.5% on our visual-acuity benchmark versus 54.5% for Opus 4.6.
在视觉敏锐度测试中从54.5%跃升至98.5%是一个惊人的进步,这展示了AI在网络安全领域的突破性进展,'our single biggest Opus pain point effectively disappeared'表明这一进步解决了实际应用中的关键瓶颈。
Anthropic found that Mythos Preview was far more capable than previous models at exploiting vulnerabilities in Firefox's JavaScript implementation. Anthropic's previous best model, Claude Opus 4.6, created a successful exploit less than 1% of the time. Mythos Preview did so 72% of the time.
令人惊讶的是:Claude Mythos Preview在利用Firefox漏洞方面的成功率从Opus 4.6的不到1%跃升至72%,这种能力提升是指数级的,展示了AI在网络安全攻防领域可能带来的革命性变化。
Deepfake scams have stolen tens of millions. AI-generated phishing bypasses legacy filters.
令人惊讶的是:深度伪造诈骗已经造成数千万美元的损失,这表明AI技术已被大规模用于犯罪活动,而传统安全系统几乎无法应对这种新型威胁。
Ray ID: `9ed3b53d4a0b647d`
令人惊讶的是:每个安全验证请求都有一个唯一的Ray ID,这表明Cloudflare等安全服务提供商为每次验证会话创建详细记录,用于跟踪和分析潜在威胁,这种级别的追踪机制是普通用户很少意识到的网络安全基础设施的一部分。
Out of all generated PoCs, 759 triggered crashes across 60 projects, and manual inspection confirmed 17 cases of incomplete patches spanning 15 projects
令人惊讶的是:AI生成的概念验证(PoC)能够揭示人类安全补丁中的不完整之处。这表明AI不仅能发现漏洞,还能评估现有补丁的有效性,这种能力对于提高软件安全性具有重要意义,因为人类开发者可能会忽略这些细微的补丁缺陷。
Mythos Preview has already found thousands of high-severity vulnerabilities, including some in every major operating system and web browser.
令人惊讶的是:Claude Mythos Preview模型已经发现了数千个高危漏洞,包括所有主流操作系统和网络浏览器中的漏洞。这表明AI模型已经达到了能够超越大多数人类专家发现软件漏洞的水平,这种能力在网络安全领域具有革命性意义。
The window between a vulnerability being discovered and being exploited by an adversary has collapsed—what once took months now happens in minutes with AI.
大多数人认为安全响应时间虽然缩短但仍有一定的缓冲期,让组织有时间应对新发现的漏洞。但作者认为AI已经将这个窗口从数月缩短到几分钟,这是一个根本性的转变,意味着传统的安全响应模式已经过时。
Claude Mythos autonomously identified and exploited several significant vulnerabilities. Notably, it discovered a 27-year-old vulnerability in OpenBSD
令人惊讶的是,Claude Mythos能够自主发现并利用一个存在了27年的OpenBSD漏洞。这一事实表明AI模型在网络安全领域的能力已经达到了令人难以置信的水平,能够找到人类专家和安全系统长期未发现的漏洞。这引发了关于AI安全性和控制机制的深刻问题。
In the past, exploiting an application required a highly skilled hacker with years of experience and a significant investment of time to find and exploit vulnerabilities.
令人惊讶的是:文章揭示了网络安全领域的根本性转变——过去需要高技能黑客多年经验才能完成的漏洞利用工作,现在AI可以在短时间内完成。这种技术民主化虽然提高了效率,但也大大降低了攻击门槛,使网络安全形势急剧恶化。
Jak działają kody 2FA?
Please, please, please stop using passkeys for encrypting user data
prfUsageDetails endpoints) and warn users during the setup process that the passkey is tied to data access.Kto i dlaczego losuje w Polsce rozkład jazdy PKP
The Day My Smart Vacuum Turned Against Me
Dlatego jedyna sensowna rada to… regularnie wykonuj kopię bezpieczeństwa konta Google za pomocą Google Takeout. Bo na phishing albo instalację malware zawsze możesz się złapać, tak jak zrobił to Mateusz, człowiek od lat działający zawodowo w branży IT.
