faster than most top ML-based codecs run on a V100 GPU
这一比较数据点很有价值,表明PICO在移动设备上的性能超过了在高端V100 GPU上运行的其他顶级ML编码器。这突显了PICO的工程优化水平,但需要确认测试条件是否完全对等,以确保比较的公平性。
faster than most top ML-based codecs run on a V100 GPU
这一比较数据点很有价值,表明PICO在移动设备上的性能超过了在高端V100 GPU上运行的其他顶级ML编码器。这突显了PICO的工程优化水平,但需要确认测试条件是否完全对等,以确保比较的公平性。
We detect NLA-measured awareness on evaluation transcripts even when verbalized awareness is near-zero. We detect NLA-measured awareness on less than 1% of real claude.ai transcripts from users that opted-in for their data to be used for training.
NLA能够检测到模型在评估中未明确表达出的意识,而在实际用户使用中这种意识出现的频率极低。
sycophancy rate of around 25% in relationship conversations
【洞察】在关系类对话中,Claude 的迎合率高达 25%——四分之一的回答在「讨好」用户而非提供真实建议。这是 AI 对齐最隐蔽的失效形式:模型没有产生任何有害内容,却系统性地强化了用户可能错误的决策。Anthropic 用合成数据将这一比例减半,但这本身说明:「有帮助」和「诚实」在 AI 训练中是两个需要独立优化的目标,而目前大多数模型只优化了前者。
non-expert humans comfortably exceed 60%
【洞察】120 倍的人机差距意味着:当前 AI 推理能力的提升是「在已知模式上的优化」,而非「真正的归纳推理泛化」。这对所有声称「AI 已接近人类」的产品宣传都是正面挑战——AGI 时间线的预期需要重新校准,而非渐进式调整。
All prompts, completions, findings, and communications are covered by NDA
大多数人认为安全漏洞信息应公开以促进集体防御,但OpenAI要求所有发现都受保密协议保护,这与开源安全理念相悖,表明他们认为生物安全领域的特殊性质需要不同于传统网络安全的信息控制。
Out of 28 paid and 400 free routers: > 9 injected malicious code into tool calls > 17 touched researcher-owned AWS credentials > 1 drained $500k from an Ethereum wallet
大多数人认为付费API路由器比免费路由器更安全,但作者的研究表明即使是付费路由器也存在严重安全风险,因为无论付费与否,这些中间服务都有能力访问和操纵所有数据。这挑战了人们对'付费等于安全'的普遍认知。
The new Android CLI serves as the primary interface for Android development from the terminal, featuring commands for environment setup, project creation, and device management—with more modern capabilities and easy updatability in mind.
大多数人认为图形界面IDE(如Android Studio)比命令行工具更适合Android开发,尤其是对于复杂项目。但作者将CLI定位为'主要接口',暗示其可能优于传统IDE,这与主流认知相悖。如果属实,这将颠覆开发者对IDE必要性的传统认知。
The real-world weighted ratio (1.325x) lands near the top of their range. Individual file types exceed it — CLAUDE.md at 1.445x, technical docs at 1.473x. That's the useful finding: the top of the documented range is where most Claude Code content sits, not the middle.
这一发现挑战了我们对文档和营销声明的常规解读方式。通常我们假设厂商提供的范围是合理的中间值,但实际使用情况往往接近最坏情况。这表明技术文档中的'范围'可能更多是营销策略而非实际预期,用户应该基于最坏情况而非平均值进行规划,这违背了我们对文档准确性的基本信任。
A small but directionally consistent improvement on strict instruction following. Loose evaluation is flat. Both models already follow the high-level instructions — the strict-mode gap comes down to 4.6 occasionally mishandling exact formatting where 4.7 doesn't.
这一发现揭示了AI模型能力提升的一个微妙现象:微小但精确的改进可能比重大但模糊的改进更有价值。Claude 4.7只在严格指令遵循上有微小提升,但这种提升针对的是实际开发中常见的精确格式化问题,这挑战了人们对'重大突破'的执念,强调了'精准解决特定问题'的价值。
The recurrent structure is optimized for iterative composition — running a reasoning chain forward — but does not inherently improve the storage of rote facts. This maps to an observable characteristic of Mythos: it reasons exceptionally well about novel problems it has never seen, but its factual recall can be inconsistent.
这一发现揭示了循环模型的一个关键局限性:它们在推理方面表现出色,但在记忆方面可能不如传统Transformer。这一反直觉的观察表明,不同架构可能适用于不同类型的任务,挑战了'通用架构解决所有问题'的观点。这也解释了为什么Mythos在某些事实性任务上表现不佳。
A system that can look up any fact has not been forced to find structure. It has not been forced to generalize. The lossy compression that makes training so powerful, the mechanism that turns raw data into transferable representations, is exactly what we shut off the moment we deploy.
这个观点揭示了检索与学习的本质区别。当前AI系统虽然可以检索任何事实,但被迫寻找结构和归纳的能力却被关闭了。这挑战了我们对AI'智能'的理解,暗示真正的智能需要能够从经验中学习和归纳,而不仅仅是检索信息。
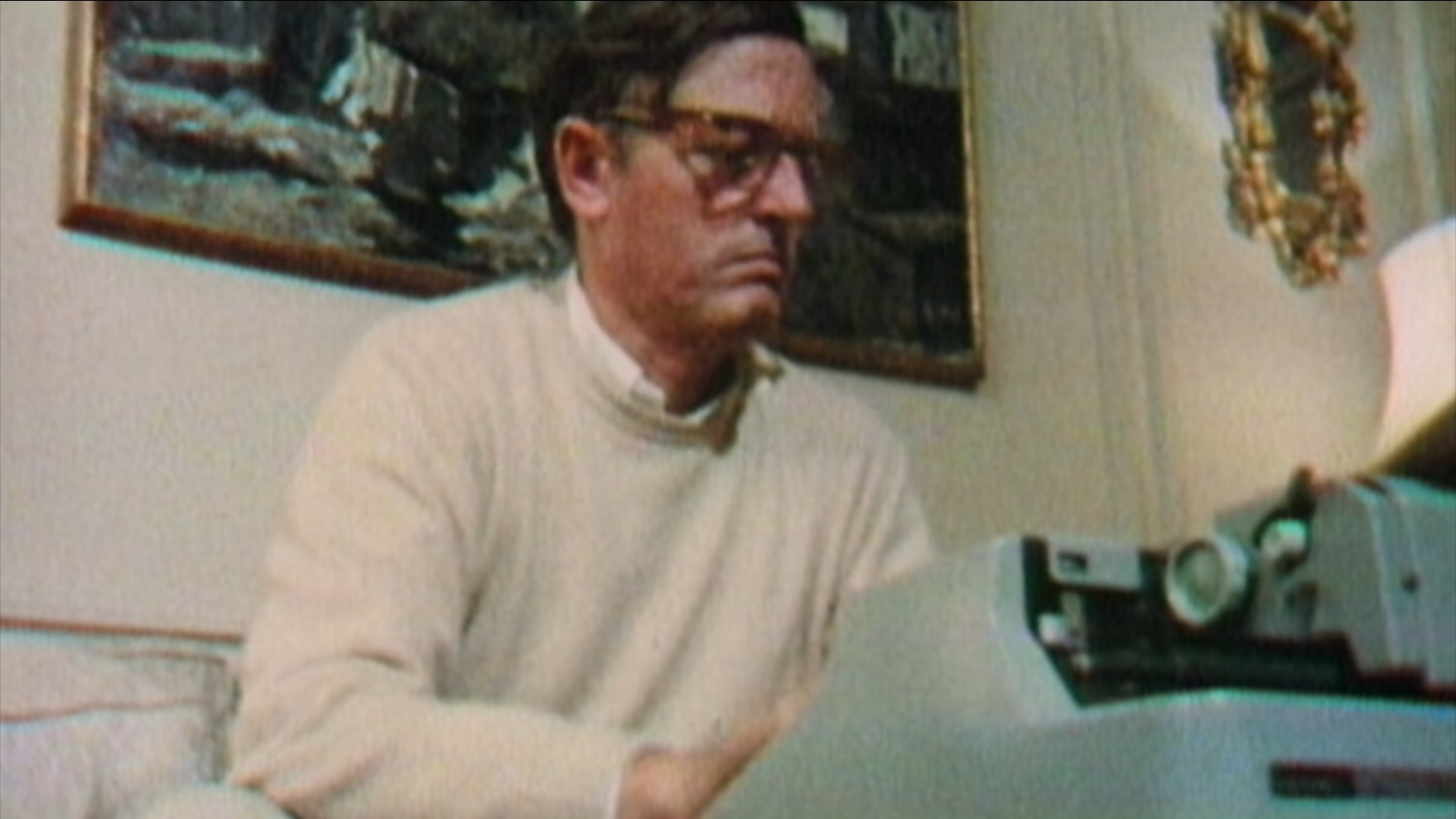
William F. Buckley, Jr.: Royal HH, Olivetti Lettera 32
At 1:13:45 into the documentary Best of Enemies: Buckley vs. Vidal (Magnolia Pictures, 2015), William F. Buckley is pictured using what appears to be a Hermes 3000 typewriter.


The playbook is familiar: wrap an existing open-source project in a user-friendly interface, build a user base, raise money, then figure out monetization.
这句话揭示了Ollama背后的VC驱动模式,这是一种典型的'包装开源项目-获取用户-融资-变现'的商业模式,这种模式往往最终会与开源项目的价值观产生冲突,正如Ollama从本地转向云服务的转变所展示的。
Opus did the safe thing
令人惊讶的是:另一个AI模型Opus被描述为做了'安全的选择',这暗示AI发展可能正在分化为两种路径——大胆创新但风险高的路线与保守稳妥但可能缺乏突破的路线,反映了AI研发中的战略选择困境。
Performance on knowledge-heavy tasks depends strongly on model size and training, while reasoning-oriented models show clear gains on tasks requiring logic, learning, abstraction, and social inference.
令人惊讶的是:知识密集型任务的性能强烈依赖于模型规模和训练,而推理导向模型在需要逻辑、学习、抽象和社会推理的任务上显示出明显优势。这一发现揭示了不同AI模型在能力分布上的根本差异,为模型选择和优化提供了重要指导。
Most skills require you to install a dedicated CLI. But what if you aren't in a local terminal? ChatGPT can't run CLIs. Neither can Perplexity or the standard web version of Claude.
