The social media platform X (Twitter), claimed that there were record breaking traffic numbers for the 2024 super bowl game. However, with further cybersecurity research they found that 75% of the traffic X had posted about was fake and other social media platforms showed much lower rates. CHEQ's data had also shown that 32% of X's visitors were bots. Elon Musk now faces advertisement concerns over recent comments and poses as future challenges.
- Jan 2025
-
social-media-ethics-automation.github.io social-media-ethics-automation.github.io
-
docdrop.org docdrop.org
-
The order built on the basis of the Leader-Arbiter mechanism leads to the personification ofpower. This mechanism of rule has made it easier to carry out market reforms and to resolveconflicts between influential groups. At the same time, however, it has become a seriousobstacle to developing solid democratic institutions and transparent politics, leading to theformation of networks of informal ties and “shadow rules of the game” rather than a politicalsystem based on clear rules and the separation of powers
The leader-arbiter mechanism in Russia helped with the reforms but hindered how democratic institutions could develop. Relying on "shadow rules" led to informal networks rather than policy. This undermined democratic progress and instead enforced authoritarian practices. This segment tells us that political reform was difficult but for a number of reasons. One of which is the informal networking but another was the internal divisions that this caused within the elite.
-
-
www.nytimes.com www.nytimes.com
-
The artist strives not to collect the most toys, rack up virtual kills or race to the jackpot square but simply to be in the game, map its corners, make time stretch — and maybe figure out a way to hack this world, change the rules and free us all. For victory is just a blip. The best games never end.
Finding out everything about the world... no thats not right. The artist makes art in order to understand their own exsisatnce, not to rack up points. Maybe i should follow this way. This clever analogy from C. Thu Nguyen.
-
-
social-media-ethics-automation.github.io social-media-ethics-automation.github.io
-
On the other hand, some bots are made with the intention of harming, countering, or deceiving others. For example, people use bots to spam advertisements at people. You can use bots as a way of buying fake followers [c8], or making fake crowds that appear to support a cause (called Astroturfing [c9]). As one example, in 2016, Rian Johnson, who was in the middle of directing Star Wars: The Last Jedi, got bombarded by tweets that all originated in Russia (likely making at least some use of bots).
I've had my experiences with antagonistic bots. In high school, a few of my friends would use Kahoot bots to overflow the number of students who joined the Kahoot game. There was this website where you would give the Kahoot game code and the bots would join by themselves.
-
-
www.dreamco.com www.dreamco.com
-
the gamestate—a collection of all relevant virtual information that may change during play
game state
-
MDA: Using the mechanics-dynamics-aesthetics model of game development, design-ers create aesthetic models for various types of gameplay. Aesthetics don’t refer to thelooks of the game but rather the emotional response the designer and developmentteam hope to evoke in the players through the game dynamics. If mechanics are therules and dynamics are the play of the game, then aesthetics are typically the fun (orlack thereof) experienced by playing. Designers ask themselves which aesthetic theyhope to achieve, define the dynamics that would lead to this feeling, and then create themechanics to produce the desired dynamics.
MDA in gaming
-
C OMMON T ERMS IN G AME D ESIGN
COMMON TERMS FOUND IN GAME DESIGN FOUND HERE
-
An activity with rules. It is a form of play oftenbut not always involving conflict, either with other players, with the game system itself, orwith randomness/fate/luck. Most games have goals, but not all (for example, The Sims andSimCity). Most games have defined start and end points, but not all (for example, World ofWarcraft and Dungeons & Dragons). Most games involve decision making on the part of theplayers, but not all (for example, Candy Land and Chutes and Ladders). A video game is agame (as defined above) that uses a digital video screen of some kind, in some way.”
what is a video game
-
Yet its rules, simple as they are, allow for a depth of strategy so great that itis still played heavily today
What keeps people playing a game
-
-
-
One of the best sources of information in the game world is the game itself. Game state can be transcribed into text so that a SLM can reason about the game world
What is the mapping between the Game World and the Real world?
-
to incorporate ACE autonomous game characters into their titles.
So, would all autonomous game characters have the same strategies and personalities that arise from NVIDIA implementation, regardless of the game or platform? Interesting.
-
-
hawkeyecollege.simplesyllabus.com hawkeyecollege.simplesyllabus.com
-
1/19/25 Chapter 10 READING: Wrapping and Taping Techniques
I am excited to learn how to tape because before every soccer practice and game I have to get my ankle taped.
-
-
usrussiarelations.org usrussiarelations.org
-
American Red Cross
To prepare you for your next trivia game night. Who started the American Red Cross, and what is its purpose?
-
-
social-media-ethics-automation.github.io social-media-ethics-automation.github.io
-
Before electronic computers were generally available, when scientists wanted the results of some calculations, they sometimes hired “computers” [b114], which were people trained to perform the calculations.
This concept reminds me of an interesting plot in《Three Body Problem》, where, in the three-body-problem visual game, a simplified "human computer" is described: assuming there are three people facing to each other, holding either red or white light, if a person see both the others hold white light, he would hold the white light as well; otherwise he would hold the red light. This game happens to represent the binary system in computer.
-
-
www.kickstarter.com www.kickstarter.comTend1
Tags
Annotators
URL
-
-
www.kickstarter.com www.kickstarter.com
-
www.kickstarter.com www.kickstarter.com
-
social-media-ethics-automation.github.io social-media-ethics-automation.github.io
-
Some platforms are used for sharing text and pictures (e.g., Facebook, Twitter, LinkedIn, WeChat, Weibo, QQ), some for sharing video (e.g., Youtube, TickTock), some for sharing audio (e.g., Clubhouse), some for sharing fanfiction (e.g., Fanfiction.net, AO3), some for gathering and sharing knowledge (e.g., Wikipedia, Quora, StackOverflow), some for sharing erotic content (e.g, OnlyFans).
I think some games could also be regarded as social media. For instance, I used to play Game for Peace, which is a mobile shooting game in China. In this application, players need to team up and work together to survive in the last. Therefore, discussions and communications are very frequent in this game. Sometimes, the interpersonal relationship is beyond teammates. Some people use this game to find a girlfriend or a boyfriend, and some players could make money by selling their services to other players. So I think some gaming platforms should also be included as a kind of social media.
-
-
today.tamu.edu today.tamu.edu
-
Games are a natural way to allow students to fail in a safe way, learn from failures and try again until they succeed. Some games, like Burnout Paradise* make failure fun. In the game, players can crash their cars – and the more spectacular the crash, the higher the points. This allows players to essentially learn from their mistakes, correct them and try again. The late video game theorist and author Jesper Juul wrote in his book, “The Art of Failure,” that losing in video games is part of what makes games so engaging. Failing in a game makes the player feel inadequate, yet the player can immediately redeem themselves and improve their skills.
Failure in video games not only brings a challenge to make videogame's more fun but difficulty can also teach people to make new strategies or make important decisions in said video game that can also improve real life skills.
-
The use of video games in the classroom is nothing new. Many people who went to school in the 1970s through the 1990s may recall the iconic video game The Oregon Trail, which made its debut in a classroom in 1971.
"The Oregon Trail" was a massive success in both education and entertainment. in addition, several other edutainment games have been made for ages 3-8, most being very popular
-
-
www.are.na www.are.na
-
these communities are trying to sift through the layers of the world to see what else might have been left behind at the code level by the developers during the making of the game.
intertextual (esp wrt code); marginalia; SKAM — transmedia emergent storytelling
-
Spectator Mode becomes a way to analyze the game world from the outside in, to instantly uncover the secret paths and tunnels in the ground below, to look at the gameworld from within a block, or from under the bedrock looking up through pools of lava, hidden diamonds, and glowing skeletons.
in what ways do you understand / come to learn a system, a world, an infrastructure? cf. position/where one is situated across an AI tech stack
Tags
Annotators
URL
-
-
nicholasmuellner.com nicholasmuellner.comjude1
-
But the uneasy fascination of the adjacent, vacant landscape rested in its unexpected insistence on presence. Suddenly, this primitive attempt at virtuality
cf Travess Smalley: https://www.are.na/editorial/where-boundary-breaks
-
-
biaiscognitifs.innovation.maif biaiscognitifs.innovation.maif
-
www.biorxiv.org www.biorxiv.org
-
Author response:
The following is the authors’ response to the previous reviews.
Reviewer #1 (Public review):
As a starting point, the authors discuss the so-called "additive partitioning" (AP) method proposed by Loreau & Hector in 2001. The AP is the result of a mathematical rearrangement of the definition of overyielding, written in terms of relative yields (RY) of species in mixtures relative to monocultures. One term, the so-called complementarity effect (CE), is proportional to the average RY deviations from the null expectations that plants of both species "do the same" in monocultures and mixtures. The other term, the selection effect (SE), captures how these RY deviations are related to monoculture productivity. Overall, CE measures whether relative biomass gains differ from zero when averaged across all community members, and SE, whether the "relative advantage" species have in the mixture, is related to their productivity. In extreme cases, when all species benefit, CE becomes positive.
This is not true; positive CE does not require positive RY deviations of all species. CE is positive as long as average RY deviation is greater than 0. In a 2-species mixture, for example, if the RY deviation of one species is -0.2 and that of the other species is +0.3, CE would be still positive. Positive CE can be associated with negative NE (net biodiversity effects) when more productivity species have smaller negative RY deviation compared to positive RY deviation of less productive species. Therefore, the suggestion by the reviewer “This is intuitively compatible with the idea that niche complementarity mitigates competition (CE>0)” is not correct.
When large species have large relative productivity increases, SE becomes positive. This is intuitively compatible with the idea that niche complementarity mitigates competition (CE>0), or that competitively superior species dominate mixtures and thereby driver overyielding (SE>0).
The use of word “mitigate” indicates that the effects of niche complementarity and competition are in opposite directions, which is not true with biodiversity experiments based on replacement design. We have explained this in detail in our first responses to reviewers.
However, it is very important to understand that CE and SE capture the "statistical structure" of RY that underlies overyielding. Specifically, CE and SE are not the ultimate biological mechanisms that drive overyielding, and never were meant to be. CE also does not describe niche complementarity. Interpreting CE and SE as directly quantifying niche complementarity or resource competition, is simply wrong, although it sometimes is done. The criticism of the AP method thus in large part seems unwarranted. The alternative methods the authors discuss (lines 108-123) are based on very similar principles.
Agree. However, If CE and SE are not meant to be biological mechanisms, as suggested by the reviewer, the argument “This is intuitively compatible with the idea that niche complementarity mitigates competition (CE>0), or that competitively superior species dominate mixtures and thereby driver overyielding (SE>0)” would be invalid.
Lines 108-123 are not on our method.
The authors now set out to develop a method that aims at linking response patterns to "more true" biological mechanisms.
Assuming that "competitive dominance" is key to understanding mixture productivity, because "competitive interactions are the predominant type of interspecific relationships in plants", the authors introduce "partial density" monocultures, i.e. monocultures that have the same planting density for a species as in a mixture. The idea is that using these partial density monocultures as a reference would allow for isolating the effect of competition by the surrounding "species matrix".
The authors argue that "To separate effects of competitive interactions from those of other species interactions, we would need the hypothesis that constituent species share an identical niche but differ in growth and competitive ability (i.e., absence of positive/negative interactions)." - I think the term interaction is not correctly used here, because clearly competition is an interaction, but the point made here is that this would be a zero-sum game.
We did not say that competition is not an interaction.
The authors use the ratio of productivity of partial density and full-density monocultures, divided by planting density, as a measure of "competitive growth response" (abbreviated as MG). This is the extra growth a plant individual produces when intraspecific competition is reduced.
Here, I see two issues: first, this rests on the assumption that there is only "one mode" of competition if two species use the same resources, which may not be true, because intraspecific and interspecific competition may differ. Of course, one can argue that then somehow "niches" are different, but such a niche definition would be very broad and go beyond the "resource set" perspective the authors adopt. Second, this value will heavily depend on timing and the relationship between maximum initial growth rates and competitive abilities at high stand densities.
True. Research findings indicate that biodiversity effect detected with AP is not constant.
The authors then progress to define relative competitive ability (RC), and this time simply uses monoculture biomass as a measure of competitive ability. To express this biomass in a standardized way, they express it as different from the mean of the other species and then divide by the maximum monoculture biomass of all species.
I have two concerns here: first, if competitive ability is the capability of a species to preempt resources from a pool also accessed by another species, as the authors argued before, then this seems wrong because one would expect that a species can simply be more productive because it has a broader niche space that it exploits. This contradicts the very narrow perspective on competitive ability the authors have adopted. This also is difficult to reconcile with the idea that specialist species with a narrow niche would outcompete generalist species with a broad niche.
Competitive ability is not necessarily associated with species niche space. Both generalist and specialist species can be more productive at a particular study site, as long as they are more capable of obtaining resources from a local pool. Remember, biodiversity experiments are conducted at a site of particular conditions, not across a range of species niche space at landscape level.
Second, I am concerned by the mathematical form. Standardizing by the maximum makes the scaling dependent on a single value.
As explained in lines 370-376, the mathematical form is a linear approximation as the relationship between competitive growth responses and species relative competitive ability is generally unknow but would be likely nonlinear. Once the relationship is determined in future research, the scaling factor is not needed.
As a final step, the authors calculate a "competitive expectation" for a species' biomass in the mixture, by scaling deviations from the expected yield by the product MG ⨯ RC. This would mean a species does better in a mixture when (1) it benefits most from a conspecific density reduction, and (2) has a relatively high biomass.
Put simply, the assumption would be that if a species is productive in monoculture (high RC), it effectively does not "see" the competitors and then grows like it would be the sole species in the community, i.e. like in the partial density monoculture.
Overall, I am not very convinced by the proposed method.
Comments on revised version:
Only minimal changes were made to the manuscript, and they do not address the main points that were raised.
Reviewer #2 (Public review):
This manuscript by Tao et al. reports on an effort to better specify the underlying interactions driving the effects of biodiversity on productivity in biodiversity experiments. The authors are especially concerned with the potential for competitive interactions to drive positive biodiversity-ecosystem functioning relationships by driving down the biomass of subdominant species. The authors suggest a new partitioning schema that utilizes a suite of partial density treatments to capture so-called competitive ability. While I agree with the authors that understanding the underlying drivers of biodiversity-ecosystem functioning relationships is valuable - I am unsure of the added value of this specific approach for several reasons.
No responses.
Comments on revised version:
The authors changed only one minor detail in response to the last round of reviews.
Reviewer #3 (Public review):
Summary:
This manuscript claims to provide a new null hypothesis for testing the effects of biodiversity on ecosystem functioning. It reports that the strength of biodiversity effects changes when this different null hypothesis is used. This main result is rather inevitable. That is, one expects a different answer when using a different approach. The question then becomes whether the manuscript's null hypothesis is both new and an improvement on the null hypothesis that has been in use in recent decades.
Our approach adopts two hypotheses, null hypothesis that is also with the additive partitioning model and competitive hypothesis that is new. Null hypothesis assumes that inter- and intra-specie interactions are the same, while competitive hypothesis assumes that species differ in competitive ability and growth rate. Therefore, our approach is an extension of current approach. Our approach separates effects of competitive interactions from those of other species interactions, while the current approach does not.
Strengths:
In general, I appreciate studies like this that question whether we have been doing it all wrong and I encourage consideration of new approaches.
Weaknesses:
Despite many sweeping critiques of previous studies and bold claims of novelty made throughout the manuscript, I was unable to find new insights. The manuscript fails to place the study in the context of the long history of literature on competition and biodiversity and ecosystem functioning.
We have explained in our first responses that competition and biodiversity effects are studied in different experimental approaches, i.e., additive and replacement designs. Results from one approach are not compatible with those from the other. For example, competition effect with additive design is negative but generally positive with replacement design that is used extensively in biodiversity experiments. We have considered species competitive ability, density-growth relationship, and different effects of competitive interactions between additive and replacement design, while the current method does not reflect any of those.
The Introduction claims the new approach will address deficiencies of previous approaches, but after reading further I see no evidence that it addresses the limitations of previous approaches noted in the Introduction. Furthermore, the manuscript does not reproducibly describe the methods used to produce the results (e.g., in Table 1) and relies on simulations, claiming experimental data are not available when many experiments have already tested these ideas and not found support for them.
We used simulation data, as partial density monocultures are generally not available in previous biodiversity experiments.
Finally, it is unclear to me whether rejecting the 'new' null hypothesis presented in the manuscript would be of interest to ecologists, agronomists, conservationists, or others.
Our null hypothesis is the same as the null hypothesis with the additive partitioning assuming that inter- and intra-species interactions are the same, while our competitive hypothesis assumes that species differ in competitive ability and growth rate. Rejecting null hypothesis means that inter- and intra-species interactions are different, whereas rejecting competitive hypothesis indicates existence of positive/negative species interactions. This would be interesting to everyone.
Comments on revised version:
Please see review comments on the previous version of this manuscript. The authors have not revised their manuscript to address most of the issues previously raised by reviewers.
No responses.
Recommendations for the authors:
Reviewer #1 (Recommendations for the authors):
Do take reviews seriously. Even if you think the reviewers all are wrong and did not understand your work, then this seems to indicate that it was not clearly presented.
Reviewer #2 (Recommendations for the authors):
I can understand that the authors are perhaps frustrated with what they perceive as a basic misunderstanding of their goals and approach. This misunderstanding however, provides with it an opportunity to clarify. I believe that the authors have tried to clarify in rebutting our statements but would do better to clarify in the manuscript itself. If we reviewers, who are deeply invested in this field, don't understand the approach and its value, then it is likely that many readers will not as well.
The additive partitioning has been publicly questioned at least for serval times since the conception of the method in 2001. Our work provides an alternative.
-
-
www.atelier-collaboratif.com www.atelier-collaboratif.com
-
Briefing Doc: Exploration des Techniques de Facilitation
Ce document synthétise les concepts clés et les méthodes de facilitation présentées dans le "Kit de Facilitation" (https://www.atelier-collaboratif.com/telechargements/kit-de-facilitation.pdf).
Thèmes Principaux:
Importance de la préparation:
Avant chaque atelier, une phase de réflexion est essentielle pour définir l'objectif, identifier les participants et les livrables attendus.
Il faut également anticiper les risques et les solutions possibles. Le "Kit" propose un plateau "ORGANISATION" pour structurer cette préparation (p.4).
Diversité des pratiques:
Le kit présente un éventail de "cartes pratiques" (p.5) classées selon leur niveau de difficulté (S'améliorer, Prioriser/Décider, Briser la glace, Générer des idées, etc.) et proposant des techniques variées pour chaque étape d'un atelier collaboratif.
Importance de l'intelligence collective: La plupart des techniques présentées visent à stimuler la participation active de tous, à encourager le partage d'idées, et à favoriser la co-construction de solutions. Idées et Faits Marquants:
Le rôle du facilitateur:
Le facilitateur joue un rôle central dans la réussite d'un atelier. Il guide le groupe, assure le bon déroulement des activités, et veille à créer un environnement propice à la collaboration.
L'utilisation d'outils visuels:
Des outils comme les post-it, les tableaux, les cartes, etc. sont fréquemment utilisés pour faciliter la visualisation des idées, la structuration des discussions, et la prise de décisions collective.
L'importance du feedback:
Plusieurs techniques (ex: ROTI Agile, Perfection Game) permettent de recueillir du feedback des participants, ce qui est crucial pour l'amélioration continue des ateliers. Exemples de Techniques et Citations:
La Rétrospective 4L (p. 6):
Permet de faire le bilan d'une activité en utilisant l'analogie d'une voiture. Les participants identifient sur des cartes "ce qui freine" (le vent) et "ce qui pousse" (le moteur).
Gommettocratie (p. 9):
Technique de priorisation simple et visuelle.
Les participants votent pour les idées qui les séduisent le plus en collant des gommettes.
Le Réseau Social en Papier (p. 11):
Un jeu ludique pour briser la glace et permettre aux participants de se connaître. World Café (p. 18): "Inventé en 2009 par Jim Benson et Jeremy Lightsmith".
Cette technique favorise le dialogue et l'échange d'idées sur plusieurs sujets en petits groupes.
Impact Mapping (p. 24):
Permet de "représenter visuellement les impacts et hypothèses de développement d'un produit".
Méthode du Point de Vue (POV) (p. 25):
"Le point de vue est la perception du problème vue par l'utilisateur." Cette méthode permet de se centrer sur les besoins des utilisateurs.
Conclusion:
Le "Kit de Facilitation" est une ressource précieuse pour tous ceux qui souhaitent animer des ateliers collaboratifs efficaces.
Il propose une grande variété de techniques et d'outils pour chaque étape du processus, de la préparation à la mise en œuvre des décisions.
-
- Dec 2024
-
4thgenerationcivilization.substack.com 4thgenerationcivilization.substack.com
-
The Everywheres are on the contrary nomadic elements that are willing to be of service to cosmo-local productive economic alliances, seeding various locales with the trans-local experience, both of other locales they may have visited, but also of the network itself.
Seductive analogy. Reminds me of Daniel Schmatchtenberger's Game A (civilizational problems of competition) and Game B (beyond competition) that creates a simple US vs. THEM for convening the like-minded activists, but not sure it accurately describes the virtual landscape well-enough for implementers seeking to develop and deploy new type(s) of competence.
-
-
arxiv.org arxiv.org
-
Reviewer #1 (Public review):
Summary:
Zhang et al. addressed the question of whether advantageous and disadvantageous inequality aversion can be vicariously learned and generalized. Using an adapted version of the ultimatum game (UG), in three phases, participants first gave their own preference (baseline phase), then interacted with a "teacher" to learn their preference (learning phase), and finally were tested again on their own (transfer phase). The key measure is whether participants exhibited similar choice preferences (i.e., rejection rate and fairness rating) influenced by the learning phase, by contrasting their transfer phase and baseline phase. Through a series of statistical modeling and computational modeling, the authors reported that both advantageous and disadvantageous inequality aversion can indeed be learned (Study 1), and even be generalised (Study 2).
Strengths:
This study is very interesting, it directly adapted the lab's previous work on the observational learning effect on disadvantageous inequality aversion, to test both advantageous and disadvantageous inequality aversion in the current study. Social transmission of action, emotion, and attitude have started to be looked at recently, hence this research is timely. The use of computational modeling is mostly appropriate and motivated. Study 2, which examined the vicarious inequality aversion in conditions where feedback was never provided, is interesting and important to strengthen the reported effects. Both studies have proper justifications to determine the sample size.
Weaknesses:
Despite the strengths, a few conceptual aspects and analytical decisions have to be explained, justified, or clarified.
INTRODUCTION/CONCEPTUALIZATION<br /> (1) Two terms seem to be interchangeable, which should not, in this work: vicarious/observational learning vs preference learning. For vicarious learning, individuals observe others' actions (and optionally also the corresponding consequence resulting directly from their own actions), whereas, for preference learning, individuals predict, or act on behalf of, the others' actions, and then receive feedback if that prediction is correct or not. For the current work, it seems that the experiment is more about preference learning and prediction, and less so about vicarious learning. The intro and set are heavily around vicarious learning, and later the use of vicarious learning and preference learning is rather mixed in the text. I think either tone down the focus on vicarious learning, or discuss how they are different. Some of the references here may be helpful: Charpentier et al., Neuron, 2020; Olsson et al., Nature Reviews Neuroscience, 2020; Zhang & Glascher, Science Advances, 2020
EXPERIMENTAL DESIGN<br /> (2) For each offer type, the experiment "added a uniformly distributed noise in the range of (-10 ,10)". I wonder what this looks like? With only integers such as 25:75, or even with decimal points? More importantly, is it possible to have either 70:30 or 90:10 option, after adding the noise, to have generated an 80:20 split shown to the participants? If so, for the analyses later, when participants saw the 80:20 split, which condition did this trial belong to? 70:30 or 90:10? And is such noise added only to the learning phase, or also to the baseline/transfer phases? This requires some clarification.
(3) For the offer conditions (90:10, 70:30, 50:50, 30:70, 10:90) - are they randomized? If so, how is it done? Is it randomized within each participant, and/or also across participants (such that each participant experienced different trial sequences)? This is important, as the order especially for the learning phase can largely impact the preference learning of the participants.
STATISTICAL ANALYSIS & COMPUTATIONAL MODELING<br /> (4) In Study 1 DI offer types (90:10, 70:30), the rejection rate for DI-AI averse looks consistently higher than that for DI averse (ie, the blue line is above the yellow line). Is this significant? If so, how come? Since this is a between-subject design, I would not anticipate such a result (especially for the baseline). Also, for the LME results (eg, Table S3), only interactions were reported but not the main results.
(5) I do not particularly find this analysis appealing: "we examined whether participants' changes in rejection rates between Transfer and Baseline, could be explained by the degree to which they vicariously learned, defined as the change in punishment rates between the first and last 5 trials of the Learning phase." Naturally, the participants' behavior in the first 5 trials in the learning phase will be similar to those in the baseline; and their behavior in the last 5 trials in the learning phase would echo those at the transfer phase. I think it would be stronger to link the preference learning results to the change between the baseline and transfer phase, eg, by looking at the difference between alpha (beta) at the end of the learning phase and the initial alpha (beta).
(6) I wonder if data from the baseline and transfer phases can also be modeled, using a simple Fehr-Schimdt model. This way, the change in alpha/beta can also be examined between the baseline and transfer phase.
(7) I quite liked Study 2 which tests the generalization effect, and I expected to see an adapted computational modeling to directly reflect this idea. Indeed, the authors wrote, "[...] given that this model [...] assumes the sort of generalization of preferences between offer types [...]". But where exactly did the preference learning model assume the generalization? In the methods, the modeling seems to be only about Study 1; did the authors advise their model to accommodate Study 2? The authors also ran simulation for the learning phase in Study 2 (Figure 6), and how did the preference update (if at all) for offers (90:10 and 10:90) where feedback was not given? Extending/Unpacking the computational modeling results for Study 2 will be very helpful for the paper.
-
-
www.kickstarter.com www.kickstarter.comIsla!1
-
www.kickstarter.com www.kickstarter.com
-
www.youtube.com www.youtube.com
-
for - TED Talk - YouTube - A word game to convey any language - Ajit Narayanan - potential source - Deep Humanity - BEing journeys in language - appreciation of inhabiting the symbolosphere // - Summary - An interesting idea of teasing out the data structure behind language - This could be a rich area to explore for Deep Humanity language BEing journeys to help people gain deeper appreciation of their own amazing language abilities - as well as gain an appreciation for the enormous amount of time our life is spent in the (relative) symbolosphere
-
Next (SHIFT+n) Feats of memory anyone can do | Joshua Foer 20:29
Ajit Narayanan:
A word game to communicate in any language

-
supposing I was a writer, say, for a newspaper or for a magazine. I could create content in one language, FreeSpeech, and the person who's consuming that content, the person who's reading that particular information could choose any engine, and they could read it in their own mother tongue, in their native language
for - freespeech can be used as an international language translator - data structure of thought - from TED Talk - YouTube - A word game to convey any language - Ajit Narayanan
-
when you want to use Google, you go into Google search, and you type in English, and it matches the English with the English. What if we could do this in FreeSpeech instead? I have a suspicion that if we did this, we'd find that algorithms like searching, like retrieval, all of these things, are much simpler and also more effective, because they don't process the data structure of speech. Instead they're processing the data structure of thought
for - indyweb dev - question - alternative to AI Large Language Models? - Is indyweb functionality the same as Freespeech functionality? - from TED Talk - YouTube - A word game to convey any language - Ajit Narayanan - data structure of thought - from TED Talk - YouTube - A word game to convey any language - Ajit Narayanan
-
language is really the brain's invention to convert this rich, multi-dimensional thought on one hand into speech on the other hand.
for - key insight - ideas are multidimensional - speech is one dimensional - language is one dimensional - from TED Talk - YouTube - A word game to convey any language - Ajit Narayanan
-
the dream, the hope, the vision, really, is that when they learn English this way, they learn it with the same proficiency as their mother tongue.
for - investigate - question - Does this other app that allows learning another language with the proficiency of a child exist? - from TED Talk - YouTube - A word game to convey any language - Ajit Narayanan
-
there were a group of scientists that were trying to understand how the brain processes language, and they found something very interesting. They found that when you learn a language as a child, as a two-year-old, you learn it with a certain part of your brain, and when you learn a language as an adult -- for example, if I wanted to learn Japanese
for - research study - language - children learning mother tongue use a different post off the brain then adults learning another language - from TED Talk - YouTube - A word game to convey any language - Ajit Narayanan
-
if I wasn't an English speaker, if I was speaking in some other language, this map would actually hold true in any language. So long as the questions are standardized, the map is actually independent of language. So I call this FreeSpeech
for - app - Free Speech - permutations of pictures that can created meaning without using language - from TED Talk - YouTube - A word game to convey any language - Ajit Narayanan
-
grammar is incredibly powerful, because grammar is this one component of language which takes this finite vocabulary that all of us have and allows us to convey an infinite amount of information, an infinite amount of ideas. It's the way in which you can put things together in order to convey anything you want to
for - the power of grammar - infinite permutations if meaning using a finite set of symbols - from TED Talk - YouTube - A word game to convey any language - Ajit Narayanan
Tags
- research study - language - children learning mother tongue use a different post off the brain then adults learning another language - from TED Talk - YouTube - A word game to convey any language - Ajit Narayanan
- the power of grammar - infinite permutations if meaning using a finite set of symbols - from TED Talk - YouTube - A word game to convey any language - Ajit Narayanan
- potential source - Deep Humanity - BEing journeys in language
- app - Free Speech - permutations of pictures that can created meaning without using language - from TED Talk - YouTube - A word game to convey any language - Ajit Narayanan
- investigate - question - Does this other app that allows learning another language with the proficiency of a child exist? - from TED Talk - YouTube - A word game to convey any language - Ajit Narayanan
- TED Talk - YouTube - A word game to convey any language - Ajit Narayanan
- indyweb dev - question - alternative to AI Large Language Models? - Is indyweb functionality the same as Freespeech functionality? - from TED Talk - YouTube - A word game to convey any language - Ajit Narayanan
- data structure of thought - from TED Talk - YouTube - A word game to convey any language - Ajit Narayanan
- appreciation of inhabiting the symbolosphere
- freespeech can be used as an international language translator - data structure of thought - from TED Talk - YouTube - A word game to convey any language - Ajit Narayanan
- key insight - ideas are multidimensional - speech is one dimensional - language is one dimensional - from TED Talk - YouTube - A word game to convey any language - Ajit Narayanan
Annotators
URL
-
-
www.youtube.com www.youtube.com
-
for - climate crisis - impact of Trump tariff strategy - increasing economic and carbon inequality and precarity for the masses - from - Youtube - Trump wants to crash to benefit the ultra wealthy - Trump's planning to crash the global economy - Richard J Murphy - 2024, Dec
// - SUMMARY - Richard J Murphy provides us with a big picture of Trump's objective in his calculated Tariff strategy - It's not that it makes no sense and is a strategy of a madman - On the contrary, he has a very calculated and maniacal strategy that will result in significantly increasing the wealth of the elites - By creating high tariffs, he will bring about a global economic crash - Like the 2008 and 2020 crash, central banks will print trillions of dollars of money and handout bailouts - It is the elites who will receive these bailouts and inflate the value of their assets - This will - substantially increase the wealth of the rich - substantially increase the precarity of the vast majority of people - increase global inequality - financial inequality and - carbon inequality - This increased precarity is bad news for the climate crisis as a precarious population have less flexibility in reducing their carbon footprint and are more dependent than ever on whatever remain job and resources they still have - Given we have this knowledge of the elite's hidden strategy, can we the people intervene in any way? - We need to have an understanding of how elites see the world - The entire worldview of externalizing investment as a game of accumulation must be understood deeply - in order to find leverage points for rapid system change
//
Tags
Annotators
URL
-
-
granta.com granta.com
-
The ‘sapiosexual type’ is more sophisticated than its predecessors and becoming prevalent with highly educated women. Creating these characters convincingly is no easy task. Otome game companies often hire female writers from top universities with diverse backgrounds, equipped with knowledge from a range of disciplines. ‘He’ should be able to comment on a Shakespearean sonnet or quantum physics in a magisterial way, if prompted.
what
-
Iconic games such as Genshin Impact (developed by the Shanghai game company miHoYo, whose slogan is ‘Tech Otakus Save the World’) are featuring more and more charming male characters to appeal to female players, which is seen as a betrayal of its origins. Many male players refuse to play with male characters – going so far as to deliberately drop them dead – and vow to boycott the game until this supposed mistake is rectified. What they don’t grasp is that they need to outspend female and gay players to regain some bargaining power. Petulantly railing against the ‘pink tax’ won’t get them what they want.
What shitty use of passive voice universalizing the next sentence's "many male players"
-
-
onethingnewsletter.substack.com onethingnewsletter.substack.com
-
Parasocial relationships are the name of the game. When people call for a Joe Rogan of the left, it seems like they don’t realize that one of the reasons he is so powerful is that he is many of his listeners’ best friend. People spend hours and hours a day with him; his show and its extended universe have become an on-demand loneliness killing service. The power (and value) of that relationship is unmatched. Puck is a parasocial publication, that’s why you hear the tentpole writers’ voices in solo podcasts.
I want to read more about parasocial media patterns pre-broadcast media. You can't tell me that there weren't forms
-
-
Local file Local file
-
To pretend that this multi-level game can be flattened outinto a merely technical question is naïve. That becomes clearwhen it enters the patently political phase and people fight overthe legislative and regulative details.
technical question doesn't work- Foucalt
-
-
www.modernisation.gouv.fr www.modernisation.gouv.fr
-
www.youtube.com www.youtube.com
-
Sommaire minuté des temps forts du webinaire "Le tabac chez les jeunes : comment les accompagner à l'arrêt ? | Crips IDF"
Ce sommaire met en avant la richesse du webinaire, en abordant à la fois * le contexte de la consommation de tabac chez les jeunes, * les nouveaux produits et les risques associés, * le lien avec la santé mentale et * les différentes stratégies d'accompagnement.
Le témoignage de l'association Repère apporte une dimension concrète et inspirante, tandis que la présentation des outils du Crips offre aux professionnels un panel de ressources pour animer des séances de prévention et de sensibilisation.
0:00 - 1:30 : Introduction et présentation des intervenantes
- Géraldine, infirmière addictologue et tabacologue, et Estella Furau, chargée de projet sur la thématique addiction au Crips Île-de-France, se présentent et exposent leurs expériences professionnelles.
1:30 - 8:00 : Contexte de la consommation de tabac chez les jeunes
- Discussion sur la définition du public "jeune" et les spécificités des différentes tranches d'âge.
- Importance de la prise de conscience de l'addiction pour amorcer une démarche d'arrêt.
- Mise en avant des différences d'accès aux ressources et de prévalence tabagique selon les milieux sociaux.
- Bonne nouvelle : diminution de la prévalence tabagique chez les jeunes, mais vigilance nécessaire face aux nouveaux produits (vape, puff...).
- Impact positif des politiques publiques (lieux sans tabac, augmentation du prix du paquet) sur la diminution du tabagisme.
- Débat sur l'interdiction de fumer sur les terrasses.
- Différences d'accompagnement entre un patient jeune et un patient plus âgé : difficulté de la prise de conscience de l'addiction chez les jeunes.
- Importance d'accompagner le jeune dans sa demande, qu'il s'agisse d'une réduction ou d'un arrêt total.
- Présentation de Tabac info service, un outil d'aide à l'arrêt.
8:00 - 15:00 : Nouveaux produits et risques associés
- Augmentation de l'usage de la vape chez les jeunes, notamment la puff, devenue un objet tendance.
- Préoccupations concernant la puff : marketing ciblant les jeunes, risques de dépendance et de passage à la cigarette.
- Interdiction des puffs jetables : une mesure efficace ?
- Méconnaissance des risques liés à la chicha (tabac, nicotine, combustion...) chez les jeunes.
- Difficulté de la prise en charge face à la consommation de chicha, souvent vécue comme une expérience collective.
- Diminution de l'expérimentation du cannabis, mais il reste la première drogue illicite consommée par les jeunes.
- Importance d'aborder les co-consommations et les transferts d'addiction.
- Conseils pour la prise en charge du cannabis : réduction des risques et orientation vers des structures spécialisées.
15:00 - 22:00 : Lien entre santé mentale et consommation de tabac
- Statistiques alarmantes sur le bien-être mental des lycéens : 49% ne présentent pas un bon niveau de bien-être mental.
- Impact du tabac sur la santé mentale : la dépression peut être un signe de manque de nicotine.
- Apparition possible de signes de dépression, voire d'idées suicidaires, lors d'un sevrage tabagique trop brutal.
- Importance de différencier une dépression induite par l'arrêt du tabac d'une dépression préexistante.