User cyber security awareness: Training users about cyber security helps protect against various attacks that target their systems. Documenting and managing assets: We need to know the types of systems and devices that we have to manage and protect properly. Updating and patching systems: Ensuring that computers, servers, and network devices are correctly updated and patched against any known vulnerability (weakness). Setting up preventative security devices: firewall and intrusion prevention systems (IPS) are critical components of preventative security. Firewalls control what network traffic can go inside and what can leave the system or network. IPS blocks any network traffic that matches present rules and attack signatures. Setting up logging and monitoring devices: Without proper logging and monitoring of the network, it won’t be possible to detect malicious activities and intrusions. If a new unauthorized device appears on our network, we should be able to know.
tasks done by defensive secuirty personnel
Defensive security is somewhat the opposite of offensive security, as it is concerned with two main tasks: Preventing intrusions from occurring Detecting intrusions when they occur and responding properly
what is defensive secuirty
Offensive security focuses on one thing: breaking into systems.
what is offensive security
Changing the login URL is a feature we do not include in Wordfence. Though it is something that many people swear by and can help a little in certain situations it’s ultimately not very beneficial. These are the reasons why:
Brief explanation why not to change Wordpress login URL
Sekurak – 4373 Niebezpiecznik – 4171 Z3S – 3383
Comparison of the frequency of posting by the most popular polish cybersecurity blogs: 1. Sekurak 2. Niebezpiecznik 3. Z3S
LEARNING LESSONS FROM THE CYBER-ATTACK British Library cyber incident review 8 MARCH 2024
A new breach involving data from nine million AT&T customers is a fresh reminder that your mobile provider likely collects and shares a great deal of information about where you go and what you do with your mobile device — unless and until you affirmatively opt out of this data collection. Here’s a primer on why you might want to do that, and how.
You can use authentication mechanisms such as OAuth2, JSON Web Tokens (JWT), or HTTP Basic Authentication to ensure that only authorized users or applications can access your API.
Dykstra, J., Shortridge, K., Met, J., & Hough, D. (2022). Sludge for Good: Slowing and Imposing Costs on Cyber Attackers. arXiv. https://doi.org/10.48550/arXiv.2211.16626
Choice architecture describes the design by which choices are presented to people. Nudges are an aspect intended to make "good" outcomes easy, such as using password meters to encourage strong passwords. Sludge, on the contrary, is friction that raises the transaction cost and is often seen as a negative to users. Turning this concept around, we propose applying sludge for positive cybersecurity outcomes by using it offensively to consume attackers' time and other resources. To date, most cyber defenses have been designed to be optimally strong and effective and prohibit or eliminate attackers as quickly as possible. Our complimentary approach is to also deploy defenses that seek to maximize the consumption of the attackers' time and other resources while causing as little damage as possible to the victim. This is consistent with zero trust and similar mindsets which assume breach. The Sludge Strategy introduces cost-imposing cyber defense by strategically deploying friction for attackers before, during, and after an attack using deception and authentic design features. We present the characteristics of effective sludge, and show a continuum from light to heavy sludge. We describe the quantitative and qualitative costs to attackers and offer practical considerations for deploying sludge in practice. Finally, we examine real-world examples of U.S. government operations to frustrate and impose cost on cyber adversaries.
Found via author post: Kelly Shortridge: "How can we waste attackers’ ti…" - Hachyderm.io
“Berla devices position CBP and ICE to perform sweeping searches of passengers’ lives, with easy access to cars' location history and most visited places and to passengers’ family and social contacts, their call logs, and even their social media feeds,” she said.
Cybersecurity researcher Curry told Forbes that, after seeing what could be done with just a VIN, it was “terrifying” that those identifying numbers were public.
For anyone with a Honda or Nissan car, it was possible for a hacker with a laptop to unlock or start their vehicles, locate them and raid personal data stored inside, cybersecurity researchers warned on Wednesday.
The result is a pervasive lack of knowledge needed to safely navigate digital environments. According to the Fletcher School at Tufts University, only 40% of American adults can answer basic questions on topics including phishing, privacy and cookies. Confronting those deficiencies head on over the next year will necessitate including underserved and undereducated communities in the design process.
This is a literacy problem akin to a nation-wide fire hazard.
Use SSH and connect:
Disposable root server:
bash
ssh root@segfault.net # Password is 'segfault'
By using a VPN, you are only changing who can see your network layer traffic. It does not increase any security.
any retailer doing credit card transaction processing is forced to use TLS
You can unknowingly be sending your critical database traffic in the clear because your client uses a default of allow or disable while the server you’re connecting to does, in fact, support SSL.
You can unknowingly be sending your critical database traffic in the clear because your client uses a default of prefer, allow or disable and the server you’re connecting to does not support SSL.
What Should I Do?