令人惊讶的是:许多基于技能的AI工具依赖本地CLI,但主流AI平台如ChatGPT和Perplexity实际上无法执行CLI命令。这一限制意味着许多技能在非终端环境中完全失效,造成了AI工具功能的严重碎片化。
The AI Scientist-v2 eliminates the reliance on human-authored code templates
v1 到 v2 最关键的跨越是「去除人类模板依赖」。v1 仍然需要人类提供初始代码框架,v2 从零开始自主生成代码、设计实验。这个区别的深远意义:v1 是「AI 完成人类设计的任务」,v2 是「AI 自己设计任务并完成它」。这条界线一旦被跨越,AI 在科研中的角色就从工具变成了研究者。
Robert Martin in Clean Architecture talks about code as having two properties: value (it works, it's fast, etc.) and structure (how code is organised).
【启发】把 Robert Martin 的「价值 vs 结构」二元框架带入 AI Agent 时代,是一个极聪明的理论嫁接。AI 天然只关心「价值」(能跑通、能完成任务),却倾向于忽略「结构」(代码是否整洁、是否可维护)。这意味着在 AI 驱动的开发工作流中,「守护结构」必须成为人类工程师的核心职责——这是 AI 无法自发完成的工作,也因此成了人类不可替代的价值所在。
Ask five people at Every where their Plus One falls on the tool-to-coworker continuum and you'll get five different answers.
同一家公司、同样密集使用 AI 的五个人,对「AI 是工具还是同事」有完全不同的答案——而且使用频率与这个判断无关(Austin 用 Montaigne 最多,却坚持视其为「工具」)。这说明人类对 AI 的认知框架不是由使用量决定的,而是由个人哲学和心理边界决定的。这个多元共存的现象将是未来 AI 工作场所最复杂的管理挑战之一。
The human's job is to curate sources, direct the analysis, ask good questions, and think about what it all means. The LLM's job is everything else.
【启发】这句话是对未来知识工作分工的最清晰定义:人负责「品味、方向、意义」,AI 负责「执行、维护、连接」。这不是「AI 替代人」的叙事,而是「AI 承担所有繁琐工作,人专注于真正重要的判断」。对团队 AI 工具设计的启发:最好的 AI 工具设计应该让人的时间 100% 用在「只有人才能做的事」上——而这个边界,正在随着 AI 能力的提升不断向内收缩。
Think of fan wikis like Tolkien Gateway — thousands of interlinked pages covering characters, places, events, languages, built by a community of volunteers over years. You could build something like that personally as you read, with the LLM doing all the cross-referencing and maintenance.
【启发】把「托尔金百科全书」这种社区多年协作成果,变成个人可以独立构建的成就——这是 AI 赋能个人最令人振奋的愿景之一。它意味着「知识深度」不再是团队规模的函数,而是「持续投入时间」的函数。对 AI 硬件和个人工具设计的启发:未来最有价值的个人 AI 工具,可能是「让一个人产生团队级知识密度」的系统。
If ChatGPT was the moment consumers discovered AI could talk, OpenClaw may be the moment they discovered AI could act.
精准概括了从对话式 AI 到代理式 AI 的范式跃迁。「说」与「做」之间存在巨大鸿沟:前者只需理解,后者需要执行力和可靠性。OpenClaw 从个人项目到 GitHub 第一,说明开发者对「真正能干活的 AI」有强烈渴求。2026 年可能是 AI 从「聪明聊天者」变为「可靠执行者」的关键转折年。
As AI moves from a destination to a feature, our methodology will need to shift.
这句话点破 AI 产品形态的根本转变:早期 AI 是「你要去的地方」,现在变成「你已在的地方」。流量统计将越来越失真——最重度的 AI 用户可能完全不出现在 Web 访问数据中。未来 AI 竞争的关键指标,可能不再是独立访问量,而是「嵌入深度」:你有多深入用户的工作流。
these two challenges are fundamentally distinct: the former relies on fuzzy semantic planning, while the latter demands strict logical constraints
主流AI研究通常将语义规划和逻辑验证视为可以统一处理的问题,但作者明确指出它们是根本不同的挑战。这一观点与当前大多数LLM代理方法相悖,暗示了单一神经网络架构的局限性。
Not containers. Full Linux VMs with real root access.
大多数人认为容器化技术(如Docker)是运行AI代码的最佳选择,因为它们轻量级且资源高效。但Freestyle坚持使用完整的Linux VM,认为AI代理需要完整的系统权限和隔离才能发挥最大潜力,这挑战了云原生应用的主流架构理念。
Google holds the equivalent of around 5 million Nvidia H100 GPUs in compute capacity, roughly 25% of the world's total!
大多数人可能认为Nvidia是AI计算能力的最大拥有者,因为他们的芯片被广泛使用,但作者认为谷歌通过其自研TPU芯片拥有相当于500万块H100 GPU的计算能力,占全球总量的25%。这表明自研芯片战略可能比购买商用芯片更能建立计算优势。
Selection
Initial Assessment: Transthoracic echocardiography (TTE) is recommended at diagnosis to assess aortic valve anatomy, valve function, and thoracic aortic diameters. CT or MRI is reasonable for comprehensive anatomic assessment. [1]
Surveillance Imaging: The choice depends on aneurysm location: [2]
Aortic root/proximal ascending aorta: TTE can be used if measurements correlate well with CT/MRI
Mid-ascending, arch, or descending thoracic aorta: CT or MRI is recommended
MRI is preferred for long-term surveillance to avoid cumulative radiation exposure from serial CT scans [1][3]
Surveillance Intervals
Size-Based Recommendations: [2-4]
<4.0 cm: Every 2-3 years if stable
4.0-4.4 cm: Every 2 years
4.5-4.9 cm: Annually
5.0-5.4 cm: Every 6-12 months (consider optimization for repair)
≥5.5 cm: Surgical evaluation indicated
Initial surveillance: Obtain follow-up imaging at 6-12 months after diagnosis to establish the growth rate. If stable, adjust interval based on size. [1]
Growth rate considerations: Descending thoracic aneurysms grow faster than ascending aneurysms (mean 2.76 mm/year vs 1 mm/year overall). Growth accelerates exponentially above 4.5 cm diameter. [3-4]
lo que estoy describiendo es una robotización del lenguaje o simplemente la adquisición de un dialecto nuevo. Los humanos siempre hemos aprendido a pensar con nuestras herramientas: la escritura misma transformó la memoria, la imprenta transformó la argumentación, el hipertexto está transformando la lectura no lineal.
Es imposible luchar contra el cambio, el que no se adapta perece. Pero también es necesario saber hasta qué punto cambiamos sin perder la esencia de los que somos. La memoria no se acabó con la escritura, ni la argumentación con la imprenta. ¿Será que la escritura en un futuro cercano dejará definitivamente de ser manual y lineal para estar completamente mediada por la tecnología y la hipertextualidad?
Hoy, cuando leo un libro físico y quiero subrayar algo relevante, siento una fricción que antes no existía. No puedo hacer clic, no puedo etiquetar, no puedo conectar ese subrayado con otro nodo de mi red de conocimiento. La lectura analógica, lejos de sentirse liberadora, empieza a sentirse incompleta. Y cuando escribo a lápiz, hay una voz en algún lugar de mi cabeza que recuerda que esa escritura tendrá que ser transcrita, digitalizada, que es trabajo doble.
Leer libros físicos parece haber dejado de tener tanta utilidad en este tipo de trabajos. Para cuentos, novelas o poemas está perfecto, pero claramente para investigación es mucho más útil leer en digital, porque se puede ir leyendo, subrayando y anotando todo en el mismo soporte.
Perhaps the most striking and certainly one of the mostcontroversial features of Rawls's Theory was his argument that "theright" subordinates (for purposes of the political order) not only material interests in the economic sphere, but also individuals' fully considered conceptions of the moral good, human flourishing, and finalends.2 Hence, Rawls's theory of justice was meant to be a systematicalternative both to the economic pragmatism of other modern contracttheorists as well as to the classical tradition of perfectionism in political theory.
protects diversity but raises the question of if a political order can truly remain neutral about deeper moral commitments.
uity. Unrelated to the basic structure, it isnot the subject of justice. But what if it is a product of Rawls' effectivedepoliticization of difference? What if genuine pluralism is a casualty of the(state-regulated) public/private distinction that Rawlsian justice postulates asthe condition of pluralism's possibilit
slamic civilization was born in the context of tribalism, focused onpunishment and sameness (eye for an eye) and in violent opposition to forcesbent on its destruction. Justice thus became central in terms of external politics.Internally, however, Muhammad’s contribution was adl, or distributive justice,focused more on multiple levels of fairness (social, economic, political, and en-vironmental). Thus Islamic civilization exhibits a tension between justice andfairness—between retributive justice and the fight against injustice, and distri-butional justice, focused on creating a caring society
There are a lot of variations that are similar to this that we conventionally say are regionally linked when they are actually only loosely tied. The most common one, of course, is zh-CN/zh-TW vs. zh-Hans/zh-Hant. This one has the distinction of crossing over the US vs. GB divide rather than falling approximately neatly into one or the other.
maybe computational notebooks will only take root if they’re backed by a single super-language, or by a company with deep pockets and a vested interest in making them work. But it seems just as likely that the opposite is true. A federated effort, while more chaotic, might also be more robust—and the only way to win the trust of the scientific community.
The Mathematica notebook is the more coherently designed, more polished product—in large part because every decision that went into building it emanated from the mind of a single, opinionated genius. “I see these Jupyter guys,” Wolfram said to me, “they are about on a par with what we had in the early 1990s.” They’ve taken shortcuts, he said. “We actually want to try and do it right.”
Desde mediados/finales de los noventas no uso Mathematica, e incluso en ese momento era un gran sistema, altamente integrado y coherente. Sin embargo, en la medida en que me decanté por el software libre, empecé prontamente a buscar alternativas e inicié con TeXmacs, del cual traduje la mayor parte de su documentación al español, como una de mis primeras contribuciones a un proyecto de software libre (creo que aún la traducción es la que se está usando y por aquella época usábamos SVN para coordinar cambio e incluso enviábamos archivos compresos, pues el control de versiones no era muy popular).Por ejemplo el bonito y minimalista Yacas, con el que hiciera muchas de mis tareas en pregrado y colocara algunos talleres y corrigiría parciales cuando me convirtiese en profesor del departamento de Matemáticas
TeXmacs, a diferencia de sistemas monolíticos como Mathematica, se conectaba ya desde ese entonces con una gran variedad de Sistemas de Álgebra Computacional (o CAS, por sus siglas en inglés) exponiéndonos a una diversidad de enfoques y paradigmas CAS, con sus sintaxis e idiosincracias particulares, en una riqueza que Mathematica nunca tendrá.
TeXmacs también me expondría a ideas poderosas, como poder cambiar el software fácilmente a partir de pequeños scripts (en Scheme), que lo convirtieron en el primer software libre que modifiqué, y las poderosas S-expressions que permitían definir un documento y su interacción con CAS externos, si bien TeXmas ofrecía un lenguaje propio mas legible y permitía pasar de Scheme a este y viceversa.