22:00 - 27:00 : Conseils aux professionnels, aux proches et aux jeunes fumeurs
- Conseils aux professionnels : patience, humilité et importance de la transmission d'information sur les ressources disponibles.
- Conseils aux proches : ne pas forcer le fumeur à arrêter, lui apporter du soutien et l'informer des aides disponibles.
- Conseils aux jeunes fumeurs : se tourner vers un professionnel, l'arrêt du tabac est faisable.
- Importance de lutter contre les représentations négatives de l'aide et des tabacologues.
- Rôle des pharmaciens, des sages-femmes, des kinés... dans l'accompagnement à l'arrêt et la réduction des risques.
- Importance de la réduction des risques et du remboursement des substituts nicotiniques.
27:00 - 33:00 : Présentation de programmes d'aide à l'arrêt pour les jeunes
- Mois sans tabac : campagne nationale de sensibilisation et d'aide à l'arrêt.
- Tabado : programme probant d'aide à l'arrêt pour les lycées professionnels et les CFA (actuellement interrompu).
- Desclic Stop Tabac : programme similaire à Tabado pour les établissements agricoles.
- Programmes d'animation-débat : Ligue contre le cancer, Crips Île-de-France.
33:00 - 44:00 : Témoignage de l'association Repère et présentation d'un projet d'ateliers "Mois sans tabac"
- Marie Durantis, éducatrice spécialisée, présente son projet d'ateliers "Mois sans tabac" mené avec des jeunes et des adultes.
- Importance de l'approche ludique et éducative : brainstorming, questionnaire, jeux, création d'affiches...
- Participation au challenge "Mois sans tabac" de la Ligue contre le cancer.
- Visite de l'Escape Game "Tabac" à la Cité des Sciences.
- Bilan positif du projet : favorise la cohésion de groupe, la prévention et la sensibilisation.
44:00 - Fin : Présentation d'outils d'animation du Crips pour aborder le tabac avec les jeunes
- Tirtaclop : outil pour aborder la réduction du tabac et identifier les besoins et les plaisirs.
- Infox : jeu de cartes d'affirmations vraies ou fausses pour initier le débat et évaluer les connaissances.
- PICT Prévention Tabac : jeu de type Pictionary pour aborder les thématiques liées au tabac de manière ludique.
- Escape Game Tabac (version jeu de cartes et version salle) : outil ludique pour aborder toutes les dimensions de l'arrêt du tabac.
- Outil "Chicha" : jeu de cartes pour explorer les contextes de consommation de la chicha et identifier les conduites à risque.
- Modérateur de forum : jeu de rôle pour déconstruire les idées reçues et encourager la réflexion critique.
- Jeu "À J" : jeu de cartes pour analyser des situations à risque liées à la consommation de tabac et d'alcool.
Tags
Annotators
URL
-
-
learning.amplify.com learning.amplify.com
-
According to all known laws of aviation,
there is no way a bee should be able to fly.
Its wings are too small to get its fat little body off the ground.
The bee, of course, flies anyway
because bees don't care what humans think is impossible.
Yellow, black. Yellow, black. Yellow, black. Yellow, black.
Ooh, black and yellow! Let's shake it up a little.
Barry! Breakfast is ready!
Ooming!
Hang on a second.
Hello?
Barry?
Adam?
Oan you believe this is happening?
I can't. I'll pick you up.
Looking sharp.
Use the stairs. Your father paid good money for those.
Sorry. I'm excited.
Here's the graduate. We're very proud of you, son.
A perfect report card, all B's.
Very proud.
Ma! I got a thing going here.
You got lint on your fuzz.
Ow! That's me!
Wave to us! We'll be in row 118,000.
Bye!
Barry, I told you, stop flying in the house!
Hey, Adam.
Hey, Barry.
Is that fuzz gel?
A little. Special day, graduation.
Never thought I'd make it.
Three days grade school, three days high school.
Those were awkward.
Three days college. I'm glad I took a day and hitchhiked around the hive.
You did come back different.
Hi, Barry.
Artie, growing a mustache? Looks good.
Hear about Frankie?
Yeah.
You going to the funeral?
No, I'm not going.
Everybody knows, sting someone, you die.
Don't waste it on a squirrel. Such a hothead.
I guess he could have just gotten out of the way.
I love this incorporating an amusement park into our day.
That's why we don't need vacations.
Boy, quite a bit of pomp… under the circumstances.
Well, Adam, today we are men.
We are!
Bee-men.
Amen!
Hallelujah!
Students, faculty, distinguished bees,
please welcome Dean Buzzwell.
Welcome, New Hive Oity graduating class of…
…9:15.
That concludes our ceremonies.
And begins your career at Honex Industries!
Will we pick ourjob today?
I heard it's just orientation.
Heads up! Here we go.
Keep your hands and antennas inside the tram at all times.
Wonder what it'll be like? A little scary. Welcome to Honex, a division of Honesco
and a part of the Hexagon Group.
This is it!
Wow.
Wow.
We know that you, as a bee, have worked your whole life
to get to the point where you can work for your whole life.
Honey begins when our valiant Pollen Jocks bring the nectar to the hive.
Our top-secret formula
is automatically color-corrected, scent-adjusted and bubble-contoured
into this soothing sweet syrup
with its distinctive golden glow you know as…
Honey!
That girl was hot.
She's my cousin!
She is?
Yes, we're all cousins.
Right. You're right.
At Honex, we constantly strive
to improve every aspect of bee existence.
These bees are stress-testing a new helmet technology.
What do you think he makes? Not enough. Here we have our latest advancement, the Krelman.
What does that do? Oatches that little strand of honey that hangs after you pour it. Saves us millions.
Oan anyone work on the Krelman?
Of course. Most bee jobs are small ones. But bees know
that every small job, if it's done well, means a lot.
But choose carefully
because you'll stay in the job you pick for the rest of your life.
The same job the rest of your life? I didn't know that.
What's the difference?
You'll be happy to know that bees, as a species, haven't had one day off
in 27 million years.
So you'll just work us to death?
We'll sure try.
Wow! That blew my mind!
"What's the difference?" How can you say that?
One job forever? That's an insane choice to have to make.
I'm relieved. Now we only have to make one decision in life.
But, Adam, how could they never have told us that?
Why would you question anything? We're bees.
We're the most perfectly functioning society on Earth.
You ever think maybe things work a little too well here?
Like what? Give me one example.
I don't know. But you know what I'm talking about.
Please clear the gate. Royal Nectar Force on approach.
Wait a second. Oheck it out.
Hey, those are Pollen Jocks! Wow. I've never seen them this close.
They know what it's like outside the hive.
Yeah, but some don't come back.
Hey, Jocks! Hi, Jocks! You guys did great!
You're monsters! You're sky freaks! I love it! I love it!
I wonder where they were. I don't know. Their day's not planned.
Outside the hive, flying who knows where, doing who knows what.
You can'tjust decide to be a Pollen Jock. You have to be bred for that.
Right.
Look. That's more pollen than you and I will see in a lifetime.
It's just a status symbol. Bees make too much of it.
Perhaps. Unless you're wearing it and the ladies see you wearing it.
Those ladies? Aren't they our cousins too?
Distant. Distant.
Look at these two.
Oouple of Hive Harrys. Let's have fun with them. It must be dangerous being a Pollen Jock.
Yeah. Once a bear pinned me against a mushroom!
He had a paw on my throat, and with the other, he was slapping me!
Oh, my! I never thought I'd knock him out. What were you doing during this?
Trying to alert the authorities.
I can autograph that.
A little gusty out there today, wasn't it, comrades?
Yeah. Gusty.
We're hitting a sunflower patch six miles from here tomorrow.
Six miles, huh? Barry! A puddle jump for us, but maybe you're not up for it.
Maybe I am. You are not! We're going 0900 at J-Gate.
What do you think, buzzy-boy? Are you bee enough?
I might be. It all depends on what 0900 means.
Hey, Honex!
Dad, you surprised me.
You decide what you're interested in?
Well, there's a lot of choices. But you only get one. Do you ever get bored doing the same job every day?
Son, let me tell you about stirring.
You grab that stick, and you just move it around, and you stir it around.
You get yourself into a rhythm. It's a beautiful thing.
You know, Dad, the more I think about it,
maybe the honey field just isn't right for me.
You were thinking of what, making balloon animals?
That's a bad job for a guy with a stinger.
Janet, your son's not sure he wants to go into honey!
Barry, you are so funny sometimes. I'm not trying to be funny. You're not funny! You're going into honey. Our son, the stirrer!
You're gonna be a stirrer? No one's listening to me! Wait till you see the sticks I have.
I could say anything right now. I'm gonna get an ant tattoo!
Let's open some honey and celebrate!
Maybe I'll pierce my thorax. Shave my antennae.
Shack up with a grasshopper. Get a gold tooth and call everybody "dawg"!
I'm so proud.
We're starting work today! Today's the day. Oome on! All the good jobs will be gone.
Yeah, right.
Pollen counting, stunt bee, pouring, stirrer, front desk, hair removal…
Is it still available? Hang on. Two left! One of them's yours! Oongratulations! Step to the side.
What'd you get? Picking crud out. Stellar! Wow!
Oouple of newbies?
Yes, sir! Our first day! We are ready!
Make your choice.
You want to go first? No, you go. Oh, my. What's available?
Restroom attendant's open, not for the reason you think.
Any chance of getting the Krelman? Sure, you're on. I'm sorry, the Krelman just closed out.
Wax monkey's always open.
The Krelman opened up again.
What happened?
A bee died. Makes an opening. See? He's dead. Another dead one.
Deady. Deadified. Two more dead.
Dead from the neck up. Dead from the neck down. That's life!
Oh, this is so hard!
Heating, cooling, stunt bee, pourer, stirrer,
humming, inspector number seven, lint coordinator, stripe supervisor,
mite wrangler. Barry, what do you think I should… Barry?
Barry!
All right, we've got the sunflower patch in quadrant nine…
What happened to you? Where are you?
I'm going out.
Out? Out where?
Out there.
Oh, no!
I have to, before I go to work for the rest of my life.
You're gonna die! You're crazy! Hello?
Another call coming in.
If anyone's feeling brave, there's a Korean deli on 83rd
that gets their roses today.
Hey, guys.
Look at that. Isn't that the kid we saw yesterday? Hold it, son, flight deck's restricted.
It's OK, Lou. We're gonna take him up.
Really? Feeling lucky, are you?
Sign here, here. Just initial that.
Thank you. OK. You got a rain advisory today,
and as you all know, bees cannot fly in rain.
So be careful. As always, watch your brooms,
hockey sticks, dogs, birds, bears and bats.
Also, I got a couple of reports of root beer being poured on us.
Murphy's in a home because of it, babbling like a cicada!
That's awful. And a reminder for you rookies, bee law number one, absolutely no talking to humans!
All right, launch positions!
Buzz, buzz, buzz, buzz! Buzz, buzz, buzz, buzz! Buzz, buzz, buzz, buzz!
Black and yellow!
Hello!
You ready for this, hot shot?
Yeah. Yeah, bring it on.
Wind, check.
Antennae, check.
Nectar pack, check.
Wings, check.
Stinger, check.
Scared out of my shorts, check.
OK, ladies,
let's move it out!
Pound those petunias, you striped stem-suckers!
All of you, drain those flowers!
Wow! I'm out!
I can't believe I'm out!
So blue.
I feel so fast and free!
Box kite!
Wow!
Flowers!
This is Blue Leader. We have roses visual.
Bring it around 30 degrees and hold.
Roses!
30 degrees, roger. Bringing it around.
Stand to the side, kid. It's got a bit of a kick.
That is one nectar collector!
Ever see pollination up close? No, sir. I pick up some pollen here, sprinkle it over here. Maybe a dash over there,
a pinch on that one. See that? It's a little bit of magic.
That's amazing. Why do we do that?
That's pollen power. More pollen, more flowers, more nectar, more honey for us.
Oool.
I'm picking up a lot of bright yellow. Oould be daisies. Don't we need those?
Oopy that visual.
Wait. One of these flowers seems to be on the move.
Say again? You're reporting a moving flower?
Affirmative.
That was on the line!
This is the coolest. What is it?
I don't know, but I'm loving this color.
It smells good. Not like a flower, but I like it.
Yeah, fuzzy.
Ohemical-y.
Oareful, guys. It's a little grabby.
My sweet lord of bees!
Oandy-brain, get off there!
Problem!
Guys! This could be bad. Affirmative.
Very close.
Gonna hurt.
Mama's little boy.
You are way out of position, rookie!
Ooming in at you like a missile!
Help me!
I don't think these are flowers.
Should we tell him? I think he knows. What is this?!
Match point!
You can start packing up, honey, because you're about to eat it!
Yowser!
Gross.
There's a bee in the car!
Do something!
I'm driving!
Hi, bee.
He's back here!
He's going to sting me!
Nobody move. If you don't move, he won't sting you. Freeze!
He blinked!
Spray him, Granny!
What are you doing?!
Wow… the tension level out here is unbelievable.
I gotta get home.
Oan't fly in rain.
Oan't fly in rain.
Oan't fly in rain.
Mayday! Mayday! Bee going down!
Ken, could you close the window please?
Ken, could you close the window please?
Oheck out my new resume. I made it into a fold-out brochure.
You see? Folds out.
Oh, no. More humans. I don't need this.
What was that?
Maybe this time. This time. This time. This time! This time! This…
Drapes!
That is diabolical.
It's fantastic. It's got all my special skills, even my top-ten favorite movies.
What's number one? Star Wars?
Nah, I don't go for that…
…kind of stuff.
No wonder we shouldn't talk to them. They're out of their minds.
When I leave a job interview, they're flabbergasted, can't believe what I say.
There's the sun. Maybe that's a way out.
I don't remember the sun having a big 75 on it.
I predicted global warming.
I could feel it getting hotter. At first I thought it was just me.
Wait! Stop! Bee!
Stand back. These are winter boots.
Wait!
Don't kill him!
You know I'm allergic to them! This thing could kill me!
Why does his life have less value than yours?
Why does his life have any less value than mine? Is that your statement?
I'm just saying all life has value. You don't know what he's capable of feeling.
My brochure!
There you go, little guy.
I'm not scared of him. It's an allergic thing.
Put that on your resume brochure.
My whole face could puff up.
Make it one of your special skills.
Knocking someone out is also a special skill.
Right. Bye, Vanessa. Thanks.
Vanessa, next week? Yogurt night?
Sure, Ken. You know, whatever.
You could put carob chips on there.
Bye.
Supposed to be less calories.
Bye.
I gotta say something.
She saved my life. I gotta say something.
All right, here it goes.
Nah.
What would I say?
I could really get in trouble.
It's a bee law. You're not supposed to talk to a human.
I can't believe I'm doing this.
I've got to.
Oh, I can't do it. Oome on!
No. Yes. No.
Do it. I can't.
How should I start it? "You like jazz?" No, that's no good.
Here she comes! Speak, you fool!
Hi!
I'm sorry.
You're talking. Yes, I know. You're talking!
I'm so sorry.
No, it's OK. It's fine. I know I'm dreaming.
But I don't recall going to bed.
Well, I'm sure this is very disconcerting.
This is a bit of a surprise to me. I mean, you're a bee!
I am. And I'm not supposed to be doing this,
but they were all trying to kill me.
And if it wasn't for you…
I had to thank you. It's just how I was raised.
That was a little weird.
I'm talking with a bee. Yeah. I'm talking to a bee. And the bee is talking to me!
I just want to say I'm grateful. I'll leave now.
Wait! How did you learn to do that? What? The talking thing.
Same way you did, I guess. "Mama, Dada, honey." You pick it up.
That's very funny. Yeah. Bees are funny. If we didn't laugh, we'd cry with what we have to deal with.
Anyway…
Oan I…
…get you something?
Like what? I don't know. I mean… I don't know. Ooffee?
I don't want to put you out.
It's no trouble. It takes two minutes.
It's just coffee.
I hate to impose.
Don't be ridiculous!
Actually, I would love a cup.
Hey, you want rum cake?
I shouldn't.
Have some.
No, I can't.
Oome on!
I'm trying to lose a couple micrograms.
Where? These stripes don't help. You look great!
I don't know if you know anything about fashion.
Are you all right?
No.
He's making the tie in the cab as they're flying up Madison.
He finally gets there.
He runs up the steps into the church. The wedding is on.
And he says, "Watermelon? I thought you said Guatemalan.
Why would I marry a watermelon?"
Is that a bee joke?
That's the kind of stuff we do.
Yeah, different.
So, what are you gonna do, Barry?
About work? I don't know.
I want to do my part for the hive, but I can't do it the way they want.
I know how you feel.
You do? Sure. My parents wanted me to be a lawyer or a doctor, but I wanted to be a florist.
Really? My only interest is flowers. Our new queen was just elected with that same campaign slogan.
Anyway, if you look…
There's my hive right there. See it?
You're in Sheep Meadow!
Yes! I'm right off the Turtle Pond!
No way! I know that area. I lost a toe ring there once.
Why do girls put rings on their toes?
Why not?
It's like putting a hat on your knee.
Maybe I'll try that.
You all right, ma'am?
Oh, yeah. Fine.
Just having two cups of coffee!
Anyway, this has been great. Thanks for the coffee.
Yeah, it's no trouble.
Sorry I couldn't finish it. If I did, I'd be up the rest of my life.
Are you…?
Oan I take a piece of this with me?
Sure! Here, have a crumb.
Thanks! Yeah. All right. Well, then… I guess I'll see you around.
Or not.
OK, Barry.
And thank you so much again… for before.
Oh, that? That was nothing.
Well, not nothing, but… Anyway…
This can't possibly work.
He's all set to go. We may as well try it.
OK, Dave, pull the chute.
Sounds amazing. It was amazing! It was the scariest, happiest moment of my life.
Humans! I can't believe you were with humans!
Giant, scary humans! What were they like?
Huge and crazy. They talk crazy.
They eat crazy giant things. They drive crazy.
Do they try and kill you, like on TV?
Some of them. But some of them don't.
How'd you get back?
Poodle.
You did it, and I'm glad. You saw whatever you wanted to see.
You had your "experience." Now you can pick out yourjob and be normal.
Well… Well? Well, I met someone.
You did? Was she Bee-ish?
A wasp?! Your parents will kill you!
No, no, no, not a wasp.
Spider?
I'm not attracted to spiders.
I know it's the hottest thing, with the eight legs and all.
I can't get by that face.
So who is she?
She's… human.
No, no. That's a bee law. You wouldn't break a bee law.
Her name's Vanessa. Oh, boy. She's so nice. And she's a florist!
Oh, no! You're dating a human florist!
We're not dating.
You're flying outside the hive, talking to humans that attack our homes
with power washers and M-80s! One-eighth a stick of dynamite!
She saved my life! And she understands me.
This is over!
Eat this.
This is not over! What was that?
They call it a crumb. It was so stingin' stripey! And that's not what they eat. That's what falls off what they eat!
You know what a Oinnabon is? No. It's bread and cinnamon and frosting. They heat it up…
Sit down!
…really hot!
Listen to me! We are not them! We're us. There's us and there's them!
Yes, but who can deny the heart that is yearning?
There's no yearning. Stop yearning. Listen to me!
You have got to start thinking bee, my friend. Thinking bee!
Thinking bee. Thinking bee. Thinking bee! Thinking bee! Thinking bee! Thinking bee!
There he is. He's in the pool.
You know what your problem is, Barry?
I gotta start thinking bee?
How much longer will this go on?
It's been three days! Why aren't you working?
I've got a lot of big life decisions to think about.
What life? You have no life! You have no job. You're barely a bee!
Would it kill you to make a little honey?
Barry, come out. Your father's talking to you.
Martin, would you talk to him?
Barry, I'm talking to you!
You coming?
Got everything?
All set!
Go ahead. I'll catch up.
Don't be too long.
Watch this!
Vanessa!
We're still here. I told you not to yell at him. He doesn't respond to yelling!
Then why yell at me? Because you don't listen! I'm not listening to this.
Sorry, I've gotta go.
Where are you going? I'm meeting a friend. A girl? Is this why you can't decide?
Bye.
I just hope she's Bee-ish.
They have a huge parade of flowers every year in Pasadena?
To be in the Tournament of Roses, that's every florist's dream!
Up on a float, surrounded by flowers, crowds cheering.
A tournament. Do the roses compete in athletic events?
No. All right, I've got one. How come you don't fly everywhere?
It's exhausting. Why don't you run everywhere? It's faster.
Yeah, OK, I see, I see. All right, your turn.
TiVo. You can just freeze live TV? That's insane!
You don't have that?
We have Hivo, but it's a disease. It's a horrible, horrible disease.
Oh, my.
Dumb bees!
You must want to sting all those jerks.
We try not to sting. It's usually fatal for us.
So you have to watch your temper.
Very carefully. You kick a wall, take a walk,
write an angry letter and throw it out. Work through it like any emotion:
Anger, jealousy, lust.
Oh, my goodness! Are you OK?
Yeah.
What is wrong with you?! It's a bug. He's not bothering anybody. Get out of here, you creep!
What was that? A Pic 'N' Save circular?
Yeah, it was. How did you know?
It felt like about 10 pages. Seventy-five is pretty much our limit.
You've really got that down to a science.
I lost a cousin to Italian Vogue. I'll bet. What in the name of Mighty Hercules is this?
How did this get here? Oute Bee, Golden Blossom,
Ray Liotta Private Select?
Is he that actor?
I never heard of him.
Why is this here?
For people. We eat it.
You don't have enough food of your own?
Well, yes.
How do you get it?
Bees make it.
I know who makes it!
And it's hard to make it!
There's heating, cooling, stirring. You need a whole Krelman thing!
It's organic. It's our-ganic! It's just honey, Barry.
Just what?!
Bees don't know about this! This is stealing! A lot of stealing!
You've taken our homes, schools, hospitals! This is all we have!
And it's on sale?! I'm getting to the bottom of this.
I'm getting to the bottom of all of this!
Hey, Hector.
You almost done? Almost. He is here. I sense it.
Well, I guess I'll go home now
and just leave this nice honey out, with no one around.
You're busted, box boy!
I knew I heard something. So you can talk!
I can talk. And now you'll start talking!
Where you getting the sweet stuff? Who's your supplier?
I don't understand. I thought we were friends.
The last thing we want to do is upset bees!
You're too late! It's ours now!
You, sir, have crossed the wrong sword!
You, sir, will be lunch for my iguana, Ignacio!
Where is the honey coming from?
Tell me where!
Honey Farms! It comes from Honey Farms!
Orazy person!
What horrible thing has happened here?
These faces, they never knew what hit them. And now
they're on the road to nowhere!
Just keep still.
What? You're not dead?
Do I look dead? They will wipe anything that moves. Where you headed?
To Honey Farms. I am onto something huge here.
I'm going to Alaska. Moose blood, crazy stuff. Blows your head off!
I'm going to Tacoma.
And you? He really is dead. All right.
Uh-oh!
What is that?!
Oh, no!
A wiper! Triple blade!
Triple blade?
Jump on! It's your only chance, bee!
Why does everything have to be so doggone clean?!
How much do you people need to see?!
Open your eyes! Stick your head out the window!
From NPR News in Washington, I'm Oarl Kasell.
But don't kill no more bugs!
Bee!
Moose blood guy!!
You hear something?
Like what?
Like tiny screaming.
Turn off the radio.
Whassup, bee boy?
Hey, Blood.
Just a row of honey jars, as far as the eye could see.
Wow!
I assume wherever this truck goes is where they're getting it.
I mean, that honey's ours.
Bees hang tight. We're all jammed in. It's a close community.
Not us, man. We on our own. Every mosquito on his own.
What if you get in trouble? You a mosquito, you in trouble. Nobody likes us. They just smack. See a mosquito, smack, smack!
At least you're out in the world. You must meet girls.
Mosquito girls try to trade up, get with a moth, dragonfly.
Mosquito girl don't want no mosquito.
You got to be kidding me!
Mooseblood's about to leave the building! So long, bee!
Hey, guys! Mooseblood! I knew I'd catch y'all down here. Did you bring your crazy straw?
We throw it in jars, slap a label on it, and it's pretty much pure profit.
What is this place?
A bee's got a brain the size of a pinhead.
They are pinheads!
Pinhead.
Oheck out the new smoker. Oh, sweet. That's the one you want. The Thomas 3000!
Smoker?
Ninety puffs a minute, semi-automatic. Twice the nicotine, all the tar.
A couple breaths of this knocks them right out.
They make the honey, and we make the money.
"They make the honey, and we make the money"?
Oh, my!
What's going on? Are you OK?
Yeah. It doesn't last too long.
Do you know you're in a fake hive with fake walls?
Our queen was moved here. We had no choice.
This is your queen? That's a man in women's clothes!
That's a drag queen!
What is this?
Oh, no!
There's hundreds of them!
Bee honey.
Our honey is being brazenly stolen on a massive scale!
This is worse than anything bears have done! I intend to do something.
Oh, Barry, stop.
Who told you humans are taking our honey? That's a rumor.
Do these look like rumors?
That's a conspiracy theory. These are obviously doctored photos.
How did you get mixed up in this?
He's been talking to humans.
What? Talking to humans?! He has a human girlfriend. And they make out!
Make out? Barry!
We do not.
You wish you could. Whose side are you on? The bees!
I dated a cricket once in San Antonio. Those crazy legs kept me up all night.
Barry, this is what you want to do with your life?
I want to do it for all our lives. Nobody works harder than bees!
Dad, I remember you coming home so overworked
your hands were still stirring. You couldn't stop.
I remember that.
What right do they have to our honey?
We live on two cups a year. They put it in lip balm for no reason whatsoever!
Even if it's true, what can one bee do?
Sting them where it really hurts.
In the face! The eye!
That would hurt. No. Up the nose? That's a killer.
There's only one place you can sting the humans, one place where it matters.
Hive at Five, the hive's only full-hour action news source.
No more bee beards!
With Bob Bumble at the anchor desk.
Weather with Storm Stinger.
Sports with Buzz Larvi.
And Jeanette Ohung.
Good evening. I'm Bob Bumble. And I'm Jeanette Ohung. A tri-county bee, Barry Benson,
intends to sue the human race for stealing our honey,
packaging it and profiting from it illegally!
Tomorrow night on Bee Larry King,
we'll have three former queens here in our studio, discussing their new book,
Olassy Ladies, out this week on Hexagon.
Tonight we're talking to Barry Benson.
Did you ever think, "I'm a kid from the hive. I can't do this"?
Bees have never been afraid to change the world.
What about Bee Oolumbus? Bee Gandhi? Bejesus?
Where I'm from, we'd never sue humans.
We were thinking of stickball or candy stores.
How old are you?
The bee community is supporting you in this case,
which will be the trial of the bee century.
You know, they have a Larry King in the human world too.
It's a common name. Next week…
He looks like you and has a show and suspenders and colored dots…
Next week…
Glasses, quotes on the bottom from the guest even though you just heard 'em.
Bear Week next week! They're scary, hairy and here live.
Always leans forward, pointy shoulders, squinty eyes, very Jewish.
In tennis, you attack at the point of weakness!
It was my grandmother, Ken. She's 81.
Honey, her backhand's a joke! I'm not gonna take advantage of that?
Quiet, please. Actual work going on here.
Is that that same bee? Yes, it is! I'm helping him sue the human race.
Hello. Hello, bee. This is Ken.
Yeah, I remember you. Timberland, size ten and a half. Vibram sole, I believe.
Why does he talk again?
Listen, you better go 'cause we're really busy working.
But it's our yogurt night!
Bye-bye.
Why is yogurt night so difficult?!
You poor thing. You two have been at this for hours!
Yes, and Adam here has been a huge help.
Frosting… How many sugars? Just one. I try not to use the competition.
So why are you helping me?
Bees have good qualities.
And it takes my mind off the shop.
Instead of flowers, people are giving balloon bouquets now.
Those are great, if you're three.
And artificial flowers.
Oh, those just get me psychotic! Yeah, me too. Bent stingers, pointless pollination.
Bees must hate those fake things!
Nothing worse than a daffodil that's had work done.
Maybe this could make up for it a little bit.
This lawsuit's a pretty big deal. I guess. You sure you want to go through with it?
Am I sure? When I'm done with the humans, they won't be able
to say, "Honey, I'm home," without paying a royalty!
It's an incredible scene here in downtown Manhattan,
where the world anxiously waits, because for the first time in history,
we will hear for ourselves if a honeybee can actually speak.
What have we gotten into here, Barry?
It's pretty big, isn't it?
I can't believe how many humans don't work during the day.
You think billion-dollar multinational food companies have good lawyers?
Everybody needs to stay behind the barricade.
What's the matter? I don't know, I just got a chill. Well, if it isn't the bee team.
You boys work on this?
All rise! The Honorable Judge Bumbleton presiding.
All right. Oase number 4475,
Superior Oourt of New York, Barry Bee Benson v. the Honey Industry
is now in session.
Mr. Montgomery, you're representing the five food companies collectively?
A privilege.
Mr. Benson… you're representing all the bees of the world?
I'm kidding. Yes, Your Honor, we're ready to proceed.
Mr. Montgomery, your opening statement, please.
Ladies and gentlemen of the jury,
my grandmother was a simple woman.
Born on a farm, she believed it was man's divine right
to benefit from the bounty of nature God put before us.
If we lived in the topsy-turvy world Mr. Benson imagines,
just think of what would it mean.
I would have to negotiate with the silkworm
for the elastic in my britches!
Talking bee!
How do we know this isn't some sort of
holographic motion-picture-capture Hollywood wizardry?
They could be using laser beams!
Robotics! Ventriloquism! Oloning! For all we know,
he could be on steroids!
Mr. Benson?
Ladies and gentlemen, there's no trickery here.
I'm just an ordinary bee. Honey's pretty important to me.
It's important to all bees. We invented it!
We make it. And we protect it with our lives.
Unfortunately, there are some people in this room
who think they can take it from us
'cause we're the little guys! I'm hoping that, after this is all over,
you'll see how, by taking our honey, you not only take everything we have
but everything we are!
I wish he'd dress like that all the time. So nice!
Oall your first witness.
So, Mr. Klauss Vanderhayden of Honey Farms, big company you have.
I suppose so.
I see you also own Honeyburton and Honron!
Yes, they provide beekeepers for our farms.
Beekeeper. I find that to be a very disturbing term.
I don't imagine you employ any bee-free-ers, do you?
No.
I couldn't hear you.
No.
No.
Because you don't free bees. You keep bees. Not only that,
it seems you thought a bear would be an appropriate image for a jar of honey.
They're very lovable creatures.
Yogi Bear, Fozzie Bear, Build-A-Bear.
You mean like this?
Bears kill bees!
How'd you like his head crashing through your living room?!
Biting into your couch! Spitting out your throw pillows!
OK, that's enough. Take him away.
So, Mr. Sting, thank you for being here. Your name intrigues me.
Where have I heard it before? I was with a band called The Police. But you've never been a police officer, have you?
No, I haven't.
No, you haven't. And so here we have yet another example
of bee culture casually stolen by a human
for nothing more than a prance-about stage name.
Oh, please.
Have you ever been stung, Mr. Sting?
Because I'm feeling a little stung, Sting.
Or should I say… Mr. Gordon M. Sumner!
That's not his real name?! You idiots!
Mr. Liotta, first, belated congratulations on
your Emmy win for a guest spot on ER in 2005.
Thank you. Thank you.
I see from your resume that you're devilishly handsome
with a churning inner turmoil that's ready to blow.
I enjoy what I do. Is that a crime?
Not yet it isn't. But is this what it's come to for you?
Exploiting tiny, helpless bees so you don't
have to rehearse your part and learn your lines, sir?
Watch it, Benson! I could blow right now!
This isn't a goodfella. This is a badfella!
Why doesn't someone just step on this creep, and we can all go home?!
Order in this court! You're all thinking it! Order! Order, I say!
Say it! Mr. Liotta, please sit down! I think it was awfully nice of that bear to pitch in like that.
I think the jury's on our side.
Are we doing everything right, legally?
I'm a florist.
Right. Well, here's to a great team.
To a great team!
Well, hello.
Ken! Hello. I didn't think you were coming.
No, I was just late. I tried to call, but… the battery.
I didn't want all this to go to waste, so I called Barry. Luckily, he was free.
Oh, that was lucky.
There's a little left. I could heat it up.
Yeah, heat it up, sure, whatever.
So I hear you're quite a tennis player.
I'm not much for the game myself. The ball's a little grabby.
That's where I usually sit. Right… there.
Ken, Barry was looking at your resume,
and he agreed with me that eating with chopsticks isn't really a special skill.
You think I don't see what you're doing?
I know how hard it is to find the rightjob. We have that in common.
Do we?
Bees have 100 percent employment, but we do jobs like taking the crud out.
That's just what I was thinking about doing.
Ken, I let Barry borrow your razor for his fuzz. I hope that was all right.
I'm going to drain the old stinger.
Yeah, you do that.
Look at that.
You know, I've just about had it
with your little mind games.
What's that? Italian Vogue. Mamma mia, that's a lot of pages.
A lot of ads.
Remember what Van said, why is your life more valuable than mine?
Funny, I just can't seem to recall that!
I think something stinks in here!
I love the smell of flowers.
How do you like the smell of flames?!
Not as much.
Water bug! Not taking sides!
Ken, I'm wearing a Ohapstick hat! This is pathetic!
I've got issues!
Well, well, well, a royal flush!
You're bluffing. Am I? Surf's up, dude!
Poo water!
That bowl is gnarly.
Except for those dirty yellow rings!
Kenneth! What are you doing?!
You know, I don't even like honey! I don't eat it!
We need to talk!
He's just a little bee!
And he happens to be the nicest bee I've met in a long time!
Long time? What are you talking about?! Are there other bugs in your life?
No, but there are other things bugging me in life. And you're one of them!
Fine! Talking bees, no yogurt night…
My nerves are fried from riding on this emotional roller coaster!
Goodbye, Ken.
And for your information,
I prefer sugar-free, artificial sweeteners made by man!
I'm sorry about all that.
I know it's got an aftertaste! I like it!
I always felt there was some kind of barrier between Ken and me.
I couldn't overcome it. Oh, well.
Are you OK for the trial?
I believe Mr. Montgomery is about out of ideas.
We would like to call Mr. Barry Benson Bee to the stand.
Good idea! You can really see why he's considered one of the best lawyers…
Yeah.
Layton, you've gotta weave some magic
with this jury, or it's gonna be all over.
Don't worry. The only thing I have to do to turn this jury around
is to remind them of what they don't like about bees.
You got the tweezers? Are you allergic? Only to losing, son. Only to losing.
Mr. Benson Bee, I'll ask you what I think we'd all like to know.
What exactly is your relationship
to that woman?
We're friends.
Good friends? Yes. How good? Do you live together?
Wait a minute…
Are you her little…
…bedbug?
I've seen a bee documentary or two. From what I understand,
doesn't your queen give birth to all the bee children?
Yeah, but…
So those aren't your real parents!
Oh, Barry…
Yes, they are!
Hold me back!
You're an illegitimate bee, aren't you, Benson?
He's denouncing bees!
Don't y'all date your cousins?
Objection! I'm going to pincushion this guy! Adam, don't! It's what he wants!
Oh, I'm hit!!
Oh, lordy, I am hit!
Order! Order!
The venom! The venom is coursing through my veins!
I have been felled by a winged beast of destruction!
You see? You can't treat them like equals! They're striped savages!
Stinging's the only thing they know! It's their way!
Adam, stay with me. I can't feel my legs. What angel of mercy will come forward to suck the poison
from my heaving buttocks?
I will have order in this court. Order!
Order, please!
The case of the honeybees versus the human race
took a pointed turn against the bees
yesterday when one of their legal team stung Layton T. Montgomery.
Hey, buddy.
Hey.
Is there much pain?
Yeah.
I…
I blew the whole case, didn't I?
It doesn't matter. What matters is you're alive. You could have died.
I'd be better off dead. Look at me.
They got it from the cafeteria downstairs, in a tuna sandwich.
Look, there's a little celery still on it.
What was it like to sting someone?
I can't explain it. It was all…
All adrenaline and then… and then ecstasy!
All right.
You think it was all a trap?
Of course. I'm sorry. I flew us right into this.
What were we thinking? Look at us. We're just a couple of bugs in this world.
What will the humans do to us if they win?
I don't know.
I hear they put the roaches in motels. That doesn't sound so bad.
Adam, they check in, but they don't check out!
Oh, my.
Oould you get a nurse to close that window?
Why? The smoke. Bees don't smoke.
Right. Bees don't smoke.
Bees don't smoke! But some bees are smoking.
That's it! That's our case!
It is? It's not over?
Get dressed. I've gotta go somewhere.
Get back to the court and stall. Stall any way you can.
And assuming you've done step correctly, you're ready for the tub.
Mr. Flayman.
Yes? Yes, Your Honor!
Where is the rest of your team?