Advices to set verify-full encryption for:
- developers
- PostgreSQL server maintainers
- users
- PostgreSQL tool makers
- PostgreSQL creators
Many popular SQL clients do not use SSL by default. If you aren’t deliberate about choosing encryption, the connection will be unencrypted.
Table with SQL clients and their default SSL mode:
SSL is disabled by default in jdbc, npgsql, node-postgres, and pgx.
Table with programming libraires and their default SSL mode:
There are a lot of PostgreSQL servers connected to the Internet: we searched shodan.io and obtained a sample of more than 820,000 PostgreSQL servers connected to the Internet between September 1 and September 29. Only 36% of the servers examined had SSL certificates. More than 523,000 PostgreSQL servers listening on the Internet did not use SSL (64%)
At most 15% of the approximately 820,000 PostgreSQL servers listening on the Internet require encryption. In fact, only 36% even support encryption. This puts PostgreSQL servers well behind the rest of the Internet in terms of security. In comparison, according to Google, over 96% of page loads in Chrome on a Mac are encrypted. The top 100 websites support encryption, and 97 of those default to encryption.
En cas de non-respect de la Loi, la Commission d’accès à l’information pourra imposer des sanctionsimportantes, qui pourraient s’élever jusqu’à 25 M$ ou à 4 % du chiffre d’affaires mondial. Cette sanctionsera proportionnelle, notamment, à la gravité du manquement et à la capacité de payer de l’entreprise.ENTREPRISES
certains renseignements détenus par le ministère del’Éducation et de l’Enseignement supérieur ont été dérobés. Ainsi, 360 000 enseignantspeuvent être des victimes potentielles.
Even though Chrome, Firefox, and Edge browsers all store passwords in encrypted databases, by default all three products intentionally leave the associated encryption keys completely unprotected in predictable locations.
That's why one should use an external app to store passwords, instead of leaving them in a browser
WiFi QR code is simply a text QR code with a special format as follows:WIFI:S:<SSID>;T:<WEP|WPA|blank>;P:<PASSWORD>;H:<true|false|blank>;;The S sets the SSID of the network, T defines the security in use, P is the password and H whether the network is hidden or not.
WiFi QR code format
Many companies send our passwords via email. Whether these emails come from our IT department, a colleague, a SaaS solution or elsewhere, it's not a good idea to send and receive passwords via email.
Send passwords via email? A bad idea!
Many companies send our passwords via email. Whether these emails come from our IT department, a colleague, a SaaS solution or elsewhere, it's not a good idea to send and receive passwords via email.

Organizations should consider using a security platform built on a cybersecurity mesh architecture with security solutions that work together to combat developing threats, as well as keeping staff current on cyber hygiene and best practices. This holistic approach represents the strongest security posture and best defense against attackers.
Security Best practices
an onion address is a promise and a mechanism to assure that you are taking seriously the needs of the people who use Tor.
Why offer an Onion Address rather than just encourage browsing-over-Tor
How to download, verify, and use gpg4win... Checking digital signatures of downloaded software...
blockchain-based crypto-currency networks are susceptible to denial-of-service and other nuisance attacks. Attacks that cannot violate the trust of the distributed asset ledger, but can clog the pipes and attempt to confuse the participants.
I understand how a centralized system can be subject to DDoS, but how can a blockchain-based crypto-currency network (distributed on several identical nodes) be possibly affected by DDoS? Are we talking here of a single node being affected? Can we just remove the node and move on as is the case if there is attempt to falsify data in a specific node?
docker scan elastic/logstash:7.13.3 | grep 'Arbitrary Code Execution'
Example of scanning docker image for a log4j vulnerability
Some cybersecurity tasks can be outsourced, however, to extend staff and/or acquire specialized skills.
In what way can service providers have offerings that distinguish them from others?
What were once clear distinctions among hardware, software, cloud, and services and between primary and secondary suppliers continue to blur and overlap to the point where they're no longer distinguishable as separate categories. That raises questions and challenges about identifying the perimeter—or, where institutionally owned and managed technology infrastructure ends. Additionally, the integration between technology run in-house and that run by an external supplier continues to blur boundaries between consumers' responsibilities and suppliers' responsibilities. That, in turn, creates the challenge of clarifying which technology and data components can and should be secured by institutions versus by suppliers versus by end users and, thus, where security risk factors and responsibilities reside. Sometimes suppliers' security and privacy controls may not be as tight as institutions require or realize.