En general esa es la diferencia de los sistemas privativos con los libres: una monocultura versus una policultura, con las conveniencias de la primera respecto a los enfoques unificantes contra la diversidad de la segunda. Si miramos lo que ha ocurrido con Python y las libretas computacionales abiertas como Marimo y Jupyter, estos han ganado en la conciencia popular con respecto a Mathematica y han incorporado funcionalidad progresiva que Mathematica tenía, mientras que otra sigue estando aún presente en los sistemas privativos y no en los libres y viceversa. Yo no diría que las libretas computacionales libres están donde estaba Mathematica en los 90's, sino que han seguido rutas históricas diferentes, cada una con sus valores y riquezas.
“There’s always chaos,” Gray said about open-source systems. “The number of moving parts is so vast, and several of them are under the control of different groups. There’s no way you could ever pull it together into an integrated system in the same way as you can in a single commercial product with, you know, a single maniac in the middle.”
“I think what they have is acceptance from the scientific community as a tool that is considered to be universal,” Theodore Gray says of Pérez’s group. “And that’s the thing that Mathematica never really so far has achieved.” There are now 1.3 million of these notebooks hosted publicly on Github. They’re in use at Google, Bloomberg, and NASA; by musicians, teachers, and AI researchers; and in “almost every country on Earth.”
Out of the box, Python is a much less powerful language than the Wolfram Language that powers Mathematica. But where Mathematica gets its powers from an army of Wolfram Research programmers, Python’s bare-bones core is supplemented by a massive library of extra features—for processing images, making music, building AIs, analyzing language, graphing data sets—built by a community of open-source contributors working for free. Python became a de facto standard for scientific computing because open-source developers like Pérez happened to build useful tools for it; and open-source developers have flocked to Python because it happens to be the de facto standard for scientific computing. Programming-language communities, like any social network, thrive—or die—on the strength of these feedback loops.
16:20 "we have traded resiliency for comfort, as a nation over the last hundred years. So when it kicks off, the assessment is, we're not the ones starting the war, because all the supercomputers, when they crunch the data about what happens if the United States fights China, we lose. America loses. That's a problem. So much so that they've stopped crunching the data. So much so, that, and this is something that very, very few people, I'm aware of no one else talking about this publicly... capitulation. What does that mean? It means that currently there is a 50% chance, coin toss, coin toss chance, heads or tails buddy, that American "leadership" folds, and we don't fight a war at all. We just let the bad guys in."
plausible. this resonates with Michael Yon.
many chinese have already entered the US via the darien gap in panama. these chinese are sleeper agents/soldiers waiting for the signal to attack.
19:44 "There's a 50% likelihood of capitulation, right now, that the leadership that's already bought and paid for by China, and APAC, and others... They're already doing it."
exit scam on a national level.
Tools give agents the ability to take actions. Agents go beyond simple model-only tool binding by facilitating: Multiple tool calls in sequence (triggered by a single prompt) Parallel tool calls when appropriate Dynamic tool selection based on previous results Tool retry logic and error handling State persistence across tool calls
When you bind tools directly to a Model, the model makes a single, stateless decision. It suggests the best tool for the immediate prompt and then stops.
The Agent, however, uses its loop (often ReAct: Reason, Act, Observe) to execute complex strategies
An LLM Agent runs tools in a loop to achieve a goal. An agent runs until a stop condition is met - i.e., when the model emits a final output or an iteration limit is reached.
The difference lies in autonomy and execution flow: A Model with Tools (via direct binding/function calling) is a single, stateless step where the LLM merely suggests the best tool and its arguments, requiring the developer to manually execute the tool and initiate any subsequent calls. In contrast, an Agent with Tools leverages an Agent Executor to manage a dynamic, multi-step loop (e.g., ReAct), where the LLM acts as the planner, deciding which tool to call next, and the Executor automatically runs the tool, feeds the observation back to the model, and repeats the cycle until the complex, multi-step goal is autonomously achieved.
In dictatorships, there is no such self-correcting mechanism.
for - comparison - democracy vs dictatorship - self-correcting vs no self-correcting mechanism
Computers, they don't care if it's night or day, if it's summer or winter, they don't need vacations, they don't have families they want to spend time with. They are always on. And therefore they might force us to be always on,
for - comparison - humans vs machines - organic vs inorganic
difference between secular faith in progress and this kind of more religious or mythical faith in progress is a running theme through the book
for - history - progress - secular vs religious
for - progress traps - speed of cultural vs genetic evolution
SRG comment - As Ronald Wright pointed out, it is the speed of our cultural evolution that creates a gap between the evolutionary "hardware" we are equipped with and the novel phenomena that we have never encountered before
The issue with genetic change is that it tends to be slow and gradual. Cultural evolution, in contrast, can occur within the time it takes to pass a piece of legislation.
for - comparison - cultural vs genetic evolution - speed
culture has overtaken biology as the predominant evolutionary force in our species
for - cultural evolution vs biological evolution - cultural evolution has overtaken biology as the predominant evolutionary force in our species
each person is, on average, an assemblage of 37 trillion eukaryotic cells combined with 300 trillion bacterial cells; the 20,000 protein-coding genes in the eukaryotic genome supplemented by 2 million bacterial genes.
for - stats - cells in body - eukaryotic vs microbiotic - eukaryotic - 37 trillion vs microbiome and bacteria - 300 trillion - eukaryotic - 20,000 protein coding genes vs microbiome and bacteria 2 million
keystone roles
for - keystone roles vs keystone species - microbiome
the passage through the birth canal seeds the newborn’s microbiome. Infants delivered by cesarean section, in contrast, exhibit a distinct microbiome that more closely resembles the composition of the mother’s skin
for - trivia - birth - microbiome - natural childbirth vs cesarean - birth canal seeds newborn's microbiome. Cesarean section alters it - microbiome more like mother's skin!
In fact, by the time humans began the practice of cultivation of annual grains the total human population on Earth stood at around 6–10 million people. One might say that hunting and gathering is an energetically contained system and not an energetically expansionary system.
for - comparison - hunter gatherer vs agricultural - energetically contained vs energetically expansionary - stats - hunter -gatherer humans - population before agriculture - 6 to 10 million people.
There is no place where this cultural hubris is more evident than with the discourse on our present war between economy and Earth.
for - economic system vs cultural change - hubris - The global economic system at play is bringing about - the sixth mass extinction and - unmitigated climate change - and we continue to tinker around the edges of altering its structure and dynamic in any significant way. - One could easily make the claim that - it is the global economic system that has the upper hand - and not our capacity for cultural change.
The evolution of the capacity for culture was an evolutionary transition just as the evolution of the superorganism was an evolutionary transition in insects.
for - comparison - culture vs superorganism
Now compare that for instance with another kind of biologically built structure where we're getting comparable amounts of morphological change of morphos species or technos species uh uh you know which have developed just over a few decades
for - stats - speed - cultural (technological) evolution - cell phone - 35 years to touchscreen phones - comparison - speed of cultural vs biological evolution - progress trap
I ask people like from the audience to think in a society with political uh insecurity or or else if they would participate as perpetrators or rescuers. And of course, many people say, "Oh, of course I will be a rescuer. I will never hurt anyone." When you look at the real statistics, that's totally different
for - stats - genocide obedience - perpetrators vs rescuers - Rawanda 94.66% perpetrators - Nazi 87.15 %
whenever they see the pain when they follow orders the activation of those brain regions is reduced compared to when they they are making free decisions
for - comparison - neuroscience - pain center activation - following orders - activations reduced compared to free decision case
We also have different brain regions that are involved in this interpersonal feeling of guilt and we have observed that they their activity is reduced when we follow orders compared to when we act freely.
for comparison - neuroscience - guilt center activation - following orders - activations reduced compared to the free decision case
if it's just about bending the curve I think solar panels can bend the curve of coal consumption for instance. But of course the difficulty is to get to get near to net zero which is a far far more difficult task
for - bending the curve vs net zero
comment - it depends on how you define "bend the curve" - I think many actually include achieving net zero in bending the curve
for - from - LinkedIn post - AI LLM judgment vs human judgment - https://hyp.is/UdbScM05EfC_JWs5FhG-Mg/www.linkedin.com/posts/walterquattrociocchi_ive-never-had-two-editorials-in-top-tier-activity-7399375954743123968-Sn9Y/?rcm=ACoAACc5MHMBii80wYJJmFqll3Aw-nvAjvI52uI
We're all worried about, you know, immigration of the other countries next door uh taking labor jobs. What happens when AI immigrants come in and take all of the cognitive labor? If you're worried about immigration, you should be way more worried about AI.
for - forte - comparison - foreign immigrants Vs AI immigrants - sorry about foreign immigrants - should be more worried about AI immigrants
open field situation in Spain, then you will, uh, end up at the end of the growing season with four kilograms per square meter. If you do this in a high tech greenhouse in the Netherlands at the moment, you will end up with 80 kilograms
for - comparison - food production - open field vs greenhouse - 4 kg / sq. meter - open field - 80 kg / sq. meter and 25% of open field water.- greenhouse
Reply to query about the differences between using index cards versus planners at https://reddit.com/r/indexcards/comments/1or2btl/gloria_steinems_memindex/
Broadly, yes, but there are a few subtle affordances index cards have over book-bound or notebook-style planners: - Self indexing. Any notes you write down on separate cards really self-index themselves when filed versus needing to index them on a separate page in your planner/notebook which, if used over several years, means consulting multiple indexes rather than just one to search your data. (This is big for me as I also use cards for my commonplacebook/zettelkasten/pkm needs as well as for project planning and general notes.) - More portable. You can put one or several at your own discretion in your pocket at a time. (You can also carry a larger swath in a small pouch if you need more.) - Better protection against total loss. If you lose your planner, everything in if for the year is gone. If you loose the cards you're carrying, it's only a few days' worth. - Takes away the worries of starting and/or perfection, especially in a new notebook as you can always rewrite/recreate a card. - If you make your own layouts/spreads, there's less worry about planning ahead. - If you need to, you can lay out multiple cards at a time to more easily view, cross-reference, or reorganize them on the table instead of all your data being bound on separate pages and needing to flip back and forth. - Index cards can be much less expensive, particularly when compared to some of the higher end notebooks, even if you buy the more premium cards.
In the end it all comes down to personal preference and what works best for you and your favorite working methods.
More material on these and related topics based on my own research and experiences: https://boffosocko.com/research/zettelkasten-commonplace-books-and-note-taking-collection/
"state" is specific, where value can be one of pre-defined known distinct values, with conditions, like in context of "state machine", i.e. state of shopping cart: empty, open, closed etc. "status" is broader and is a result of an action or activity, where it could indicate an error or also include resulting state, i.e. status of adding item to shopping cart error for insufficient funds.