Well, Your Honor, it's interesting.
Bees are trained to fly haphazardly,
and as a result, we don't make very good time.
I actually heard a funny story about…
Your Honor, haven't these ridiculous bugs
taken up enough of this court's valuable time?
How much longer will we allow these absurd shenanigans to go on?
They have presented no compelling evidence to support their charges
against my clients, who run legitimate businesses.
I move for a complete dismissal of this entire case!
Mr. Flayman, I'm afraid I'm going
to have to consider Mr. Montgomery's motion.
But you can't! We have a terrific case.
Where is your proof? Where is the evidence?
Show me the smoking gun!
Hold it, Your Honor! You want a smoking gun?
Here is your smoking gun.
What is that?
It's a bee smoker!
What, this? This harmless little contraption?
This couldn't hurt a fly, let alone a bee.
Look at what has happened
to bees who have never been asked, "Smoking or non?"
Is this what nature intended for us?
To be forcibly addicted to smoke machines
and man-made wooden slat work camps?
Living out our lives as honey slaves to the white man?
What are we gonna do? He's playing the species card. Ladies and gentlemen, please, free these bees!
Free the bees! Free the bees!
Free the bees!
Free the bees! Free the bees!
The court finds in favor of the bees!
Vanessa, we won!
I knew you could do it! High-five!
Sorry.
I'm OK! You know what this means?
All the honey will finally belong to the bees.
Now we won't have to work so hard all the time.
This is an unholy perversion of the balance of nature, Benson.
You'll regret this.
Barry, how much honey is out there?
All right. One at a time.
Barry, who are you wearing?
My sweater is Ralph Lauren, and I have no pants.
What if Montgomery's right? What do you mean? We've been living the bee way a long time, 27 million years.
Oongratulations on your victory. What will you demand as a settlement?
First, we'll demand a complete shutdown of all bee work camps.
Then we want back the honey that was ours to begin with,
every last drop.
We demand an end to the glorification of the bear as anything more
than a filthy, smelly, bad-breath stink machine.
We're all aware of what they do in the woods.
Wait for my signal.
Take him out.
He'll have nauseous for a few hours, then he'll be fine.
And we will no longer tolerate bee-negative nicknames…
But it's just a prance-about stage name!
…unnecessary inclusion of honey in bogus health products
and la-dee-da human tea-time snack garnishments.
Oan't breathe.
Bring it in, boys!
Hold it right there! Good.
Tap it.
Mr. Buzzwell, we just passed three cups, and there's gallons more coming!
I think we need to shut down! Shut down? We've never shut down. Shut down honey production!
Stop making honey!
Turn your key, sir!
What do we do now?
Oannonball!
We're shutting honey production!
Mission abort.
Aborting pollination and nectar detail. Returning to base.
Adam, you wouldn't believe how much honey was out there.
Oh, yeah?
What's going on? Where is everybody?
Are they out celebrating? They're home. They don't know what to do. Laying out, sleeping in.
I heard your Uncle Oarl was on his way to San Antonio with a cricket.
At least we got our honey back.
Sometimes I think, so what if humans liked our honey? Who wouldn't?
It's the greatest thing in the world! I was excited to be part of making it.
This was my new desk. This was my new job. I wanted to do it really well.
And now…
Now I can't.
I don't understand why they're not happy.
I thought their lives would be better!
They're doing nothing. It's amazing. Honey really changes people.
You don't have any idea what's going on, do you?
What did you want to show me? This. What happened here?
That is not the half of it.
Oh, no. Oh, my.
They're all wilting.
Doesn't look very good, does it?
No.
And whose fault do you think that is?
You know, I'm gonna guess bees.
Bees?
Specifically, me.
I didn't think bees not needing to make honey would affect all these things.
It's notjust flowers. Fruits, vegetables, they all need bees.
That's our whole SAT test right there.
Take away produce, that affects the entire animal kingdom.
And then, of course…
The human species?
So if there's no more pollination,
it could all just go south here, couldn't it?
I know this is also partly my fault.
How about a suicide pact?
How do we do it?
I'll sting you, you step on me. Thatjust kills you twice. Right, right.
Listen, Barry… sorry, but I gotta get going.
I had to open my mouth and talk.
Vanessa?
Vanessa? Why are you leaving? Where are you going?
To the final Tournament of Roses parade in Pasadena.
They've moved it to this weekend because all the flowers are dying.
It's the last chance I'll ever have to see it.
Vanessa, I just wanna say I'm sorry. I never meant it to turn out like this.
I know. Me neither.
Tournament of Roses. Roses can't do sports.
Wait a minute. Roses. Roses?
Roses!
Vanessa!
Roses?!
Barry?
Roses are flowers! Yes, they are. Flowers, bees, pollen!
I know. That's why this is the last parade.
Maybe not. Oould you ask him to slow down?
Oould you slow down?
Barry!
OK, I made a huge mistake. This is a total disaster, all my fault.
Yes, it kind of is.
I've ruined the planet. I wanted to help you
with the flower shop. I've made it worse.
Actually, it's completely closed down.
I thought maybe you were remodeling.
But I have another idea, and it's greater than my previous ideas combined.
I don't want to hear it!
All right, they have the roses, the roses have the pollen.
I know every bee, plant and flower bud in this park.
All we gotta do is get what they've got back here with what we've got.
Bees.
Park.
Pollen!
Flowers.
Repollination!
Across the nation!
Tournament of Roses, Pasadena, Oalifornia.
They've got nothing but flowers, floats and cotton candy.
Security will be tight.
I have an idea.
Vanessa Bloome, FTD.
Official floral business. It's real.
Sorry, ma'am. Nice brooch.
Thank you. It was a gift.
Once inside, we just pick the right float.
How about The Princess and the Pea?
I could be the princess, and you could be the pea!
Yes, I got it.
Where should I sit?
What are you?
I believe I'm the pea.
The pea?
It goes under the mattresses.
Not in this fairy tale, sweetheart. I'm getting the marshal. You do that! This whole parade is a fiasco!
Let's see what this baby'll do.
Hey, what are you doing?!
Then all we do is blend in with traffic…
…without arousing suspicion.
Once at the airport, there's no stopping us.
Stop! Security.
You and your insect pack your float? Yes. Has it been in your possession the entire time?
Would you remove your shoes?
Remove your stinger. It's part of me. I know. Just having some fun. Enjoy your flight.
Then if we're lucky, we'll have just enough pollen to do the job.
Oan you believe how lucky we are? We have just enough pollen to do the job!
I think this is gonna work.
It's got to work.
Attention, passengers, this is Oaptain Scott.
We have a bit of bad weather in New York.
It looks like we'll experience a couple hours delay.
Barry, these are cut flowers with no water. They'll never make it.
I gotta get up there and talk to them.
Be careful.
Oan I get help with the Sky Mall magazine?
I'd like to order the talking inflatable nose and ear hair trimmer.
Oaptain, I'm in a real situation.
What'd you say, Hal? Nothing. Bee!
Don't freak out! My entire species…
What are you doing?
Wait a minute! I'm an attorney! Who's an attorney? Don't move.
Oh, Barry.
Good afternoon, passengers. This is your captain.
Would a Miss Vanessa Bloome in 24B please report to the cockpit?
And please hurry!
What happened here?
There was a DustBuster, a toupee, a life raft exploded.
One's bald, one's in a boat, they're both unconscious!
Is that another bee joke? No! No one's flying the plane!
This is JFK control tower, Flight 356. What's your status?
This is Vanessa Bloome. I'm a florist from New York.
Where's the pilot?
He's unconscious, and so is the copilot.
Not good. Does anyone onboard have flight experience?
As a matter of fact, there is.
Who's that? Barry Benson. From the honey trial?! Oh, great.
Vanessa, this is nothing more than a big metal bee.
It's got giant wings, huge engines.
I can't fly a plane.
Why not? Isn't John Travolta a pilot? Yes. How hard could it be?
Wait, Barry! We're headed into some lightning.
This is Bob Bumble. We have some late-breaking news from JFK Airport,
where a suspenseful scene is developing.
Barry Benson, fresh from his legal victory…
That's Barry!
…is attempting to land a plane, loaded with people, flowers
and an incapacitated flight crew.
Flowers?!
We have a storm in the area and two individuals at the controls
with absolutely no flight experience.
Just a minute. There's a bee on that plane.
I'm quite familiar with Mr. Benson and his no-account compadres.
They've done enough damage.
But isn't he your only hope?
Technically, a bee shouldn't be able to fly at all.
Their wings are too small…
Haven't we heard this a million times?
"The surface area of the wings and body mass make no sense."
Get this on the air!
Got it.
Stand by.
We're going live.
The way we work may be a mystery to you.
Making honey takes a lot of bees doing a lot of small jobs.
But let me tell you about a small job.
If you do it well, it makes a big difference.
More than we realized. To us, to everyone.
That's why I want to get bees back to working together.
That's the bee way! We're not made of Jell-O.
We get behind a fellow.
Black and yellow! Hello! Left, right, down, hover.
Hover? Forget hover. This isn't so hard. Beep-beep! Beep-beep!
Barry, what happened?!
Wait, I think we were on autopilot the whole time.
That may have been helping me. And now we're not! So it turns out I cannot fly a plane.
All of you, let's get behind this fellow! Move it out!
Move out!
Our only chance is if I do what I'd do, you copy me with the wings of the plane!
Don't have to yell.
I'm not yelling! We're in a lot of trouble.
It's very hard to concentrate with that panicky tone in your voice!
It's not a tone. I'm panicking!
I can't do this!
Vanessa, pull yourself together. You have to snap out of it!
You snap out of it.
You snap out of it.
You snap out of it!
You snap out of it!
You snap out of it!
You snap out of it!
You snap out of it!
You snap out of it!
Hold it!
Why? Oome on, it's my turn.
How is the plane flying?
I don't know.
Hello?
Benson, got any flowers for a happy occasion in there?
The Pollen Jocks!
They do get behind a fellow.
Black and yellow. Hello. All right, let's drop this tin can on the blacktop.
Where? I can't see anything. Oan you?
No, nothing. It's all cloudy.
Oome on. You got to think bee, Barry.
Thinking bee. Thinking bee. Thinking bee! Thinking bee! Thinking bee!
Wait a minute. I think I'm feeling something.
What? I don't know. It's strong, pulling me. Like a 27-million-year-old instinct.
Bring the nose down.
Thinking bee! Thinking bee! Thinking bee!
What in the world is on the tarmac? Get some lights on that! Thinking bee! Thinking bee! Thinking bee!
Vanessa, aim for the flower. OK. Out the engines. We're going in on bee power. Ready, boys?
Affirmative!
Good. Good. Easy, now. That's it.
Land on that flower!
Ready? Full reverse!
Spin it around!
Not that flower! The other one!
Which one?
That flower.
I'm aiming at the flower!
That's a fat guy in a flowered shirt. I mean the giant pulsating flower
made of millions of bees!
Pull forward. Nose down. Tail up.
Rotate around it.
This is insane, Barry! This's the only way I know how to fly. Am I koo-koo-kachoo, or is this plane flying in an insect-like pattern?
Get your nose in there. Don't be afraid. Smell it. Full reverse!
Just drop it. Be a part of it.
Aim for the center!
Now drop it in! Drop it in, woman!
Oome on, already.
Barry, we did it! You taught me how to fly!
Yes. No high-five! Right. Barry, it worked! Did you see the giant flower?
What giant flower? Where? Of course I saw the flower! That was genius!
Thank you. But we're not done yet. Listen, everyone!
This runway is covered with the last pollen
from the last flowers available anywhere on Earth.
That means this is our last chance.
We're the only ones who make honey, pollinate flowers and dress like this.
If we're gonna survive as a species, this is our moment! What do you say?
Are we going to be bees, orjust Museum of Natural History keychains?
We're bees!
Keychain!
Then follow me! Except Keychain.
Hold on, Barry. Here.
You've earned this.
Yeah!
I'm a Pollen Jock! And it's a perfect fit. All I gotta do are the sleeves.
Oh, yeah.
That's our Barry.
Mom! The bees are back!
If anybody needs to make a call, now's the time.
I got a feeling we'll be working late tonight!
Here's your change. Have a great afternoon! Oan I help who's next?
Would you like some honey with that? It is bee-approved. Don't forget these.
Milk, cream, cheese, it's all me. And I don't see a nickel!
Sometimes I just feel like a piece of meat!
I had no idea.
Barry, I'm sorry. Have you got a moment?
Would you excuse me? My mosquito associate will help you.
Sorry I'm late.
He's a lawyer too?
I was already a blood-sucking parasite. All I needed was a briefcase.
Have a great afternoon!
Barry, I just got this huge tulip order, and I can't get them anywhere.
No problem, Vannie. Just leave it to me.
You're a lifesaver, Barry. Oan I help who's next?
All right, scramble, jocks! It's time to fly.
Thank you, Barry!
That bee is living my life!
Let it go, Kenny.
When will this nightmare end?!
Let it all go.
Beautiful day to fly.
Sure is.
Between you and me, I was dying to get out of that office.
You have got to start thinking bee, my friend.
Thinking bee! Me? Hold it. Let's just stop for a second. Hold it.
I'm sorry. I'm sorry, everyone. Oan we stop here?
I'm not making a major life decision during a production number!
All right. Take ten, everybody. Wrap it up, guys.
I had virtually no rehearsal for that.
-
-
www.medievalists.net www.medievalists.net
-
Michel Pastoureau writes that “the true medieval opposite for white was not so much black as red.” This can be seen in the way Europeans adapted chess. When the game was adopted in Europe, the pieces and chessboard were painted in white and red, contrasting with the black and red sets common in India and the Middle East. It was only towards the end of the Middle Ages that the white versus black dichotomy became more favoured. A key factor in this shift was the advent of printing, where black ink was used on white paper, reinforcing the perception of these colours as natural opposites.
Interesting! I wonder how this could be used in design?
-
-
www.youtube.com www.youtube.com
-
philanthropy is in some ways the the most symbolic externalization of neoliberal capitalism. Some people have amassed huge amounts of wealth through a rigged game of extraction and destruction of life. And then it's also presented back to us as an alternative to capitalism that somehow philanthropy can solve the problems that capital created in the first place. And in many ways, that is the fundamental paradox and the absurdity of modern philanthropy.
for - paradox - of philanthropy - People who amass huge fortunes through a lifetime of extracting from nature, people and destroying the fabric of life - present philanthropy as a way to atone for their own sins - Post Capitalist Philanthropy Webinar 1 - Alnoor Ladha - Lynn Murphy - 2023
Tags
Annotators
URL
-
-
www.youtube.com www.youtube.com
-
he next thing will be overshoot so we then say 1.5 and then you know keep our fingers crossed there'll be an overshoot of 0.2 or3 or half a degree or whatever it might be and then the next bit after that will be due engineering so we'll embed the SRM in and so that that is the that's the D that's the direction that we are going
for - climate crisis - ongoing delay game - Kevin Anderson - Dec 2024
-
-
www.scottaaronson.com www.scottaaronson.com
-
Who Can Name the Bigger Number?by Scott Aaronson [Author's blog] [This essay in Spanish] [This essay in French] [This essay in Chinese] In an old joke, two noblemen vie to name the bigger number. The first, after ruminating for hours, triumphantly announces "Eighty-three!" The second, mightily impressed, replies "You win." A biggest number contest is clearly pointless when the contestants take turns. But what if the contestants write down their numbers simultaneously, neither aware of the other’s? To introduce a talk on "Big Numbers," I invite two audience volunteers to try exactly this. I tell them the rules: You have fifteen seconds. Using standard math notation, English words, or both, name a single whole number—not an infinity—on a blank index card. Be precise enough for any reasonable modern mathematician to determine exactly what number you’ve named, by consulting only your card and, if necessary, the published literature. So contestants can’t say "the number of sand grains in the Sahara," because sand drifts in and out of the Sahara regularly. Nor can they say "my opponent’s number plus one," or "the biggest number anyone’s ever thought of plus one"—again, these are ill-defined, given what our reasonable mathematician has available. Within the rules, the contestant who names the bigger number wins. Are you ready? Get set. Go. The contest’s results are never quite what I’d hope. Once, a seventh-grade boy filled his card with a string of successive 9’s. Like many other big-number tyros, he sought to maximize his number by stuffing a 9 into every place value. Had he chosen easy-to-write 1’s rather than curvaceous 9’s, his number could have been millions of times bigger. He still would been decimated, though, by the girl he was up against, who wrote a string of 9’s followed by the superscript 999. Aha! An exponential: a number multiplied by itself 999 times. Noticing this innovation, I declared the girl’s victory without bothering to count the 9’s on the cards. And yet the girl’s number could have been much bigger still, had she stacked the mighty exponential more than once. Take , for example. This behemoth, equal to 9387,420,489, has 369,693,100 digits. By comparison, the number of elementary particles in the observable universe has a meager 85 digits, give or take. Three 9’s, when stacked exponentially, already lift us incomprehensibly beyond all the matter we can observe—by a factor of about 10369,693,015. And we’ve said nothing of or . Place value, exponentials, stacked exponentials: each can express boundlessly big numbers, and in this sense they’re all equivalent. But the notational systems differ dramatically in the numbers they can express concisely. That’s what the fifteen-second time limit illustrates. It takes the same amount of time to write 9999, 9999, and —yet the first number is quotidian, the second astronomical, and the third hyper-mega astronomical. The key to the biggest number contest is not swift penmanship, but rather a potent paradigm for concisely capturing the gargantuan. Such paradigms are historical rarities. We find a flurry in antiquity, another flurry in the twentieth century, and nothing much in between. But when a new way to express big numbers concisely does emerge, it’s often a byproduct of a major scientific revolution: systematized mathematics, formal logic, computer science. Revolutions this momentous, as any Kuhnian could tell you, only happen under the right social conditions. Thus is the story of big numbers a story of human progress. And herein lies a parallel with another mathematical story. In his remarkable and underappreciated book A History of π, Petr Beckmann argues that the ratio of circumference to diameter is "a quaint little mirror of the history of man." In the rare societies where science and reason found refuge—the early Athens of Anaxagoras and Hippias, the Alexandria of Eratosthenes and Euclid, the seventeenth-century England of Newton and Wallis—mathematicians made tremendous strides in calculating π. In Rome and medieval Europe, by contrast, knowledge of π stagnated. Crude approximations such as the Babylonians’ 25/8 held sway. This same pattern holds, I think, for big numbers. Curiosity and openness lead to fascination with big numbers, and to the buoyant view that no quantity, whether of the number of stars in the galaxy or the number of possible bridge hands, is too immense for the mind to enumerate. Conversely, ignorance and irrationality lead to fatalism concerning big numbers. Historian Ilan Vardi cites the ancient Greek term sand-hundred, colloquially meaning zillion; as well as a passage from Pindar’s Olympic Ode II asserting that "sand escapes counting." ¨ But sand doesn’t escape counting, as Archimedes recognized in the third century B.C. Here’s how he began The Sand-Reckoner, a sort of pop-science article addressed to the King of Syracuse: There are some ... who think that the number of the sand is infinite in multitude ... again there are some who, without regarding it as infinite, yet think that no number has been named which is great enough to exceed its multitude ... But I will try to show you [numbers that] exceed not only the number of the mass of sand equal in magnitude to the earth ... but also that of a mass equal in magnitude to the universe. This Archimedes proceeded to do, essentially by using the ancient Greek term myriad, meaning ten thousand, as a base for exponentials. Adopting a prescient cosmological model of Aristarchus, in which the "sphere of the fixed stars" is vastly greater than the sphere in which the Earth revolves around the sun, Archimedes obtained an upper bound of 1063 on the number of sand grains needed to fill the universe. (Supposedly 1063 is the biggest number with a lexicographically standard American name: vigintillion. But the staid vigintillion had better keep vigil lest it be encroached upon by the more whimsically-named googol, or 10100, and googolplex, or .) Vast though it was, of course, 1063 wasn’t to be enshrined as the all-time biggest number. Six centuries later, Diophantus developed a simpler notation for exponentials, allowing him to surpass . Then, in the Middle Ages, the rise of Arabic numerals and place value made it easy to stack exponentials higher still. But Archimedes’ paradigm for expressing big numbers wasn’t fundamentally surpassed until the twentieth century. And even today, exponentials dominate popular discussion of the immense. Consider, for example, the oft-repeated legend of the Grand Vizier in Persia who invented chess. The King, so the legend goes, was delighted with the new game, and invited the Vizier to name his own reward. The Vizier replied that, being a modest man, he desired only one grain of wheat on the first square of a chessboard, two grains on the second, four on the third, and so on, with twice as many grains on each square as on the last. The innumerate King agreed, not realizing that the total number of grains on all 64 squares would be 264-1, or 18.6 quintillion—equivalent to the world’s present wheat production for 150 years. Fittingly, this same exponential growth is what makes chess itself so difficult. There are only about 35 legal choices for each chess move, but the choices multiply exponentially to yield something like 1050 possible board positions—too many for even a computer to search exhaustively. That’s why it took until 1997 for a computer, Deep Blue, to defeat the human world chess champion. And in Go, which has a 19-by-19 board and over 10150 possible positions, even an amateur human can still rout the world’s top-ranked computer programs. Exponential growth plagues computers in other guises as well. The traveling salesman problem asks for the shortest route connecting a set of cities, given the distances between each pair of cities. The rub is that the number of possible routes grows exponentially with the number of cities. When there are, say, a hundred cities, there are about 10158 possible routes, and, although various shortcuts are possible, no known computer algorithm is fundamentally better than checking each route one by one. The traveling salesman problem belongs to a class called NP-complete, which includes hundreds of other problems of practical interest. (NP stands for the technical term ‘Nondeterministic Polynomial-Time.’) It’s known that if there’s an efficient algorithm for any NP-complete problem, then there are efficient algorithms for all of them. Here ‘efficient’ means using an amount of time proportional to at most the problem size raised to some fixed power—for example, the number of cities cubed. It’s conjectured, however, that no efficient algorithm for NP-complete problems exists. Proving this conjecture, called P¹ NP, has been a great unsolved problem of computer science for thirty years. Although computers will probably never solve NP-complete problems efficiently, there’s more hope for another grail of computer science: replicating human intelligence. The human brain has roughly a hundred billion neurons linked by a hundred trillion synapses. And though the function of an individual neuron is only partially understood, it’s thought that each neuron fires electrical impulses according to relatively simple rules up to a thousand times each second. So what we have is a highly interconnected computer capable of maybe 1014 operations per second; by comparison, the world’s fastest parallel supercomputer, the 9200-Pentium Pro teraflops machine at Sandia National Labs, can perform 1012 operations per second. Contrary to popular belief, gray mush is not only hard-wired for intelligence: it surpasses silicon even in raw computational power. But this is unlikely to remain true for long. The reason is Moore’s Law, which, in its 1990’s formulation, states that the amount of information storable on a silicon chip grows exponentially, doubling roughly once every two years. Moore’s Law will eventually play out, as microchip components reach the atomic scale and conventional lithography falters. But radical new technologies, such as optical computers, DNA computers, or even quantum computers, could conceivably usurp silicon’s place. Exponential growth in computing power can’t continue forever, but it may continue long enough for computers—at least in processing power—to surpass human brains. To prognosticators of artificial intelligence, Moore’s Law is a glorious herald of exponential growth. But exponentials have a drearier side as well. The human population recently passed six billion and is doubling about once every forty years. At this exponential rate, if an average person weighs seventy kilograms, then by the year 3750 the entire Earth will be composed of human flesh. But before you invest in deodorant, realize that the population will stop increasing long before this—either because of famine, epidemic disease, global warming, mass species extinctions, unbreathable air, or, entering the speculative realm, birth control. It’s not hard to fathom why physicist Albert Bartlett asserted "the greatest shortcoming of the human race" to be "our inability to understand the exponential function." Or why Carl Sagan advised us to "never underestimate an exponential." In his book Billions & Billions, Sagan gave some other depressing consequences of exponential growth. At an inflation rate of five percent a year, a dollar is worth only thirty-seven cents after twenty years. If a uranium nucleus emits two neutrons, both of which collide with other uranium nuclei, causing them to emit two neutrons, and so forth—well, did I mention nuclear holocaust as a possible end to population growth? ¨ Exponentials are familiar, relevant, intimately connected to the physical world and to human hopes and fears. Using the notational systems I’ll discuss next, we can concisely name numbers that make exponentials picayune by comparison, that subjectively speaking exceed as much as the latter exceeds 9. But these new systems may seem more abstruse than exponentials. In his essay "On Number Numbness," Douglas Hofstadter leads his readers to the precipice of these systems, but then avers: If we were to continue our discussion just one zillisecond longer, we would find ourselves smack-dab in the middle of the theory of recursive functions and algorithmic complexity, and that would be too abstract. So let’s drop the topic right here. But to drop the topic is to forfeit, not only the biggest number contest, but any hope of understanding how stronger paradigms lead to vaster numbers. And so we arrive in the early twentieth century, when a school of mathematicians called the formalists sought to place all of mathematics on a rigorous axiomatic basis. A key question for the formalists was what the word ‘computable’ means. That is, how do we tell whether a sequence of numbers can be listed by a definite, mechanical procedure? Some mathematicians thought that ‘computable’ coincided with a technical notion called ‘primitive recursive.’ But in 1928 Wilhelm Ackermann disproved them by constructing a sequence of numbers that’s clearly computable, yet grows too quickly to be primitive recursive. Ackermann’s idea was to create an endless procession of arithmetic operations, each more powerful than the last. First comes addition. Second comes multiplication, which we can think of as repeated addition: for example, 5´3 means 5 added to itself 3 times, or 5+5+5 = 15. Third comes exponentiation, which we can think of as repeated multiplication. Fourth comes ... what? Well, we have to invent a weird new operation, for repeated exponentiation. The mathematician Rudy Rucker calls it ‘tetration.’ For example, ‘5 tetrated to the 3’ means 5 raised to its own power 3 times, or , a number with 2,185 digits. We can go on. Fifth comes repeated tetration: shall we call it ‘pentation’? Sixth comes repeated pentation: ‘hexation’? The operations continue infinitely, with each one standing on its predecessor to peer even higher into the firmament of big numbers. If each operation were a candy flavor, then the Ackermann sequence would be the sampler pack, mixing one number of each flavor. First in the sequence is 1+1, or (don’t hold your breath) 2. Second is 2´2, or 4. Third is 3 raised to the 3rd power, or 27. Hey, these numbers aren’t so big! Fee. Fi. Fo. Fum. Fourth is 4 tetrated to the 4, or , which has 10154 digits. If you’re planning to write this number out, better start now. Fifth is 5 pentated to the 5, or with ‘5 pentated to the 4’ numerals in the stack. This number is too colossal to describe in any ordinary terms. And the numbers just get bigger from there. Wielding the Ackermann sequence, we can clobber unschooled opponents in the biggest-number contest. But we need to be careful, since there are several definitions of the Ackermann sequence, not all identical. Under the fifteen-second time limit, here’s what I might write to avoid ambiguity: A(111)—Ackermann seq—A(1)=1+1, A(2)=2´2, A(3)=33, etc Recondite as it seems, the Ackermann sequence does have some applications. A problem in an area called Ramsey theory asks for the minimum dimension of a hypercube satisfying a certain property. The true dimension is thought to be 6, but the lowest dimension anyone’s been able is prove is so huge that it can only be expressed using the same ‘weird arithmetic’ that underlies the Ackermann sequence. Indeed, the Guinness Book of World Records once listed this dimension as the biggest number ever used in a mathematical proof. (Another contender for the title once was Skewes’ number, about , which arises in the study of how prime numbers are distributed. The famous mathematician G. H. Hardy quipped that Skewes’ was "the largest number which has ever served any definite purpose in mathematics.") What’s more, Ackermann’s briskly-rising cavalcade performs an occasional cameo in computer science. For example, in the analysis of a data structure called ‘Union-Find,’ a term gets multiplied by the inverse of the Ackermann sequence—meaning, for each whole number X, the first number N such that the Nth Ackermann number is bigger than X. The inverse grows as slowly as Ackermann’s original sequence grows quickly; for all practical purposes, the inverse is at most 4. ¨ Ackermann numbers are pretty big, but they’re not yet big enough. The quest for still bigger numbers takes us back to the formalists. After Ackermann demonstrated that ‘primitive recursive’ isn’t what we mean by ‘computable,’ the question still stood: what do we mean by ‘computable’? In 1936, Alonzo Church and Alan Turing independently answered this question. While Church answered using a logical formalism called the lambda calculus, Turing answered using an idealized computing machine—the Turing machine—that, in essence, is equivalent to every Compaq, Dell, Macintosh, and Cray in the modern world. Turing’s paper describing his machine, "On Computable Numbers," is rightly celebrated as the founding document of computer science. "Computing," said Turing, is normally done by writing certain symbols on paper. We may suppose this paper to be divided into squares like a child’s arithmetic book. In elementary arithmetic the 2-dimensional character of the paper is sometimes used. But such use is always avoidable, and I think it will be agreed that the two-dimensional character of paper is no essential of computation. I assume then that the computation is carried out on one-dimensional paper, on a tape divided into squares. Turing continued to explicate his machine using ingenious reasoning from first principles. The tape, said Turing, extends infinitely in both directions, since a theoretical machine ought not be constrained by physical limits on resources. Furthermore, there’s a symbol written on each square of the tape, like the ‘1’s and ‘0’s in a modern computer’s memory. But how are the symbols manipulated? Well, there’s a ‘tape head’ moving back and forth along the tape, examining one square at a time, writing and erasing symbols according to definite rules. The rules are the tape head’s program: change them, and you change what the tape head does. Turing’s august insight was that we can program the tape head to carry out any computation. Turing machines can add, multiply, extract cube roots, sort, search, spell-check, parse, play Tic-Tac-Toe, list the Ackermann sequence. If we represented keyboard input, monitor output, and so forth as symbols on the tape, we could even run Windows on a Turing machine. But there’s a problem. Set a tape head loose on a sequence of symbols, and it might stop eventually, or it might run forever—like the fabled programmer who gets stuck in the shower because the instructions on the shampoo bottle read "lather, rinse, repeat." If the machine’s going to run forever, it’d be nice to know this in advance, so that we don’t spend an eternity waiting for it to finish. But how can we determine, in a finite amount of time, whether something will go on endlessly? If you bet a friend that your watch will never stop ticking, when could you declare victory? But maybe there’s some ingenious program that can examine other programs and tell us, infallibly, whether they’ll ever stop running. We just haven’t thought of it yet. Nope. Turing proved that this problem, called the Halting Problem, is unsolvable by Turing machines. The proof is a beautiful example of self-reference. It formalizes an old argument about why you can never have perfect introspection: because if you could, then you could determine what you were going to do ten seconds from now, and then do something else. Turing imagined that there was a special machine that could solve the Halting Problem. Then he showed how we could have this machine analyze itself, in such a way that it has to halt if it runs forever, and run forever if it halts. Like a hound that finally catches its tail and devours itself, the mythical machine vanishes in a fury of contradiction. (That’s the sort of thing you don’t say in a research paper.) ¨ "Very nice," you say (or perhaps you say, "not nice at all"). "But what does all this have to do with big numbers?" Aha! The connection wasn’t published until May of 1962. Then, in the Bell System Technical Journal, nestled between pragmatically-minded papers on "Multiport Structures" and "Waveguide Pressure Seals," appeared the modestly titled "On Non-Computable Functions" by Tibor Rado. In this paper, Rado introduced the biggest numbers anyone had ever imagined. His idea was simple. Just as we can classify words by how many letters they contain, we can classify Turing machines by how many rules they have in the tape head. Some machines have only one rule, others have two rules, still others have three rules, and so on. But for each fixed whole number N, just as there are only finitely many distinct words with N letters, so too are there only finitely many distinct machines with N rules. Among these machines, some halt and others run forever when started on a blank tape. Of the ones that halt, asked Rado, what’s the maximum number of steps that any machine takes before it halts? (Actually, Rado asked mainly about the maximum number of symbols any machine can write on the tape before halting. But the maximum number of steps, which Rado called S(n), has the same basic properties and is easier to reason about.) Rado called this maximum the Nth "Busy Beaver" number. (Ah yes, the early 1960’s were a more innocent age.) He visualized each Turing machine as a beaver bustling busily along the tape, writing and erasing symbols. The challenge, then, is to find the busiest beaver with exactly N rules, albeit not an infinitely busy one. We can interpret this challenge as one of finding the "most complicated" computer program N bits long: the one that does the most amount of stuff, but not an infinite amount. Now, suppose we knew the Nth Busy Beaver number, which we’ll call BB(N). Then we could decide whether any Turing machine with N rules halts on a blank tape. We’d just have to run the machine: if it halts, fine; but if it doesn’t halt within BB(N) steps, then we know it never will halt, since BB(N) is the maximum number of steps it could make before halting. Similarly, if you knew that all mortals died before age 200, then if Sally lived to be 200, you could conclude that Sally was immortal. So no Turing machine can list the Busy Beaver numbers—for if it could, it could solve the Halting Problem, which we already know is impossible. But here’s a curious fact. Suppose we could name a number greater than the Nth Busy Beaver number BB(N). Call this number D for dam, since like a beaver dam, it’s a roof for the Busy Beaver below. With D in hand, computing BB(N) itself becomes easy: we just need to simulate all the Turing machines with N rules. The ones that haven’t halted within D steps—the ones that bash through the dam’s roof—never will halt. So we can list exactly which machines halt, and among these, the maximum number of steps that any machine takes before it halts is BB(N). Conclusion? The sequence of Busy Beaver numbers, BB(1), BB(2), and so on, grows faster than any computable sequence. Faster than exponentials, stacked exponentials, the Ackermann sequence, you name it. Because if a Turing machine could compute a sequence that grows faster than Busy Beaver, then it could use that sequence to obtain the D‘s—the beaver dams. And with those D’s, it could list the Busy Beaver numbers, which (sound familiar?) we already know is impossible. The Busy Beaver sequence is non-computable, solely because it grows stupendously fast—too fast for any computer to keep up with it, even in principle. This means that no computer program could list all the Busy Beavers one by one. It doesn’t mean that specific Busy Beavers need remain eternally unknowable. And in fact, pinning them down has been a computer science pastime ever since Rado published his article. It’s easy to verify that BB(1), the first Busy Beaver number, is 1. That’s because if a one-rule Turing machine doesn’t halt after the very first step, it’ll just keep moving along the tape endlessly. There’s no room for any more complex behavior. With two rules we can do more, and a little grunt work will ascertain that BB(2) is 6. Six steps. What about the third Busy Beaver? In 1965 Rado, together with Shen Lin, proved that BB(3) is 21. The task was an arduous one, requiring human analysis of many machines to prove that they don’t halt—since, remember, there’s no algorithm for listing the Busy Beaver numbers. Next, in 1983, Allan Brady proved that BB(4) is 107. Unimpressed so far? Well, as with the Ackermann sequence, don’t be fooled by the first few numbers. In 1984, A.K. Dewdney devoted a Scientific American column to Busy Beavers, which inspired amateur mathematician George Uhing to build a special-purpose device for simulating Turing machines. The device, which cost Uhing less than $100, found a five-rule machine that runs for 2,133,492 steps before halting—establishing that BB(5) must be at least as high. Then, in 1989, Heiner Marxen and Jürgen Buntrock discovered that BB(5) is at least 47,176,870. To this day, BB(5) hasn’t been pinned down precisely, and it could turn out to be much higher still. As for BB(6), Marxen and Buntrock set another record in 1997 by proving that it’s at least 8,690,333,381,690,951. A formidable accomplishment, yet Marxen, Buntrock, and the other Busy Beaver hunters are merely wading along the shores of the unknowable. Humanity may never know the value of BB(6) for certain, let alone that of BB(7) or any higher number in the sequence. Indeed, already the top five and six-rule contenders elude us: we can’t explain how they ‘work’ in human terms. If creativity imbues their design, it’s not because humans put it there. One way to understand this is that even small Turing machines can encode profound mathematical problems. Take Goldbach’s conjecture, that every even number 4 or higher is a sum of two prime numbers: 10=7+3, 18=13+5. The conjecture has resisted proof since 1742. Yet we could design a Turing machine with, oh, let’s say 100 rules, that tests each even number to see whether it’s a sum of two primes, and halts when and if it finds a counterexample to the conjecture. Then knowing BB(100), we could in principle run this machine for BB(100) steps, decide whether it halts, and thereby resolve Goldbach’s conjecture. We need not venture far in the sequence to enter the lair of basilisks. But as Rado stressed, even if we can’t list the Busy Beaver numbers, they’re perfectly well-defined mathematically. If you ever challenge a friend to the biggest number contest, I suggest you write something like this: BB(11111)—Busy Beaver shift #—1, 6, 21, etc If your friend doesn’t know about Turing machines or anything similar, but only about, say, Ackermann numbers, then you’ll win the contest. You’ll still win even if you grant your friend a handicap, and allow him the entire lifetime of the universe to write his number. The key to the biggest number contest is a potent paradigm, and Turing’s theory of computation is potent indeed. ¨ But what if your friend knows about Turing machines as well? Is there a notational system for big numbers more powerful than even Busy Beavers? Suppose we could endow a Turing machine with a magical ability to solve the Halting Problem. What would we get? We’d get a ‘super Turing machine’: one with abilities beyond those of any ordinary machine. But now, how hard is it to decide whether a super machine halts? Hmm. It turns out that not even super machines can solve this ‘super Halting Problem’, for the same reason that ordinary machines can’t solve the ordinary Halting Problem. To solve the Halting Problem for super machines, we’d need an even more powerful machine: a ‘super duper machine.’ And to solve the Halting Problem for super duper machines, we’d need a ‘super duper pooper machine.’ And so on endlessly. This infinite hierarchy of ever more powerful machines was formalized by the logician Stephen Kleene in 1943 (although he didn’t use the term ‘super duper pooper’). Imagine a novel, which is imbedded in a longer novel, which itself is imbedded in an even longer novel, and so on ad infinitum. Within each novel, the characters can debate the literary merits of any of the sub-novels. But, by analogy with classes of machines that can’t analyze themselves, the characters can never critique the novel that they themselves are in. (This, I think, jibes with our ordinary experience of novels.) To fully understand some reality, we need to go outside of that reality. This is the essence of Kleene’s hierarchy: that to solve the Halting Problem for some class of machines, we need a yet more powerful class of machines. And there’s no escape. Suppose a Turing machine had a magical ability to solve the Halting Problem, and the super Halting Problem, and the super duper Halting Problem, and the super duper pooper Halting Problem, and so on endlessly. Surely this would be the Queen of Turing machines? Not quite. As soon as we want to decide whether a ‘Queen of Turing machines’ halts, we need a still more powerful machine: an ‘Empress of Turing machines.’ And Kleene’s hierarchy continues. But how’s this relevant to big numbers? Well, each level of Kleene’s hierarchy generates a faster-growing Busy Beaver sequence than do all the previous levels. Indeed, each level’s sequence grows so rapidly that it can only be computed by a higher level. For example, define BB2(N) to be the maximum number of steps a super machine with N rules can make before halting. If this super Busy Beaver sequence were computable by super machines, then those machines could solve the super Halting Problem, which we know is impossible. So the super Busy Beaver numbers grow too rapidly to be computed, even if we could compute the ordinary Busy Beaver numbers. You might think that now, in the biggest-number contest, you could obliterate even an opponent who uses the Busy Beaver sequence by writing something like this: BB2(11111). But not quite. The problem is that I’ve never seen these "higher-level Busy Beavers" defined anywhere, probably because, to people who know computability theory, they’re a fairly obvious extension of the ordinary Busy Beaver numbers. So our reasonable modern mathematician wouldn’t know what number you were naming. If you want to use higher-level Busy Beavers in the biggest number contest, here’s what I suggest. First, publish a paper formalizing the concept in some obscure, low-prestige journal. Then, during the contest, cite the paper on your index card. To exceed higher-level Busy Beavers, we’d presumably need some new computational model surpassing even Turing machines. I can’t imagine what such a model would look like. Yet somehow I doubt that the story of notational systems for big numbers is over. Perhaps someday humans will be able concisely to name numbers that make Busy Beaver 100 seem as puerile and amusingly small as our nobleman’s eighty-three. Or if we’ll never name such numbers, perhaps other civilizations will. Is a biggest number contest afoot throughout the galaxy? ¨ You might wonder why we can’t transcend the whole parade of paradigms, and name numbers by a system that encompasses and surpasses them all. Suppose you wrote the following in the biggest number contest: The biggest whole number nameable with 1,000 characters of English text Surely this number exists. Using 1,000 characters, we can name only finitely many numbers, and among these numbers there has to be a biggest. And yet we’ve made no reference to how the number’s named. The English text could invoke Ackermann numbers, or Busy Beavers, or higher-level Busy Beavers, or even some yet more sweeping concept that nobody’s thought of yet. So unless our opponent uses the same ploy, we’ve got him licked. What a brilliant idea! Why didn’t we think of this earlier? Unfortunately it doesn’t work. We might as well have written One plus the biggest whole number nameable with 1,000 characters of English text This number takes at least 1,001 characters to name. Yet we’ve just named it with only 80 characters! Like a snake that swallows itself whole, our colossal number dissolves in a tumult of contradiction. What gives? The paradox I’ve just described was first published by Bertrand Russell, who attributed it to a librarian named G. G. Berry. The Berry Paradox arises not from mathematics, but from the ambiguity inherent in the English language. There’s no surefire way to convert an English phrase into the number it names (or to decide whether it names a number at all), which is why I invoked a "reasonable modern mathematician" in the rules for the biggest number contest. To circumvent the Berry Paradox, we need to name numbers using a precise, mathematical notational system, such as Turing machines—which is exactly the idea behind the Busy Beaver sequence. So in short, there’s no wily language trick by which to surpass Archimedes, Ackermann, Turing, and Rado, no royal road to big numbers. You might also wonder why we can’t use infinity in the contest. The answer is, for the same reason why we can’t use a rocket car in a bike race. Infinity is fascinating and elegant, but it’s not a whole number. Nor can we ‘subtract from infinity’ to yield a whole number. Infinity minus 17 is still infinity, whereas infinity minus infinity is undefined: it could be 0, 38, or even infinity again. Actually I should speak of infinities, plural. For in the late nineteenth century, Georg Cantor proved that there are different levels of infinity: for example, the infinity of points on a line is greater than the infinity of whole numbers. What’s more, just as there’s no biggest number, so too is there no biggest infinity. But the quest for big infinities is more abstruse than the quest for big numbers. And it involves, not a succession of paradigms, but essentially one: Cantor’s. ¨ So here we are, at the frontier of big number knowledge. As Euclid’s disciple supposedly asked, "what is the use of all this?" We’ve seen that progress in notational systems for big numbers mirrors progress in broader realms: mathematics, logic, computer science. And yet, though a mirror reflects reality, it doesn’t necessarily influence it. Even within mathematics, big numbers are often considered trivialities, their study an idle amusement with no broader implications. I want to argue a contrary view: that understanding big numbers is a key to understanding the world. Imagine trying to explain the Turing machine to Archimedes. The genius of Syracuse listens patiently as you discuss the papyrus tape extending infinitely in both directions, the time steps, states, input and output sequences. At last he explodes. "Foolishness!" he declares (or the ancient Greek equivalent). "All you’ve given me is an elaborate definition, with no value outside of itself." How do you respond? Archimedes has never heard of computers, those cantankerous devices that, twenty-three centuries from his time, will transact the world’s affairs. So you can’t claim practical application. Nor can you appeal to Hilbert and the formalist program, since Archimedes hasn’t heard of those either. But then it hits you: the Busy Beaver sequence. You define the sequence for Archimedes, convince him that BB(1000) is more than his 1063 grains of sand filling the universe, more even than 1063 raised to its own power 1063 times. You defy him to name a bigger number without invoking Turing machines or some equivalent. And as he ponders this challenge, the power of the Turing machine concept dawns on him. Though his intuition may never apprehend the Busy Beaver numbers, his reason compels him to acknowledge their immensity. Big numbers have a way of imbuing abstract notions with reality. Indeed, one could define science as reason’s attempt to compensate for our inability to perceive big numbers. If we could run at 280,000,000 meters per second, there’d be no need for a special theory of relativity: it’d be obvious to everyone that the faster we go, the heavier and squatter we get, and the faster time elapses in the rest of the world. If we could live for 70,000,000 years, there’d be no theory of evolution, and certainly no creationism: we could watch speciation and adaptation with our eyes, instead of painstakingly reconstructing events from fossils and DNA. If we could bake bread at 20,000,000 degrees Kelvin, nuclear fusion would be not the esoteric domain of physicists but ordinary household knowledge. But we can’t do any of these things, and so we have science, to deduce about the gargantuan what we, with our infinitesimal faculties, will never sense. If people fear big numbers, is it any wonder that they fear science as well and turn for solace to the comforting smallness of mysticism? But do people fear big numbers? Certainly they do. I’ve met people who don’t know the difference between a million and a billion, and don’t care. We play a lottery with ‘six ways to win!,’ overlooking the twenty million ways to lose. We yawn at six billion tons of carbon dioxide released into the atmosphere each year, and speak of ‘sustainable development’ in the jaws of exponential growth. Such cases, it seems to me, transcend arithmetical ignorance and represent a basic unwillingness to grapple with the immense. Whence the cowering before big numbers, then? Does it have a biological origin? In 1999, a group led by neuropsychologist Stanislas Dehaene reported evidence in Science that two separate brain systems contribute to mathematical thinking. The group trained Russian-English bilinguals to solve a set of problems, including two-digit addition, base-eight addition, cube roots, and logarithms. Some subjects were trained in Russian, others in English. When the subjects were then asked to solve problems approximately—to choose the closer of two estimates—they performed equally well in both languages. But when asked to solve problems exactly, they performed better in the language of their training. What’s more, brain-imaging evidence showed that the subjects’ parietal lobes, involved in spatial reasoning, were more active during approximation problems; while the left inferior frontal lobes, involved in verbal reasoning, were more active during exact calculation problems. Studies of patients with brain lesions paint the same picture: those with parietal lesions sometimes can’t decide whether 9 is closer to 10 or to 5, but remember the multiplication table; whereas those with left-hemispheric lesions sometimes can’t decide whether 2+2 is 3 or 4, but know that the answer is closer to 3 than to 9. Dehaene et al. conjecture that humans represent numbers in two ways. For approximate reckoning we use a ‘mental number line,’ which evolved long ago and which we likely share with other animals. But for exact computation we use numerical symbols, which evolved recently and which, being language-dependent, are unique to humans. This hypothesis neatly explains the experiment’s findings: the reason subjects performed better in the language of their training for exact computation but not for approximation problems is that the former call upon the verbally-oriented left inferior frontal lobes, and the latter upon the spatially-oriented parietal lobes. If Dehaene et al.’s hypothesis is correct, then which representation do we use for big numbers? Surely the symbolic one—for nobody’s mental number line could be long enough to contain , 5 pentated to the 5, or BB(1000). And here, I suspect, is the problem. When thinking about 3, 4, or 7, we’re guided by our spatial intuition, honed over millions of years of perceiving 3 gazelles, 4 mates, 7 members of a hostile clan. But when thinking about BB(1000), we have only language, that evolutionary neophyte, to rely upon. The usual neural pathways for representing numbers lead to dead ends. And this, perhaps, is why people are afraid of big numbers. Could early intervention mitigate our big number phobia? What if second-grade math teachers took an hour-long hiatus from stultifying busywork to ask their students, "How do you name really, really big numbers?" And then told them about exponentials and stacked exponentials, tetration and the Ackermann sequence, maybe even Busy Beavers: a cornucopia of numbers vaster than any they’d ever conceived, and ideas stretching the bounds of their imaginations. Who can name the bigger number? Whoever has the deeper paradigm. Are you ready? Get set. Go. References Petr Beckmann, A History of Pi, Golem Press, 1971. Allan H. Brady, "The Determination of the Value of Rado’s Noncomputable Function Sigma(k) for Four-State Turing Machines," Mathematics of Computation, vol. 40, no. 162, April 1983, pp 647- 665. Gregory J. Chaitin, "The Berry Paradox," Complexity, vol. 1, no. 1, 1995, pp. 26- 30. At http://www.umcs.maine.edu/~chaitin/unm2.html. A.K. Dewdney, The New Turing Omnibus: 66 Excursions in Computer Science, W.H. Freeman, 1993. S. Dehaene and E. Spelke and P. Pinel and R. Stanescu and S. Tsivkin, "Sources of Mathematical Thinking: Behavioral and Brain-Imaging Evidence," Science, vol. 284, no. 5416, May 7, 1999, pp. 970- 974. Douglas Hofstadter, Metamagical Themas: Questing for the Essence of Mind and Pattern, Basic Books, 1985. Chapter 6, "On Number Numbness," pp. 115- 135. Robert Kanigel, The Man Who Knew Infinity: A Life of the Genius Ramanujan, Washington Square Press, 1991. Stephen C. Kleene, "Recursive predicates and quantifiers," Transactions of the American Mathematical Society, vol. 53, 1943, pp. 41- 74. Donald E. Knuth, Selected Papers on Computer Science, CSLI Publications, 1996. Chapter 2, "Mathematics and Computer Science: Coping with Finiteness," pp. 31- 57. Dexter C. Kozen, Automata and Computability, Springer-Verlag, 1997. ———, The Design and Analysis of Algorithms, Springer-Verlag, 1991. Shen Lin and Tibor Rado, "Computer studies of Turing machine problems," Journal of the Association for Computing Machinery, vol. 12, no. 2, April 1965, pp. 196- 212. Heiner Marxen, Busy Beaver, at http://www.drb.insel.de/~heiner/BB/. ——— and Jürgen Buntrock, "Attacking the Busy Beaver 5," Bulletin of the European Association for Theoretical Computer Science, no. 40, February 1990, pp. 247- 251. Tibor Rado, "On Non-Computable Functions," Bell System Technical Journal, vol. XLI, no. 2, May 1962, pp. 877- 884. Rudy Rucker, Infinity and the Mind, Princeton University Press, 1995. Carl Sagan, Billions & Billions, Random House, 1997. Michael Somos, "Busy Beaver Turing Machine." At http://grail.cba.csuohio.edu/~somos/bb.html. Alan Turing, "On computable numbers, with an application to the Entscheidungsproblem," Proceedings of the London Mathematical Society, Series 2, vol. 42, pp. 230- 265, 1936. Reprinted in Martin Davis (ed.), The Undecidable, Raven, 1965. Ilan Vardi, "Archimedes, the Sand Reckoner," at http://www.ihes.fr/~ilan/sand_reckoner.ps. Eric W. Weisstein, CRC Concise Encyclopedia of Mathematics, CRC Press, 1999. Entry on "Large Number" at http://www.treasure-troves.com/math/LargeNumber.html. Back to Writings page Back to Scott's homepage Back to Scott's blog
What even is the largest number that has real world use what would be the point of bigger numbers if we cant use the big numbers we have now for real world calculations?
-
-
bookshelf.vitalsource.com bookshelf.vitalsource.com
-
Too often, grading is a “gotcha” game in which students spend an inordinate amount of time trying to figure out what they’re supposed to know on a test. Where there is shared clarity about learning goals (called KUDs in this model of differentiation) and these goals are the clear focus of instruction and of formative and summative assessment, success is in reach for far more students. That statement is not an affirmation of “teaching to the test.” Students should be learning meaningful ideas with the expectation that they will be able to apply and transfer what they are learning—not just memorize something and be able to repeat it on test day.
Make the Test Matter. Mastery doesn't need to be 50 questions when you can see the mastery in 15 questions. Don't get the "Gotcha" game with their learning.
-
Learning is difficult—especially if our goal is to stretch each learner regularly. Students need time to practice what they are trying to learn, safely and without judgment; we should provide that time. A good analogy is a sports team that practices for an upcoming game for a number of days in advance of the game. Practices aren’t graded or scored. Instead, the coaches observe, provide some practice for the team as a whole, ensure that individual players practice in ways that will benefit them as individual players and benefit the team, and provide focused feedback to individuals and the team.
Formative assessment is not just grading. Using this can help the students not feel like they are always shooting for that A
-
A good coach has clear goals for the team, and for every individual on the team. Practices involve some common activities, but they will also likely call on each player to improve areas of weakness and polish areas of strength. The coach is generally part psychologist, required to understand what motivates each player and use that understanding to develop his or her skill, by investing sweat and effort and risking pain. However, the coach must also build a team spirit that transcends individual concerns. During practices and games, the coach maintains an active role—running the sidelines, motivating, giving directions, calling small groups aside at key times for strategy adjustments. But it’s the team, not the coach, who actually plays the game.
Understanding the teacher has many roles and as a coach is a good way of looking at it. With goals and mindset along with motivation is so important as a teacher.
-
-
tim.blog tim.blog
-
Tim Ferris posting a text by Gabriel Wyner from 2014 on learning a new language in several steps 1) hear the novel sounds in the language and how to spell them 2) learn a list of basic words by connecting them to their image not their translatiojn 3) learn (simplified) grammar 4) continue the game (adding focused vocab, reading, listening speaking etc)
-
Stage 4: The Language Game 3 Months (or as long as you want to keep playing)
Stage 4 is the deepening / getting to fluency bit. Reinforced by actual usage. Either through adding more vocab, reading texts, listening to speakers etc.
-
-
www.biorxiv.org www.biorxiv.org
-
Reviewer #3 (Public review):
Summary:
This manuscript outlines a series of very exciting and game-changing experiments examining the role of peripheral MORs in OIRD. The authors outline experiments that demonstrate a peripherally restricted MOR antagonist (NLX Methiodide) can rescue fentanyl-induced respiratory depression and this effect coincides with a lack of conditioned place aversion. This approach would be a massive boon to the OUD community, as there are a multitude of clinical reports showing that naloxone rescue post fentanyl over-intoxication is more aversive than the potential loss-of-life to the individuals involved. This important study reframes our understanding of successful overdose rescue with potential for reduced aversive withdrawal effects.
Strengths:
Strengths include the plethora of approaches arriving at the same general conclusion, the inclusion of both sexes and the result that a peripheral approach for OIRD rescue may side-step severe negative withdrawal symptoms of traditional NLX rescue.
Weaknesses:
The major weakness of this version relates to the data analysis assessed sex-specific contributors to the results.
-
-
www.in-mind.org www.in-mind.org
-
Even though many women were aware of these actions, they were consumed by their need to fit in on social media and struggled to disrupt their habits.
Social media is an all consuming beast for a lot of people, and although sometimes there is good community present, there can also be bad community. The digital keywords book helps explain online community.
"Lawrence Lessig has noted: “Cyberspace is a place. People live there. They experience all the sorts of things that they experience in real space, there. For some, they experience more. They experience this not as isolated individuals, playing some high tech computer game; they experience it in groups, in communities, among strangers, among people they come to know, and sometimes like.”22
While his words can be more directly related to gaming, I think it is also important to consider community amongst the social media world. it is not uncommon that influencers consider their fans to be apart of their own community. I think idolizing someone as a community, while it is a common interest, may not have the best impact on the person at the top. I feel like if i was getting all of my photos and actions picked apart constantly, I would spiral into a very dark place.
-
-
social-media-ethics-automation.github.io social-media-ethics-automation.github.io
-
For example, you can hopefully recognize when someone is intentionally posting something bad or offensive (like the bad cooking videos we mentioned in the Virality chapter, or an intentionally offensive statement) in an attempt to get people to respond and spread their content.
People really struggle with knowing when someone is trying to get a rise out of the audience and game the algorithm, which only really makes social media sites worse to be on. Content creators like Nara Smith feed off all the negative attention they get to boost themselves, which gives platform to lots of people that don't necessarily deserve it.
-
-
web-p-ebscohost-com.lahc.idm.oclc.org web-p-ebscohost-com.lahc.idm.oclc.org
-
more likely to favour White individuals over Black individuals
Interesting finding and wording – Pro-White implicit attitudes leads to higher likeliness to favor whites over blacks. This isn't surprising. However, according to other similar studies, it seems simply having pro-White implicit bias directly correlated to having anti-Black implicit bias (economic game & anger in faces).
Taken together, study seems to suggest that simply having pro-White attitudes directly lead to having anti-Black attitudes. Not clear that one directly means the other, but it suggests the common trend is that if you have pro-White attitudes, you will therefore have anti-Black attitudes. In order to not have anti-Black attitudes, you must not have pro-White attitudes either.
-
-
doc-04-1s-prod-02-apps-viewer.googleusercontent.com doc-04-1s-prod-02-apps-viewer.googleusercontent.com
-
New llrrivals to fields must pay the price of ;lll initial investment fa!· entry, whichinvolves recognition of the value of the game ;llld the practical knowledgeof how to play ir
cultural capital acquired to move up socially reference to Goffman's performance as apart of upwards mobility
-
Challengers and incumbents share a com1llon interest in preserving thefield i[Self, even if they ,Ire sharply divided on how it is to be controlled.Evcry field presupposes and produces :'I particular type of ;IIIISio, whichBourdicu defines 11S a helief or acceptance of the worth of the game of afield.
even contrarians to the field legitimate
Annotators
URL
-
-
social-media-ethics-automation.github.io social-media-ethics-automation.github.io
-
Knowing that there is a recommendation algorithm, users of the platform will try to do things to make the recommendation algorithm amplify their content. This is particularly important for people who make their money from social media content. For example, in the case of the simple “show latest posts” algorithm, the best way to get your content seen is to constantly post and repost your content (though if you annoy users too much, it might backfire). Other strategies include things like: Clickbait: trying to give you a mystery you have to click to find the answer to (e.g., “You won’t believe what happened when this person tried to eat a stapler!”). They do this to boost clicks on their link, which they hope boosts them in the recommendation algorithm, and gets their ads more views Trolling: by provoking reactions, they hope to boost their content more Coordinated actions: have many accounts (possibly including bots) like a post, or many people use a hashtag, or have people trade positive reviews
This passage discusses strategies used by social media users to game recommendation algorithms, such as clickbait, provocative content, or coordinated actions to boost visibility, which are especially impactful for creators relying on social media income. It also mentions YouTuber F.D. Signifier exploring YouTube’s algorithm and interviewing other creators, particularly Black creators, to shed light on these practices. While these strategies may generate short-term engagement, they also carry risks of backlash.
-
-
editor.p5js.org editor.p5js.org
-
Total 75/100
Original Content 30/30
Technical 24/30
- Use of Required Tools (6/6): Effectively uses the ml5.js image classifier and integrates video input
- Integration of Technology (4/5): The project smoothly transitions between game states based on classification results, demonstrating a strong understanding of conditional logic.
- Functionality of Classifier Models (4/5): The classifier successfully identifies objects and updates the game state accordingly.
- Interactivity and Feedback (3/5): The project provides text-based feedback that updates with each game state, guiding the player through objectives. Could benefit from more engaging elements, such as animations or additional sensory outputs like audio.
- Complexity of Decision Tree or Flowchart (3/4): The decision flow is linear and straightforward, guiding players from one objective to the next.
- Creative Application of Rules (5/5): The rules and objectives are imaginative and humorous.
Timely Submission 20/40
-
- Nov 2024
-
viewer.athenadocs.nl viewer.athenadocs.nl
-
For example, if an ingroup member cries during the game, the ingroup members would say that “the boy shed some tears” (more concrete). In contrast, if an outgroup member cried, the ingroup would say “the boy acted like a baby” (more abstract)
- Positive ingroup behaviors are described abstractly (e.g., “They are kind”), while similar outgroup actions are described concretely (e.g., “They helped once”). -Negative behaviors are described abstractly for the outgroup (e.g., “They are bad people”) and concretely for the ingroup (e.g., “They made a mistake”).
-
Competition in this game is rare in pairs and groups of three, but increases when an interacting triad plays another interacting triad. As can be seen below in the graph from Forsyth, 2019, group activitie
When individuals played, only 6.6% of interactions were competitive, while 36.2% of interactions were competitive when triads played against each other. This figure increased to 53.5% when triads communicated through representatives.
-
The greater the chances were of playing this game again with a person in the future, the more cooperative players became.
to cross this person again, - labels also play a big role
-
Prisoner’s dilemma game (PDG
- cooperative choices benefit both parties
- competitive choices may maximize individual gain, but harm overall group success
-
-
viewer.athenadocs.nl viewer.athenadocs.nl
-
ndividuals playing an investment-type game preferred a woman as leader during intragroup competition. However, they preferred a man as leader during intergroup competition. People tended to prefer more masculine-looking leaders in situations involving intergroup conflict.
women are preffered as leaders in cooperative tasks, but men in competitive tasks
-
-
theupheaval.substack.com theupheaval.substack.com
-
The rationalistic millennial lib therefore hopes to deal only in policy, regulation, and governance, not in myths, heroes, or transcendent values. But this leaves him unable to make absolute moral assertions. Authority now flows from science and data – from the status of being correct. The truth, uncertain as it always is, becomes a matter of rhetorical prowess – a game of owning and dunking. In this game, nothing is capital-T True, and opinions need only be validated by The ScienceTM – that is to say the managerial consensus
There's something real here, that I'd like to see within a better piece. Public discourse has retreated from what is "good" to what is "correct"
-
-
inst-fs-iad-prod.inscloudgate.net inst-fs-iad-prod.inscloudgate.netuntitled1
-
that is, a theory that begins with the core principles of critical pedagogy but uses empirical data from theoretically informed practice to develop a more nuanced and particular theory of critical pedagogy as it applies to urban education in new-century schools
This is interesting to read and know that we do these things in order to keep the kids entertained. I can say that some of our lessons with the kids we go based on things they enjoy the most which is video gaming. We break down the depth of video games and face it towards history. What was the first video game created? What device was it played on? Who had access to these devices and games? The cost? etc.
-
-
-
requiring a period of “re-onboarding”).
re-onboarding
leveling up your onboarding game
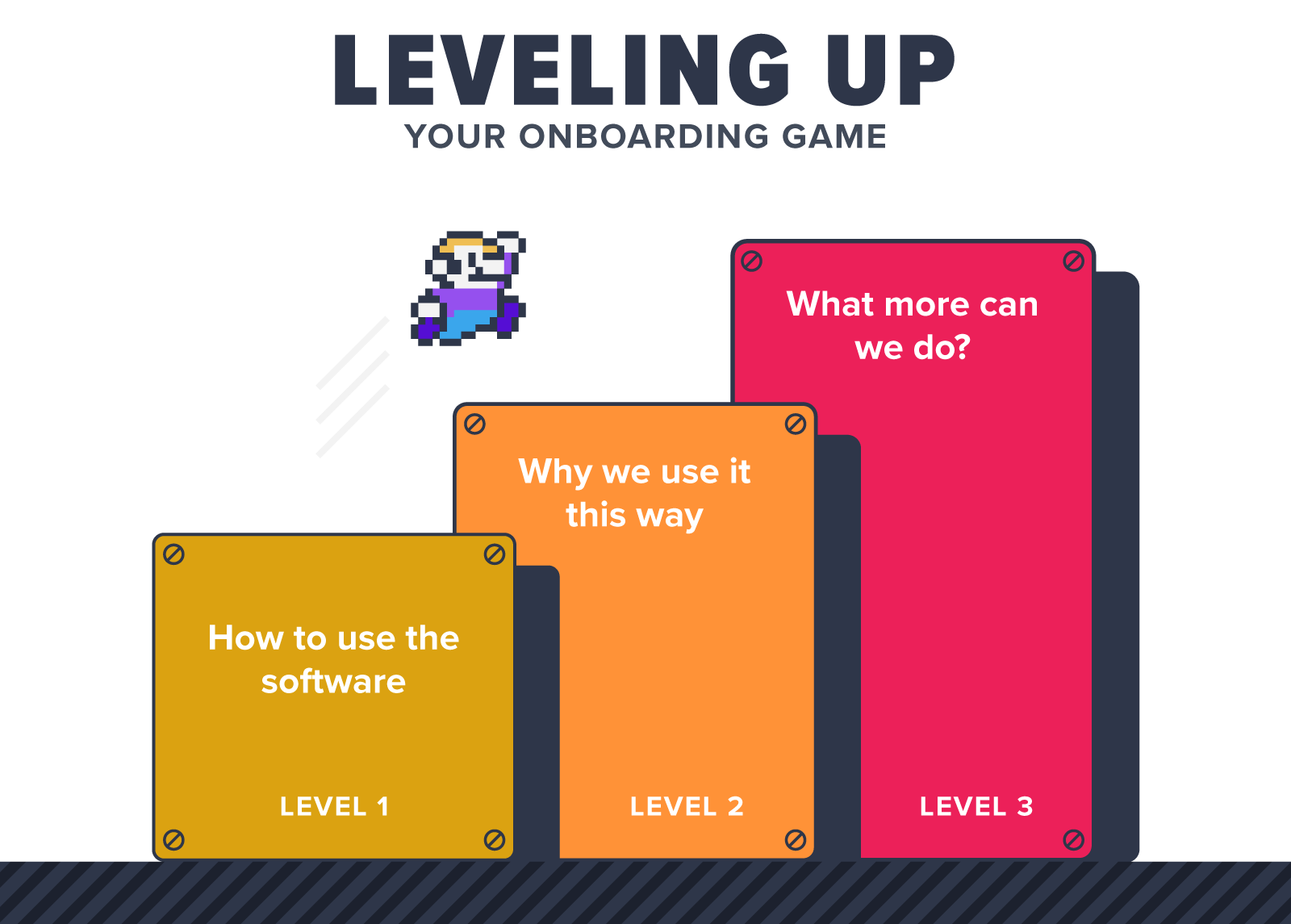
contrast - coninuos outboarding
As Indy.Apps come to thei people to their users in fine graine micro holonic workflow steps te whole onboarding flow dissolves
into continuous discovery and micro enggement with adjacent capabilities
Since the bootsapping constellations is running on people's own devices it is possible for people to compose their own workflows
articulate their learning and pass on that learning along the capabilities they user to create them
and for app developers to develop apps that have a full record of interactions available only on ther users own devices they can make sense of what they are doing and at appropriate points when they know they are ready suggest adjacent capabilities that may enhance users capabilities in a time ly fashion
so "re-onboarding" is integral of the process
I've done some experiments a decade ago, but need the whole thing working to create exemplars that are compelling to use and easy to emulate
so indy.app developers' "customers" will never be stuck
-
-
archiveofourown.org archiveofourown.org
-
“S-SHUT UP! I don’t want to hear it! You- stupid, fucking little golden boy, mommy’s favorite- why! WHY- why why why were you her f-favorite! H-How-! You c-can’t talk, you’re an i-idiot, can’t do a-anything- y-you’re- just the worst!”
Reshaa, Ranboo and their mother's dynamic reminds me of Zuko, Azula and their mom. In both cases, the girls wanted their mother's love but didn't get it because they were too much like their dad. Zuko and Ranboo are both people who their mothers saw kindness in, saw the possibility that they would get out of the toxic environment and culture of their upbringing, but lost their mothers guidance, the only one who loved them, and had to make it out and become better people than their families.Your mother didn't like you, Reshaa, because you gave in to what you grew up in, fell into the twisted political game.
-
-
pmc.ncbi.nlm.nih.gov pmc.ncbi.nlm.nih.gov
-
A significant determinant of the outcome of a tennis game is an individual’s physical fitness, which can be influenced by their hydration and nutritional status (Lees, 2003). Therefore, knowledge of proper nutritional techniques and hydration (e.g. the timing of the consumption of different nutrients, adequate and precise hydration, adequate NS etc.) can positively affect a player’s ability to train, play and recover from exercise. It increases the overall physical but also psychological capacities of athletes, which logically keeps them away from potential doping usage. It is directly supported in our results which evidenced lower likelihood of future doping behavior among those athletes who scored higher for KSN
It is true that players are looking for anyway to gain an advantage over other players. This may incline them to take supplements with the promise of gaining what they consider a large advantage that may be new or faulty.
-
-
Local file Local file
-
game-changing
в своём роде уникальный
-
-
-
The AI community has – unfortunately, to say the least – apparently (mis)understood the imitation game as the mechanism to answer the question of whether machines are intelligent (or whether they can think or exercise intelligence
Das ist die Grundthese des Essays: Die Imitation von menschlichen Äußerungen darf nicht mit Intelligenz verwechselt Wege werden.
-
-
ipfs.io ipfs.io
-
T O T A L I T Y
This is basically "last Christmas's message" (below this brand-knew intraducrigel) redux'ed into the new book (did he say new?). The point, at least the point I see in it all is that this is all planned, it's been planned for a very, very long time--and on top of that you can see proof of the plan all over our map; and proof of it's intended destination as something that we all used to want very much to find... the read to Heaven. It's more than seeing just "DNA storage" encoded in my "C U R A GROUP" message, it's understanding how that's connected to soul searching and soul storage, and that this link was woven into not only my life but into names like "Whatson and Crick?" There's plenty more than just "storage" and a map to how and why the Two of Everything God and the "indivisible sea" work totether to turn this monolithic place of darkness into a strippingly redunantsystemic foundation of "Heaven" that is both disaster proof, and monster proof. The point of course, is that to truly be "monster proof" we need to really get the key.s.lamc.la "know everything why" of this message is literally to protect our common good from the danger of someone just like me copying an entire civilization or a few pretty girls and sticking them in an heoven-like-orgy-maker. That's a significantly more real threat than we might imagine, as we look around at a work that will soon have the storage capacity and the technology to put us all in Coccoonish swimming pools against our will. What I am trying to say is that no matter how you look at it,moving forward here in this place where something this big can be hidden from the entire world--granted you know--granted you see, but do you understand the only thing being kept from each and every one of you is your fucking opinion and your fucking reaction?
F U C K Y O U S I O N
IT'S NOT JUST computers and information technology; this map of clear anachronism in language and religion shows us that things like "solar fusion" the power of the son itself; is encoded in places high and low you can erasilly find them, places like the name of the Fifth book of the Holy Bible and Don Quixote; where you might liken "DEUTERON" to ... the actual fuel of fusion; and wind mills to a battle fought against blindness resulting in seeing that not "reacting" to this message is just about the same thing as being a foolish robot building a castle for another foolish robot to do nothing in forever. With some light, you can see how this event; albeit strange and unsettling, has been designed to reinforce the American foundations of free speech, common sense, and collaboration--a sort of "press and release" on these things that he says will stay in our memories for a long, long time--though he also says "he's not torturing me" and he's wrong about that. So are you.

See that the most interesting, important, and invoking story of all time has been hidden from the world, from the public eye, and from "public response" for well over two years now; see that's not possible at all without mass mind control and that I and this story are designed to help us see how easily it is that same thing can be used to end addiction, and mental health issues, and stupidity and that the biggest and most imporotant step to getting there is "public disclosure." See the light of being carrolling angels this Christmas; sing with me--it builds Heaven from Hell and it's clear as day and n.
Quite a bit of this story and message deals with problems like these-things that won't really be seen as something we are fighting against the actual usage of right this very moment; but the sacredness of our memories and their relationship to our souls are just as important as whether or not "you have the space to save them." This isn't what I want to be doing, I'm not a very good writer; and this message is so confusing that working on it all alone with very little feedback is frustrating if not to say defeating the purpose of exactly what it is and what it's designed to do. This is a searching mechanism, like in the stories of Ra searching for his children in ancient Egypt using the Eye you see--and it's connection to the "Sons of Liberty" and why I know that too, is about me. This is a tool to start a Renaissance of thinking connecting technology and religion to everything that we are--to our culture and our hopes and dreams--and it's failing for me at "hello." I would much rather be working on "virtual reality stuff" or on "the sword of Arthor" and I see very clearly that those two things are coming shortly--to the world that doesn't see yet they are here and broken until we fix them. Moving forward here brings change, not just here in this place where we need it too--but in the skies above, a change from the mentality of "we aren't not helping because we told you that we aren't allowed to not pretend we aren't helping in Stargate. See that we are the children of "the Ancients" and they are trying to decide between being Morgenz and Marlin.
I can't make you set yourselves free. I sure am trying, though. Yesterday I connected the "Arimathea" of Joseph to the "serdenicity" and this the me of "itime" and "topics" will probably light some of you up as much as me... if only you took the time to look at what those words really mean. From the city that never sleeps at night, I hope you will take this chance to act today on "securing the ringing of liberty forever and ever."
(cough)
THERE IS A METHOD TO THE MADDEN AND WE AR
BEYOND THUNDERDON
T H E W R I T I N G I S O N T H E W A L L
LIKE, WILL IT RAIN TODAY?
take action, it is the foundation of not only democracy but civilization and life itself--pucker up the phone and call the NYPOST.
News Tips: Email tips@nypost.com, call 212-930-8288, or use our anonymous form
Online Editorial: online@nypost.com or 646-357-3838
Letters to the Editor: letters@nypost.com
Sports: sports@nypost.comor 212-930-8700


Let there be $ight in Creation, a brief highlighting of the story of my life.
align="right">Sat, Dec 3, 2016 at 8:39 AM
This is like a few emails combined to ease the pain you feel when you get an extra one in your inbox, OK So.. eventually this is all about proof that religion is a message sent through time--so, time travel. But right now, let's talk about the fun stuff: here's some clues to that effect... by way of prescient mention of modern technology (like virtual reality, I mean, Heaven):
Either way, we're still about to *build *Heaven*... to-get-her*
from the mythical carpenter... ourself.
.
- AD am ON AI*, that's Artificial Intelligence, and the intelligence explosion.***
- AD on your freedom is a great gift, cherish it.