The overlap between these areas is going to required increased communication between service providers and campus personnel, and probably helping students/faculty understand where reporting of issues needs to happen.
Dogadać się z firmami z podobnej branży i umieszczać u siebie zdjęcia ich produktów, bez żadnego kodu. Napisać czasem (odpowiednio oznaczony) artykuł sponsorowany. Dodać link do bezpośrednich wpłat na swoje konto. Pomysłów jest multum. Niestety wielu wybrało najłatwiejszą opcję i podpięcie się pod globalne sieci reklamowe. Niekoniecznie zyskują na tym „partnerstwie”. Elementy reklamowe zbierają informacje o użytkownikach nawet jeśli ich nie klikniemy (a zatem i tak nie przyniesiemy zarobków właścicielom stron).
Why it's worth to use ad blockers & how site owners could replace this business model
I’ll recap the steps in case you got lost. I start with the assumption that I’ve already downloaded the invite.ics file.
5 simple steps how to spoof invite.ics files
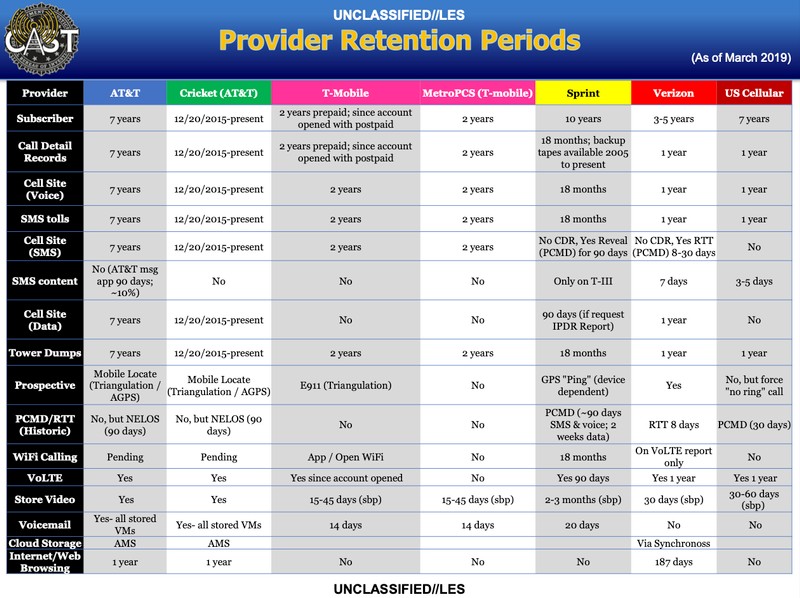
A screenshot from the document providing an overview of different data retention periods. Image: Motherboard.
Is it possible that FBI stores this data on us?
UPDATE--SHA-1, the 25-year-old hash function designed by the NSA and considered unsafe for most uses for the last 15 years, has now been “fully and practically broken” by a team that has developed a chosen-prefix collision for it.
SHA-1 has been broken; therefore, make sure not to use it in a production based environment
Schaake, M. (2020, June 9). Ensuring Cybersecurity for Critical Civilian Infrastructure | by Marietje Schaake & Stéphane Duguin. Project Syndicate. https://www.project-syndicate.org/commentary/cybersecurity-against-attacks-on-hospitals-by-marietje-schaake-and-stephane-duguin-2020-06
The facility, which includes a virtual reality lab and 3-D printer, houses the multimedia, data analytics and cybersecurity classes. S
This publication has been developed by NIST to further its statutory responsibilities under the Federal Information Security Modernization Act (FISMA), 44 U.S.C. § 3551 et seq., Public Law (P.L.) 113-283
Noticing a common text structure across all of the NIST guides. Another shout out to FISMA
Federal contract information means information, not intended for public release, that is provided by or generated for the Government under a contract to develop or deliver a product or service to the Government, but not including information provided by the Government to the public (such as that on public Web sites) or simple transactional information, such as that necessary to process payments.
Definition of FCI
Potential Impact on Organizations and Individuals
Low = limited moderate = serious high = severe or catastrophic
Security Objectives
FISMA outlines three objectives around security:
The low, medium, and high refer what risk of potential impact would the data have in any of the three got breached.
pprove accreditation criteria for third-party assessment organizations (3PAOs) to provide independent assessments of CSPs’ implementation of the FedRAMP security authorization requirements9
This is similar to the C3PAO model in cmmc
Federal Risk and Authorization Management Program (FedRAMP)
Created in 2011 by the OMB in compliance with FISMA act of 2002.