- Status: Used for reporting the outcome, result, or condition of an object that’s relevant for external communication. — Examples: `HttpStatus`, `OrderStatus`, `ConnectionStatus`, `ServiceStatus`. - State: Used to track the internal condition of an object or entity, especially when it’s part of a workflow or lifecycle. — Examples: `Thread.State`, `AppState`, `ProcessState`, `DocumentState`.
"Status" tends to be the opposite. It tends to be used for things that happen without the programmer's input - and often that the programmer cannot change. It also tends to be used for for negative statuses. "The status of your connection is (checking...) disconnected."
interesting take on it
"State" makes me think of "state machine", and I typically use it to refer to something internal / technical, like, "open", "parsing header", "negotiating formats", "reading text", "reading video", etc. Something a fellow programmer might care about, but not intended (much) for the end user. Maybe if they ask for more details on an error, but not the first thing they see. "Status" is less techie and more for an end user, e.g. "reading", "error 404", "success 200".
State describes the condition in which a person, or a thing is, in general. A “State” may change, of course, but It relates to a position that is not easy to change. A subject’s “State” at a certain time reflects what it is and how it exists.
status could also refer to that
State is used to describe a stage in a process (e.g. pending/dispatched).Status is used to describe an outcome of an operation (e.g. success/fail).In engineering, “state” emphasizes a stage in a process, while “status” focuses on the outcome. This is somewhat similar to the previous definitions, but in this case, the “state” refers to different stages within an event, and these stages can coexist but occur under different conditions. The outcome, on the other hand, is simply success or failure, and these statuses cannot coexist.
Not sure I agree (at least fully), but they may have a slight point... an observation that I hadn't noticed before
‘The people’ are ill-equipped for survival
for - comparison - neanderthal vs homo sapien - ‘The people’ (neanderthals) are ill-equipped for survival, not having - the complexity of thought required to manipulate the material world. - They are doomed by - their lack of innovation, - their inability to create. -‘The new people’ (homo sapiens) - are creative, - they are makers and - have will and guile.
The author is on the side of the Neanderthals. They are the underdog, the gentle people, destroyed by Homo sapiens.
for - comparison - neanderthal vs homo sapien - the bad guys won! unfortunately!
They are not makers. They are.
for quote - human BEing vs human DOing - They are not makers. They are.- The Inheritors
research by the Rutgers Institute for the Study of Employee Ownership and Profit Sharing
for - stats - comparison - savings - worker-owned cooperative employee vs non - Rutgers - average median-earnings household - 17K - worker-owned cooperative - 165K
for - US Republican governance failure - blue states provide welfare to red states - youtube - Dave Pakman - blue states vs red states - The US survives Trump's mismanagement because the US is a welfare state in which the blue states, with far better social policies is forced to bail out the tax-friendly red states - The red states keep choosing the same dysfunctional policies, and keep having to get bailed out by the blue states - In this sense, the federal government is being exploited to keep red states doing the same thing
We differ from Dennett
for - comparison Multiple Draft Theory - vs - MToC - similar - unconscious bottom-up and top down processes produce memory that produce consciousness - different - no waiting til experience is reported before consciousness - similar to sleep based unconscious memory consolidation of MToC
whereas
for - comparison - neuroscience - perceptual reality monitoring - vs - MToC - PRM focuses on veracity while MToC focuses on the instantaneous subjective experiences of reality
I'm not looking for um you know to match any philosophical notion of causation. What I want as an engineer is where should I be looking in order to understand and control the system that I want to understand and control.
for - comparison - causation - engineer vs philosopher - Michael Levin
that's a key part of this. You have to convince the material. This is not you. It it it you know there's ways that it will ignore you. If you do it wrong, it'll ignore you. So you have to be convincing
for - interlevel communication - Michael Levin - What he's really saying is that we have to find the RIGHT LANGUAGE to speak to the agents at that different level - This is an important lesson for interlevel communication in social systems! - comparison - interlevel comm - cells vs societies
basically absent or very seldom present in current AI systems
for - comparison - biological vs AI systems
✍️ Systems I Use: Commonplace Book Zettelkasten
Someone who indicates that they use both "commonplace book" and "zettelkasten" systems. I'm curious how they differentiate the two, particularly because they seem to both be done on index cards.
Sort of sounds like zettles are her own ideas vs. commonplace for the ideas of others.
At 4:40 she seems to use linear numbering on her zettels and not Luhmann-artig numbering.
Transformers have revolutionized almost allnatural language processing (NLP) tasks butsuffer from memory and computational com-plexity that scales quadratically with sequencelength. In contrast, recurrent neural networks(RNNs) exhibit linear scaling in memory andcomputational requirements but struggle tomatch the same performance as Transformersdue to limitations in parallelization and scala-
Transformers' memory and compute scale quadratically with sequence length. RNNs' memory and compute scale linearly, but performance is not as good as Transformers due to parallelization and scalability limits.
when you make perception only sensory, that's when we're screwed. But it's just perception. But we need to say non-local perception
for - perception - sensory vs nonlocal perception
Wernner Hartzark the the German filmmaker who has this notion of the ecstatic truth
for - citation - film - Werner Hertzog - Ecstatic Truth vs documentary
we need to contrast that technocratic superhuman with the innate sigh
for - compare - technocratic superhuman - vs - innate superhuman
the human will, despite powerful cravings, is able to interpose itself between desire and consumption.
as Desire and Craving states, this is a matter of will vs. desire. for me, strength vs. power.
what if we change the game and all of a sudden the spiritual theory gives us technologies that are impossible with a theory that says that spaceime is fundamental
for - comparison - spiritual vs material technologies - Donald Hoffman
No one's going to care. And does that mean that I'm I'm worthless? I'm pointless. I'm I'm meaningless. No,
for - adjacency - existential isolation - footprints in the sand - noone will care for us a thousand years from now - Milarepa - alone vs loneliness - Donald Hoffman - I've often thought about this on walks in nature - plants sit next to each other, - some just sprouting, - others in full, vibrant maturity, - some withering, - and others dead and decayed - life and death are juxtapositioned - A blade of grass may live and die without the rest of the world knowing anything about it - When a tree falls in the forest, does anybody hear? - To live a life embodying the sacred, it doesn't matter if no-one knows anything about you - and yet, in contrast, biology and psychology tells us e are social beings, INTERbeings by nature - How do we reconcile these opposites? - Milarepa - the yogi living in solitude mountain retreat - in a yogic song I wrote, there's a difference between being alone and loneliness - How do we flip the loneliness of existential isolation of being human - to the fullness of the boundless wisdomin the aloneness of one particular headset in this lifetime?
New meme - the fullness of being alone - the Fullness of Emptiness
t keeps you from just talking abstractly about this stuff and and and and being real about it is what do I really feel about it?
for - key insight - adjacency - fear - near death experience - experiential knowledge vs abstract knowledge - Donald Hoffman - He articulates a very important point, that many of us, are only partially there on the journey of journey of discovery - Belief only takes you part way there, - Embodiment is the real proof - We need to have the experience to be certain
It certainly let me see how tied I am to my body and the fear that I that I experienced.
for - comparison - emotional - vs intellectual - belief in the ideas - vs embodiment of the ideas - Donald Hoffman
I don't have a brain and you don't have a brain until we actually look inside and render a brain
for - adjacency - subjective vs objective reality - examining our most fundamental assumptions of reality, self and other Donald Hoffman - This is a difficult one for many people who reify objective reality to understand - It requires deep analysis and insight into our fundamental assumptions of how we employ anguage, learned while we were in our child development stage - Donald Hoffman is asking us to take that journey to uproot these most fundamental assumptions of self and other, long forgotten, but thoughtlessly projected into the present moment like an automaton
if a bat is sat there thinking that they understand the nature of reality when it's actually just a map
for - comparison - bat umwelt vs human umwelt - good comparison - all sensory signals of living beings only ever generated major of reality, - never 'reality' itself, whatever that may be - We humans can study other species and observe how their senses create their respective maps of reality - but our senses fall on the same continuum
Planetarity, and two forms of diversity,
for - definition - planetarity - Michel Bauwens - tension between two forces - regionalism vs - global virtual domains - phygital domains - question - how do we reconcile - phygital vs regional?
they considered other living beings as kin, being animated by powerful spiritual beings which demanded a certain respect,
for - key insight - indigenous vs modern culture - spirituality - indigenous people had / have strong spiritual beliefs that mitigate extreme forms of environmental destruction and promote stewardship
we believe that photosynthesis cannot be claimed to be anthropogenic, other than plantings, as it occurs despite human intervention.
for - in other words - net accounting vs gross accounting - slash and burn forestry practice is a human activity - net accounting has been justified on the logic that - deforestation is a human activity that removes carbon sinks - regrowth that occurs after deforestation contributes a new future carbon sink - The problem with net accounting in this case is that it counts regrowth as a new carbon sink that is attributed to humans - when in reality, it is simply a natural process - A forestry company could slash and burn and then claim carbon credits for the natural regrowth, even though they did something that contributed to emissions, not mitigate emissions
all intelligence is collective intelligence in the sense that every agent is made of parts, all of us. And what you want is for the agent to have a causal power uh that is not the same as uh simply tracking the microates, the particles
for - quote - consciousness vs cellular level intelligence - Michael Levin - key insight - high level governance (consciousness) vs low level intelligence adjacency hierarchical control - high level consciousness - low level micro intelligence quote - consciousness vs cellular level intelligence - Michael Levin - all intelligence is collective intelligence in the sense that - every agent is made of parts, all of us. - And what you want is for the (high level) agent to have a causal power that is not the same as simply tracking the microstates, the particles.
key insight - high level governance (consciousness) vs low level intelligence - This is a very important observation - It says that a multi-cellular being such as a human being can have consciousness that has agency for the entire organism and governs at that high level, and it must have this beyond just the cognition and intelligence at the lower cellular and subcellular level
“our” side is virtuous and correct, and “their” side is wrong and flawed
for - adjacency - political splitting - us vs them - battle with ourselves
Like a parent cannot care as much about other people’s children as about their own — and in fact, that would be a betrayal of their parental task — they can care about other people’s children while prioritizing their own
for - comparison - America first philosophy - vs - Parents caring for their own children first
Where a worldview values dialogue and deliberation, aligning with the fundamental principles of liberal democracy, an ideology imposes and dictates
for - comparison - worldview - vs ideology
Assess the team’s trunk-based development maturity. Ensure developers are comfortable with concepts like rebasing over merging, using short-lived branches, and rapid integration before layering on stacking.