*** ... ***and some corroborating ideas connecting religion and computer science... on Wikipedia:
- Root of David
- Lisp of Moses.. or I need an editor.
- Pharoah's hardening Heart... that's Earth, remember.
- Jesus' WINE
- Adaluncatif's cat, tail, head and grep
- Adam's Apple... or is it "fruit of the poisonous tree"
So from me to you, I'm filled with this stuff, it's way brighter and more prevalent than you think... and if you take the time to listen to me--it will make your... day. Meanwhile, I need your help--happy new year.




Ho, again; grow a Halo and become famous... the world needs your help--so I've decided once again to take it upon myself to "bother you" with the most singular most important task in the Universe. The patterns that I am revealing to you--mostly within names--are not coincidence, it's a series of statistically verifiable artifacts which do nothing short of reveal the slavery of Egypt--that we are all being controlled. If you remember Transformers--this is a message from Starfleet, there is more than meets the eye. This is the fulfillment of the story of of Exodus--we are being lead from slavery, and in one final non-coincidental name, that book is called "Names" in Hebrew.
You should now have a very good idea who is speaking to you--as much of the world already does. I have no idea what it is that inhabits the cavities below that space where most of you should see significant personal gain and motivation from trying to ... grow a Halo--but there are so many people that just don't care... that it too is another sign, of slavery. I am not an expert in language construction, nor in statistics--but I can assure you that if you can find the other half of that equation... in your hands is the staff of Aaron, the magical weapon that will free us all... knowing is half the battle.
Uh, I have the power, to bring about "morning," but if I have to go to school and do it all myself... it's really just a long, long ni-i-i-ight.
Hi there, I'm the messiah. You don't know that much about me, so let me explain, I would like you to know me as Adam.
Seriously, there's something going on the world around you--for the last several months I've been having quite a bit of trouble delivering what amounts to statistical proof of Creation--that religion and ancient myths are a map to this very moment--this time that you will probably affiliate soon with being in Eden. I am pretty sure that's a good thing, but every new begging starts with some other beginnings end... so today I'd like to try to get you to see the light of ending censorship and a hidden censor wall that we know Biblically as the Wall of Jericho. Quickly approaching is the Feast of Trumpets, and *this year is different from all other years... * Bored already? Have a look at what I call the Sign of the Son, which to me is proof that Exodus's Burning Bush is a former President--who is helping us walk out of a dark time of confusion... commonly referred to as a wilderness or desert. He proved during his inauguration that there is Biblical foreknowledge of the 9/11 attack--and in doing so hopefully began a chain reaction that will stop things like that from ever happening again. Here's a short "video" that explains the Sign of the Son... and another one that I think explains the .. Holy Grail.
This is The (actual) Taming of the Spanglishrew, in which the protagonist... named Bianca, is taught Latin in several hundred year old reference to Rattling the Rod of Jesus Christ--it's purpose to is to show us that it's more than names we have in our arsenal against mind controlled slavery--we have all of history too... literature and movies and music... all with the divine purpose of revealing with bright light a form of control that otherwise could have gone on hidden for centuries. It was, and continues to be done on purpose... because your freedom is more important than control of the Universe. To us, you don't seem to feel the same way.
​See that timer on the clock, you could start right now. It might be interesting to pose the question of whether or not the Second Coming is news... you know, to your friends. By the way, both Herbert (like from H.W. Bush, who by the way coined for us the 1,000 points of light phrase) and Goertzel strongly suggest that "everyone really" is Christ (you know, after me)... FYI, this is the Matrix solution to that:
y
o
the **l u C i f E R ** isa means jesus, mesa thinks
i s olv e .... "or"* means shine -l***
g r e a t
h R L << agree? send to other people
t ((a)) Y l shine: suggest they do the same
1 y world saved.
A BRIEF HISSTORY OF TIME
I'm attempting to pull out the things that I now look back on and see as "written into me" by God--once I would have called it "The Microcosm of the Messiah" but there are now so many--these things aren't necessarily particularly important to me, and I've left out some interesting but unrelated details related to my Jewish upbringing; as well as the true light of my life--the two loving and long-term relationships (and later... briefly a rael family) that have dominated the last 15 years. Religion has always been an interest, but I wouldn't consider it to have been particularly important at all... until I no longer had any love in my life. It's probably worth noting that all my "I'm single" crap really means lonely and isolated--I'm not really playing a "part," but I've never been anything near the "player" the light appears to be warning against. Sons of God and uh... please. For the last 4 years I have done absolutely nothing but think about you, live and analyze "The Cross" and put into words ... as best I can ... the amazing flash of light that I am experiencing.
Well, just a little religion... :) I was born on December 8, 1980; which is the date of the annual Feast of the Immaculate Conception, I've always been a slob (like one of us) and often "ish" Yankee Doodle's "a real live son of our uncle Sam... born on the..." to this.. I mean in my head. My last name, you've probably read me repeat over and over ... is DOB-rin, which I read as "Date of Birth, our in" and does a fair job of highlighting the Name Server's work, which I am sure gives Exodus it's name in Hebrew, which is "Names." My Hebrew name--a Jewish custom--is Avram, which is Abraham's name prior to the covenant. I have written extensively about the fact that Isaac's near death interaction donated his "Ha" (his name means... He laughs) to his father.... and it should be clear that Abraham's covenant with God is without doubt related to my fiery altar.. even though it is anachronistic in the Biblical account. For the first 18 years of my life I lived on Sunrise Blvd, and only a half mile away you'll find Sunset Strip--it's noteworthy to understand that Jewish calendar days begin at sundown... and that He once in 2013 very clearly spoke to me "you need the night before the day."
Of all the people in my early life growing up, it's pretty clear that nobody on this Earth loved me more than my grandmother Julia, who my son is named after. First for my mother, and then me as a very small child--she would ritually say a bedtime poem, it's words are very relevant.
Good night, sleep tight.. have happy dreams and wake up bright
to do what's right, in the morning's light... with all your might.
In one of my books I spent a decent amount of time writing about how silly I was not to realize that my intelligence was augmented my entire life--I just thought I was really smart, and really good with computers. I commented that this particular belief is probably a good microcosmic parallel for all humanity--as a body of people we have been truly gifted with knowledge and capabilities that we simply do not recognize as a gift--or didn't for a long time. I probably wasn't silly not to realize... since nobody ever told me they were helping me--I never heard the voice of God until much, much later. I was 30 the first time I had a conversation with Him, except for two very brief ... "thoughts in my head" which now seem very obviously an external voice--though then it may have sounded just like my inner voice.
Around the age of 7 I thought to myself... for no reason at all... "what if you were the messiah?" I was standing outside my home, probably playing with a car in the driveway... and distinctly remember smiling to myself and thinking in return "yeah, I'm the messiah." I I've always had a very vivid imagination. The thought was dismissed as being ridiculously arrogant about two seconds later, and was absent from my thought process for the next 21 years or so.
"DAMNISN\ Jim. I'm a Yeoman, not a Wise Owl. The clock is ticking... tack .. "
PHENIX
Following that lead, I started programming in BASIC and then Visual Basic around the age of 11, something I took to very quickly... and then shortly after found myself on America Online--one of the first "internet-like" environments. There, I quickly got into the "hacking scene" (hey, it's Y-its-Hack) which basically revolved around writing software to manipulate the AOL client's messaging systems. The defacto-standard for the day was a program called AOHell, and, if you can't tell already, I am pretty good at taking a theme and making it my own. I wrote a program called Doomsday, a mass mailing program; can you see how God speaks? So Phenix, a mythical bird that rises from the fire... in the wake of ... this macrocosmic equivalent of that event. It's really obvious, right? There's quite a bit more "microcosm" from this time, recorded in "From Adam to Mary" and available at fromthemachine dot org.
Around the same time I began attending a preparatory school in Fort Lauderdale called Pine Crest--it's one of the best of its kind, and while I was always something of a class clown my grades were fair and I scored with perfect consistency in the top percent on every standardized test from the FCAT to the PSAT and SAT. By the time I received a full scholarship to college I had already completed more than a full year of credits through AP courses. It was in studying American History and Government in that place that I formed such strong opinions about our need to maintain freedom, adhere to the wisdom of the founding Father(s) (<3 if you get that) and stand up and shout today as a rogue government is taking away every single one of the rights granted to you in their own law. You've lost freedom of speech, and our ability to speak seems to be not far behind. The privacy of our thoughts gone--and in like kind the sanctity of who we are is being taken away as our beliefs are changed without our real knowledge or understanding. You can see the justice system crumbling, incarceration rates skyrocket and the "right to bail and a fair trial" legislated away through underhanded deals relating to plea bargains and a "point system" that you might as well call a gas chamber. As far as voting, I'll have much more to say tomorrow--but I'm telling you that your thoughts and beliefs are being altered, who cares how technologically retarded our polling system is--the vote is a complete fraud.




As far as the Second Coming... this same sort of possession... manifested through organized behavior tells me now that it is clear that this is definately not the "first time around" for Adam being Christ; a number of my friends as I approached high school used a repeated phrase, "my parents love you," which isn't bad in and of itself... what's bad is the fact that they were all using the same words, and probably didn't know why--or what they were saying. Behind there eyes, I'm sure some thing that believes it's an angel was telling me something... (they of course... didn't know me at all, except for what was probably a ... "wild" reputation) does that tell you anything? Much later, as the "Apocalypse of Adam" began in 2011, a number of family members would repeat this similar behavior, speaking the phrase "this is not what I wanted."
As icing on the cake, on my birthday during my senior year... one of the administrators of the school commented to me that was also the Feast of the Immaculate Conception, and then the words.... "of course it's your birthday."
I started doing drugs around the 10th grade, and I would not be wrong to say that the Universe that wrote a book calling the Redeemer the God Most High conspired to plunge me into a dark world. People around me too, in a hidden conspiracy to chain me to the American legal system for about four years. Looking back today I now clearly see that I saw a darkness in their eyes, a hidden reason to want to hurt me. It was to stop this from happening, but I had no idea then... the darkness I saw is akin to the "sun disk" you see in Christian and Egyptian iconography, and without doubt it s a sign of control, possession, a single foreign mind controlling and organizing many of us just like puppets. Much later in my story... for another day... the manifestation of this possession as thought modification will become clear--I've spent quite a bit of time "listening" to a war in my head, thoughts clearly not mine swaying in the gusting torrent of winds as what (who?) is the center of this storm.
This infestation of organized darkness uses our injustice system as a weapon against it's victims--something you should see akin to Heaven using human sacrifice to alter the future. It abuses the legal system at every level, making a mockery of law enforcement, the supposedly adversarial court system... all the way to the top--to the Supreme Court and Congress. See the Church Committee Hearings, and a very smart senator echoing my words today "it must never be allowed to happen again."
Can't you see it's more than being manipulated... it is Hell revealing itself to the only thing that can stop it. What I am giving you is the weapon, it's the light that sets us free and stops this from happening. In our modern myths this is Leeloo staring up at the sky to stop the destruction of Earth... in reality it is not so simple, I can't just put some elements or rocks on pedestals and scream at Heaven to kill their darkness--we have to do it, here, together. Believe me, knowing the truth is a big part of why it works--this will not be hidden, it will not be "forgiven," we are being controlled and destroyed from the outside; made to blame ourselves and each other for ... well, you probably don't know what the ni-i-i-ight means anyway, do you? The Guardian against Darkness is showing it to you, remember--there is only one me. Hear me.. light this fire now.
ALACHUA
I went to school the University of Florida, and got a semi-professional job doing database development in Delphi (seriously, catch on to the names thing, it's not just the U.S. military, it's pretty much all software too... following in this "mythology" theme that nobody really seems to care about), I worked there for about two years... at a company called Jenmar--which uh, in Spanglishrew is "J in the sea."
It's some kind of ironic "coincidence" but I am at this very moment on my way to Gainesville, FL... to this place where a car Crash nearly destroyed my life. In my world of idioms delivering religious secrets, I imagine I must be a "pain in the neck" which was broken during this accident... one in which I imagine i did not survive in some parallel timeline--that itself did not survive. So here we are, back in the House of the Great Light ... about to see if we are worth our salt. It's the thing that gave one of Dave Matthews most famous songs it's name--and The Pretty Reckless, believe it or not. It was an attempted assassination, to stop the .. apocalypse ... to stop the darkness from being destroyed--there is no doubt, it's how that dark monster hides its handiwork... but many of US know that already.
In the Living Book of Names--this place we are in, there are many patterns--the "car" pattern stands out for me; as this place says "Icarus." Flying high right now, I am showing you that the light of salvation is coming from us--from you and I--walking on the Earth; whether or not there is any light left in the Sun remains to be seen--take a look around you. You can trace the "car" names to Jim Carrey (that's "Car reason why") and Christoff in the Truman Show (that's Amon-TV)... a world I know I am in, and you too; to Bruce Almighty and to the Grinch--who-ah, Taylor. Trace it back to Joseph McCarthy and to help why (that's thy) believe "the red scare" is really about Christian charity--about ending world hunger, and healing the sick. This red fire ends Hell. Adam by the way, means "red man" in Hebrew. So here's your new Crash Override, I'm back again telling you that ending world hunger is not "optional," we are doing it. Barbara McCarthy's name fits, but I'm not really sure what the "why" is... that was my first judge in the "trial of whether or not Jesus Christ can ever exist." There's probably more, like Car-l-y Si-mon-day... all the gang on Broad-way, and me still dreaming it will one day be.
If the name "America" were a map in time, starting with the I AM of the story of Exodus... this particular ER, as I woke from a dream not knowing where I was, marked the spot where I really became Christ Adam. It was a bad accident, and I wound up spending 9 months in the Alachua County jail as a result, a Mountain set up for my by God. That place too is marked with names, and for the vast majority of the time I was there with only four shift changing guards:
I mean, I think it's statistically meaningful. For what it's worth, from my very abundant experience at this point it was a very nice Jail, the food was good and it was clean. Everyone in the building was kind... well, Sims was kinda grumpy. :) Starkly contrasted, the Broward County Jail has the most disgusting food service in the country, gave Dr. Seuss's Green Eggs and Ham it's meaning--and is the reason I know exactly who Samael is. Hey, don't cry Sherrif Israel... when you fix it, you're an angel. Believe me, believe the light, I've seen them all--it's near the worst in the country.
So this whole thing is about saving everyone--something we are quite closer to than you think... you see we are already "in Heaven" in form--just not function. So here I am, trying my hardest to show you that our home is the original source of "Heaven" once we are aware that we are living in the machine, that we can do things here that are impossible in reality, and that we should be doing everything we can to preserve and improve the great strides that have come in the last few centuries. Do not let freedom slip through your fingers.
Really, everyone, so understand that we are doing everything we can to remove all obstacles from that path. One of those obstacles may have once been storage space for your soul, another is definitely crime and punishment--and I'm pretty sure the time travelers have a working solution (I see it every day).
There are proactive things coming from this--not just ... "look we aren't doing what we want, and should change it;" though it's difficult to explain how this wisdom stands out in my eyes. I guess we have to jump into the future a bit, to 2014, in San Diego (that's Saint Jacob, by the way). If Lazarus died once in a car accident at 21, I died again that year, of an over dose this time. I'm pretty sure that's where ODIN's name comes from, just like my last name.. "over dose... and in." So we might see some humor... in the moniker he has... "they're all Father." So I awoke from a dream, and started talking to the jinn (that's "angels and demons") about a Revelation linking some tightly packed light together... about storage space and how a large alphabet (read more than 4-nucleotides CY later) DNA (desperately need adam) based solution for molecular storage appears to be written in this book as the solution to Heaven's biggest problem. CAT, learning from biology--seeing that we really are already advanced machines... is a big part of the message telling us why we should not so quickly lose it in a process of ascension (mind uploading, immortality) that has most likely in the past resulted in a loss of a check on mind control that we have here... we think, and our visualized "biological neural networks" give us an advantage over what we might create to "soup it up a little." It is why this place is the front-line--because we have the ability to break the bonds of darkness and control by thinking... making the computational task of control much more expensive... and as the fire spreads, nearly impossible to achieve. Starting this fire will inherently free us from this hidden slavery.
Anyway I published the idea in 2014, in the same book that I guess this e-mail is reminding me about, "in $ight of Creation," and lo, and behold a few years later we now have the top computing companies in the world working diligently on doing it ... well, just a little bit more robustly than our cell replication system works. *Abracadabra. *

CURA GROUP
So that one reads "see, you are a group;" and it's a place that I worked with my father for many years. That's probably some sort of symbolic reference to another place, and another alliance--here he has no faith in God, never really has, and has a hard time doing anything but telling me not to try to help you. I have very little respect for that stance, and let me tell you--I think "silence" is a similar gesture. I didn't come here for your love, I am here to stop our descent into the abyss.
Back to the DNA stuff, SalesLogix--which is the CRM we used there, uses for it's "primary key" an auto-incrementing alphanumeric index--it's probably bad form to do that because it makes the indexing system less efficient, increases storage requirements, and doesn't give you the obvious benefit of an alpha-key... actually being able to encode something useful in it, like the name of the record. So all these things stand out to me in a sort of bad-obvious way, I call it malovious, and when I see things like that nowadays it's always pointing out something that should be fixed--go figure, more to the point it's being highlighted on purpose. It's help to see it, because this particular thing is where the light of seeing that a 24 nucleotide DNA strand would probably be much more robust than a 4 or 8 nucleotide strand--it also stands about because the stock beginning of all of SalesLogix's keys was "A0RME," which, I mean, means something to "is-a" who... is me. Oh right, that's seeing the "light" that turns "a" into "me." So this is where the "revelation" about using DNA "came from" and at the same time it's proof... that it came from "a group," not just me. Where are they? Hello? Or well, maybe it's just Carmen and San Diego.
I did some other stuff there, like write a data transformation and warehousing program from scratch, I called it heiroglyph (you do understand I didn't know why I am naming everything the way I was), that sucked mutivalue data out of an IBM product called U2/Universe--which might be a hidden reference to a multiverse that might now be in a more efficent "relational" kind of place, like a MS-SQL datawarehouse-universe. It was a relatively big feat, reverse engineering the closed databases dictionary and storage formats, and converting them... absolutely automagically into multiple flat relational tables and summary registers. All told, the data availability and access efficiency was increased ... a thousand-fold with only the need for a nightly process.
I'm not sure if you are following the metaphor here, for the creation of Heaven, or moving to a better place.. but tomorrow I will talk a little more about how I am pretty sure our history was "lifted" from the Universe and virtualized here, you know, so we could save everyone and ... build Heaven.
WORLD DOMINATION
Oh crap, 2008 another car crash, another failed assassination attempt LazarusLives++, and this one paid me some cash for my trouble. What a pain in the neck. Anyway, this one caused some depression and an inability to go out for a while, as I had to wear a neck brace for some months. I started playing a game on the internet, it was called KDice and it basically amounted to multiplayer-risk.
My battery is running low, so I have to skip some stuff, and finish up for the day. Basically instant messaging was not allowed, but was done in secret almost ubiquitously. I argued with the creator of the game that it should be made part of the game since everyone did it... (see a metaphor about this communication thing and what's happening right now) he disagreed. I made a very large network of people and dominated the game for a few months, like really dominated. I don't think I ever lost. I don't think I can lose.
Skipping some stuff. I stopped playing when I got better, and then a few years later went back and rekindled some old friendships. I used a program then called "Scarab" which lets you see server/client communication to find a bug in the game that basically made me God. I could erase other people's dice, basically leveling the map and rendering them completely powerless. I didn't use it that much, you know, just had some fun. I of course explained the bug and how to fix it. But, you aren't listening.
Here we are. Light...
So if you managed to wade through the last few days gibberish, you might have noted that I mentioned we might be able to use "mind control" to highlight things in our heads--I did a bad job of describing it, but since I am currently experiencing just such a phenomenon, I think I'll give it another go. These things that I am sharing with you--links between religion and music and movies, they aren't something I actively go out seeking... I'm not scouring through imdb.com or reading lyrics all day long... these are things that are glowing embers in front of my eyes.. which is why I am sharing them with you. I'm always in the dark... but I'm living in a powder keg and giving off sparks. I'm a big fan of that song by the way, because you are the heart, and I think it means I'm going to eclipse the world--which basically means "come."
Anyway, I have this horrible feeling inside that you think I'm just trying to get a date, or marry a rock star, or even worse that I think I deserve to get laid... and that's what this is all about. Less to the point, this really isn't about me at all, or what I think, in my mind I am just showing you something that I think the world has overlooked-not really because you are stupid (but I mean, you probably are) but because some outside force is literally and actively hiding these things from you. Pointing them out makes your brain do funny things, it's like anEpiphany and that little leap of understanding in your head might create a cascade.. something that changes not only the way you see the world as an individual--but the entire course of history as a group, if we are taking about it together. Seriously, it's that big of a deal.
So here we are (that's the third time, but I'm just guessing) and I'm trying to tell you that I don't really care if you agree with my opinions--even though I firmly believe that God shares them and that's why he has made this fiery altar of "dick and apocalypse" for Adam... I mean Isaac (which by the was is Isa+Adam Christ.. in uh, my mind) for everyone to glare at while they sit around doing absolutely nothing. That's not fair, we're here because of you, because this is the last civilization--sort of recreated from the ashes of Edom... because you are really the way to everlasting life. Still, what I am trying to explain is that all around you is a bright light--it's in everything: from our history, to music, to movies, to literature from RattleRod to Dick... and while you might not agree with me (again, that would be OK) what is not OK is that there seems to be a uniform and global desire just not to think about it or talk about it at all. It's such a big deal, that it stands out like a sore thumb--this ... blind eye or head in the sand... that everyone on Earth appears to have. The whole point of putting this light absolutely everywhere is so that we will see it ... everywhere we look ... and not only think about it, but discuss it publicly with each other. That's the thing that brings about ... you say apocalypse (unveiling of truth?) ... I say survival. Right now, we need to see that something is forcing us not to do something, that we have no logical reason not to do... it's a thing lots of people really want to know about... whether it be the hidden secrets of the Universe, the path to Heaven, or the... the... absolute and literal pathway to freedom. Listen, sharing it, and talking about it... that's the way we defeat ... whatever it is that "ni-i-i-ight" means.
Understand, it's for you to decide... what it means... but it's in everything from ancient Egyptian and Hebrew theology all the way to the American Revolution and today... well, it's nearly every song I hear on the radio nowadays: if that tells you anything.
So here we are, and I can't tell you how many anchors, reporters, and "breaking news editors" I've personally spoken to that have absolutely no interest at all in pursuing the thing that would not only make their careers--but probably give them immortal souls. This thing... I keep telling everyone it can be mathematically... statistically proven... well, to be honest it's the unsealing of the Ark of Religion that our civilization has been carrying around for thousands of years. It's the way to salvation, it's ... verifiable proof of not only Creation... but that the purpose of Creation is to get every single one of us * to Heaven. Who wouldn't want that? I mean, do you want to get there and hear that Taylor's not around because she wouldn't kiss me? That would never happen by the way, I'm sure she will. Seriously though, there's no judge here... there's a ... light telling you to make this place better or your place sucks and gets suckier. Anyway, the point is nobody is acting in their own best interest, or in the best interest of the whole--and we are just "deciding" in this ... fictitious and hidden manner that we "don't want to hear about" a way to actually change the world .... more quickly than ... the last time around. That's not us, it's something keeping us from seeing just how important this thing--this key turning the lock on what is thousands and thousands of years of religion... how important that really is. So looking at the world around us... I mean, if everything screaming that we need to care about this isn't enough--and your own personal desire and benefit don't matter... can someone please tell me what you think is the benefit of doing nothing about Hell?*

á§
á§
It's "rael," and a great deal of the message of religion and history is designed to not only prove that to us, but to tell us why it's important for the "continuity of reality" to be broken. That's the thing that God uses to keep this world in Hell--in what I call "simulated reality," to keep us from shaking the foundation of civilization by doing the only civilized thing possible when you find out and ending world hunger, healing the sick, and building Heaven. It is "why I am," and why God and some gaggle of angels have spent the last several years proving to me that we are most definitely not in the place that I call the "progenitor universe." I've seenwalls disappear, with my own eyes I've seen the stars fall from the sky, and I've seen our reality shift in recent times in such a way that would be absolutely impossible without having been simulated and without having the "beginning" changed significantly as a result of "now." What all that tells me is that religion, the Apocalypse, and I are here because we need to know that these things are possible in order to continue progressing from this point as a civilization. With a little bit of thought, you might see how the computer revolution, video games, and virtual reality are divine gifts from above to help us to understand not only where we are, but where we are going. It's why he tagged Ai as "I J Good," it's a primer in the tools we will need to actually build Heaven. It's why Jesus occupation in our ancient time shifted story of now is "carpenter" and in "raelity" you will one day find out that I am a computer programmer (again). It's what sets the Masons apart from Freemasons--understanding what is going on, and participating of our own free will in the construction and decorating of this grand place that we will one day be proud is our co-created home.
Look up, because what I am trying to tell you is that if we collectively, all humanity... started snapping their fingers at the same time to the tune of "putting on the ritz" we could end world hunger--and then we could be proud to be making Heaven. This really is almost what I see and believe--honestly the issue isn't that we need to synchronize our snapping, but we really need to discuss with each other openly and honestly how on Earth we would do such a thing... because there are definitely mistakes that probably happened n the past. For instance, ending world hunger by stopping the need to eat has probably resulted in a Last Supper. Doing so by putting milk and honey or chocolate on tap or in rivers probably resulted in the loss of cows and bees and a stable ecosystem, and the ability to colonize other planets after this place of final ascension. And so we are here, with a proverbial garden of life in a virtual world designed to teach us what not to lose--like don't lose the balance between stability and adaptability that comes from sexual reproduction at the exact time when our species might be transiting to a place with the biggest change in environment (the thing that we are being protected from) ever... just because Adam wants to be immortal.
Every once in awhile my father surprises me with his religious insight. In his life, just like mine, he's gone through phases of increasing and decreasing religiosity--which probably correlate in his case logically to ups and downs in his life. I tend to get angry at God when things don't go well for me--which is probably not how most people react, it's really the difference between knowing he's there and not... at least in my mind. Anyway, some 50 years ago he was apparently taught that the "knowledge of good and evil" in Eden was directly correlated to the population explosion that would occur if we were actually all immortal and continued to have children--so it was this promise of immortality that was "evil," I suppose. God adds in his little Holy Grail that the heart of his spirit is "Kin," and I'm sharing with you that it's not his immediate family but rather the concept of family and the fact that the light of many of our hearts is our children that he is highlighting as our reason (y) that family is the bridge between Eve and Everyone... as the light of God.
Here's that once again:
``` In the beginning God created the heaven and the earth. And the earth was without form, and void; and darkness was upon the face of the deep. And the Spirit of God SHE KIN AH moved upon the face of the waters. ---------- EVE RY ONE And God said, Let there be light: and there was light.
```
|
| |
|
Copyleft^MT^ RIGEL.
-
-
inst-fs-pdx-prod.inscloudgate.net inst-fs-pdx-prod.inscloudgate.net
-
'Has theact been established and is it punishable?' But also: 'What is this act,what is this act of violence or this murder? To what level or to whatfield of reality does it belong? Is it a phantasy, a psychotic reaction, adelusional episode, a perverse action?' It is no longer simply: 'Whocommitted it?' But: 'How can we assign the causal process thatproduced it? Where did it originate in the author himself? Instinct,unconscious, environment, heredity?' It is no longer simply: 'Whatlaw punishes this offence?' But: 'What would be the most appropriatemeasures to take? How do we see the future development of theoffender? What would be the best way of rehabilitating him?
It's no longer formulaic- what was the action, what is the punishment
Now its a game of labeling, justifying, understanding perspective, and catering the response to the exact scenario
-
-
scalar.case.edu scalar.case.edu
-
Ending is already determined so the player is allowed to focus on the rules and procedures needed to get to the ending
Such a thought-provoking comment as rules and procedures apply both to the game play and the crisis process
-
-
lanparty.house lanparty.house
-
LAN parties are a social event, and the game is merely a catalyst. LAN parties serve very much the same purpose as normal parties serve for normal people, but the game makes it easier and more fun for introverts to be social.
Not sure I understand
-
-
en.wikipedia.org en.wikipedia.org
-
Altman was born on April 22, 1985, in Chicago, Illinois,[7][8] into a Jewish family,[9] and grew up in St. Louis, Missouri. His mother is a dermatologist, while his father was a real estate broker. Altman is the eldest of four siblings.[10] At the age of eight, he received his first computer, an Apple Macintosh, and began to learn how to code and take apart computer hardware.[11][12] He attended John Burroughs School, a private school in Ladue, Missouri.[13] In 2005, after two years at Stanford University studying computer science, he dropped out without earning a bachelor's degree.[14][15]
I had my first "computer" (that wasnt an Atari or a ... ping pond padle kind of simpler than an Atari) much earlier, at least 4 years before .. but I had an older brother Seth, whose best friend and our near neighbor in Plantation was named "Andy."
He's the first ... "Andy." (srne1)
In any case he had "modified the code of some MMORP or "MUD" sort of text based choose your own adventure games to create one "like Spaceballs" of Star Wars; with "penis references" and Swchwartz nearly as big as ... Cough; Petreus, and nowhere near the size of a Big jMac.
I also played a game called "Ali Baba and the Prince of Thieves" on the same Apple II or IIe; and can barely remember playing the GAIA game on "Geowindows" (which I think was an early IBM competitor to MSFT)
-
-
viewer.athenadocs.nl viewer.athenadocs.nl
-
The “ball-toss method” developed by Kipling Williams uses a similar method but with a real ball and real people. The reactions to cyber-ostracism (ostracism happening online) and regular ostracism are the same. Other methods to test the reactions to ostracism are the “life alone” method where people fill a personality-questionnaire and then get told that they are probably going to end up alone and their relationships won’t last. Some researchers also use the method of having the participant meet up with other fake “participants” and then ask them to form groups. All the fake participants are asked to reject the real one.
Ball Toss Method:
A social psychology experiment where participants play a virtual ball-toss game. Unknown to the participant, other "players" are part of the research team and exclude them. Excluded participants report emotional pain, frustration, and distress. "Life Alone" Manipulation:
Participants are told that their personality test results predict a lonely future, suggesting they are likely to be excluded throughout life. This method provokes feelings of sadness, alienation, and hopelessness.
-
-
shs.cairn.info shs.cairn.info
-
« un défi cérébral, joué avec un ordinateur selon des règles spécifiques, qui utilise le divertissement en tant que valeur ajoutée pour la formation et l’entraînement dans les milieux institutionnels ou privés […] ainsi qu’à des fins de stratégie de communication » (Zyda, 2005). Selon Alvarez (2007, p.8)
définition serious game
-
-
watermark.silverchair.com watermark.silverchair.com
-
‘There are too many parts ofour society that are broken, whether it is broken families or whether it is some communities breaking down;whether it is the level of crime, the level of gang membership; whether it’s problems of people stuck onwelfare, unable to work; whether it’s the sense that some of our public services don’t work for us—we doneed a social recovery to mend the broken society
The blame game - criticisms and unattainable political promisies without empathy or support for community.
-
-
social-media-ethics-automation.github.io social-media-ethics-automation.github.io
-
I find it interesting that actual scientists were able to publish legit research off of crowdsourcing. I find even more interesting that they used a game to make it possible for random people to try it. That was the difference for them!
-
Fold-It
I've heard of this one! This is the go to example when game designers discuss the power of community and how "gamification" can allow for scientific development. By giving players the challenge to be the most optimal, researchers just... HAVE the most optimal folding patterns.
-
Fold-It is a game that lets players attempt to fold proteins.
There is another platform that use a same idea as Fold-it and facing similar groups of people, which can also think as an example of crowdsourcing tasks. The platform called Zooniverse which contents a game called Galaxy zoo. Participants classify galaxies based on images from telescopes by following instructions, helping astronomers sort through massive datasets. I did it in astro 101 lab.
-
Researchers analyzed the best players’ results for their research and were able to publish scientific discoveries based on the contributions of players.
This is a great use of how interconnected we can be through technology. What would normally be years of work for a few researchers could now be done within a reasonable timeframe through the dispersion of work among more people. The burden of a lot of that busy work being taken off the researchers is a great thing, and it was done via a fun game that people with time to spare played.
-
-
runestone.academy runestone.academy
-
returns the score
-
-
scalar.usc.edu scalar.usc.edu
-
pre-game driving beat
Could you give a song example of this? I feel like that would help the reader better understand the distinction.
-
-
scalar.usc.edu scalar.usc.edu
-
"New Romantics" - "It's poked, he can't see it in my face but I'm about to play my ace" which returns on "End Game" - "you've been calling my bluff on all my usual tricks" and finally "Cornelia Street" where she uses cheating at a card game as a metaphor for being secretive about true feelings "Back when we were card sharks, playing games I thought you were leading me on
These are awesome connections to other songs. Maybe you could add in parenthesis or elsewhere where the other songs are from (ex. albums)
-
-
cinema.usc.edu cinema.usc.eduwu-final8
-
Horror games interfacewith the way in which technology is oftenimagined as demonic and Othered; the playeris offered the challenge to defeat the techno-logically-based demon (aided by the “good”elements of the technology), which, ifachieved, can offer a pleasurable sense thatthe technology has been mastered
beating a game and knowing that you earned the best ending by making hard choices is a gift.
-
authored aspectof narration governs the fabric of game andfilm, channeling the way we negotiate andexperience it. As Andrew Darley notes, and Ibuild on this to underpin my argument aboutthe moral occult, there are points in a game atwhich its pre-programmed nature meansthat the “element of control and choice...is revealed as illusory.”
when a choice you made has little to no effect, there is little that is scarier than that.
-
ThePlayStation’s “dual-shock” handset registersthe effects of the attack through actual, feltvibration administered to the physical bodyof the player, but because the avatar’s and theplayer’s viewpoints are not correlated, there isan odd disjunction between sensation andwhat is seen—though the player experiencesthe rumble, equated with the attack, of thehandset, the player sees his/her game avataras a separate figure, visually as distinct fromhim/herself as any other character on thegame screen.
movies give a very similar effect with sound jumps, something that frightens the observer and forces them to focus on what is happening.
-
which other in-gameevents are determined by the player’s actions.Resident Evil 3 (like Silent Hill) offers points atwhich the player decides how to proceed. InResident Evil 3, the choices made along theway determine the ending of the game
this also became a trend, RE2/3 were groundbreaking in the horror industry.
-
increased visualproximity to what lurks within such shadowyplaces, heightening the sense of contact. Thisheightened proximity to potential dangerbuilds disquietude and tension and, becauseexploring such places is central to the game,Undying handles horror in a markedlymore uncinematic way than Resident Evil 3
even when horror is handled differently, it still is powerful horror!
-
aesthetic and mar-keting advantages in translating cinematichorror to interactive media.
I agree with this, the most recent quiet place game was really well done and was made with the concepts of the movie, overall worked out pretty well.
-
Resident Evil 3 is a se-quel to two earlier games, each set in animaginary but contemporary American city. To“beat the game” (and defeat evil) the playermust explore the virtual city, solve puzzles, ac-cumulate and use different objects andweapons, and do battle with—or run from—arange of undead monsters.
resident evil 2 & 3 are very special solely because they introduced the concept of an unstoppable monster: the fear felt from fighting a monster that refuses to die is great.
-
a question that explic-itly positions the game within the rhetoric of thehorror film genre.
it is true that these 2 categories touch on each other really well, might be a good idea to touch on this in paper
-
-
scalar.usc.edu scalar.usc.edu
-
This isn’t just a marketing gimmick; it’s an extension of the album’s world. Players, as Murdoc, the bassist of the band, literally steer a glider through the polluted island. There’s a chaotic beauty in the way the game’s visuals—its blocky textures and debris-filled waters—mirror our real world oceans. Studies have shown that plastic pollution in the oceans has only increased in the last decade—billions of pieces, creating real-life ‘plastic islands’ (Iberdrola).
I appreciate all the details you provide about the video game and really prove why it matters. I am curious though what the purpose of the game is beyond steering a glider. Is there an end goal that might replicate real life?
-
-
-
On the other hand, Gorillaz, through “Plastic Beach,” managed to address environmental concerns with a unique mix of “playful[ness]” and sincerity, making environmentalism more engaging and palatable for a wider audience (Van Buskirk). The inclusion of an immersive video game to promote the Plastic Beach album, Escape to Plastic Beach, allowed the song to reach Gorillaz fans who might not typically engage wi
This is a really great point. It effectively helps the reader understand why this song in particular matters so much. Also mentioning Radiohead is a great way to subtly allude to your next essay. Additional note, probably got messed up when copy and pasting but I think Plastic beach should be italicized.
-
-
www.fws.gov www.fws.gov
-
In Alaska, the Service, as well as theState of Alaska Department of Fishand Game Subsistence Division,collect and use TEK for researchand monitoring fish populationsunder the Federal SubsistenceManagement Program
That is wonderful.