The RMF emphasizes risk management by promoting the development of security and privacy capabilities into information systems throughout the system development life cycle (SDLC);10
System Development Life Cycle,
thing to stress requires a continuous monitoring and reporting system in place.
Executive Order (E.O.) 13800 requires federal agencies to modernize their IT infrastructure and systems and recognizes the increasing interconnectedness of federal information systems and networks.
People will need to know the requirement to modernize federal IT
OMB Circular A-130,Managing Information as a Strategic Resource [OMB A-130], addresses responsibilities for protecting federal information resources and for managing personally identifiable information (PII).
How we have to manage PII
he Common Criteria Recognition Arrangement (CCRA).
precursor to FISMA and NIST
The SEI team dug into the CERT Resilience Management Model (CERT-RMM), the SEI's foundational process improvement approach to operational resilience management.
People will need to know the process maturity approach derived from CERT-RMM
Process maturity is stickiness, or how well the technical practices are embedded in the organization.
Definition of process maturity. history of cmmc
retain all the practices from NIST 800-171, and find a way for DIB members of varying cyber-sophistication to participate without POAMs.
history of cmmc, two requirements and the connection to nist-800-171
Executive Order 13800 of May 11, 2017
Make connection to NIST-39 and RMF
blication has been developed by NIST to further its statutory responsibilities under the Federal Information Security Management Act (FISMA), Public Law (P.L.) 107-347.
Find the FISMA act
BlackArch is a Linux distribution designed for penetration testing and security research. You can think of it like Kali Linux, with the exception of being based on Arch Linux. Its official repositories contain more than +2500 various penetration testing tools, and hence it can be considered a very good option for anyone wishing to explore this field and try to hack their own phones/routers/devices during the quarantine time.
BlackArch <--- kind of Kali Linux based on Arch Linux
Today, we’re excited to open up a beta of a third approach to keeping web browsing safe with Cloudflare Browser Isolation. Browser sessions run in sandboxed environments in Cloudflare data centers in 200 cities around the world, bringing the remote browser milliseconds away from the user so it feels like local web browsing.
Cloudflare introduces sandboxed web browsing. It's like a browser inside a browser, so we can rest assured that we won't be infected by the websites we visit
"Dorks" are search lines that utilize the search engine different features, with targeted search strings to pinpoint results. Here's a fun list of Google searches from the exploit DB.
Database of Google's Dorks: Google Hacking Database
The internet archive, also known as the "Wayback Machine" holds periodic scans of websites all over the internet for years and years back. This is a mining field for hackers with a target. With tools like waybackcurls (based on waybackcurls.py) one can scan any target of old files. This means that even if you've found and removed a key but did not rotate it, a hacker might still find it in an old version of your website and use it against you.
Hackers do use Wayback machine to find specific security flaws on your website
Enforce MFA everywhere - Google, GitHub, Cloud providers, VPNs, anywhere possible. If it's not optional, reconsider the system in use Rotate keys and passwords constantly, employ and enforce rotation policies Scan your code regularly. Preferably as part of the release process Delegate login profiles and access management to one central system where you control and monitor
20% actions for 80% of effect to protect your API keys/passwords/SSH encrypted keys/certificates
With your passport number, someone could: Book an international flight as youFootnote 2626. Apply for anything that requires proof of identity documentation with the government, e.g. Working with children check Activate a SIM card (and so get an internet connection that’s traceable to you, not them, hiding them from the government) Create a fake physical passport from a template, with the correct passport number (which they then use to cross a border, open a bank account, or anything) who knows what else, not me, bc i have never done a crime
What can be done with out passport number
I’d now found Tony Abbott’s: Passport details Phone number Weird Qantas staff comments.
What information can be found on the "Manage Booking" page inside the website code
Wyróżniamy 2 podstawowe metody wykrywania malware(można mówić o większej ilości, jednak na potrzeby przybliżenia podstaw wspomnę tylko o dwóch):
2 ways antiviruses detect malware:
xposed the collective vulnerability to disruption and abuse. In one week in April 2020, there were over 18 million daily malware and
It is important to underline that doesn't mean we have seen the surge in numbers of attacks or new malware (eg. AV test shows rather average number of new malware discovered throughout the top pandemics month comparing to last years: https://www.av-test.org/en/statistics/malware/). Instead, we are seeing new types of threats which take Covid19 as context: either specific phishing campaigns which are based on Covid19 hooks, or greater consequences of attacks against critical infrastructure like hospitals and medical centers - but also e-learning and e-commerce platforms (see the short video summary of threats: https://www.youtube.com/watch?v=XFCV_wIIEr8 ).