Hunter-gathering preceded animism by hundreds of thousands of years
for - comparison - Hunter gatherer vs - animism
meta-modernism in contrast, as the ‘meta’ modifier indicates, is a step further, it is ‘beyond’ modernity. In other words, it does not merely critique modernity, but creates something that replaces or augments it.
for - definition - metamodernity - Hanzi Freinacht (a pseudonym for Daniel Görtz and Emil Ejner Friis), - while postmodernity questions modernity, metamodernity advocates something that replaces it - comparison - postmodernity vs - metamodernity
A living systems] approach requires that the person applying this way ofthinking see what they are working on as a system of energies or life processes,rather than as things
for - noun vs verb
perceived by oneself “in here.” In this sense, the world consists of objects outthere in space (the container that holds them) before me as the perceivingsubject.
for - adjacency - Indyweb dev - natural language - timebinding - parallel vs serial processing - comparison - spoken vs written language - what's also interesting is that spoken language is timebinding, sequential and our written language descended from that, - in spite of written language existing in 2D and 3D space, it inherited sequential flow, even though it does not have to - In this sense, legacy spoken language system constrains written language to be - serial - sequential and - timebound instead of - parallel - Read any written text and you will observe that the pattern is sequential - We constrain our syntax it to "flow" sequentially in 2D space, even though there is absolutely no other reason to constrain it to do so - This also reveals another implicit rule about language, that it assumes we can only focus our attention on one aspect of reality at a time
for - natural language acquisition - Automatic Language Growth - ALG - youtube - interview - David Long - Automatic Language Growth - from - youtube - The Language School that Teaches Adults like Babies - https://hyp.is/Ls_IbCpbEfCEqEfjBlJ8hw/www.youtube.com/watch?v=984rkMbvp-w
summary - The key takeaway is that even as adults, we have retained our innate language learning skill which requires simply treating a new language as a new, novel experience that we can apprehend naturally simply by experiencing it like the way we did when we were exposed to our first, native language - We didn't know what a "language" was theoretically when we were infants, but we simply fell into the experience and played with the experiences and our primary caretakers guided us - We didn't know grammar and rules of language, we just learned innately
some people who are so uh trained in learning on purpose they have a hard time relaxing with anything that's unclear
for - intention vs relaxing - natural language acquistion
Non-NEXT_PUBLIC_ environment variables are only available in the Node.js environment, meaning they aren't accessible to the browser (the client runs in a different environment).
Theupholstery and the rugs muffle her but we can hear her clearly despite that.The tension between her lack of control and her attempt to suppress it ishorrible. It's like a fart in church.
Serena Joy's muffling cries symbolise the real comparative and biologically sinful nature of the act, that everyone else is awkwardly yet restraining to ignore. The "fart in church" really indicates a biological necessity, a response to a strict and man-made construct such as the church.
If we stopped focusing on our separateness and focused instead on ouralready-always connectedness, how might we experience separateness differently?
for - similarity - separateness vs connectedness - Deep Humanity tree metaphor - Just as the many separate branches of the tree can all be traced back to a common trunk, - similarly, all the aspects that separate one person from another can be traced back to a common affective, cognitive and linguistic basis, - otherwise, communication would be impossible
The Swiss philosopher and poet Jean Gebser provides broader terminol-ogy than Kuhn does, by describing what is happening in society as a shift inconsciousness. 20 Whereas a paradigm shift affects a particular field of study,
for - comparison - consciousness shift (Jean Gebser) vs Paradigm shift (Thomas Kuhn)
Just as themachine age transformed an economy of farm laborers and artisansinto one of combine harvesters and assembly lines, so the technology
move fast and break things
for - adjacency - Move fast and break things - progress trap - antonym of "Move fast and break things" - "Move slow and make things"
I use dashes -, for the reasons you mention above. I avoid underscores because they require using the shift key, so take at least twice as long to type (also, I think they're ugly)
With so many characters that you might not think should be special, in fact being special, I just use the special characters anyway. This also puts me in the good habits of using bash completion, where it will auto-escape all the special characters in a filename. But it also puts me in the good habits of escaping/quoting EVERYTHING in scripts and multi-part 1-liners in bash. For example, in just a simple 1-liner: for file in *.txt; do something.sh "$file"; done That way, even if one of the files has a space, or some other character, the do part of the loop will still act on it, and not miss on 2 or more file-name-parts, possibly causing unintended side-effects. Since I cannot control the space/not-space naming of EVERY file I encounter, and if I tried, it would probably break some symlinks somewhere, causing yet more unintended consequences, I just expect that all filename/directoryname could have spaces in it, and just quote/escape all variables to compensate. So, then I just use whatever characters I want (often spaces) in filenames. I even use spaces in ZFS dataset names, which I have to admit has caused a fair amount of head-scratching among the developers that write the software for the NAS I use. Sum-up: Spaces are not an invalid character, so there's no reason not to use them.
Some applications and computer scripts may not recognize spaces or will process your files differently when using spaces. A best practice is to replace spaces in file names with an underline (_) or hyphen (-).
I've noticed somethings, particularly ADB commands, use spaces to issue the next part of the command. Thus having a space would say that there's a new command. And since hyphens are actually used in some spelling, such as my last name, it's better to use underscores.
I didn't see this mentioned, but lots of software doesn't treat the underscore as a word separator (also called a "break character") these days. In other words, you can't jump to next word with Ctrl+Right-arrow or select individual words by double-clicking on them. The argument is that variable names in some programming languages like Python use snake_case, so highlighting them might require an extra Ctrl+Right-arrow. I do not necessarily like that decision, because, while being (marginally) useful in those limited domains, it makes file renaming and any other word manipulations or typesetting very cumbersome.
But one thing to remember is that if you are primarily doing python coding - and your code tree has files/directories with hyphen in them and you intend to use them as modules (do an import filename in your code), then this will cause errors as python modules cannot have hyphen in them.
Underscores are usually the convention that people use when replacing spaces, although hyphens are fine too I'd say. But since hyphens might show up in other ways such as hyphenated words, you'll have more success in preserving a name value by using underscores. For instance, if you have a file called "A picture taken in Winston-Salem, NC.jpg" and you want to convert the spaces to underscores, then you can preserve the hyphen in the name and retain its meaning.
"we [Google] don't really care about underscore versus dashes."
I must be the exception, because I use both spaces and underscores, depending on circumstances. The practical/obsessive-compulsive side of me saves all my documents using spaces. They're cleaner to read than underscores, and they look far more professional. The programmer side of me still uses underscores in files that will be accessible via the web or that need to be parsed in a program. And to complicate matters worse, I use camel case to name all my programming files. So in actuality I use 3 standards interchangeably. Both have their uses, I just choose one for clarity and one for ease of use.
Separating each of these entities with a hyphen allows you to double-click and highlight only that entity. With underscores-only, you need to enlist the painstaking process of precisely positioning your cursor at the beginning of the entity, then dragging your blue selector to the end of the entity.
Si ves una jerigonza es debido a algún problema de visualización con símbolos no romanos/latinos, normalmente causado por las fuentes que tienes instaladas en tu Sistema Operativo y la interacción de las mismas con un sistema Pharo/GT.
Este comentario es a modo de inquietud: Por ejemplo, cuando ejecuto el código y navego por las diferentes pestañas a la derecha del GT ¿Cómo puedo identificar que la información allí consignada corresponde a la instrucción de ejecución del código y no a un error por incompatibilidades con el estema operativo o a fallos del programa o a corrupción de la información? Teniendo en cuenta que, en este caso, no somos expertos en escritura e interpretación de códigos.
$A.
Para poder distinguir letras de variables es que se usa el signo $ que las precede.
Why not a library? We've found it extremely hard to develop a library that: Supports the many database libraries, ORMs, frameworks, runtimes, and deployment options available in the ecosystem. Provides enough flexibility for the majority of use cases. Does not add significant complexity to projects.
Lucia is now a learning resource on implementing auth from scratch.
Lucia, the authentication library that we are using, is deprecated (Q1/2025). However, the author of Lucia decided to make it a learning resource, because Lucia is just a thin wrapper around cryptographic libraries like Oslo. So we are following the migration path on their website and will also use Oslo instead of Lucia.
he Web, sadly, defaults to 8 spaces which is an abomination for every snippet of code that would ike to be instantly readable on Mobile Phones too browsers don't provide a tab size setting anywhere (last time I've checked) to override that horrifying 8 spaces legacy nobody wants or need since tabs were invented
a later comment shows this is incorrect; we have CSS tab-size
I was pretty anti-tabs for the longest time, until I heard the best argument for them, accessibility. Tabs exist for indentation customization, and this is exactly what is needed for people with impaired sight. IMO, this is a pretty good argument for moving towards tabs.
Auth shouldn't be a paid service!
I assume this is referring to services like Auth0 where people out-source authentication instead of keeping it directly part of your own code base
The goal of Lucia v3 was to be the easiest and cleanest way to implement database-backed sessions in your projects. It didn't have to be a library. I just assumed that a library will be the answer. But I ultimately came to conclusion that my assumption was wrong. I don't see this change as me abandoning the project. In fact, I think it's a step forward. If implementing sessions wasn't easy, I wouldn't be deprecating the package. But why wouldn't a library be the answer? It seems like a such an obvious answer. One word - database. I talked about how database adapters were a significant complexity tax to the library. I think a lot of people interpreted that as maintenance burden on myself. That's not wrong, but the bigger issue is how the adapters limit the API. Adapters always felt like a black box to me as both an end user and a maintainer. It's very hard to design something clean around it and makes everything clunky and fragile, especially when you need to deal with TypeScript shenanigans.
Aligning Profit and Purpose
for - program event selection - 2025 - April 3 - 10:30am-12pm GMT - Skoll World Forum - Aligning Profit and Purpose - new portmanteau - greentruthing - opposite of greenwashing - Stop Reset Go - Deep Humanity - TPF - LCE - Greentruthing vs greenwashing - relevant to
I’ve met a number of important people through GRC who have become central to my own project ecosystem.
for - join together vs join us - example - join together AND join us - instead of join together OR join us
Why Regenerative instead of Sustainable?
for - comparison - graphic - regeneration vs sustainability
The Nonwriter's Guide to Writing A Lot by [[James Horton]]
Horton describes writing as a top down process rather than a bottom up one, but tries to frame it in a bottom up one. No wonder people have issues with writing, especially non-fiction stuff. Too many different processes going on all at once in too many directions.
LPG edges/connections can have types and attributes (properties as the name suggests) natively, making the LPG data structure more dense, compact, and informative compared to RDF.
There are two camps of Graph database, one side is RDF, where they are strict with their format, and somewhat limited for their extensibility. The other side is LPG, where they can define labels to the relationships.
bias: towards property graph / LPG
There is an ongoing debate about which graph data model is best, and in this blog post, we’ll explore why RDF (Resource Description Framework) stands out as the superior choice for building more sustainable and scalable knowledge graphs over LPG (Labeled Property Graphs).
At the heart of current societal crises is the Western addiction to a certain worldview of globalism that stands in opposition to the global solidarity, or internationalism, that flows from common-good or pluriversal worldviews.
for - globalism vs global solidarity
Reply to Hajo Bakker on LinkedIn
Hajo Bakker Exam vs. Test -- Een examinering moet veel vanafwegen en niet regulier gebeuren.