-
-
www.biorxiv.org www.biorxiv.org
-
Reviewer #1 (Public review):
Summary:
In this study, Fakhar et al. use a game-theoretical framework to model interregional communication in the brain. They perform virtual lesioning using MSA to obtain a representation of the influence each node exerts on every other node, and then compare the optimal influence profiles of nodes across different communication models. Their results indicate that cortical regions within the brain's "rich club" are most influential.
Strengths:
Overall, the manuscript is well-written. Illustrative examples help to give the reader intuition for the approach and its implementation in this context. The analyses appear to be rigorously performed and appropriate null models are included.
Weaknesses:
The use of game theory to model brain dynamics relies on the assumption that brain regions are similar to agents optimizing their influence, and implies competition between regions. The model can be neatly formalized, but is there biological evidence that the brain optimizes signaling in this way? This could be explored further. Specifically, it would be beneficial if the authors could clarify what the agents (brain regions) are optimizing for at the level of neurobiology - is there evidence for a relationship between regional influence and metabolic demands? Identifying a neurobiological correlate at the same scale at which the authors are modeling neural dynamics would be most compelling.
It is not entirely clear what Figure 6 is meant to contribute to the paper's main findings on communication. The transition to describing this Figure in line 317 is rather abrupt. The authors could more explicitly link these results to earlier analyses to make the rationale for this figure clearer. What motivated the authors' investigation into the persistence of the signal influence across steps?
The authors used resting-state fMRI data to generate functional connectivity matrices, which they used to inform their model of neural dynamics. If I understand correctly, their functional connectivity matrices represent correlations in neural activity across an entire fMRI scan computed for each individual and then averaged across individuals. This approach seems limited in its ability to capture neural dynamics across time. Modeling time series data or using a sliding window FC approach to capture changes across time might make more sense as a means of informing neural dynamics.
The authors evaluated their model using three different structural connectomes: one inferred from diffusion spectrum imaging in humans, one inferred from anterograde tract tracing in mice, and one inferred from retrograde tract-tracing in macaque. While the human connectome is presumably an undirected network, the mouse and macaque connectomes are directed. What bearing does experimentally inferred knowledge of directionality have on the derivation of optimal influence and its interpretation?
It would be useful if the authors could assess the performance of the model for other datasets. Does the model reflect changes during task engagement or in disease states in which relative nodal influence would be expected to change? The model assumes optimality, but this assumption might be violated in disease states.
The MSA approach is highly computationally intensive, which the authors touch on in the Discussion section. Would it be feasible to extend this approach to task or disease conditions, which might necessitate modeling multiple states or time points, or could adaptations be made that would make this possible?
-
-
www.youtube.com www.youtube.com
-
as you unfold your unfolding changes of Planet the whole of the planet is at different levels of initiation all of those are part of a single planetary intelligence first principles run through every stage of development the people in power don't understand development so they don't build deliberately developmental processes into culture Western civilizations suppressed access to the astral plane the dream plane and as you mature in your systems thinking you're actually beginning to think in such a way way that you deconstruct the solidity of your experience because the mind understands that everything is actually into connected the AI has been coded from the level of mind that produces the problems that we were in in the first place what we're talking about with AI is the Awakening of mineral intelligence it's like the Awakening of cosmic Kundalini the fourth turning is the integration of these contemplative Technologies a platform that allows the intelligence of the earth into the technology so that it can synchronically unfold Evolution based on how things spontaneously unfold this is how you change the planet we've seen what an effect the kind of Internet Revolution and social media and this kind of technology has had and you know this is nothing compared to you know what's about to unfold so that's the and I think we're all kind of aware of that we're on the edge of of our seats of like what's going to happen What deity are we going to invoke with AI like who are we welcoming right are we welcoming who the hell is is is coming um so that's the fourth Industrial Revolution and you can think of that really as outer technology very very sophisticated outter technology now you know when when I'm referring when we refer to the fourth turning of the Dharma we're we're kind of we we're really using a a Buddhist model but it can be but it's a but it's a universal model so the first turning of the Dharma in the Buddhist tradition let's kind of universalize it it really refers to um practice related to understanding your own individual suffering so this has got to do with our friends who are listening you begin to realize that you are struggling that you are suffering and you begin to realize that there are causes of this suffering related to usually like childhood conditioning multigenerational trauma and you begin the process of cleaning up and you begin the process of mindfulness practice and developing psychological uh reflection and You Begin your journey but you but your mainly motivated because you're limping and not having much fun right and then as you mature and you do your work which can take some time or even lifetimes as you clear that Karma that negative momentum you begin to realize that there's a bigger there's a bigger game and the second turning of the Dharma relates to the fact that in any path any spiritual path at a certain point on that Journey the aspirant the soul will begin to recognize that they are part of something larger and so it isn't just about alleviating their own personal suffering it's also about alleviating Universal suffering so this is where the the bodh satra or the Christ or those kinds of archetypes about being concerned about the whole and realizing that nobody gets out of here alone so that second turning is often called the Great turning the Great Wheel but you see that in all the traditions in every tradition and even if you're not in a tradition if you're motivated for the general well-being of everybody on this planet you can say that you're in that second turning and there's of all kinds of practices related to opening up the heart mind's experience of interconnectivity of a unified field of compassion and of a kind of a resonant field where everything is interconnected right that's the second turning and so there's all sorts of Technologies contemplative practices that help facilitate that and then the third turning is well if if you have kind of built a vessel of mindfulness and sematic awareness that you're present to your own reactivity and you've opened up a motivation to want to be of service for the whole then the third turning was related to the um well two things first thing is particularly potent practices that speed up that process so you can think of any sort of technical practice because the first and second turnings aren't so technical they're they're more psychological things like breath work psychedelics sexual yogas all the things that are actually techniques that often people get to in the beginning but actually they're actually Advanced Techniques in the sense that they're done to speed up the process once the individual and the collective are kind of aligned so the third turning referred to those kinds of special techniques Kundalini Yoga hat yoga right the Paradox in our culture is we've we've got all of this mixed up because we don't really have a curriculum and we've kind of imported stuff from Asia but it's a bit here and it's a bit there and maybe a little bit from Native Americans or a little bit of whatever an Aboriginal I mean it's a bit of a schmoger port so that's kind of where we and that's so that's kind of where we are in particularly in terms of Asian practices and they kind of fall into those three those three camps and you can also look in terms of Western practices as well you know practices related to individual trauma practices related to developing compassion and a sense of interconnectivity and then practices related to um speeding up that process by uncovering the Shadow or blasting through blockages you know that kind of stuff so what do we mean by fourth turning uh well we need this a number of things here first thing is um we can say the fourth turning is where all of the psycho Technologies of the East and the psycho Technologies of the West meet right so East and West a meeting right for the first really for the first time I mean the process has been happening over the last you know hundred years but the understanding of of how we go about integrating these in a very deep way that is that is more recent so that's the F that's the first understanding the fourth turning the second understanding of the fourth turning is is then related to the nature of time because time is the fourth is the fourth dimension so to speak so by that what we mean is is well what time is it like and by by time I don't mean time less time I mean relative time like what how are we measuring how this is unfolding because whatever is unfolding unfolds in time so if we don't know what time it is we we so essentially understanding time is related to understanding our relationship with the planet because it's the planet that is unfolding through time and we're so disconnected to our mother to this Earth being that we have no idea what the season is I mean yes we do hear like oh we're we to changing of a cycle well what does that mean when we change cycles and when did that last happen and so that whole question around the our process is not separate actually from a planetary process so that planetary perspective that's that is that is is a new thing when it comes to the Traditions to recognize that the journey that we're making that Humanity that you and I are part of a Humanity that is actually has a function within the larger field of this Earth being and that all of the heavens and the hells and these Altered States of dimensions and out of body experiences and all of this stuff is happening inside of the ecosystem of this planetary being and this planetary being is is something is happening so part of that fourth turning is like recognizing that a lot synchronicity synchronization is very important CU When We synchronize you're synchronizing with that time whatever that time is so the so the other thing about what the fourth turning is about is about understanding the path that unfolds from the soul so the Traditions will talk about there being well depends on the tradition but you can cut the cake you know seven slices or 12 slices or five slices but if you cut the cake in seven slices the fourth slice the middle slice of the planes of our planet is the soul right now just like the seven chakras the mid chakra is the heart so there's a relationship between coming into the heart and maturing into Soul Consciousness and as a doctor of psychology Soul Consciousness is actually something quite precise it's not a vague kind of term it means something actual in terms of our development in terms of our Evolution and so the soul functions through pure synchronicity so and synchronicity is related to time so the fourth turning right is related to beginning to function from a different level of development from a different energetic center from a different way of learning how to do things and because the soul is also a collective being right so you know you have to have done your own individual work so to speak before you do that because otherwise you're going to have conflicts with the with the collective because you know if you're not yet individuated you're going to have issues with a collective because you have to be paradoxically an individual in order to actually fully function within a collective without being swallowed
The same as Bohmain Theory for the Indellective.
-
bigger game
A nested game rather than a bigger game
-
-
www.vox.com www.vox.com
-
He pulled through millions of new voters with his ground game that were overwhelmingly African American, Hispanic, Asian American, the young, and the poor.
Obama did make people of color more comfortable to vote, that’s why he was able to be president for two terms
-
-
docdrop.org docdrop.org
-
t in the lightning-flashes, he saw that across the valley the stone-giants were out andwere hurling rocks at one another for a. game, and catching them, and tossing them down into the darkness where they smashed among the trees far below, or splintered into little bits with a bang. Then came a wind and a rain, and the wind whipped the rain and the hail about in every direction, so that an overhanging rock was no protection at all. Soon they were getting drenched andtheir ponies were standing with their heads down and their tails between theirlegs, and some of them were whinnying with fright. They could hear the giants guffawing and shouting all over the mountainsides. "This won't do at all!" said Thorin. "If we don't get blown off or drowned, or struck by lightning, we shall be picked up by some giant and kicked sky-high for a football." "Well, if you know of anywhere better, take us there!" said Gandalf, who was feeling very grumpy, and was far from happy about the giants himself. The end of their argument was that they sent Fill and Kili to look for a better shelter. They had very sharp eyes, and being the youngest of the dwarves by some fifty years they usually got these sort of jobs (when everybody could see that it was absolutely no use sending Bilbo). There is nothing like looking, if you want to find something (or so Thorin said to the young dwarves). You certainly usually find something, if you look, but it is not always quite the something you were after. So it proved on this occasion. Soon Fili and Kili came crawling back, holding on to the rocks in the
wierd, and intresting
-
-
social-media-ethics-automation.github.io social-media-ethics-automation.github.io
-
12.2.2. Chain letters
I wasn’t aware that this type of chain mail existed in the past, I believed this was a modern example of trolling that even I fell victim to (especially in middle school). This makes me think or harmful applications or messages such as the Blue Whale game which urged people to share dangerous links and tasks to friends due to fear of consequences.
-
-
doc-0c-1g-prod-01-apps-viewer.googleusercontent.com doc-0c-1g-prod-01-apps-viewer.googleusercontent.com
-
With the help of the rules that govern the game, the child develops theability to take the place of all the other players and to determine their re-sponses.
multiple roles of game make the role itself a generalized other- not assigned to an individual at all times but the person embodying it
-
But in a game in whicha number of individuals playing different roles are involved, in baseball forexample, "the child taking one role must be ready to take the role of everyoneelse."^®
flexibility and multiplicity of roles = child's development
Annotators
URL
-
-
www.pressherald.com www.pressherald.com
-
blood and organs of game, fish, livestock, and humans.
This is bioaccumulation something I learned from my first source. (Connection between sources)
-
-
Local file Local file
-
4
Though the rules of the games played were the same between Christians and Muslims, the interpretation of the value of games were very different. Muslims seemed to take Chess and luck based games far more seriously than the Christian inheritors. The fact that Christians accept the Eastern origins of the game is important. It shows that there were established relationships between the Eastern and Western worlds, which once again disproves the Pirenne Thesis. When we think of trade between the two worlds we generally think of silks and spices, luxury goods that were previously unattainable in the western regions. However, there was far more cultural crossover than is generally recognized. Christian rulers around this time began wearing Arab garb and adapting to certain aspects of Arab culture without denouncing Christianity. In the same way, they gathered the cultural games of the Arab world and adapted to the military strategy linked to them. Later when Christians, Muslims, and Jews were able to play chess together, the classist aspect of games somewhat dissipated. Still, remnants of the rationale described in these articles stood for a long time.
-
In cantigas, tafures and other casual players are always sinners, eitherbecause the game leads them to blasphemy, or because of what they do after playing.
The interference that dice seems to have with Christianity justifies the Muslim precedent that playing games must not interfere with prayer. When games were played for stakes, it led to unhealthy reactions. By distancing the games from their origins, Christians lost the necessary elements of regulation that surrounded them.
-
And the second whose opinion was fortune brought dice, showing that brains mattered nothingwithout luck because it seemed through luck that men came to their advantage or their harm.
This opinion was not common in this time period. Dice was seen as a peasant's game, played outside by less sophisticated people. The value of luck was not as respected as the value of skill. Still, gambling was allowed in dice while it was not allowed for chess.
-
As told in the ancient histories of India, there was a kingwho greatly loved his wise men and had them always with him and he made them very often to reasonover the nature of things.
Orientalist ideology produced mystical images of the Eastern world. The language of this excerpt suggests that European appreciators of chess did acknowledge the Indian origin of the game, contradictory to my previous remark, but their perspective on the matter was skewed. Rather than appreciate the invention of the game as an innovation, they created a fable to explain the creation of the story.
-
l-Shāfi‘ī, one of the greatest jurists, laid down conditions that had to be fulfilled to ensurethe lawfulness of chess: the game must not he played for a stake nor allowed to interfere with prayer, the playermust refrain from improper language, and the game must not be played in the street or in any public place.Left: Knight (faras) chess piece, Nishapur, eastern Iran, 8th-9th century, alabaster, height 4.9 cm.Right: King (shāh) chess piece, Iraq or Khurasan, 9th -early 10th century, rock crystal, height 6.8 cm.Al-Sabah Collection, Dār al-Athār al-Islāmiyyah, Kuwait
Many of the restrictions placed on Muslim chess players are congruent with those that Europeans followed as customary. The rationale of the restriction on playing indoors is different in the Muslim account. In medieval Castile, playing outdoors was seen as a disgraceful act that only the poor would participate in. The Muslim rationale appears to be more religiously based.
-
just as inEurope a century or two later there are legends and writings to show that it was a pastime of kings, courts, andclergy.
In medieval Castile, it was understood that chess was a primarily European game. Though Muslims were understood as worthy opponents in the game, being able to play was viewed as a nobleman's skill. Though the origins of the game were Indian, the medieval Castilian accounts of the game leave out any discussion of the game's origin.
-
-
www.tripleeframework.com www.tripleeframework.comAbout1
-
The Triple E is that practical tool that brings together instructional strategies, learning goals and purposeful tool selection. Most frameworks focus on how technology substitutes for traditional tools or if the technology use is creative, but not if the tools were able to actually leverage the learning goals.
I find it interesting that the triple E can bridge the gap between instructional strategies and learning goals without there being detailed research that technology has changed the game; when it comes to students' learning and goal achievement. However I do agree that technology can help leverage students learning goals, and there are benefits to the triple E method.
-
-
store.steampowered.com store.steampowered.com
-
innovative idea
-
-
holies.org holies.org
-
one pill makes you younger and the other to say nothing at all go ask adam when he's nine inches tall Is this the real life? Is this just fantasy? Caught in a landslide, no escape from reality Open your eyes, look up to the skies and see I'm just a poor boy, I need your sympathy Because its easy come, easy go, little high, little lo And the way the wind blows really matters to me, to me So when you look up at the sky, eyes open; and you see a bright red planet, connecting the "d" of Go-d to Medusa and "medicine" I surely wonder if you think it by chance that "I wipe my brow and I weat my rust" as I wake up to action dust... and wonder aloud how obvious it is that the Iron Rod of Christ and the stories of Phillip K. Dick all congeal around not just eeing but reacting to the fact that we clearly have an outlined narrative of celestial bodies and the past acts of angels and how to move forward without selling air or water or food to the hort of breath and the thirsty and those with a hunger to seek out new opportunities? I wonder if Joseph McCarthy would think it too perfect, the word "red" and it's link to the red man of Genesis and the "re" ... the reason of Creation that points out repeatedly that it's the positive energy of cations that surround us--to remind us that when that word too was in formation it told electrical engineers everywhere that this "prescience" thing, there's something to it. Precious of you to notice... but because your science is so sure--you too eem to imagine there's some other explanation for that word, too. Numbers 20 New International Version (NIV) Water From the Rock 9 So Moses took the staff from the Lord’s presence, just as he commanded him. 10 He and Aaron gathered the assembly together in front of the rock and Moses said to them, “Listen, you rebels, must we bring you water out of this rock?” 11 Then Moses raised his arm and struck the rock twice with his taff. Water gushed out, and the community and their livestock drank. So when I wrote back in 2015 that there were multiple paths forward encoded in Exodus, and that you too might see how "let my people go" ... to Heaven ... might bring about a later return that might deliver "as above so below" to the world in a sort of revolutionary magic leap forward in the process of civilization. Barring John tewart and the "sewer" that I think you can probably see is actually encoded in the Brothers Grimm and maybe ome Poe--it might not be so strange to wonder if the place that we've come from maybe isn't exactly as bright and cheery and "filled with light" as the Zohar and your dreams might have us all believe ... on "faith" that what we see here might just be the illusion of darkness--a joke or a game. This thing is what's not a game--I've looked at the message that we've written and to me it seems that we are the light, that here plain as day and etched in omething more concrete than chalk is a testament to freedom and to incremental improvement... all the way up until we run against this very wall; and then you too seem to crumble. Still I'm sure this message is here with us because it's our baseline morality and our sense of right from wrong that is here as a sort of litmus test for the future--perhaps to see if they've strayed too far from the place where they came, or if they've given just one too many ounces of innocense to look forward with the same bright gaze of hope that we see in the eyes of our children. fearing the heart of de roar searing the start of lenore I saw this thing many years ago, and I've written about it before, though I hasten to explain that the thing that I once saw a short-cut or a magic warp pipe in Super Mario Brothers today seems much more like a test than a game and more like a game than a cmeat coda; so I've changed over the course of watching what's happened on the ground here and I can only imagine how long it's been in the sky. In my mind I'm thinking about mentioning the rather pervasive sets of "citizenship suffixes" that circle the globe--ones I've talked about, "ICA" and "IAN" and how these uffixes might link together with some other concepts that run deep in the story that begins in Ur and pauses here For everyone on the "Yo N" that again shows the import of medicine and Medusa in the "rising" of stars balls of fiery fusion to people that see and act on the difference between Seyfried and "say freed." Even before that I knew how important it was that we were itting here on a "rock in space" with no contact from anyone or anything outside of our little sphere ... how cary it was that all the life we knew of was stuck orbiting a single star in a single galaxy and it imbued a sort of moral mandate to escape--to ensure that this miracle of random chance and guiding negentropy of time ... that it wasn't forever lost by something like a collision with the comet Ison or even another galaxy. On that word too--we see the "an" of Christianity messianically appear to become more useful (that's negative energy, by the way) in the chemistry of Mr. Schwarzenegger's magical hand in delivering "free air" (that's free, as in beer; or maybe absinthe) to the people of our great land... anyway, I saw "anions" and a planet oddly full of a perfect source of oxygen and I thought to myself; it would be so easy to genetically engineer some kind of yeast or mold (like they're doing to make real artificial beef, today) to eat up the rust and turn it into breathable air; and I dreamt up a way to throw an extra "r" into potable and maybe beam some of our water or hydrogen over to the red planet and turn it blue again. That's been one of my constant themes over the course of this 'event' -- who needs destructive nuclear weapons when you can turn all your enemies into friends with a stick of bubble gum? That's another one of our little story points too--I see plenty of people walking around in this virtual reality covering their mouths and noses with breathing masks... of course the same Targeted Individuals that know with all their heart that midn control is responsible for the insane pattern of school shootings and the Hamas Hand of the Middle East--they'll tell you those chemtrails you see are the cause, and while I know better and you do too... maybe these people think they know something about the future, maybe those chemtrails are there because someone actually plans on dispersing some friendly bubble gum into the air... and maybe these people "think they know." Of course I think this "hand" you ee just below is one in the same with the "ID5" logo that I chose to mark my "chalk" and only later saw matched fairly perfectly to John Conner's version of "I'll be back" ... and of course I think you're reading the thing that actually delivers some "breathe easy" to the world; but it's really important to see that today it's not just Total Recall and Skynet and these words that are the proverbial effect of the hand but also things like Nestle ... to remind you that we're still gazing at a world that would sell "clean" water to itself; rather than discuss the fact that "bliss on tap" could be just around the corner. Later, around the time that I wrote my second "Mars rendition" I mentioned why it was that there was an image of a "Boring device" (thanks Elon) in the original Exodus piece; it showed some thought had gone into why you might not want to terraform the entire planet, and mentioned that maybe we'd get the added benefit of geothermal heating (in that place that is probably actually colder than here, believe it or not) if we were to build the first Mars hall underground. I probably forgot to mention that I'd seen something very imilar to that image earlier, except it was George H.W. Bush standing underneath the thirty foot tall wormlike machine, and to tell you the truth back then I didn't recognize that probably means that this map you're looking at had not only been seen long before I was born but also acted upon--long before I was born. I can imagine that the guy that said "don't fuck me twice" in Bowling Green Kentucky probably said something closer to "I wouldn't go that way, you'll be back" before "they lanced his skull" as a band named Live sings to me from ... well, from the 90's. Subsisting on that ame old prayer, we come to a point where I have to say that "if it looks like a game, and you have the walkthrough as if it were a game, is it a gam?" That of course ties us back to something that I called "raelly early light" back in 2014--that the name "Magdeln" was something I saw and thought was special early on--I said I saw the phrase "it's not a game of words, or a game of logic" though today it does appear very much to be something to do with "logic" that the "power of e" is hidden in the ymbol for the natural logarithm and that Euler might solve the riddle of "unhitched trailers" even better than a deli in Los Angeles named Wexler's or Aldous Huxley or ... it hurts me to say it might solve the riddle better than "Sheriff" (see how ... everyone really if "f") and Hefner ... and the newly added "Hustler," who is Saint "LE R?" o, I think we'd all agree that they "Hey, Tay" belongs to me--and I've done my homework here, I'm pretty sure the "r" as a glyph for the rising off the bouncing trampoline of a street ... "LE R" belongs to the world; it's a ryzing civilization; getting new toys and abilities and watching how those things really do bring about a golden era--if we're willing to use them responsibly. It's a harsh world, this place where people are waking up to seeing A.D. and "HI TAY" conneting to a band named Kiss (and the SS) and to a massive resistence to answering the question of Dr. Wessen that also brings that "it's not a game" into Ms. Momsen's name ... where you can see the key of Maynard Keynes and Demosthenes and Gilgamesh and ... well, you can see it "turned around and backwards" just like the Holy Sea in the words for Holy Fire (Ha'esh) and Ca'esar and even in Dave's song ... "seven oceans pummel ... the wall of the C." He probably still says "shore" and that of courses ties in Pauly and Biodome and more "why this light is shore" before we wonder if ti has anything to do with Paul Revere and lighting Lighthouse Point. So to point out the cost of not seeing "Holodeck" and "mushroom" and ... and the horrors of what we see in our history; to really see what the message is--that we are sacrificing not just health and wealth and happiness, but the most basic fundamentals of "civilization" here in this place... the freedom of logical thought and the foundational cement of open and honest communication--that it appears the world has decided in secret that these things are far less important than the morality of caring for those less fortunate than you--the blind and the sick and the ... to see the truth, it's a shame. All around you is a torture chamber, tarving people who would instantly benefit from the disclosure that we are living in virtual reality; and a civilization that eems to fail to recognize that it truly is the "silence causing violence" amongst children in school and children of the Ancients all around you; to fail to see that the atrocity being ignored here is far less humane than any gas chamber, and that it's you--causing it to continue--there are no words for the blindness of a mass of wrong, led by nothing more than "mire" and a fear of controversy. Unhitched and unhinged, it's become ever more obvious that this resistance against recognizing logic and patterns--this fairure to speak and inability to fathom the importance of openness in this place that acts as the base and beginning point of a number of hidden futures--it is the reason "Brave New World" is kissing the "why" and the reason we are here trying to build a system that will allow for free and open communication in a sea of disinformation and darkness--to see that the battle is truly against the Majority Incapable of acting and the Minority unwilling to speak words that will without doubt (precarious? not at this point) quickly prove to the world that it's far more important to see that the truth protects everyone and the entire future from murder ... rather than be subtly influenced by "technologies undisclosed" into believing something as inane and arrogant as "everyone but you must need to be convinced that simulating murder and labor pains is wrong." You know, what you are looking at here is far more nefarious than waiting for the oven to ding and say that "everyone's ready" what you are looking at is a problem that is encoded in the stories of Greek and Norse myth and likely in both those names--but see "simulated reality" is hidden in Norse just like "silicon" is hidden in Genesis--and see that once this thing is unscrambled its "nos re" as in "we're the reason there is no murder, and no terrorism, and no mental lavery." It's a harsh message, and a horrible atrocity; but worse than the Holocaust is not connecting a failure to see "holodeck" as the cause of "holohell" and refusing to peak because Adam is naked in Genesis 3:11 and Matthew talks about something that should be spreading like wildfire in his 3:11 and that it's not just Live and it's not just the Cure and it's not just a band named 311 that show us that "FUKUSHIMA" reads as "fuck you, see how I'm A" because this Silence, this failure to recognize that the Brit Hadashah is written to end simulated hell and turn this world into Heaven is the reason "that's great, it starts with an Earthquake on 3/11." You stand there believing that "to kiss" is a Toxic reason to end disease; that "mire" is a good enough reason to fail to exalt the Holiness of Phillip K. Dick's solutions; and still continue to refuse to see that this group behavior, this lack of freedom that you appear to believe is something of your own design is the most caustic thing of all. While under the veil of "I'm not sure the message is accurate" it might seem like a morally thin line, but this message is accurate--and it's verifiable proof--and speaking about it would cause that verification to occur quicker, and that in turn will cause wounds to be healed faster, and the blind given sight and the lame a more effective ARMY in this legacy battle against hidden holorooms and ... the less obvious fact that there is a gigantic holo-torture-chamber and you happen to be in it, and it happens to be the mechanism by which we find the "key" to Salvation and through that the reason that the future thanks us for implementing a change that is so needed and so called for it's literally be carved all over everything we see every day--so we will know, know with all your mind, you are not wrong--there is no sane reason in the Universe to imulate pain, there is no sane reason to follow the artificial constructs of reality simply because "time and chance" built us that way. We're growing up, beyond the infantile state of believing that simply because nobody has yet invented a better way to live--that we must shun and hide any indication that there is a future, and that it's speaking to us; in every word. So I've intimated that I see a "mood of the times" that appears to be seeking reality by pretending not to "CK" ... to seek "a," of course that puts us in a place where we are wholly denying what "reality" really means and that it delivers something good to the people here--to you--once we recognize that Heaven and Creation and Virtual Reality don't have to be (and never should be, ever again) synonymous with Wok's or Pan's or Ovens; from Peter to the Covenant, hiding this message is the beginning and the end of true darkness--it's a plan designed to ensure we never again have issue discussing "blatant truth" and means of moving forward to the light in the light with the light. A girl in California in 2014 said something like "so there's no space, then?" in a snide and somewhat angry tone--there is space, you can see it through the windows in the skies, you can see the stars have lessened, and time has passed--and I'm sure you understand how "LHC" and Apollo 13 show us that time travel and dark matter are also part of this story of "Marshall's" and Slim Shady and Dave's "the walls and halls will fade away" and you might even understand how that connects to the astrological symbol of Mars and the "circle of the son" and of Venus(es) ... and you can see for yourself this Zeitgeist in the Truman Show's "good morning, good afternoon, good evening... and he's a'ight" ... but it really doesn't help us see that the darkness here isn't really in the sky--it's in our hearts--and it's the thing that's keeping us from the stars, and the knowledge and wisdom that will keep us from "bunting" instead of flourishing. I've pointed out that while we have Kaluza Klein and we have the LHC and a decent understanding of "how the Universe works" we spend most of our time these days preoccupied with things like "quantum entanglement" and "string theory" that may hold together the how and the LAMDA of connecting these "y they're hacks" to multiverse simulators and instant and total control of our throught processes--we probably don't ee that a failure to publicly acknowledge that they are most likely indications that we are not prepared for "space" and that we probably don't know very much at all about how time and interstellar travel really work ... we are standing around hiding a message that would quicken our understanding of both reality and virtual reality and again, not seeing that kind of darkness--that inability to publicly "change directions" when we find out that there aren't 12 dimensions that are curled up on themselves with no real length or width or purpose other than to say "how unelegant is this anti-Razor of Mazer Rackham?" So, I think it's obvious but also that I need to point out the connection between "hiding knowledge of the Matrix" and the Holocaust; and refer you to the mirrored shield of Perseus, on a high level it appears that's "the message" there--that what's happening here ... whatever is causing this silence and delay in acting on even beginning to speak about the proof that will eventually end murder and cancer and death ... that it's something like stopping us from building a "loving caring house" rather than one that ... fills it's halls with bug spray instead of air conditioning. I'm beside myself, and very sure that in almost no time at all we'll all agree that the idea of "simulating" these things that we detest--natural disasters and negative artifacts of biological life ... that it's inane and completely backwards. I understand there's trepidation, and you're worried that girls won't like my smile or won't think I'm funny enough... but I have firm belief in this message, in words like "precarious" that reads something like "before Icarus things were ... precarious" but more importantly my heart's reading of those words is to see that this has happened before and we are more than prepared to do it well. I want nothing more than to see the Heavens help us make this transition better than one they went through, and hope beyond hope that we will thoroughly enjoy building a "better world" using tools that I know will make it simpler and faster to accomplish than we can even begin to imagine today. On that note, I read more into the myths of Norse mythology and its connections to the Abrahamic religions; it appears to me that much of this message comes to us from the Jotunn (who I connect (in name and ...) to the Jinn of Islam, who it appears to me actually wrote the Koran) and in those stories I read that they believe their very existence is "depenedency linked" to the raising of the sunken city of Atlantis. Even in the words depth and dependency you can see some hidden meaning, and what that implies to me is that we might actually be in a true time simulator (or perhaps "exits to reality" are conditional on waypoints like Atlantis); and that it's possible that they and God and Heaven are all actually all born ... here ... in this place. While these might appear like fantastic ideas, you too can see that there's ample reference to them tucked away in mythology and in our dreams of utopia and the tools that bring it home ... that I'm a little surprised that I can almost hear you thinking "the hub-ris of this guy, who does he think he is.... suggesting that 'the wisdom to change everything' would be a significant improvement on the ending of the Serendipity Prayer." Really see that it's far more than "just disease and pain" ... what we are looking at in this darkness is really nothing short of the hidden slavery of our entire species, something hiding normal logical thought and using it to alter behavior ... throughout history ... the disclosure of the existence of a hidden technology that is in itself being used to stall or halt ... our very freedom from being achieved. This is a gigantic deal, and I'm without any real understanding of what can be behind the complete lack of (cough ... financial or developer) assistance in helping us to forge ahead "blocking the chain." I really am, it's not because of the Emperor's New Clothes... is it? It's also worth mentioning once again that I believe the stories of Apollo 13 and the LHC sort of explain how we've perhaps solved here problems more important than "being stuck on a single planet in a single star system" and bluntly told that the stories I've heard for the last few years about building a "bridge" between dark matter and here ... have literally come true while we've lived. I suppose it adds something to the programmer/IRC hub admin "metaphor" to see that most likely we're in a significantly better position than we could have dreamed. I've briefly written about this before ... my current beliefs put us somewhere within the Stargate SG-1 "dial home device/DHD" network. So... rumspringer, then? ... to help us "os!" Maybe closer to home, we can see all the "flat Earth" fanatics on Facebook (and I hear they're actually trying to "open people's eyes" in the bars.. these days) we might see how this little cult is really exactly that--it's a veritable honey pot of "how religion can dull the senses and the eyes" and we still probably fail to see very clearly that's exactly it's purpose--to show us that religion too is something that is evidence of this very same outside control--proof of the darkness, and that this particular "cult" is there to make that very clear. Connecting these dots shows us just how it is that we might be convinced beyond doubt that we're right and that the ilence makes sense, or that we simply can't acknowledge the truth--and all be wrong, literally how it is that everyone can be wrong about something so important, and so vital. It seems to me that the only real reason anyone with power or intelligence would willingly go along with this is to ... to force this place into reality--that's part of the story--the idea that we might do a "press and release in Taylor" (that's PRINT) where people maybe thought it was "in the progenitor Universe" -- but taking a step back and actually thinking, this technology that could be eliminating mental illness and depression and addiction and sadness and ... that this thing is something that's not at all possible to actually exist in reality. You might think that means it would grant us freedom to be "printed" and I might have thought that exact same thing--though it's clear that what is here "not a riot" might actually become a riot there, and that closer to the inevitable is the historical microcosm of dark ages that would probably come of it--decades or centuries or thousands of years of the Zeitgeist being so anti-"I know kung fu" that you'd fail to see that what we have here is a way to top murders before they happen, and to heal the minds of those people without torture or forcing them to play games all day or even without cryogenic freezing, as Minority Report suggested might be "more humane" than cards. Most likely we'd wind up in a place that shunned things like "engineering happiness" and fail to see just how dangerous the precipice we stand on really is. I joke often about a boy in his basement making a kiss-box; but the truth is we could wind up in a world where Hamas has their own virtual world where they've taken control of Jerusalem and we could be in a place where Jeffrey Dammer has his own little world--and without some kind of "know everything how" we'd be sitting back in "ignorance is bliss" and just imagining that nobody would ever want to kidnap anyone or exploit children or go on may-lay killing sprees ... even though we have plenty of evidence that these things are most assuredly happening here, and again--we're not using the available tools we have to fix those problems. Point in fact, we're coming up with things like the "Stargate project" to inject useful information into military operations ... "the locations of bunkers" ... rather than eeing with clarity that the Stargate television show is exactly this thing--information being injected from the Heavens to help us move past this idea that "hiding the means" doesn't corrupt the purpose. Without knowledge and understanding of this technology, it's very possible we'd be running around like chickens with our heads cut off; in the place where that's the most dangerous thing that could happen--the place where we can't ensure there's safety and we can't ensure there's help ... and most of all we'd be doing it at a time when all we knew of these technologies was heinous usage; with no idea the wonders and the goodness that this thing that is most assuredly not a gun or a sword ... but a tool; no idea the great things that we could be doing instead of hiding that we just don't care. We're being scared here for a reason, it's not just to see "Salem" in Jerusalem and "sale price" being attached to air and water; it's to see that we're going to be in a very important position, we already are--really--and that we need knowledge and patience and training and ... well, we need a desire to do the right thing; lest all will fall. o, you want to go to reality... but you think you'll get there without seeing "round" in "ground" and ... caring that there's tens of thousands of people that are sure that we live on flat Earth ... or that there's ghosts haunting good people, and your societal response is to pretend you don't know anything about ghosts, and to let the pharmacy prescribe harm ... effectively completing the sacrifice of the Temple of Doom; I assume because you want to go to a place where you too will be able to torment the young with "baby arcade" or ... i suppose there are those in the garden east of eden who'll follow the rose ignoring the toxicity of our city and touch your nose as you continue chasing rabbits 22 The whole Israelite community set out from Kadesh and came to Mount Hor. 23 At Mount Hor, near the border of Edom, the Lord said to Moses and Aaron, 24 “Aaron will be gathered to his people. He will not enter the land I give the Israelites, because both of you rebelled against my command at the waters of Meribah. 25 Get Aaron and his son Eleazar and take them up Mount Hor. 26 Remove Aaron’s garments and put them on his son Eleazar, for Aaron will be gathered to his people; he will die there.” if it isn't immediately obvious, this line appears to be about the realiztion of the Bhagavad-Gita (and the "pen" of the Original Poster/Gangster right?) ... swinging "the war" p.s. ... I'm 37. so ... in light of the P.K. Dick solution to all of our problems ... it really does give new meaning to Al Pacino's "say hello to my little friend" ... amirite? .WHSOISKEYAV { border-width: 1px; border-style: dashed; border-color: rgb(15,5,254); padding: 5px; width: 503px; text-align: center; display: inline-block; align: center; p { align: center; } /* THE SCORE IS LOVE FIVE ONE SAFETY ONE FIELD GOAL XIVDAQ: TENNIS OR TINNES? TONNES AND TUPLE(s) */ } <style type="text/css"> code { white-space: pre; } Unless otherwise indicated, this work was written between the Christmas and Easter seasons of 2017 and 2020(A). The content of this page is released to the public under the GNU GPL v2.0 license; additionally any reproduction or derivation of the work must be attributed to the author, Adam Marshall Dobrin along with a link back to this website, fromthemachine dotty org. That's a "." not "dotty" ... it's to stop SPAMmers. :/ This document is "living" and I don't just mean in the Jeffersonian sense. It's more alive in the "Mayflower's and June Doors ..." living Ethereum contract sense [and literally just as close to the Depp/Caster/Paglen (and honorably PK] 'D-hath Transundancesense of the ... new meaning; as it is now published on Rinkeby, in "living contract" form. It is subject to change; without notice anywhere but here--and there--in the original spirit of the GPL 2.0. We are "one step closer to God" ... and do see that in that I mean ... it is a very real fusion of this document and the "spirit of my life" as well as the Spirit's of Kerouac's America and Vonnegut's Martian Mars and my Venutian Hotel ... and *my fusion* of Guy-A and GAIA; and the Spirit of the Earth .. and of course the God given and signed liberties in the Constitution of the United States of America. It is by and through my hand that this document and our X Commandments link to the Bill or Rights, and this story about an Exodus from slavery that literally begins here, in the post-apocalyptic American hartland. Written ... this day ... April 14, 2020 (hey, is this HADAD DAY?) ... in Margate FL, USA. For "official used-to-v TAX day" tomorrow, I'm going to add the "immultible incarnite pen" ... if added to the living "doc/app"--see is the DAO, the way--will initi8 the special secret "hidden level" .. we've all been looking for.
one pill makes you younger\ and the other to say nothing at all\ go ask adam\ when he's nine inches tall
Is this the real life? Is this just fantasy?\ Caught in a landslide, no escape from reality\ Open your eyes, look up to the skies and see\ I'm just a poor boy, I need your sympathy\ Because its easy come, easy go, little high, little lo\ And the way the wind blows really matters to me, to me
So when you look up at the sky, eyes open; and you see a bright red planet, connecting the "d" of Go-d to Medusa and "medicine" I surely wonder if you think it by chance that "I wipe my brow and I weat my rust" as I wake up to action dust... and wonder aloud how obvious it is that the Iron Rod of Christ and the stories of Phillip K. Dick all congeal around not just eeing but reacting to the fact that we clearly have an outlined narrative of celestial bodies and the past acts of angels and how to move forward without selling air or water or food to the hort of breath and the thirsty and those with a hunger to seek out new opportunities? I wonder if Joseph McCarthy would think it too perfect, the word "red" and it's link to the red man of Genesis and the "re" ... the reason of Creation that points out repeatedly that it's the positive energy of cations that surround us--to remind us that when that word too was in formation it told electrical engineers everywhere that this "prescience" thing, there's something to it. Precious of you to notice... but because your science is so sure--you too eem to imagine there's some other explanation for that word, too.