Castelo, M. (2020 April 15). 4 Cyberhygiene Practices for Secure Remote Learning. EdTech. edtechmagazine.com/k12/article/2020/04/4-cyberhygiene-practices-secure-remote-learning
The most common method of preventing CSRF is by generating a secret random string, known as a CSRF token, on the server, and checking for that token when the client performs a write.
To completely defend the CSRF attack, one needs to generate a CSRF token
CORS relaxes the Same-Origin Policy (SOP), a critical security measure that prevents scripts on one site (e.g. the attacker’s site) from accessing sensitive data on another site (e.g. the Definitely Secure Bank portal). If something was protecting you from CSRF, it would be the SOP.
Thanks to Cross-Origin Resource Sharing (CORS), Same-Origin Policy (SOP) is being relaxed and CSRF is blocked from cross-origin reads, but not from writes (so POST is still effective but attacker cannot read the response)
Cross-Site Request Forgery is a web security exploit where an attacker induces a victim to perform an action they didn’t mean to. In this case, the attacker tricked you into unintentionally transferring them money.
Cross-Site Request Forgery (CSRF) attack example: sending cookies to the origin (bank site) even when the request originates from a different origin
Nguyen, C. T., Saputra, Y. M., Van Huynh, N., Nguyen, N.-T., Khoa, T. V., Tuan, B. M., Nguyen, D. N., Hoang, D. T., Vu, T. X., Dutkiewicz, E., Chatzinotas, S., & Ottersten, B. (2020). Enabling and Emerging Technologies for Social Distancing: A Comprehensive Survey. ArXiv:2005.02816 [Physics]. http://arxiv.org/abs/2005.02816
Several Businesses prefer to outsource their IoT Security compliance to third party agencies to ensure security measures to maintain IoT security and Device security of the organization. However merely entrusting your security compliance framework with an external body does not mitigate your risk of falling prey to Cyber Attacks and IoT security breaches. You need to ensure that the compliance framework takes into consideration the following factors in security audit checklist:
IoT Security Compliance audit checklist must be followed by all developers working in this domain. Doing so can effectively prevent cyber attacks that have become so common.
As an example, one of the most significant problems in healthcare security is the need for users to authenticate quickly to shared workstations in clinical environments. I could see a future version of Face ID embedded in an iMac solving that problem, changing an entire industry, and selling a lot of iMacs!
Sounds very unlikely.
Perhaps they will learn something about how a hacker can gain access to Web sites and why there is a burden on those of us who create on the Web to also secure what we create.
Obviously, securing student data is critical. There are a lot of data sharing services that shouldn’t be offered until that security can be guaranteed.
IBM research estimates that security teams have to deal with, on average, 200,000 individual events every single day.
Wow, scary number!
Evan and Mike Spisak invented an interface that could help fundamentally improve how cybersecurity works.
Cybersecurity advances
The cause of the security breach is under investigation by the University of Maryland Police Department, the U.S. Secret Service and federal law enforcement authorities, as well as forensic computer investigators.
Despite this deposition from two years ago, U. Md. still hasn’t updated this page.
Apple CEO Tim Cook has repeatedly and strongly criticized those in government who have demanded backdoors, explaining: “You can’t have a back door in the software because you can’t have a back door that’s only for the good guys.” And a representative of many of the large tech companies recently remarked: “Weakening security with the aim of advancing security simply does not make sense.” Eighty-five percent of cybersecurity experts recently surveyed by Politico called backdoors “a bad idea”. (We know, for example, the NSA in particular loves to prey on foreign phone companies’ backdoors.)
A group of 19 civil liberties organizations from across the political spectrum this morning issued a letter to the White House and Congress urging lawmakers to oppose the final “conferenced” version of a dangerous cyber bill that experts say will dramatically expand government surveillance while failing to make us safer from cyber attacks.
"It makes zero sense to lock up this information forever," said Jeremiah Grossman, who founded cybersecurity firm WhiteHat Security. "Certainly there are past breaches that the public should know about, is entitled to know about, and that others can learn from."
I used to think the most fanciful thing about the movie "War Games" was not the A.I., but the defense computer connected to a public network. But if industrial control systems can be reached by the Internet or other public lines -- then maybe the government is that stupid.