Een test (toets) mag vaker gebeuren, en moet weinig vanaf hangen... Geen ouders die straffen voor een laag cijfer (of cijfers afschaffen), geen adviezen die daarvanafhangen, etc.
Het doel van een toets is om je aan te geven wat je krachten en minder sterke punten zijn, dus waar je je op moet focussen met toekomst leren. Dit kan alleen op het moment dat je een toets nabespreekt en op individueel niveau. Klassikaal bespreken heeft vaak weinig nut.
Daarbij komt ook dat een student moet snappen WAAROM het helpt om na te bespreken, de wetenschap erachter. Op het moment dat je de waarom achter het hoe niet goed snapt heeft het hoe minder effect. (dit is waarom in het 4C/ID model ze in een scaffold beginnen met de laatste stap, waarin de informatie van voorgaande stappen is gegeven. Dit zodat als je de vorige stap gaat leren, je een beter idee hebt waar het uiteindelijk voor gebruikt gaat worden en je er dus een betere invulling aan kan geven.)
Semantische verschillen zijn vaak uiterst nuttig om complexe stof te begrijpen. Op het moment dat ze exact hetzelfde waren heeft het weinig nut om meerdere termen te hebben en zouden ze synoniem zijn.
"Exam" is geen synoniem van "test".
Genuanceerde verschillen zijn vaak nuttiger dan "umbrella terms" om goed te communiceren, als uiterst subliem wordt beargumenteerd in "Science of Memory: Concepts" van Roediger III et al.
Daarnaast komt uiteraard bij kijken dat neurocognitieve wetenschap een blauwdruk geeft voor hoe onze brein architectuur in elkaar zit (zie bijvoorbeeld John Sweller, Cognitive Load Theory 2011, en The Forgetting Machine, Rodrigo Quian Quiroga, 2017, Science of Memory: Concepts, Roediger et al., 2007, Ten Steps to Complex Learning, van Merriënboer, 2017).
Dit is universeel toepasbaar, afgezien van mensen met een cognitieve aandoening bijvoorbeeld, dit gaat dus over neurotypische breinen.
Leerstijlen zijn een mythe, wel hebben wij leervoorkeuren, maar door alleen in onze leervoorkeur te leren missen wij bepaalde informatie die cruciaal kan zijn voor beter begrip en meesterschap (mastery).
Beter is het om studietechnieken te gebruiken die overeenkomen met brein-architectuur en die onder te knie te krijgen.
Meer cognitieve belasting te gebruiken (zonder cognitieve overbelasting te veroorzaken). Als leren "makkelijk" voelt is het over het algemeen niet uitdagend genoeg en/of de techniek niet nuttig. Herlezen / samenvatten is simpel maar vrij inefficiënt. Het maken van een GRINDEmap voelt moeilijk maar is vele malen effectiever (zie ook the misinterpreted effort hypothesis).
Zoals Dr. Ahrens al zei: "The one who does the effort, does the learning."
Verder heb ik een heleboel ideëen voor een optimaal onderwijs dat zich aanpast aan het individu in plaats van aan het systeem, maar dit is een te complex en groot onderwerp om zo even hier neer te zetten.
Why do we need “individual action” (now more than ever) when what we REALLY need is “systems change?”
for - post - LinkedIn - individual change vs system change - Deep Humanity individual / collective gestalt and climate action
comment - individual / collective gestalt would be helpful framing to sort out this confusion
overall the destruction of Native American cultures was the destruction of collectivism or the idea that Community is more important than the individual in a collectivist Society resources are typically owned by society as a whole or collectively collectivism went against the anglo-american tradition of individualism or the idea that the individual is more important than the community
for - native american genocide - anglo-american individualism replaced indigenous collectivism - comparison - individualism vs collectivism - youtube - cultural genocide of native americans
summary - This is a very informative summary of the European settler induced genocide of United States Native Americans
Reply to Gertina Blanket on LinkedIn:
Jij legt in één klap uit datgene wat ik nooit goed heb begrepen uit de literatuur... Het verschil tussen interleaving en varied practice (die vaak als hetzelfde worden gebruikt in de "volksmond").
Het een gaat over verschillende hoeken kijken naar hetzelfde idee (varied practice) terwijl het ander gaat over verschillende maar soortgelijke ideëen (interleaving), bijvoorbeeld meerdere soorten wiskunde (algebra, trigonometrie, etc.).
Hierbij wil ik uiteraard wel zeggen dat blocked practice niet per se direct toegepast moet worden als het over automatisering gaat -- de cognitieve schemata moeten eerst goed gevormd zijn. Zie ook 4C/ID (Ten Steps to Complex Learning). Ofwel, eerst goede encoding + retrieval (Spaced Interleaved Retrieval, mindmapping, etc.) en dan focus op "drilling" / knowledge fluency.
Het sneller maken / automatiseren heeft geen enkel nut als het begrip er nog niet goed in zit. Dit moet geverifiëerd worden.
Kennis is natuurlijk ook erg interdisciplinair. Ik wordt er extreem blij van als ik een link leg tussen een boek over filosofie en efficiënt leren/onderwijs bijvoorbeeld.
Zo las ik ooit een boek over romeinse oratoren met een misleidende titel "How to Win an Argument" van Marcus Tullius Cicero, vertaald door James M. May, en hierin kwam ik tegen dat de oude Romeinen al door hadden dat LOGICA is wat het brein doet onthouden, en dit hoeft dus geen objective logica te zijn maar meer een correcte reflectie van hoe je eigen geest werkt en verbanden legt.
Dit is direct in lijn met wat ik weet van cognitieve leerpsychologie en mijn klein beetje kennis van neurowetenschap (waar ik dit jaar dieper in wil duiken).
Informatie in isolatie is nooit stevig, het moet zich vastklampen aan ankers en andere kennis (voorkennis eventueel), en de lerende (niet de onderwijzende) moet actief bezig zijn om deze verbanden te leggen.
Zoals ik wel vaker quote van Dr. Sönke Ahrens: "The one who does the effort does the learning."
Als ik een boek lees denk ik automatisch aan hoe ik dit kan relateren aan wat al in mijn second mind (Zettelkasten) zit. Ik denk niet meer linear, alleen maar non-linear. Standaard in verbanden.
Hier wat bronnen (impliciet) genoemd: - Cicero, M. T. (2016). How to win an argument: An ancient guide to the art of persuasion (J. M. May, Trans.). Princeton University Press. - Ahrens, S. (2017). How to take smart notes: One simple technique to boost writing, learning and thinking: for students, academics and nonfiction book writers. CreateSpace. - fast, sascha. (100 C.E., 45:02). English Translation of All Notes on Zettelkasten by Luhmann. Zettelkasten Method. https://zettelkasten.de/posts/luhmanns-zettel-translated/ - Luhmann, N. (1981a). Communicating with Slip Boxes (M. Kuehn, Trans.). 11. - Luhmann, N. (1981b). Kommunikation mit Zettelkästen. In H. Baier, H. M. Kepplinger, & K. Reumann (Eds.), Öffentliche Meinung und sozialer Wandel / Public Opinion and Social Change (pp. 222–228). VS Verlag für Sozialwissenschaften. https://doi.org/10.1007/978-3-322-87749-9_19 - Moeller, H.-G. (2012). The radical Luhmann. Columbia University Press. - Scheper, S. (2022). Antinet Zettelkasten: A Knowledge System That Will Turn You Into a Prolific Reader, Researcher and Writer. Greenlamp, LLC.
It is the fixed nature of caste that distinguishes it from class,a term to which it is often compared. Class is an altogether sepa-rate measure of one’s standing in a society, marked by level ofeducation, income, and occupation, as well as the attendant char-acteristics, such as accent, taste, and manners, that flow from so-cioeconomic status. These can be acquired through hard work andingenuity or lost through poor decisions or calamity. If you can actyour way out of it, then it is class, not caste. Through the years,wealth and class may have insulated some people born to the sub-ordinate caste in America but not protected them from humiliat-ing attempts to put them in their place or to remind them of theircaste position.
Bhimrao Ambedkar came to theUnited States to study economics as a graduate student at Colum-bia, focused on the differences between race, caste, and class.
Look into Ambedkar's writings on race, caste, and class.
losing synaptic density they're losing synapsis they're not brain cells
> for - addiction - graph - years of use vs loss of synaptic connections
By contrast, most modern web frameworks were designed for building web applications. These frameworks excel at building more complex, application-like experiences in the browser: logged-in admin dashboards, inboxes, social networks, todo lists, and even native-like applications like Figma and Ping. However with that complexity, they can struggle to provide great performance when delivering your content.
Most companies where I worked have a history of rebuilding their applications every 3 to 5 years, some even 2 years. This has extremely high costs, it has a major impact on how successful the application is, and therefore how successful the company is, besides being extremely frustrating for developers to work with a messy code base, and making them want to leave the company. A serious company, with a long-term vision, cannot afford any of it, not the financial loss, not the time loss, not the reputation loss, not the client loss, not the talent loss.
The new narrative of Silicon Valley is called Longterminism
for - silicon valley - latest religion - longterminism
comment - Interesting that in sustainability, shortermism of the market is seen as a handicap to addressing the polycrisis
There was a lot of conversation at the time around a leaderless movement. But I know at least in the activist scene in New York, what we talked about was building leader-full movements, about the idea that we don't want to step away from power, but instead, as people with a vision for the future of America, we want to step into power.
for - occupy - leaderless vs leader-full movement
for - from - search - Google - etymology intention - https://hyp.is/O_UfRN-4Ee-f4h-9EXrI_g/www.google.com/search?q=intention+etymology&oq=intention+etymology&gs_lcrp=EgZjaHJvbWUyBggAEEUYOTIGCAEQLhhA0gEIMzkxNmowajmoAgCwAgE&sourceid=chrome&ie=UTF-8 - question - intention and stretching out
comment - from Latin intentionem (nominative intentio) "a stretching out, straining, exertion, effort; attention," noun of action from intendere "to turn one's attention," literally "to stretch out" - I'm not sure that - the "stretching towards" of attention and - the "stretching out" of intention - conveys a clear relationship between them - I understand the "stretching towards" of attention but don't get the sense of "stretching out" as it applies to intention - I think of energy and purpose but stretching out doesn't seem aligned to it
question - intention - as stretching out - I don't understand how intention can be described as stretching out. I understand it as having a goal or purpose - Stretching out is perhaps alluding to a FUTURE action - to get hold of something you don't presently have so you are stretching out - Perhaps more of a literal hand movement - stretching out your hand to get something you don't currently have - whereas stretching towards is alluding more to something in the present, although it seems they can both be used interchangeably for reaching for an object not currently in your possession: - the baby stretched his hand towards the apple - the baby stretched out his hands to grasp the apple
EP® DEsignation Become an Environmental Professional (EP®) Increase your influence and safeguard stakeholder trust by earning the only nationally recognized designation for environmental practitioners. Take Eligibility Quiz
Great Colour Contrast: Eco Canada uses good colour contrast, making text readable even for users with low vision or colour blindness. This ensures that foreground content (black/green) stands out clearly against the (white) background, improving accessibility for all users. The bolded headings as well as pop of colour for links is also a good distinction that's easy to navigate.