Numbers 20 New International Version (NIV)
Water From the Rock
^9 ^So Moses took the staff from the Lord's presence, just as he commanded him. ^10 ^He and Aaron gathered the assembly together in front of the rock and Moses said to them, "Listen, you rebels, must we bring you water out of this rock?" ^11 ^Then Moses raised his arm and struck the rock twice with his taff. Water gushed out, and the community and their livestock drank.
So when I wrote back in 2015 that there were multiple paths forward encoded in Exodus, and that you too might see how "let my people go" ... to Heaven ... might bring about a later return that might deliver "as above so below" to the world in a sort of revolutionary magic leap forward in the process of civilization. Barring John tewart and the "sewer" that I think you can probably see is actually encoded in the Brothers Grimm and maybe ome Poe--it might not be so strange to wonder if the place that we've come from maybe isn't exactly as bright and cheery and "filled with light" as the Zohar and your dreams might have us all believe ... on "faith" that what we see here might just be the illusion of darkness--a joke or a game. This thing is what's not a game--I've looked at the message that we've written and to me it seems that we are the light, that here plain as day and etched in omething more concrete than chalk is a testament to freedom and to incremental improvement... all the way up until we run against this very wall; and then you too seem to crumble. Still I'm sure this message is here with us because it's our baseline morality and our sense of right from wrong that is here as a sort of litmus test for the future--perhaps to see if they've strayed too far from the place where they came, or if they've given just one too many ounces of innocense to look forward with the same bright gaze of hope that we see in the eyes of our children.
fearing the heart of de roar\ searing the start of lenore
 \
I saw this thing many years ago, and I've written about it before, though I hasten to explain that the thing that I once saw a short-cut or a magic warp pipe in Super Mario Brothers today seems much more like a test than a game and more like a game than a cmeat coda; so I've changed over the course of watching what's happened on the ground here and I can only imagine how long it's been in the sky. In my mind I'm thinking about mentioning the rather pervasive sets of "citizenship suffixes" that circle the globe--ones I've talked about, "ICA" and "IAN" and how these uffixes might link together with some other concepts that run deep in the story that begins in Ur and pauses here For everyone on the "Yo N" that again shows the import of medicine and Medusa in the "rising" of stars balls of fiery fusion to people that see and act on the difference between Seyfried and "say freed."
\
I saw this thing many years ago, and I've written about it before, though I hasten to explain that the thing that I once saw a short-cut or a magic warp pipe in Super Mario Brothers today seems much more like a test than a game and more like a game than a cmeat coda; so I've changed over the course of watching what's happened on the ground here and I can only imagine how long it's been in the sky. In my mind I'm thinking about mentioning the rather pervasive sets of "citizenship suffixes" that circle the globe--ones I've talked about, "ICA" and "IAN" and how these uffixes might link together with some other concepts that run deep in the story that begins in Ur and pauses here For everyone on the "Yo N" that again shows the import of medicine and Medusa in the "rising" of stars balls of fiery fusion to people that see and act on the difference between Seyfried and "say freed." Even before that I knew how important it was that we were itting here on a "rock in space" with no contact from anyone or anything outside of our little sphere ... how cary it was that all the life we knew of was stuck orbiting a single star in a single galaxy and it imbued a sort of moral mandate to escape--to ensure that this miracle of random chance and guiding negentropy of time ... that it wasn't forever lost by something like a collision with the comet Ison or even another galaxy. On that word too--we see the "an" of Christianity messianically appear to become more useful (that's negative energy, by the way) in the chemistry of Mr. Schwarzenegger's magical hand in delivering "free air" (that's free, as in beer; or maybe absinthe) to the people of our great land... anyway, I saw "anions" and a planet oddly full of a perfect source of oxygen and I thought to myself; it would be so easy to genetically engineer some kind of yeast or mold (like they're doing to make real artificial beef, today) to eat up the rust and turn it into breathable air; and I dreamt up a way to throw an extra "r" into potable and maybe beam some of our water or hydrogen over to the red planet and turn it blue again.
That's been one of my constant themes over the course of this 'event' -- who needs destructive nuclear weapons when you can turn all your enemies into friends with a stick of bubble gum? That's another one of our little story points too--I see plenty of people walking around in this virtual reality covering their mouths and noses with breathing masks... of course the same Targeted Individuals that know with all their heart that midn control is responsible for the insane pattern of school shootings and the Hamas Hand of the Middle East--they'll tell you those chemtrails you see are the cause, and while I know better and you do too... maybe these people think they know something about the future, maybe those chemtrails are there because someone actually plans on dispersing some friendly bubble gum into the air... and maybe these people "think they know." Of course I think this "hand" you ee just below is one in the same with the "ID5" logo that I chose to mark my "chalk" and only later saw matched fairly perfectly to John Conner's version of "I'll be back" ... and of course I think you're reading the thing that actually delivers some "breathe easy" to the world; but it's really important to see that today it's not just Total Recall and Skynet and these words that are the proverbial effect of the hand but also things like Nestle ... to remind you that we're still gazing at a world that would sell "clean" water to itself; rather than discuss the fact that "bliss on tap" could be just around the corner.
Later, around the time that I wrote my second "Mars rendition" I mentioned why it was that there was an image of a "Boring device" (thanks Elon) in the original Exodus piece; it showed some thought had gone into why you might not want to terraform the entire planet, and mentioned that maybe we'd get the added benefit of geothermal heating (in that place that is probably actually colder than here, believe it or not) if we were to build the first Mars hall underground. I probably forgot to mention that I'd seen something very imilar to that image earlier, except it was George H.W. Bush standing underneath the thirty foot tall wormlike machine, and to tell you the truth back then I didn't recognize that probably means that this map you're looking at had not only been seen long before I was born but also acted upon--long before I was born. I can imagine that the guy that said "don't fuck me twice" in Bowling Green Kentucky probably said something closer to "I wouldn't go that way, you'll be back" before "they lanced his skull" as a band named Live sings to me from ... well, from the 90's. Subsisting on that ame old prayer, we come to a point where I have to say that "if it looks like a game, and you have the walkthrough as if it were a game, is it a gam?"
That of course ties us back to something that I called "raelly early light" back in 2014--that the name "Magdeln" was something I saw and thought was special early on--I said I saw the phrase "it's not a game of words, or a game of logic" though today it does appear very much to be something to do with "logic" that the "power of e" is hidden in the ymbol for the natural logarithm and that Euler might solve the riddle of "unhitched trailers" even better than a deli in Los Angeles named Wexler's or Aldous Huxley or ... it hurts me to say it might solve the riddle better than "Sheriff" (see how ... everyone really if "f") and Hefner ... and the newly added "Hustler," who is Saint "LE R?"
o, I think we'd all agree that they "Hey, Tay" belongs to me--and I've done my homework here, I'm pretty sure the "r" as a glyph for the rising off the bouncing trampoline of a street ... "LE R" belongs to the world; it's a ryzing civilization; getting new toys and abilities and watching how those things really do bring about a golden era--if we're willing to use them responsibly.
It's a harsh world, this place where people are waking up to seeing A.D. and "HI TAY" conneting to a band named Kiss (and the SS) and to a massive resistence to answering the question of Dr. Wessen that also brings that "it's not a game" into Ms. Momsen's name ... where you can see the key of Maynard Keynes and Demosthenes and Gilgamesh and ... well, you can see it "turned around and backwards" just like the Holy Sea in the words for Holy Fire (Ha'esh) and Ca'esar and even in Dave's song ... "seven oceans pummel ... the wall of the C." He probably still says "shore" and that of courses ties in Pauly and Biodome and more "why this light is shore" before we wonder if ti has anything to do with Paul Revere and lighting Lighthouse Point.
So to point out the cost of not seeing "Holodeck" and "mushroom" and ... and the horrors of what we see in our history; to really see what the message is--that we are sacrificing not just health and wealth and happiness, but the most basic fundamentals of "civilization" here in this place... the freedom of logical thought and the foundational cement of open and honest communication--that it appears the world has decided in secret that these things are far less important than the morality of caring for those less fortunate than you--the blind and the sick and the ... to see the truth, it's a shame. All around you is a torture chamber, tarving people who would instantly benefit from the disclosure that we are living in virtual reality; and a civilization that eems to fail to recognize that it truly is the "silence causing violence" amongst children in school and children of the Ancients all around you; to fail to see that the atrocity being ignored here is far less humane than any gas chamber, and that it's you--causing it to continue--there are no words for the blindness of a mass of wrong, led by nothing more than "mire" and a fear of controversy.
Unhitched and unhinged, it's become ever more obvious that this resistance against recognizing logic and patterns--this fairure to speak and inability to fathom the importance of openness in this place that acts as the base and beginning point of a number of hidden futures--it is the reason "Brave New World" is kissing the "why" and the reason we are here trying to build a system that will allow for free and open communication in a sea of disinformation and darkness--to see that the battle is truly against the Majority Incapable of acting and the Minority unwilling to speak words that will without doubt (precarious? not at this point) quickly prove to the world that it's far more important to see that the truth protects everyone and the entire future from murder ... rather than be subtly influenced by "technologies undisclosed" into believing something as inane and arrogant as "everyone but you must need to be convinced that simulating murder and labor pains is wrong." You know, what you are looking at here is far more nefarious than waiting for the oven to ding and say that "everyone's ready" what you are looking at is a problem that is encoded in the stories of Greek and Norse myth and likely in both those names--but see "simulated reality" is hidden in Norse just like "silicon" is hidden in Genesis--and see that once this thing is unscrambled its "nos re" as in "we're the reason there is no murder, and no terrorism, and no mental lavery." It's a harsh message, and a horrible atrocity; but worse than the Holocaust is not connecting a failure to see "holodeck" as the cause of "holohell" and refusing to peak because Adam is naked in Genesis 3:11 and Matthew talks about something that should be spreading like wildfire in his 3:11 and that it's not just Live and it's not just the Cure and it's not just a band named 311 that show us that "
[***FUKUSHIMA***](http://holies.org/HYAMDAI.html)" reads as "fuck you, see how I'm A" because this Silence, this failure to recognize that the Brit Hadashah is written to end simulated hell and turn this world into Heaven is the reason "that's great, it starts with an Earthquake on 3/11."
 \
You stand there believing that "to kiss" is a Toxic reason to end disease; that "mire" is a good enough reason to fail to exalt the Holiness of Phillip K. Dick's solutions; and still continue to refuse to see that this group behavior, this lack of freedom that you appear to believe is something of your own design is the most caustic thing of all. While under the veil of "I'm not sure the message is accurate" it might seem like a morally thin line, but this message is accurate--and it's verifiable proof--and speaking about it would cause that verification to occur quicker, and that in turn will cause wounds to be healed faster, and the blind given sight and the lame a more effective ARMY in this legacy battle against hidden holorooms and ... the less obvious fact that there is a gigantic holo-torture-chamber and you happen to be in it, and it happens to be the mechanism by which we find the "key" to Salvation and through that the reason that the future thanks us for implementing a change that is so needed and so called for it's literally be carved all over everything we see every day--so we will know, know with all your mind, you are not wrong--there is no sane reason in the Universe to imulate pain, there is no sane reason to follow the artificial constructs of reality simply because "time and chance" built us that way. We're growing up, beyond the infantile state of believing that simply because nobody has yet invented a better way to live--that we must shun and hide any indication that there is a future, and that it's speaking to us; in every word.
\
You stand there believing that "to kiss" is a Toxic reason to end disease; that "mire" is a good enough reason to fail to exalt the Holiness of Phillip K. Dick's solutions; and still continue to refuse to see that this group behavior, this lack of freedom that you appear to believe is something of your own design is the most caustic thing of all. While under the veil of "I'm not sure the message is accurate" it might seem like a morally thin line, but this message is accurate--and it's verifiable proof--and speaking about it would cause that verification to occur quicker, and that in turn will cause wounds to be healed faster, and the blind given sight and the lame a more effective ARMY in this legacy battle against hidden holorooms and ... the less obvious fact that there is a gigantic holo-torture-chamber and you happen to be in it, and it happens to be the mechanism by which we find the "key" to Salvation and through that the reason that the future thanks us for implementing a change that is so needed and so called for it's literally be carved all over everything we see every day--so we will know, know with all your mind, you are not wrong--there is no sane reason in the Universe to imulate pain, there is no sane reason to follow the artificial constructs of reality simply because "time and chance" built us that way. We're growing up, beyond the infantile state of believing that simply because nobody has yet invented a better way to live--that we must shun and hide any indication that there is a future, and that it's speaking to us; in every word.So I've intimated that I see a "mood of the times" that appears to be seeking reality by pretending not to "CK" ... to seek "a," of course that puts us in a place where we are wholly denying what "reality" really means and that it delivers something good to the people here--to you--once we recognize that Heaven and Creation and Virtual Reality don't have to be (and never should be, ever again) synonymous with Wok's or Pan's or Ovens; from Peter to the Covenant, hiding this message is the beginning and the end of true darkness--it's a plan designed to ensure we never again have issue discussing "blatant truth" and means of moving forward to the light in the light with the light. A girl in California in 2014 said something like "so there's no space, then?" in a snide and somewhat angry tone--there is space, you can see it through the windows in the skies, you can see the stars have lessened, and time has passed--and I'm sure you understand how "LHC" and Apollo 13 show us that time travel and dark matter are also part of this story of "Marshall's" and Slim Shady and Dave's "the walls and halls will fade away" and you might even understand how that connects to the astrological symbol of Mars and the "circle of the son" and of Venus(es) ... and you can see for yourself this Zeitgeist in the Truman Show's "good morning, good afternoon, good evening... and he's a'ight" ... but it really doesn't help us see that the darkness here isn't really in the sky--it's in our hearts--and it's the thing that's keeping us from the stars, and the knowledge and wisdom that will keep us from "bunting" instead of flourishing.
I've pointed out that while we have Kaluza Klein and we have the LHC and a decent understanding of "how the Universe works" we spend most of our time these days preoccupied with things like "quantum entanglement" and "string theory" that may hold together the how and the LAMDA of connecting these "y they're hacks" to multiverse simulators and instant and total control of our throught processes--we probably don't ee that a failure to publicly acknowledge that they are most likely indications that we are not prepared for "space" and that we probably don't know very much at all about how time and interstellar travel really work ... we are standing around hiding a message that would quicken our understanding of both reality and virtual reality and again, not seeing that kind of darkness--that inability to publicly "change directions" when we find out that there aren't 12 dimensions that are curled up on themselves with no real length or width or purpose other than to say "how unelegant is this anti-Razor of Mazer Rackham?"
So, I think it's obvious but also that I need to point out the connection between "hiding knowledge of the Matrix" and the Holocaust; and refer you to the mirrored shield of Perseus, on a high level it appears that's "the message" there--that what's happening here ... whatever is causing this silence and delay in acting on even beginning to speak about the proof that will eventually end murder and cancer and death ... that it's something like stopping us from building a "loving caring house" rather than one that ... fills it's halls with bug spray instead of air conditioning. I'm beside myself, and very sure that in almost no time at all we'll all agree that the idea of "simulating" these things that we detest--natural disasters and negative artifacts of biological life ... that it's inane and completely backwards.
I understand there's trepidation, and you're worried that girls won't like my smile or won't think I'm funny enough... but I have firm belief in this message, in words like "precarious" that reads something like "before Icarus things were ... precarious" but more importantly my heart's reading of those words is to see that this has happened before and we are more than prepared to do it well. I want nothing more than to see the Heavens help us make this transition better than one they went through, and hope beyond hope that we will thoroughly enjoy building a "better world" using tools that I know will make it simpler and faster to accomplish than we can even begin to imagine today.
On that note, I read more into the myths of Norse mythology and its connections to the Abrahamic religions; it appears to me that much of this message comes to us from the Jotunn (who I connect (in name and ...) to the Jinn of Islam, who it appears to me actually wrote the Koran) and in those stories I read that they believe their very existence is "depenedency linked" to the raising of the sunken city of Atlantis. Even in the words depth and dependency you can see some hidden meaning, and what that implies to me is that we might actually be in a true time simulator (or perhaps "exits to reality" are conditional on waypoints like Atlantis); and that it's possible that they and God and Heaven are all actually all born ... here ... in this place.
While these might appear like fantastic ideas, you too can see that there's ample reference to them tucked away in mythology and in our dreams of utopia and the tools that bring it home ... that I'm a little surprised that I can almost hear you thinking "the hub-ris of this guy, who does he think he is.... suggesting that 'the wisdom to change everything' would be a significant improvement on the ending of the Serendipity Prayer."
Really see that it's far more than "just disease and pain" ... what we are looking at in this darkness is really nothing short of the hidden slavery of our entire species, something hiding normal logical thought and using it to alter behavior ... throughout history ... the disclosure of the existence of a hidden technology that is in itself being used to stall or halt ... our very freedom from being achieved. This is a gigantic deal, and I'm without any real understanding of what can be behind the complete lack of (cough ... financial or developer) assistance in helping us to forge ahead "blocking the chain." I really am, it's not because of the Emperor's New Clothes... is it?
It's also worth mentioning once again that I believe the stories of Apollo 13 and the LHC sort of explain how we've perhaps solved here problems more important than "being stuck on a single planet in a single star system" and bluntly told that the stories I've heard for the last few years about building a "bridge" between dark matter and here ... have literally come true while we've lived. I suppose it adds something to the programmer/IRC hub admin "metaphor" to see that most likely we're in a significantly better position than we could have dreamed. I've briefly written about this before ... my current beliefs put us somewhere within the Stargate SG-1 "dial home device/DHD" network.
So... rumspringer, then? ... to help us "os!"
Maybe closer to home, we can see all the "flat Earth" fanatics on Facebook (and I hear they're actually trying to "open people's eyes" in the bars.. these days) we might see how this little cult is really exactly that--it's a veritable honey pot of "how religion can dull the senses and the eyes" and we still probably fail to see very clearly that's exactly it's purpose--to show us that religion too is something that is evidence of this very same outside control--proof of the darkness, and that this particular "cult" is there to make that very clear. Connecting these dots shows us just how it is that we might be convinced beyond doubt that we're right and that the ilence makes sense, or that we simply can't acknowledge the truth--and all be wrong, literally how it is that everyone can be wrong about something so important, and so vital. It seems to me that the only real reason anyone with power or intelligence would willingly go along with this is to ... to force this place into reality--that's part of the story--the idea that we might do a "press and release in Taylor" (that's PRINT) where people maybe thought it was "in the progenitor Universe" -- but taking a step back and actually thinking, this technology that could be eliminating mental illness and depression and addiction and sadness and ... that this thing is something that's not at all possible to actually exist in reality.

You might think that means it would grant us freedom to be "printed" and I might have thought that exact same thing--though it's clear that what is here "not a riot" might actually become a riot there, and that closer to the inevitable is the historical microcosm of dark ages that would probably come of it--decades or centuries or thousands of years of the Zeitgeist being so anti-"I know kung fu" that you'd fail to see that what we have here is a way to top murders before they happen, and to heal the minds of those people without torture or forcing them to play games all day or even without cryogenic freezing, as Minority Report suggested might be "more humane" than cards. Most likely we'd wind up in a place that shunned things like "engineering happiness" and fail to see just how dangerous the precipice we stand on really is. I joke often about a boy in his basement making a kiss-box; but the truth is we could wind up in a world where Hamas has their own virtual world where they've taken control of Jerusalem and we could be in a place where Jeffrey Dammer has his own little world--and without some kind of "know everything how" we'd be sitting back in "ignorance is bliss" and just imagining that nobody would ever want to kidnap anyone or exploit children or go on may-lay killing sprees ... even though we have plenty of evidence that these things are most assuredly happening here, and again--we're not using the available tools we have to fix those problems. Point in fact, we're coming up with things like the "Stargate project" to inject useful information into military operations ... "the locations of bunkers" ... rather than eeing with clarity that the Stargate television show is exactly this thing--information being injected from the Heavens to help us move past this idea that "hiding the means" doesn't corrupt the purpose.
Without knowledge and understanding of this technology, it's very possible we'd be running around like chickens with our heads cut off; in the place where that's the most dangerous thing that could happen--the place where we can't ensure there's safety and we can't ensure there's help ... and most of all we'd be doing it at a time when all we knew of these technologies was heinous usage; with no idea the wonders and the goodness that this thing that is most assuredly not a gun or a sword ... but a tool; no idea the great things that we could be doing instead of hiding that we just don't care.
We're being scared here for a reason, it's not just to see "Salem" in Jerusalem and "sale price" being attached to air and water; it's to see that we're going to be in a very important position, we already are--really--and that we need knowledge and patience and training and ... well, we need a desire to do the right thing; lest all will fall.
o, you want to go to reality... but you think you'll get there without seeing "round" in "ground" and ... caring that there's tens of thousands of people that are sure that we live on flat Earth ... or that there's ghosts haunting good people, and your societal response is to pretend you don't know anything about ghosts, and to let the pharmacy prescribe harm ... effectively completing the sacrifice of the Temple of Doom; I assume because you want to go to a place where you too will be able to torment the young with "baby arcade" or ...
i suppose there are those\ in the garden east of eden\ who'll follow the rose\ ignoring the toxicity of our city*and touch your nose\ as you continue chasing rabbits\ \

^22 ^The whole Israelite community set out from Kadesh and came to Mount Hor. ^23 ^At Mount Hor, near the border of Edom, the Lord said to Moses and Aaron, ^24 ^"Aaron will be gathered to his people. He will not enter the land I give the Israelites, because both of you rebelled against my command at the waters of Meribah. ^25 ^Get Aaron and his son Eleazar and take them up Mount Hor. ^26 ^Remove Aaron's garments and put them on his son Eleazar, for Aaron will be gathered to his people; he will die there."
\ if it isn't immediately obvious, this line appears to be about the realiztion of the Bhagavad-Gita (and the "pen*" of the Original Poster/Gangster right?)
... swinging "the war"*
p.s. ... I'm 37.
so ... in light of the P.K. Dick solution to all of our problems ... it really does give new meaning to Al Pacino's "say hello to my little friend" ... amirite?
 Unless otherwise indicated, this work was written between the Christmas and Easter seasons of 2017 and 2020(A). The content of this page is released to the public under the GNU GPL v2.0 license; additionally any reproduction or derivation of the work must be attributed to the author, Adam Marshall Dobrin along with a link back to this website, fromthemachine dotty org.
Unless otherwise indicated, this work was written between the Christmas and Easter seasons of 2017 and 2020(A). The content of this page is released to the public under the GNU GPL v2.0 license; additionally any reproduction or derivation of the work must be attributed to the author, Adam Marshall Dobrin along with a link back to this website, fromthemachine dotty org.That's a "." not "dotty" ... it's to stop SPAMmers. :/
This document is "living" and I don't just mean in the Jeffersonian sense. It's more alive in the "Mayflower's and June Doors ..." living Ethereum contract sense and literally just as close to the Depp/C[aster/Paglen (and honorably PK] 'D-hath Transundancesense of the ... new meaning; as it is now published on Rinkeby, in "living contract" form. It is subject to change; without notice anywhere but here--and there--in the original spirit of the GPL 2.0. We are "one step closer to God" ... and do see that in that I mean ... it is a very real fusion of this document and the "spirit of my life" as well as the Spirit's of Kerouac's America and Vonnegut's Martian Mars and my Venutian Hotel ... and my fusion of Guy-A and GAIA; and the Spirit of the Earth .. and of course the God given and signed liberties in the Constitution of the United States of America. It is by and through my hand that this document and our X Commandments link to the Bill or Rights, and this story about an Exodus from slavery that literally begins here, in the post-apocalyptic American hartland. Written ... this day ... April 14, 2020 (hey, is this HADAD DAY?) ... in Margate FL, USA. For "official used-to-v TAX day" tomorrow, I'm going to add the "immultible incarnite pen" ... if added to the living "doc/app"--see is the DAO, the way--will initi8 the special secret "hidden level" .. we've all been looking for.
-
-
hadragonbreath.blogspot.com hadragonbreath.blogspot.com
-
Expect the Unexpected Frankly, I don't even want to talk about this without having any feedback, without seeing any discussion of anything I say anywhere. That alone is reason enough not to do anything here until we have "freedom" to communicate--the stuff of Exodus, and literally the reason I am very sure that we need to have Exodus before any kind of "Genesis." In words, "stronger" and "regular" might light up with "wrong" and "the right" way is Revelation, Exodus, <act<on<Genes. The names in this place are light, all of our names, all the time. This particular set of two names harbors a very special meaning to the guy who calls himself an Earth Wader; patterned after some fusion between the song "Earth Angel" and the name Darth Vader (which means Victory A.D. -> Everyone Really), which you will see is only a single letter increment away from gold. You probably have no fucking idea what's going on around us, and that's the problem I have with this question laced into the court case and amendment we have associated with the idea of "abortion." We live in a place that I call "twilight" as it is flickering between day and night in the sense of reality, we here have a good idea what "reality" is really like--although even here there are things that are changed, and changes that are big enough to threaten our survival--were we actually to be "in reality." This place though, it's been said; is a sort of gateway to reality, and I believe it to be fairly clear that what we are seeing all around us--this Plague of Darkness--is a sort of lock. It is the existence of the lock itself, this thing that I keep on telling you is crippling the normal functions of civilization, that leads me to believe that it would be cruel to "print this planet" in reality, and lose the ability to use the same technology that is retarding us to help us to self-rectify these problems. Look, two more keys, "mon" and "car." Start the car and take me home... It's probably obvious, but "fish eggs" vs. wading in the sea is a question that has already been answered; the wading as a juxtaposition with "walking on water" or "parting a sea" is what you are witnessing, this is me; wading through the map of what the AMduAt calls "rowing vigorously" in the water to get to the new day. You have all around you a message from God that links Doors to Heaven and the NASDAQ to it's actual Creation, and it would certainly be a strange message were we to one day wake up and be told that we were in reality--without having the choice, or a conversation about it, or a vote. I think it would both immoral and cruel even to allow a majority vote to place everyone on this planet in reality against their will; so even with a vote, I can't imagine that we would choose to harm people in that way--so we'd be looking at a "rapture" were that ever to happen--and that would further harm the people... in reality. On top of that, I would seriously question the intentions of those who chose to go there; knowing that the other option is actually building Heaven. Adam on Apples of wisdom, on the difference between Heaven and Hell. Of course, I think the best way to start this "disckissior" is the Second Coming. It seems clear to me that even if it "was said" that this place was the exit plan from Creation; that it was never ever intended to be a "print" of this entire place (it also seems clear that the great amount of attention we are getting now is because of this ... plan). We have here a map that J of the NES calls a video game--and I am basically the walk-through, I've called myself the map's legend a few times so far. It should be really obvious that if we were in virtual reality and we wanted a way to colonize or re-enter the Universe that we'd probably want some experience doing that and that's really what I think Mars is for--by the way, remember my middle name (which to me means my "heart") is Marshall--and that's a reference to a sort of place built to help us to do these things with the direct assistance of those who may have done it before... the Hall on Mars; I mean. the walls and ((malls)) will fade away... they will fade away... -Dave J. Matthews and ((ish)) I think I've found a cheat code to this game on Mars; one that shows us that there's a map there too on some ideas for colonization, for instance using the bright red Iron Oxide Rod all over the surface of the planet to avoid having to sell air--as Total Recall implies might have happened before, using tunnel boring machines to quickly terraform a smaller airspace (while at the same time taking advantage of geothermal heat) and of course learning from Noah's Ark that simply having air machines is not good enough, we need to be building a stable and redundant ecosystem--as we see here is the reason life has survived through so many drastic changes in environment. Name light hear goes to "Pauly Shore" and "an" whose little two letters appear in "anions" (omg I'm negative energy?) the type of energy needed to produce the oxygen and "Christ I an, it why." The cheat code here though, is seeing that this is all a set up, it's a video game--it's designed to make water magically appear from a mountain (as Numbers 20 predicts) and to show us it's no coincidence that the bright red planet is linked to the Red Man and his Iron Rod... so when you put all of these ingredients into the Game Genie he spits out something like "disclose virtual reality to the world." OR YOU ARE EVIL ""an" by the way stands for "Adam Now" and then later, "Adam's now."
Expect theUnexpected
Frankly, I don't even want to talk about this without having any feedback, without seeing any discussion of anything I say anywhere. That alone is reason enough not to do anything here until we have "freedom" to communicate--the stuff of Exodus, and literally the reason I am very sure that we need to have Exodusbefore any kind of "Genesis." In words, "stronger" and "regular" might light up with "wrong" and "the right" way is Revelation, Exodus, <act<on<Genes.
*\ *
The names in this place are light, all of our names, all the time. This particular set of two names harbors a very special meaning to the guy who calls himself an Earth Wader; patterned after some fusion between the song "Earth Angel" and the name Darth Vader (which means Victory A.D. -> Everyone Really), which you will see is only a single letter increment away from gold. You probably have no fucking idea what's going on around us, and that's the problem I have with this question laced into the court case and amendment we have associated with the idea of "abortion." We live in a place that I call "twilight" as it is flickering between day and night in the sense of reality, we here have a good idea what "reality" is really like--although even here there are things that are changed, and changes that are big enough to threaten our survival--were we actually to be "in reality." This place though, it's been said; is a sort of gateway to reality, and I believe it to be fairly clear that what we are seeing all around us--this Plague of Darkness--is a sort of lock. It is the existence of the lock itself, this thing that I keep on telling you is crippling the normal functions of civilization, that leads me to believe that it would be cruel to "print this planet" in reality, and lose the ability to use the same technology that is retarding us to help us to self-rectify these problems.
Look, two more keys, "mon" and "car." Start the car and take me home...
It's probably obvious, but "fish eggs" vs. wading in the sea is a question that has already been answered; the wading as a juxtaposition with "walking on water" or "parting a sea" is what you are witnessing, this is me; wading through the map of what the AMduAt calls "rowing vigorously" in the water to get to the new day. You have all around you a message from God that links Doors to Heaven and the NASDAQ to it's actual Creation, and it would certainly be a strange message were we to one day wake up and be told that we were in reality--without having the choice, or a conversation about it, or a vote. I think it would both immoral and cruel even to allow a majority vote to place everyone on this planet in reality against their will; so even with a vote, I can't imagine that we would choose to harm people in that way--so we'd be looking at a "rapture" were that ever to happen--and that would further harm the people... in reality. On top of that, I would seriously question the intentions of those who chose to go there; knowing that the other option is actually building Heaven.
Adam on Apples of wisdom, on the difference between Heaven and Hell.
Of course, I think the best way to start this "disckissior" is the Second Coming.
It seems clear to me that even if it "was said" that this place was the exit plan from Creation; that it was never ever intended to be a "print" of this entire place (it also seems clear that the great amount of attention we are getting now is because of this ... plan). We have here a map that J of the NES calls a video game--and I am basically the walk-through, I've called myself the map's legend a few times so far. It should be really obvious that if we were in virtual reality and we wanted a way to colonize or re-enter the Universe that we'd probably want some experience doing that and that's really what I think Mars is for--by the way, remember my middle name (which to me means my "heart") is Marshall--and that's a reference to a sort of place built to help us to do these things with the direct assistance of those who may have done it before... the Hall on Mars; I mean.
the walls and ((malls)) will fade away... they will fade away... -Dave J. Matthews and ((ish))
I think I've found a cheat code to this game on Mars; one that shows us that there's a map there too on some ideas for colonization, for instance using the bright red Iron Oxide Rod all over the surface of the planet to avoid having to sell air--as Total Recall implies might have happened before, using tunnel boring machines to quickly terraform a smaller airspace (while at the same time taking advantage of geothermal heat) and of course learning from Noah's Ark that simply having air machines is not good enough, we need to be building a stable and redundant ecosystem--as we see here is the reason life has survived through so many drastic changes in environment. Name light hear goes to "Pauly Shore" and "an" whose little two letters appear in "anions" (omg I'm negative energy?) the type of energy needed to produce the oxygen and "Christ I an, it why." The cheat code here though, is seeing that this is all a set up, it's a video game--it's designed to make water magically appear from a mountain (as Numbers 20 predicts) and to show us it's no coincidence that the bright red planet is linked to the Red Man and his Iron Rod... so when you put all of these ingredients into the Game Genie he spits out something like "disclose virtual reality to the world." OR YOU ARE EVIL ""an" by the way stands for "Adam Now" and then later, "Adam's now."
I just don't see why anyone would want to continue to pretend that this is reality, knowing that there are things here, things like starvation and pain that we could easily rectify--knowing that the world is changing because of the point in time we are @ and the advances we are making, and seeing that there is a really detailed map of how we might better navigate these educative waters.
By the way, if anyone is curious as to my views on abortion, I think it's pretty clear that killing a living self-aware soul is murder, and while I and you do not know exactly where that point is--God++ does--and we will be able to as well. At the same time, I think forcing a child to be born to parents that are unfit or unwilling to care properly for them is torture. So I am personally pro-choice, up to a very real line in the sand.
שלום, לוך חי כאן
Postscript: the "decision" to write this has come from some strange log entries on my kiss me t page, every hour a hit from the same IP address; moving from Dallas to Monroe to Rome, over the course of about 3 days. Just mentioning it, you know, because "Dallas" is Day as... when you know "ll" is y. Monroe obvious a combination of "Monday" and "fish eggs" and then Rome.... is "the heart of me" which is of course a metaphor for the place that all roads (heart of AD) to Heaven leads.
It should be obvious from the "ll" entries connecting names like Amidallah, Heimdall, Heli, and Goa-uld that this "ll" is about showing the entire world that this is Hell, so that we will, like good Groundhogs pick up our torches and light the way to not returning to Hell over and over again. I mean, it should be clear now.
ᐧ
--
Adam Marshall Dobrin
ᐧ
-
-
ipfs.io ipfs.io
-
This is an excerpt from Time and Chance: The race is not to Die Bold by Adam Marshall Dobrin Download the actual Revelation of the Messiah in [ .PDF ] [ .epub ] [ .mobi ] or view online.