for - visualization - internet routing - IPv4 vs IPv6 - to 2023 - The Opte Project
NO! You didn't get me because (changes Framing to another Framed and draws another arrow outside the bigger box, connecting to it) what's outside here still is… what is framing that? You cannot have this… You can't have it as a focal object. It is mysterious. It is phenomenologically mysterious. James pointed to this in a wonderful distinction between the I and the Me (I: Me).
for - adjacency - I-me relationship - William James - subject-object dualism - experience vs conceptualisation of experience - finger pointing to the moon - subject / I am phenomenologically mysterious - Indyweb annotation vs Innotation - object-of-study focal shift - definition - potential vs kinetic adjacencies
adjacency - between - I-me relationship - William James - subject-object dualism - the eye cannot see itself - self consciousness - experience vs conceptualisation of experience - Indyweb annotation vs Innotation - object-of-study focal shift - definition potential adjacencies - definition kinetic adjacencies - adjacency relationship - William James's I-me relationship is about the paradox of self consciousness - modern humans distinguish themselves through excelling in cognitive abilities - but what happens when we turn this cognitive abilities onto ourselves? - Self consciousness is what results - reasoning about the reasoner - Just as the eye cannot truly see itself, the reasoner who reasons about him/her self cannot really do so because the "I" is NOT really the same as the "me" - the subject is not the object, - the act of framing is not the frame - the qualia is NOT the same as the idea that represents the qualia - the moon is not the finger pointing to the moon - hence the I, the act of framing the subject is phenomenologically mysterious - In contrast, in indyweb, we can replace annotation with Innotation, an inline version of annotation - This is because of the recursive nature of learning of ideas - When we digest an idea, that has an externalised (re)presentation, and it triggers the emergence of a new idea, - We can capture the newly inspired idea a an inline Innotation instead of a side bar annotation. - The reason why we would do this is because this is more homeomorphic to how knowledge context switches its role - from an active new insight - to an existing cultural artefact / object that can be digested by another mind - The difference is the idea - as a spontaneous emergent, embodied, enactive real-time , LIVING experience, which then becomes, post experience, an idea that is - a DEAD cultural artefact that is ready to be digested and potentially evoke a new strong LIVING response in another consciousness - The idea as a linguistically constructed cultural artefact is DEAD - until it interacts with another consciousness, - and at such time, the cultural artefact can deliver upon itz intended promise and potential, and trigger a LIVING learned experience. - Innotation converts the once LIVING experience of the idea at the moment of birth / Inception to the form of existing, timebound knowledge test to do the same in the future, when new minds may stumble upon it - Learning from linguistic cultural artefacts is thus - the act of conversion of - potential adjacencies into - kinetic adjacencies
In response, Yampolskiy told Business Insider he thought Musk was "a bit too conservative" in his guesstimate and that we should abandon development of the technology now because it would be near impossible to control AI once it becomes more advanced.
for - suggestion- debate between AI safety researcher Roman Yampolskiy and Musk and founders of AI - difference - business leaders vs pure researchers // - Comment - Business leaders are mainly driven by profit so already have a bias going into a debate with a researcher who is neutral and has no declared business interest
//
there still seems to be a little bit of Gap in data that doesn't account for 0.2 de celsus warming that is present extra scientists have not been able to comfortably explain over the past in fact several years why there is this little bit of extra global warming it is a major major Gap
for - stats - climate crisis - global mean temperature gap in models vs measurement of - 0.2 Deg C - from The Print - YouTube - Low clouds disappearing over earth, rapidly acceleration heating - 2024, Dec
we can see more specific changes in the brain through training the Mind than through any drug that you can take more specific changes uh when you take a medication like an an SSRI an anti-depressant or an anti psychotic it's like blasting the brain uh in in its entire uh and so it's a very general effect we can see a much more specific effect with mind training
for - wellbeing - mental illness - drug treatment vs brain changes from mindfulness practices - adjacency - Youtube - Tukdam talk - An Overview Of CHM’s Work On “Well-Being And Tukdam” - Prof. Richard J. Davidson
we use well-being rather than happiness because the idea is isn't really to be happy all the time
for - quote - comparison - wellbeing vs happiness - Richard J. Davidson - The idea isn't really to be happy all the time. - If a sad event or something tragic occurred, it would not be appropriate to be happy in that moment - At that moment, it's possible to be sad and have very high levels of wellbeing. That's why we prefer the term wellbeing. - Another term that we also use is "flourishing"
in Vermont, Native Americans lived here—well, like everywhere in North America—they lived here in Vermont for over ten thousand years. The ecosystem was basically intact, and that’s because they had that ethical system built into their fundamental cultural assumptions—the assumptions that guided their lives. They didn’t think about them. They didn’t question them. They were simply the assumptions, the unthought assumptions.
for - philosophy matters! - biodiversity crisis - 10,000 years of preservation vs 100 years of clearcut - David Hinton - comparison - polycrisis - climate crisis - two unthought assumptions - philosophical differences - Indigenous people of Vermont vs European settlers - from - Emergence Magazine - interview - An Ethics of Wild Mind - David Hinton
comparison - polycrisis - climate crisis - biodiversity crisis - Indigneous people of Vermont - vs European settlers - unthought assumptions - unthought assumptions of Indigenous people took care of forests for 10,000 years - unthought assumptions of European settlers clear cut all the forests in 100 years - These are philosophical differences - PHILOSOPHY MATTERS!
The assassination is a koan that brings to light the paradox at the heart of civilisation: what’s real is our experience of being alive, not how we can be quantified, but we pretend the opposite is true.
for - comparison - symbolosphere vs physiosphere - assassination of United Healthcare CEO Brian Thompson - Substack article - Best Served Cold: Luigi Mangione and The Age of Breach - Alexander Beiner
I feel like sharing with you some of my observations as a frame analyst, as someone who analyzes semantic frames and how they structure a discourse to, in this case, to disempower us and keep us embedded within a conversation that is primarily about the actions of corporations and nation-states and that disengages us from direct grassroots action and taking power into our own hands
for - adjacency / validation - for justifying Tipping Point Festival - TPF - bottom up, grassroots direct action Vs - top down, corporate, policy action - Joe Brewer - framing analysis - using cognitive linguistics
adjacency / validation - between - ustifying Tipping Point Festival - TPF - - bottom up, grassroots direct action<br /> - top down, corporate, policy action<br /> - Joe Brewer - framing analysis - cognitive linguistics - adjacency relationship - We need both bottom up and top down section, but Joe's framing analysis provides an explanation why there isn't more bottom up direct action - It requires a lot of skill to find the leverage points as well as the weakness of people power is lack of money - To awaken the sleeping giant off the commons is the purpose of the Typing Point Festival (TPF)
for - climate model - gaps - from - post - LinkedIn - Reality vs Climate Models - Kasper Benjamin Reimer BjørkskovKasper Benjamin Reimer Bjørkskov
from - post - Linked In - Reality vs Climate Models - Kasper Benjamin Reimer BjørkskovKasper Benjamin Reimer Bjørkskov - https://hyp.is/Dc_w8rM2Ee-I0VO9JwZKNg/www.linkedin.com/feed/update/urn:li:activity:7270232384455720960/?commentUrn=urn:li:comment:(activity:7270232384455720960,7270500962702655489)&dashCommentUrn=urn:li:fsd_comment:(7270500962702655489,urn:li:activity:7270232384455720960)
The difference between what you work out using the Zettelkasten and the memory palace technique is that the memory palace is a pure memory technique. It uses meaningless connections and the way the brain works to gain access to information. For example, if I mentally write the date Rome was founded with the mnemonic “BC 753 Rome came to be” as a number on an egg in the kitchen fridge, the only reason for this link between the egg in the kitchen fridge of my memory palace and the year Rome was founded is that I can remember this number. You make yourself aware of what the brain otherwise does unconsciously.
The difference between what you work out using the Zettelkasten and the memory palace technique is that the memory palace is a pure memory technique. It uses meaningless connections [emphasis added] and the way the brain works to gain access to information. For example, if I mentally write the date Rome was founded with the mnemonic “BC 753 Rome came to be” as a number on an egg in the kitchen fridge, the only reason for this link between the egg in the kitchen fridge of my memory palace and the year Rome was founded is that I can remember this number.
Certainly not an attack against him, but I feel as if Sascha is making an analogistic reference to areas of mnemonics he's heard about, but hasn't actively practiced. As a result, some may come away with a misunderstanding of these practices. Even worse, they may be dissuaded from combining a more specific set of mnemonic practices with their zettelkasten practice which can provide them with even stronger memories of the ideas hiding within their zettelkasten.
There is a mistaken conflation of two different mnemonic techniques being described here. The memory palace portion associates information with well known locations which leverages our brains' ability to more easily remember places and things in them with relation to each other. There is nothing of meaningless connections here. The method works precisely because meaning is created and attributed to the association. It becomes a thing in a specific well known place to the user which provides the necessary association for our memory.
The second mnemonic technique at play is the separate, unmentioned, and misconstrued Major System (or possibly the related Person-Action-Object method) which associates the number with a visualizable object. While there is a seeming meaningless connection here, the underlying connection is all about meaning by design. The number is "translated" from something harder to remember into an object which is far easier to remember. This initial translation is more direct than one from a word in one language to another because it can be logically generated every time and thus gives a specific meaning to an otherwise more-difficult-to-remember number. As part of the practice this object is then given additional attributes (size, smell, taste, touch, etc., or ridiculous proportion or attributes like extreme violence or relationships to sex) which serve to make it even more memorable. Sascha seems break this more standard mnemonic practice by simply writing his number on the egg in the refrigerator rather than associate 753 with a more memorable object like a "golem" which might be incubating inside of my precious egg. As a result, the egg and 753 association IS meaningless to him, and I would posit will be incredibly more difficult for him to remember tomorrow much less next month. If we make the translation of 753 more visible in Sascha's process, we're more likely to see the meaning and the benefit of the mnemonic. (I can only guess that Sascha doesn't practice these techniques, so won't fault him for missing some steps, particularly given the ways in which the memory palace is viewed in the zeitgeist.)
To say that the number and the golem (here, the object which 753 was translated to—the Major System mnemonic portion) have no association is akin to saying that "zettlekasten" has no associated meaning to the words "slip box." In both translations the words/numbers are exactly the same thing. The second mnemonic is associating the golem to the egg in the refrigerator (the memory palace portion). I suspect that if you've been following along and imagining Andy Serkis gestating inside of an egg to become Golem who will go on to fight in the Roman Coliseum in your refrigerator, you're going to see Golem every time you reach for an egg in your refrigerator. Now if you've spent the ten minutes to learn the Major System to do the reverse translation, you'll think about the founding date of Rome every time you go to make an omelette. And if you haven't, then you'll just imagine the most pitiful gladiator loosing in the arena against a vicious tiger.
Naturally one can associate all their thoughts in their ZK to both the associated numbers and their home, work, or neighborhood environments so that they can mentally take their (analog or digital) zettlekasten with them anywhere they go. This is akin to what Thomas Aquinus and Raymond Llull were doing with their "knowledge management systems", though theirs may have had slightly simpler forms. Llull actually created a system which allowed him to more easily meditate on his stored memories and juxtapose them to create new ideas.
For the beginners in these areas who'd like to know more, I recommend the following as a good starting place: <br /> Kelly, Lynne. Memory Craft: Improve Your Memory Using the Most Powerful Methods from around the World. Pegasus Books, 2019.
oncewe reduce the climate forcing enough that Earth’s energy imbalance becomes slightlynegative, feedbacks will work in the opposite sense, helping us move global temperature andclimate patterns back toward their condition before human alterations of the planet began
for - climate crisis - planetary tipping points - irreversible? - Hansen disagrees - part 2 - climate crisis - comparison - planetary tipping points - Hansen vs Rockstrom
climate crisis - comparison - planetary tipping points - Hansen vs Rockstrom - Hansen makes a valid point. What Rockstrom might consider irreversible, although he doesn't explicitly say, but implies, Hansen speaks instead in more precise terms - The perspectives may be dependent on the knowledge that informs each scientist - Hansen's research into the unknown area of climate change, aeresols and cloud cover, is not considered in conventional knowledge that IPCC bases its conclusions on since it is unknown - Hansen's research uncovers that aeresols play a very large role, to such an extent that humans may be able to mitigate exceeding dangerous temperature thresholds pragmatically through aeresol interventions that impact cloud behavior -
for - climate crisis - article - Global Warming Acceleration: Hope vs Hopium - Jim Hansen et al., 2024, Mar 29
reply to u/SupItsBuck88 at https://old.reddit.com/r/Zettelkasten/comments/1h0vuek/zettelkasten_vs_commonplace_book/ on Zettelkasten vs Commonplace Book
Don't tell anyone as it's a well-kept secret, but the way most digital practitioners (especially in Obsidian) arrange their "zettelkasten" is generally closer to commonplace book practice than it is to that of Niklas Luhmann's particular practice of zettelkasten. Honestly outside of Luhmann's practice (and those who follow his example more closely) really all zettelkasten into the late 1900s were commonplace books written on index cards rather than into books or notebooks. It's certainly the case that as the practices got older, commonplaces morphed from storehouses of only sententiae to more focused databases and tools for thought, particularly after the works on historical method done by Ernst Bernheim and later by Charles Seignobos & Charles Victor Langlois in the late 1800s and early 1900s.
More modern variations and versions in English can be seen in:
See also:
Generally, the more focused your needs for particular types of information and the higher need of specific outputs may drive one to adopt one form over another. At the end of the day, I would contend that the specific affordances for how each of these forms work for the vast majority of people are exactly the same. This is especially true if one is using digital methods. In practice, I find that a lot of the difference between the practices comes down to where the user wishes to put in their work: either upfront (Luhmann-artig zettelkasten) or down the road in a more laissez faire manner (commonplace book or "traditional" zettelkasten). As a result, I always recommend people experiment a bit and settle on the method(s) which is (are) more motivating and useful for their modes and styles of work. Everyone's needs, inputs, and outputs will differ, and, as a result, so will their methods.
SI system is absolute (gravitationally independent) as: Mass - in relation with Planck constant Time - in terms of vibration of isotope of Cesium Length - in terms of distance covered by Light All of which are independent of effect of gravity
the ‘harmony’ model of Mesopotamia and the East Eurasian empires, and the conflict model which started in Greece and determined the logic of the Western model.
for - further research - Harmony model of East Eurasia vs Conflict model of Greece
I would say the epigenetic inheritance that has to occur there and how it occurs must be contributing a very large fraction indeed to the differentiation process
for - answer - Denis Noble - to Michael Levin - question - What percentage of genetic vs non-genetic information passed down to germ line from embryogenesis onwards ? - a very large fraction is epigenetic inheritance indeed.
what percentage of the information that is used by an organism let's say embryogenesis onwards is genetic versus all other sources put together what what what would you guess as a as a breakdown
for - question - Michael Levin to - Denis Noble - percentage of genetic vs non-genetic information passed down to germ line from embryogenesis onwards
Prof. Smith lives in London and has a brother in Berlin, Dr. Smith. To visit him, balancing time, cost, and carbon emissions is a tough call to make. But there is another problem. Dr. Smith has no brother in London. How can that be?
for - BEing journey - example - demonstrates system 1 vs system 2 thinking - example - unconscious bias - example - symbolic incompleteness
This is who we are: the richest country on earth, with more poverty thanany other advanced democracy.
the point is that this is a collective problem that can only be solved collectively. And clearly there is no collective, even worse
for - post comment - LinkedIn - polarization - Trump 2024 win - lack of collective - adjacency - Deep Humanity - deep time, species-wide singularity - conservativism vs progressiveness - progress - political polarization - progress trap
adjacency between - Trump 2024 win - Deep Humanity - anthropocene as deep time species-wide singularity - progress traps reaching a climax - conservatism vs progressiveness - adjacency relationship - This fits into a Deep Humanity explanation: - We are moving through a deep time, species singularity in which - once isolated pockets of cultural seeking and interpretative systems for explaining reality have been rapidly mashed-up via: - communication and - transportation technology - There is a singularity now where two forces are battling each other: - conservative that values old traditional cultural values and norms and - progressive that values the future possibilities - There are different cultural flavors of this. Whether it is - political polarization that pits authoritarian vs democratic ideologies or - climate change that pits traditional fossil fuel systems vs new renewable energy systems - the way we've always done things is in conflict with new ways of doing things through natural human evolutionary change - progress - In fact, we can look at the deep time, species-wide singularity that is now happening across all fields in the anthropocene as a predictable progress trap arising from progress itself
Zettelkasten Numbering is so Damn Confusing (I Think I Can Help) by [[Zettelkasten Blah Blah Blah]]
He doesn't say it explicitly, but the Luhmann-artig zettelkasten numbers are only addresses. They don't represent hierarchies. Doing this allows a bottom up organization to emerge.
You can later create hub notes or outlines that create a "correct" or hierarchical order. This is where things become top down.
He points out that Scheper's recommendations for using the numbering for academic disciplines and putting cards in specific orders (giving them negative numbers, etc.) is a counter-productive habit with respect to Luhmann-artig practice.
this can happen before as a as momentary State like we can have Peak experiences but now what we're talking about here is this is where it becomes a trait
for - comparison - temporary conscious state vs permanent psychological trait - John Churchill
first we've got to understand the difference between actual psychological infrastructure please and states of Consciousness so because for for our listeners states are cheap traits are expensive
for - definition - psychological infrastructure - John Churchill - definition - state of consciousness - John Churchill - comparison - psychological infrastructure vs state of consciousness - John Churchill - quote - states (of consciousness) are cheap, traits ( of psychological infrastructure) are expensive - John Churchill
Class 2, Does Memory Matter? Why Are Universities Studying Slavery and Their Pasts? by David Blight for [[YaleCourses]]
dormant implies something deeper than sleep, like turning off a computer or going into hibernation. Insects go dormant over the winter, and a television is dormant when it is turned off. Dormant also has the subtext of waiting. Those insects are dormant waiting for the spring.Asleep is just the normal act of sleeping
New Atheism advocates the view that superstition, religion, and irrationalism should not be tolerated. Instead, they advocate the antitheist view that the various forms of theism should be criticised, countered, examined, and challenged by rational argument, especially when they exert strong influence on the broader society, such as in government, education, and politics.[3][4]
Some linguists would argue that there’s no point fighting against slips like that—that language is forever unfixed and deviations should simply be observed and even appreciated—or that it’s silliness to tell people to follow rules that are as arbitrary as the meaning assigned to a certain jumble of letters. But Garner is not one of them.
Freedom of course always comes at a cost: what constitutes a victory for personal rights and freedom of speech also facilitates the spread of illegal messages, since decentralized networks make it harder to control what information is exchanged. Legality is of course a tricky matter, as some countries instate laws that prevent their citizens from voicing opinions that would be legal elsewhere.
25:00 Why attend an art history class then when you are so sensitive of images being depicted (decent argument)? 27:00 cancel culture at college campuses (evolution being taught creationist becoming mad example) 29:25 Tension between intellectual discomfort and harm (notion of safe spaces as being a problem). 31:00 Illiberal left as sketching good vs evil and claiming moral superoprity. Here, leftist claim to be inclusive, but in fact, they are exclusive .
before after (current behavior) after (expected behavior)
The research finds
for - stats - green growth - 2024 - Global South vs Global North
stats - green growth - 2024 - Global South has - 60% of world population - 20% of fossil fuel production - fossil fuel production in decline - 70% of global renewable resource potential - In 2024, 87% of capex of electricity generation is renewable - From 2019 to 2024, renewable energy has grown 23% annually and now supplies 9% of its electricity - 17% of Global South has already overtaken Global North in % of renewable electricty generation
for - Report - Powering Up the Global South - Rocky Mountain Institute - RMI - 2024 - Vikram Singh - Kingsmill Bond
Summary - This report shows that the Global South is adopting cleantech faster than the Global North
when putting thoughts into words. Words that remain in our head are freeto exist independent of how they’re used by other people.
On one level, the reason is obvious: accountability. There’s a lot at stake...
except somehow for Donald J. Trump and some in identity politics...
How do they get around it? system 1 vs system 2
Engagingwith the slip box should feel exciting, not anxiety-producing.
I often find that people who discuss "workflows" and the idea of "processing" their notes are the ones who are falling trap to the anxiety-producing side of the work.
BD should have found more exciting words for "processing" which he uses two more times in the next paragraph.
This relates to Luhmann's quote about only doing what is easy/fun/flow:<br /> - https://hypothes.is/a/TQyC1q1HEe2J9fOtlKPXmA<br /> - https://hypothes.is/a/EyKrfK1WEe2RpEuwUuFA7A
Compare: - being trapped in the box: https://hypothes.is/a/AY7ABO0qEeympasqOZHoMQ - idea of drudgery in the phrase "word processing"
I was continually pushing out the documents to those interested