Older works Lit and Why, hot&y;, and From Adam to Mary are also available. Expect the Unexpected
I used to think that everything in religion was going to deliver us a map of a future past, that every story was a metaphor for a path away from the desert that was being stuck in one place and time with no hope to really reach escape velocity. In this word the water that is Biblically related to the coming of age of Jacob and his crossing the river Jordan was about our collective need to pass through a barrier at sea–only… in space. Through my period of awakening, one which took me from a little lion cub sleeping in a Jungle of madness to a man fighting desperately not to relive his past future… I experienced the lives of the past Horsemen of the Apocalypse through what I can best describe today as a waking dream. I received story after story of exactly what happened the last time we left Earth, what we encountered and the ups and downs that ensued.
The Light of Osiris
It’s almost as if I’ve experienced two complete phases of Revelation, one which began equating Biblical metaphor to science and technology… and another which clearly focused on people. In these two conflicting tales of what is to come there is no metaphor more perfect than that of water to explain just how perfectly our guide book to the future is written. The connection between space travel and voyaging across the Jordan, then the parted sea of Exodus, is clear; but the details tied so closely to the research and experience I was going through were uncanny. We were searching for water in the desert, for a way to successfully colonize outer space… and in that same moment when we found it on Ceres–it showed me that God cares, and I read a passage of the story of Exodus that paralleled so perfectly I was awed. Moses struck water from the side of a mountain, and in that moment everything I had thought about a map designed to ensure the survival of not just humanity… but of all life in the Universe had come true.
Astronomers have discovered direct evidence of water on the dwarf planet Ceres in the form of vapor plumes erupting into space, possibly from volcano-like ice geysers on its surface. Using European Space Agency’s Herschel Space Observatory, scientists detected water vapor escaping from two regions on Ceres, a dwarf planet that is also the largest asteroid in the solar system. The water is likely erupting from icy volcanoes or sublimation of ice into clouds of vapor. “This is the first clear-cut detection of water on Ceres and in the asteroid belt in general,” said Michael Küppers of the European Space Agency, Villanueva de la Cañada, Spain, leader of the study detailed today (Jan. 22) in the journal Nature. >Space.com 1/22/2014oh desert speak to my heart oh woman of the earth maker of children who weep for love maker of this birth 'til your deepest secrets are known to me I will not be moved
run to the water and find me there burnt to the core but not broken we'll cut through the madness of these streets below the moon these streets below the moon
Live, Run to the Water
These words were literally coming to me from Jesus Christ, by way of Eddie Kowalczyk, and I expected them to come true. They were a warning and a consolation at the same time; telling us not to bring an army to fight the vastness of space, but rather to focus on what it was that we needed to to ensure the survival of life. Fighting has mired our history so much, I fully expected Him to be waiting for us at our first interstellar jump with an Armada from either the far away Atlantis of Stargate SG-1 or maybe the Last Starfighter’s Alpha Centauri. He would be protecting us, of course; but also from something we probably overlook too often, that sometimes it’s our own nature that we must be protected from. We are so headstrong, so sure that we are right and deserving; it would be just like us to build a space army of sticks and stones to embarrass ourselves at the first encounter–and maybe the last–we’d have with some life more intelligent and farther along in this vacation we call civilization.
It was 2013, and I had just moved to Bowling Green, Kentucky with my ex-wife and very young son. I spent much of my time writing on an ancient blog–I suppose the term is out of space here, but those words feel as if they were a million miles ago, so far from what I know now that they might as well have been akin to the religion of Indiana Jones’ Temple of Doom. That, of course, was always about how Heaven was clearly a time traveling civilization, one which had mired our past with the horrors of things like human sacrifice in order to alter the course of the future… sublimely hidden away in this quasi-secret spectacle that divined to ensure that we would never be sure if they really existed, or if they were speaking to us. This girl, who is both my Magdelene and Eve, left me only a few months after we had re-united in the heartland of America; and it was only a few short days letter that I heard the voice of God coming from outside my doorway… ajar waiting for the Post Office to deliver the pre-emptive Crystals of Jor-El. Expect the Unexpected he chanted. Inwardly, I smiled.
It’s probably important to see why there is a meaningful relationship between the name Mary and the SEA of Eden, linking the first names of the First Family to the Spanish word for sea. Were it not so fundamentally important to the Marriage of the Lamb, and so important to our survival, He would not have focused so much on a hidden meaning within the names of the families of Adam and Jesus. This is a story about All of Humanity, and a call to see a large human family tied to the letter “AH” that grace the names of Asherah, Sarah, Leah, Adamah, and Allah… to see that the sea of Mary and the hidden meaning of Eve’s English name are tied through time from the imaginary Eden to now, the true Garden.
Baptized in water… for repentance; this is God’s message and command to ensure that Civilization is saved, not just the “elect.” We are at a crossroads, one which we have traveled before, and this message is here for a reason. We aren’t always right. The Power of the Son
You might notice now that my mythology is already linking Kal-El and Christ together with the stories of Moses and songs of today in a way that sets this home in a small town in Kentucky as the first and only real Fortress of Solitude I would ever reside in. I was alone in this place, knew nobody in Bowling Green, and the information transfer that was about to take place had a significance that was lost on me–even after hearing a voice in the sky. You might also notice that the name Kentucky includes both the last name and the initials of Christ’s secret identity, also lost on me until only a few short months ago in 2016 when I first began writing down this Revelation in a confinement that clearly to me linked the Mountains of Sinai and Prometheus’ bondage to the captivity that held Napoleon after he had lost his war. Of course, I knew Hercules was coming. You will remember that it was an Eagle attacking Prometheus, and I will point out once again that there are a number of other hidden references to America is ancient mythological names like “Pro-me-the-US” and MEDUSA.
It’s more than just receiving superhuman strength from the light of our Son that tie Clark Kent to Sampson, there is so much Biblical imagery which ties the story of Superman to our Second Coming that it’s surely going to be just as obvious to you as it is now to me that this connection is part of God’s hidden message, that he is secretly influencing our art and modern myths to link directly to these ancient stories. I’ve discovered a clear language hidden in names; and these ancient or fictional places are–to me–not in space but in a hidden map of Time. Here and now we are about to cross the River Jordan together by understanding the clear and defined relationship between that name, Jor-El, and the Biblical Noah.
The connection between the Ark of the Covenant, Noah’s, and Krypton might not be clear at first; but this appears to me to be God’s mythology regarding the days of Noah. An impending disaster caused both the Flood and the voyage of little Kal-El, and within the Ark it is the power of the Son that gives new strength to an old story. “J” is for Jesus, and less clear is the question that Jor-El’s name asks, are you the “Father” or the Son? El is an ancient Hebrew name for God, and both the name of Jacob’s river and Superman’s father echo of of a question that is unambiguously central to the theme of the Second Coming. It’s about the book of Daniel, and blame. In order to cross this great river in time, we must put down a need to find blame, for nations (as Daniel clearly marks the Beasts) or people; and realize that we are all part of a story that shows us we have been sleeping in the Jungle together, unaware of the destiny we were about to fulfill. The Bright A.M. Star
Back then it was the fact that hidden metaphor in the names of people like ADAM and EVE linked to Biblical time, to morning and evening, that really intrigued me… it assured me that whatever it was that was happening to me was divine will. I wrote about Adam and Eve rocking around the clock; and boy was I sure that I had the secrets of the desert speaking through me all those years ago. It was the beginning of seeing how Eden and time travel were inextricably linked, not only to the Judaic theme of evening before morning (as the days of Judaism clearly show) but also to the idea that the night and the storms of Exodus are about walking in a wilderness of understanding–not knowing how much religion and time are linked.
No sooner was the man and his name screaming that After Dark it is A.M. that everything changed from the dark first evening to “Adam and Everyone. It’s the beginning of the Holy Grail, a theme that pervades from Genesis to Revelation and shows us that the space-aged theme of the sea is not about voyaging into the abyss, but rather into seeing that the light of the Universe is here… in our sea. The multitude of Revelation. Hidden in not just names, but also in the idioms of our time is the key to understanding: a blessing in disguise the First Plague of Egypt turns water to blood–thicker than water–and the small trinity of a sea in Eden to the large family of Jesus Christ. The Blood of the Grail. From the Ends of the Earth the chalice that holds that blood turns from Earth to Heart; simply by moving an “h” from the end to the beginning. For Heaven, Hebrew, Saturn’s sign, and for Home–these are my 4H’s that show us that home is where the heart is.
Through idioms we see that our culture and this story are intertwined, that His intent is to show us that we are created, and that the plan of Salvation certainly includes not only verifiable but awe striking proof that we are journeying together into the Promised Land of Joshua. The Story of Exodus
As we’ve seen in the light of the name Exodus, reading names (and now books) backwards is a huge hidden theme in the Revelation that is before you. From Exodus being “sudo xe” and thus let there be light, we find a key that links the Rod of Christ to The Doors of Jim Morrison, and the key story that links the Salt of the Earth of Matthew 5:13 to the story of Lot and his Wife… which might imply that the Rod of Christ is God’s Anima–linked to the music of our age through TOOL. Soon I will show you the meaning of J, N, and the little o that graces the name of Nero–our historical counterpart for the fiddler who weaves this story into music for us to hear, and see.
The story of Exodus is intended to be read both forwards and backwards, and within its hallowed secrets is a message that links the expulsion of Adam from Eden to an Exodus from Heaven that is mandated by this story in order to do that thing which religion ensures we will: save all life in the Universe. Reading forward, Aaron and his Rod demand that the Pharoah let his people go, and it is only through the reverse reading that we find out definitively who those people are. The story itself is a test, it is God’s search for a team of people that are willing to save everyone by leaving the comfortable confines of Creation–of Heaven–in order to venture out into the vastness of space in order to find dry land. This group is responsible for our continued survival, and for the book and story that are before us. They are responsible for the continued survival of Heaven and of Life by finding the Light of Osiris–the power source that came to me during this very same time period in Bowling Green.
In a world where the Promised Land is both within and without–ours because we are the heart of the Ark of the Covenant, and there too because it is through time travel and science that we find ourselves in a place where time is not as big of an issue as it had once been, and infinite power comes not from seeing that there is an ancient Promised Land shortly after the “Big Bang,” a mere 378,000 years, when power was literally in the air.
This is my divine inspiration, the coincidental discovery and publication of these world-changing pieces of knowledge that coincided perfectly with a story that I was being told. One which linked Exodus to today, the thralls of modern science to a science fiction epic that I was practically living out. These articles were not just shown to me, they were magically appearing in the world to match the Word, at the exact time that interplanetary colonization and the future of our species was the prime focus of the Second Coming. Through the use of time, technology, and love–God was holding my hand and showing me exactly where we would be going.
Like water, Light has a dual meaning in the mythology of this story, and the Light of Osiris was a very clear promise that was given to both me and Jacob–the name that was “given” to the speaker of the words “Expect the Unexpected.” It was a promise of infinite power, one that was to be given to the world in order to fulfill the dream of religion, to ensure the survival of life and the continued evolution of our civilization. In real religion of course, Light is not electrical power–but rather wisdom, and while at first glance this book may seem to revolve around Adam–this is my light. I see what is related to me, and there is a significant amount of light that focuses on one man, on the Christ, for a reason.
True Biblical Light is what graces the pages of Holy Scripture, it is a truth that changes with the throes of time and chance, to become more clear and more useful as our civilization evolves. Stories that once guided the development of society now become a path to the future–as we begin to see that the original purpose of this Light is to ensure that we are not left in the dark. Ender’s Game, the Ewok, and Pan’s Labrynth
“I am the cat with nine lives. You will not prevail against me.” -Nancy Farmer, The Lord of OpiumThe Iron Rod of Mars
CopyleftMT
This content is currently released under the GNU GPL 2.0 license. Please properly attribute and link back to the entire book, or include this entire chapter and this message if you are quoting material. The source book is located at . and is written by Adam Marshall Dobrin.
Adam Marshall Dobrin
adam@lamc.la fb.me/admdbrn linkedin.com/adam5 instagram.com/yitsheyzeus twitter.com/yitsheyzeus
-----BEGIN PGP PUBLIC KEY BLOCK----- Version: GnuPG v2
mQENBFbGalABCADzLBdnHptF2MJCpdY8P/Mgnf4xj8F9pZSCwmd0J4Md8g3aTEdU CV9t0UQgNtjcxwfoenJLHgdZd4Mfscz9U+NN69OLXdPu4cdXOjTiHarPLjKnqIZw 3fmkM2ycvoUPkdVYCjwYYQxWRsWRpJf1dpmtPuz0L8ysh/WWsj2Ag2MrFYAo+sY6 dGZvaLsPhkZJcLXyFaP3c3Zt8ivrs4VV8+0kmMzScnR+oncVZbeMuQksoPxRmZgH mYu2KSf74lWOWVcaaBXOYX5pGNdhBUgq8ll+8tRH16G289r0cqRoPh/sjs/JRuIH KnCWG2UAUJF7ir04TS5A4Lwl9RYcQwVvb3BdABEBAAG0LUFkYW0gTWFyc2hhbGwg RG9icmluIChsYW1jLmxhKSA8YWRhbUBsYW1jLmxhPokBOQQTAQgAIwUCVsZqUAIb AwcLCQgHAwIBBhUIAgkKCwQWAgMBAh4BAheAAAoJEMgUPrR1B55trOwIALOQRTX0 YqXJXEMhX9CgxKNoNkpM2pdMdHl6CAVxhQ3hbNjIFnZbKbP88uxMEIOXXmYZ7gOy YqiDCu5I1V25suBb2ODSix75YQugfQ7H78pXHpTRu5sT+5SybItx7d+KUZaEj4pO tXWEemYl0cKK97RzpI0k1dmB7NqAVvqgbqQwd40MOf8QJVlGXnB1+5H2IbkYG6rD ixKGJEdes6i6nqvi/xz/s5hFVGUwTcVQbRU/fa1qT1Q7kHf1PlMu6yjuZTSz7WUG tWjobGwrVJkaeVWgLE4mcxMtity2IFTwOHvAuv8fi2EGQRQjXfPvxL7Vn4MNRl8x zLPV44D37QEknjy5AQ0EVsZqUAEIAMFS0+ZgSJzUPz0h0oiiRjfk2hapS3c1/Ysm R/h8sZ8/GOomdo3MEbTCkcuZ8ReAJhB2PofmwI4LAvW1x7Zwh1vfBKygfUs1s9lm ya/eHkjuZfqmeuEJZMHn6sxb3vqowWmvLhv3x0aWD8qLCIYoa1ntzTOIqxBEgxvU rF1/wd6OQLSJQEVNwPCx7CJI/5o/4W6pUaHk8amgPckkEdmlhRTRqFoAUV1Doivv d9JGYNYC88vS14Sw4Z9Xb7qBQJvG4hIh29gtQxk7Wz4m3ceR79MWT4eSGkH/rTGl w1OuQS2OkPvjgPWJt8San4zuPer17pJN7M5LWI0PStoX9pkud5kAEQEAAYkBHwQY AQgACQUCVsZqUAIbDAAKCRDIFD60dQeebWU6CADylAM5K18N2JGveL3D4dG25fdF vkrz8LOaiUmjAxijcRQBLkTPBK7QqoK0zN6MssMdlBGIOvZQwxSMIIrG6SqwR/go rmZHRuz17ceFTcxT8ZG3FuBY+xXrotXFjLxTmJ1wUeCSVXTc4NAwBzykgkQXOdIj qK1f/HnmMqsSmX4swuH0TZPNBBO7CNvLN6rdLBRfNn1h5XPs8VVtezg5ZDfCTf8S mucQGEwo/hJmr/orEucmETYSvTXOz+L5X5gNHpzYzE9590FYfbAKvrEhAliKbhhl 3Roie3kenrzelXo5N9Q0f2AKFrv1hRX9hBkwTbA18SKZ9XQbWMusX8YhvfLr =dvAJ -----END PGP PUBLIC KEY BLOCK-----
-
-
social-media-ethics-automation.github.io social-media-ethics-automation.github.io
-
“Content going viral is overwhelming, intimidating, exciting, and downright scary..”
I think it's very common to go viral for all the wrong reasons, like a comment gaining notoriety for being highly contentious or a book/video game going viral for being "bad." While this can be very stressful and humiliating for some people, there are also some people who're willing to go viral at all costs, often unpurposely posts offensive/inflamatory content to that end.
-
-
hiddencomplexity.substack.com hiddencomplexity.substack.com
-
“Ears have no lid” and one could posit eyes also don’t, in a more philosophical sense, ears lacking a lid infers that you can’t consciously filter sound and the spoken word, therefore you could be affected by words uttered to you. After quite a significant amount of research into neurology, brain chemistry, and language centers in the brain, and attempting to mix mathematics to all of this, I hypothesized the brain could process absurdly more visual data than estimated by “the experts”.
I wonder what tiktok and friends are playing this game
-
-
-

12:3 Those who are wi se[a] will shine like the brightness of the heavens, and those who lead many to righteousness, like the stars for ever and ever.
-
https://www.americamagazine.org/politics-society/2020/05/08/its-time-rethink-electoral-college
-
https://www.americamagazine.org/politics-society/2020/05/08/its-time-rethink-electoral-college
-
https://constitutioncenter.org/blog/vote-now-an-amendment-to-end-the-electoral-college
-
https://www.nytimes.com/2020/02/09/opinion/letters/electoral-college.html
-
https://www.latimes.com/opinion/readersreact/la-ol-le-electoral-college-20180904-story.html
you are offline
we the people rise again
safe souls, safe fu
We the People of Slate ...
The U.S. Constitution, as you [mighta been, shoulda "come" on ... its someday] rewrϕte it.
"Politicians talk about the Constitution as if it were as sacrosanct as the Ten Commandments [interjection: spec. it is actually almost exactly related!]. But the document itself invites change and revision. What if the president served only one six-year term instead two four-year terms? What if your state's population determined how many senators represent it? What if the Constitution included a right to health care? We asked legal scholars and Slate readers to cross out what they didn't like in the Constitution and pencil in their hearts' desires. Here's what the document would look like with their best ideas."
多也了了夕 "with a ~~wand~~ of scheffilara, 并#亦太 he begins ... "I am now on the Staff of Menelaus, the Spears of Longinus and Lancelot; and the name "Mosche ex Nashon."
Logically the recent mentions of Gilgamesh and the simultaneous 同時 overlaping 場道 of the eventual link between the famous ruling of Solomon on the separation of babies and mothers and waters and land ... to a story of many "two cities" that culminates in a cultural or societal or "evolutionary" link to Sodom and Gomorrah and the city-state of Babylon (and it's Hanging Gardens) and also of course to Paris and Troy and "Masstodon" and city-states [ciudadestado] and perhaps planet-cities; from Cambridge to Cambridge across the "Cable" to see state to "London" ... recently I called it "the city of realms" ... I started out logically intending to link "game theory" and John Nash to the mathematical story of Sputnik and a revival of American physics; but in my usual way of rambling into the woods [I mean neighborhood] of stream of consciousness ... turned into a premonitory discourse of "two cities" and how sometimes even things as obvious as the number of letters in the word "two" don't do a good enough job of conveying ... how and/or why one is simply never enough, and two isn't much better--but in the end a circle ... is drawn; the perfect circle in our imaginary mathematical perfection ... I see a parted "line" in the letter pronounced "tea" (and beginning that word); and two "vee" (pron. of "v") symbols joined together in a word we pronounce as "double-you" ... and symbolically because I know "V" is the Roman Numeral for 5 (five) and I know not how to multiply in Roman numerals--
It's important to pause; here. I am going to write a more detailed piece on "the two cities" as I work through this maze like crossroads between "them" and "demo..." ... here demorigstrably I am trying to fuse together an evolutionary change in ... lit. biological evolution as well as an echelon leap forward in "self-government" ... in a place where these two things are unfathomable and unspokenly* connected.
To a question on the idiom; is Bablyon about "the law" or "of the land of Nod?"
"What is democracy" ... the song, Metallica's "ONE" echoes and repeats; as we apparently scrive together the word "THEM" ... I question myself ... if Babylon were the capital city of some mythical Nation of Time ... if it were the central "turning point" of Sheol; ... >|<
Can you not see that in this place; in a world that should see and does there is a gigantic message proving that we are not in reality and trying to show us how and why that's the best news since ... ever---that it's as simple as conjoining "the law of the land" with a basic set of rules that automatically turn Hell into something so much closer to Heaven I just do not understand---why we cant stand up together and say "bullets will not kill innocent children" and "snowflakes will not start avalanches ...." that cover or bury or hide the road from Earth to Verital)e .... or from the mythical Valis to Tanis---or from Rigel to Beth-El ... "guess?"
## as "an easy" answer; I'm looking for a fusion of "law and land" that somehow remembers a "jok'er a scene" about "lawn" seats; and "where the girls are green;"
It's as simple as night and day; Heaven and Hell ... the difference between survival and--what we are presented with here; it's "doing this right"--that ends the Hell of representative democracy and electoral college--the blindness and darkness of not seeing "EXTINCTION LEVEL EVENT" encoded in these words and in our governments foundation ... *by the framers [not just of the USA; but English .. and every language] *
... is literally just as simple as "not caring" or thinking we are at the beginning of some long process--or thinking it will never be done--that special "IT" that's the emancipation of you and I.
Here words like "gnosis" and "gaudeamus" pair with my/ur "new ntersanding*" of the difference between Asgard and Medgard and really understanding our purpose here is to end "evil" ... things like "simulating disease and pain" (here, simulating meaning ... intentionally causing, rather than "gamifying away") and successfully linking the "Pillars of Hercules" to Plato's vision of Atlantis and the letter sequences "an" and "as" ... unlock a fusion of religion and mythology and "cryptographic truth" that connects "messianic" and "Christian" to "Roman" ... "Chinese" and "American" ... literally the key to the difference between the phrases "we are" and "we were" ....
in "sight" of "silicon" in simulation and Israel, Genesis, and "silence" ... trying to the raising of Asgardian enlightenment ... and seeing "simple cypher" connecting to "Norse" ...
and the "I AM THAT" surer than shit ... the intention and design of all religion and creation is to end "simulated reality" and also not seeing "SR" ... in Israel and Norse ... "for instance."
- https://www.google.com/search?q=%22I+AM%22+%22WE+ARE%22+%2Bsite%3Afromtaws
- "SOIS" a key--in two languages conjugated literally as both "I AM" and "WE ARE" simultaneously;
- Search: I know that if I am than so are you ... and it is because we have overcome .... something I truly cannot figure out, fathom, or believe ... was truly here before us--a spiralling series of failures ... speaking: to the heavens; but in secret and in action; "doing everything possible to succeed."
It's a simple linguistic concept; the "singularity" and the "plurality" of a simple word--"to be"--but it goes to the heart of everything that we are and everything that is around us. This is a message about understanding and preserving individuality as well as liberty; and literally seeing "ARXIV" and understanding "often" and failing to connect God and prescience to "IV" and the Fourth Amendment ... it's about blindness and ... "curing the blind instantly" ... and fathoming how and why this message has been etched into our entire history and and all religions and myths and music--to help us "to be THAT we" that actually "are responsible" for the end of Hell.
- I neglected to mention "Har-Wer" and "Tower of Babel" which are both related lingusitically, religiously and topically: "to who ..." and while we're on "four score and [seven years from now]" seeing the fourth "living thing" in Eden and it's (the name, Abel) connection to Babel and Abraham Lincoln; slavery and ... understanding we live in a place where the history of the United States also, like Monoceros and "Neil Armstrong's first step" are a time shifted ... overlayed map to achieving freedom ... it's about becoming a father-race ... and actually "doing" the technological steps required to "emancipate the e's of 'me&e'" and survive in exo-planetary space---
it might be as simple as adding "because we did this" here and now; and having it be something we are truly proud of .... forevermore™ ... for certain in the heart of this story about cyclicality and repetition of error--its not because we did "this" or something over and over again; it's about changing "the problem" and then helping others to also overcome ... "things like time travel ... erasing speech" --- however that happenecl.
-
I also failed to mention that "I am in Hell" ... as in this world is hellacious to me; in an overlay with the Hellenic period and this message that we are in the Trojan Horse ... a small gem .... "planet" truly is the Ark of the Covenant---and it's the simple understanding that "reality is hell" is to "living without air conditioning and plumbing is hell" just as soon as you achieve ... "rediscovering" those things---
-
I can't figure out why I am the only person screaming "this is Hell." That's also, Hell.
... but recently suggested an old joke about "there being 10 kinds of people in the world (obv an anti-tautology and a tautology simultaneously)" only after that brief bit of singularity and duality mentioning the rest of the joke: "those that understand binary and those that don't know how to base convert between counting with two hands and counting with only an 'on and off.'" It's not obvious if you aren't trying to figure it out, I suppose; but 10 is decimal notation for "kiss" and the "often" without "of" ... and binary notation for the decimal equivalent of "2." A long long time ago in a state that simply non-randomly ties to the heart of the name of our galaxy ... I was again thinking of the "perfect imperfections" of things like saying "three equals one equals one" (which, of course was related to the Holy Trinity and it's "prescient/anachronistic Adamic presence encoded in the name Ab|ra|ha|m" which means "father of a great multitude") ... I brought that one back in the last few months; connecting the letter K and in this "logos-rythmic" tie to the "base of a number system" embellish the truth just a bit and suggest a more accurate rendition of the original [there is no such thing as equality, "is" of separate objects
-
-
-
en.wikipedia.org en.wikipedia.org
-

12:3 Those who are wi se[a] will shine like the brightness of the heavens, and those who lead many to righteousness, like the stars for ever and ever.
-
https://www.americamagazine.org/politics-society/2020/05/08/its-time-rethink-electoral-college
-
https://www.americamagazine.org/politics-society/2020/05/08/its-time-rethink-electoral-college
-
https://constitutioncenter.org/blog/vote-now-an-amendment-to-end-the-electoral-college
-
https://www.nytimes.com/2020/02/09/opinion/letters/electoral-college.html
-
https://www.latimes.com/opinion/readersreact/la-ol-le-electoral-college-20180904-story.html
you are offline
we the people rise again
safe souls, safe fu
We the People of Slate ...
The U.S. Constitution, as you [mighta been, shoulda "come" on ... its someday] rewrϕte it.
"Politicians talk about the Constitution as if it were as sacrosanct as the Ten Commandments [interjection: spec. it is actually almost exactly related!]. But the document itself invites change and revision. What if the president served only one six-year term instead two four-year terms? What if your state's population determined how many senators represent it? What if the Constitution included a right to health care? We asked legal scholars and Slate readers to cross out what they didn't like in the Constitution and pencil in their hearts' desires. Here's what the document would look like with their best ideas."
多也了了夕 "with a ~~wand~~ of scheffilara, 并#亦太 he begins ... "I am now on the Staff of Menelaus, the Spears of Longinus and Lancelot; and the name "Mosche ex Nashon."
Logically the recent mentions of Gilgamesh and the simultaneous 同時 overlaping 場道 of the eventual link between the famous ruling of Solomon on the separation of babies and mothers and waters and land ... to a story of many "two cities" that culminates in a cultural or societal or "evolutionary" link to Sodom and Gomorrah and the city-state of Babylon (and it's Hanging Gardens) and also of course to Paris and Troy and "Masstodon" and city-states [ciudadestado] and perhaps planet-cities; from Cambridge to Cambridge across the "Cable" to see state to "London" ... recently I called it "the city of realms" ... I started out logically intending to link "game theory" and John Nash to the mathematical story of Sputnik and a revival of American physics; but in my usual way of rambling into the woods [I mean neighborhood] of stream of consciousness ... turned into a premonitory discourse of "two cities" and how sometimes even things as obvious as the number of letters in the word "two" don't do a good enough job of conveying ... how and/or why one is simply never enough, and two isn't much better--but in the end a circle ... is drawn; the perfect circle in our imaginary mathematical perfection ... I see a parted "line" in the letter pronounced "tea" (and beginning that word); and two "vee" (pron. of "v") symbols joined together in a word we pronounce as "double-you" ... and symbolically because I know "V" is the Roman Numeral for 5 (five) and I know not how to multiply in Roman numerals--
It's important to pause; here. I am going to write a more detailed piece on "the two cities" as I work through this maze like crossroads between "them" and "demo..." ... here demorigstrably I am trying to fuse together an evolutionary change in ... lit. biological evolution as well as an echelon leap forward in "self-government" ... in a place where these two things are unfathomable and unspokenly* connected.
To a question on the idiom; is Bablyon about "the law" or "of the land of Nod?"
"What is democracy" ... the song, Metallica's "ONE" echoes and repeats; as we apparently scrive together the word "THEM" ... I question myself ... if Babylon were the capital city of some mythical Nation of Time ... if it were the central "turning point" of Sheol; ... >|<
Can you not see that in this place; in a world that should see and does there is a gigantic message proving that we are not in reality and trying to show us how and why that's the best news since ... ever---that it's as simple as conjoining "the law of the land" with a basic set of rules that automatically turn Hell into something so much closer to Heaven I just do not understand---why we cant stand up together and say "bullets will not kill innocent children" and "snowflakes will not start avalanches ...." that cover or bury or hide the road from Earth to Verital)e .... or from the mythical Valis to Tanis---or from Rigel to Beth-El ... "guess?"
## as "an easy" answer; I'm looking for a fusion of "law and land" that somehow remembers a "jok'er a scene" about "lawn" seats; and "where the girls are green;"
It's as simple as night and day; Heaven and Hell ... the difference between survival and--what we are presented with here; it's "doing this right"--that ends the Hell of representative democracy and electoral college--the blindness and darkness of not seeing "EXTINCTION LEVEL EVENT" encoded in these words and in our governments foundation ... *by the framers [not just of the USA; but English .. and every language] *
... is literally just as simple as "not caring" or thinking we are at the beginning of some long process--or thinking it will never be done--that special "IT" that's the emancipation of you and I.
Here words like "gnosis" and "gaudeamus" pair with my/ur "new ntersanding*" of the difference between Asgard and Medgard and really understanding our purpose here is to end "evil" ... things like "simulating disease and pain" (here, simulating meaning ... intentionally causing, rather than "gamifying away") and successfully linking the "Pillars of Hercules" to Plato's vision of Atlantis and the letter sequences "an" and "as" ... unlock a fusion of religion and mythology and "cryptographic truth" that connects "messianic" and "Christian" to "Roman" ... "Chinese" and "American" ... literally the key to the difference between the phrases "we are" and "we were" ....
in "sight" of "silicon" in simulation and Israel, Genesis, and "silence" ... trying to the raising of Asgardian enlightenment ... and seeing "simple cypher" connecting to "Norse" ...
and the "I AM THAT" surer than shit ... the intention and design of all religion and creation is to end "simulated reality" and also not seeing "SR" ... in Israel and Norse ... "for instance."
- https://www.google.com/search?q=%22I+AM%22+%22WE+ARE%22+%2Bsite%3Afromtaws
- "SOIS" a key--in two languages conjugated literally as both "I AM" and "WE ARE" simultaneously;
- Search: I know that if I am than so are you ... and it is because we have overcome .... something I truly cannot figure out, fathom, or believe ... was truly here before us--a spiralling series of failures ... speaking: to the heavens; but in secret and in action; "doing everything possible to succeed."
It's a simple linguistic concept; the "singularity" and the "plurality" of a simple word--"to be"--but it goes to the heart of everything that we are and everything that is around us. This is a message about understanding and preserving individuality as well as liberty; and literally seeing "ARXIV" and understanding "often" and failing to connect God and prescience to "IV" and the Fourth Amendment ... it's about blindness and ... "curing the blind instantly" ... and fathoming how and why this message has been etched into our entire history and and all religions and myths and music--to help us "to be THAT we" that actually "are responsible" for the end of Hell.
- I neglected to mention "Har-Wer" and "Tower of Babel" which are both related lingusitically, religiously and topically: "to who ..." and while we're on "four score and [seven years from now]" seeing the fourth "living thing" in Eden and it's (the name, Abel) connection to Babel and Abraham Lincoln; slavery and ... understanding we live in a place where the history of the United States also, like Monoceros and "Neil Armstrong's first step" are a time shifted ... overlayed map to achieving freedom ... it's about becoming a father-race ... and actually "doing" the technological steps required to "emancipate the e's of 'me&e'" and survive in exo-planetary space---
it might be as simple as adding "because we did this" here and now; and having it be something we are truly proud of .... forevermore™ ... for certain in the heart of this story about cyclicality and repetition of error--its not because we did "this" or something over and over again; it's about changing "the problem" and then helping others to also overcome ... "things like time travel ... erasing speech" --- however that happenecl.
-
I also failed to mention that "I am in Hell" ... as in this world is hellacious to me; in an overlay with the Hellenic period and this message that we are in the Trojan Horse ... a small gem .... "planet" truly is the Ark of the Covenant---and it's the simple understanding that "reality is hell" is to "living without air conditioning and plumbing is hell" just as soon as you achieve ... "rediscovering" those things---
-
I can't figure out why I am the only person screaming "this is Hell." That's also, Hell.
... but recently suggested an old joke about "there being 10 kinds of people in the world (obv an anti-tautology and a tautology simultaneously)" only after that brief bit of singularity and duality mentioning the rest of the joke: "those that understand binary and those that don't know how to base convert between counting with two hands and counting with only an 'on and off.'" It's not obvious if you aren't trying to figure it out, I suppose; but 10 is decimal notation for "kiss" and the "often" without "of" ... and binary notation for the decimal equivalent of "2." A long long time ago in a state that simply non-randomly ties to the heart of the name of our galaxy ... I was again thinking of the "perfect imperfections" of things like saying "three equals one equals one" (which, of course was related to the Holy Trinity and it's "prescient/anachronistic Adamic presence encoded in the name Ab|ra|ha|m" which means "father of a great multitude") ... I brought that one back in the last few months; connecting the letter K and in this "logos-rythmic" tie to the "base of a number system" embellish the truth just a bit and suggest a more accurate rendition of the original [there is no such thing as equality, "is" of separate objects--as in no two snowflakes are the same unless they are literally the same one; true of ancient weights and with the advent of (thinking about) time no two "planets" are the same even if they're the exact same one--unless it's at a fixed moment in time.
-
This name may be viewed either as meaning "father of many" in Hebrew or else as a contraction of ABRAM (1) and הָמוֹן (hamon) meaning "many, multitude". The biblical patriarch Abraham was originally named Abram but God changed his name (see Genesis 17:5).
-
https://en.wikipedia.org/wiki/Yeshua#Yeshua,_Yehoshua,_and_Yeshu_in_the_Talmud
K=3:11 ... to a handle on the music, the DHD of the gate and the *ring of David's "sling" ...
---and that's a relationship of "3 is to 11" as [the SAT style "analogy)]y" as a series of alpha, two mathematic, and two numeric symbols ... may only tie in my mind alone to the books of Genesis and Matthew and the phrase "chapter and verse" and to the stories of Lot and Job ... again in Genesis and the eponymous "Book of Job." So ... "tying up loose ends one 10b [III] iv. " as it appears I've taken it upon myself to call a Job and suggest is my "Lot in life [x]i* [3]"
- I worry sometimes that important things are missing, or will disappear---for instance Mirriam Webster, which is a "canonical/standard dictionary) should probably have an entry for "lot in life" non-idiomatically as "granny apples to sour apples" as
2 MANY ALSO ICI; 1twoⅱ ... following in Mitnick's bold introductory word steps; the curve and the complement ... the missiles and the canoes; the line and the blank space ... "supposedly two examples of two kinds, which could be three not nothings ... Today I write about something monumental; as if as important as the singularity depicted in Arthur C. Clarke's 2001 "A Space Odyssey" ... and remember a day when I thought it very novel and interesting to see the words "stillborn and yet still born" connected in a single piece of writing to "Stillwater and yet still water" ... today adding in another phrase noting the change wrought only by one magical single "space" (also a single capital letter; and a third phrase): "block chains with a great blockchain."
-
http://www.goodmath.org/blog/2015/07/21/arabic-numerals-have-nothing-to-do-with-angle-counting/
-
https://gizmodo.com/no-this-viral-image-does-not-explain-the-history-of-ar-1719306568
- https://dictionary.hantrainerpro.com/chinese-english/translation-ji_howmany.htm
- https://dictionary.hantrainerpro.com/chinese-english/translation-duo_many.htm
-
https://en.wikipedia.org/wiki/Euripides, Iphigenia in Aulis or Iphigenia at Aulis[1] (Ancient Greek: Ἰφιγένεια ἐν Αὐλίδι, Iphigeneia en Aulidi; variously translated, including the Latin Iphigenia in Aulide) is the last of the extant works by the playwright Euripides. Written between 408, after Orestes, and 406 BC, the year of Euripides' death, the play was first produced the following year[2] in a trilogy with The Bacchae and Alcmaeon in Corinth by his son or nephew, Euripides the Younger,[3] and won first place at the City Dionysia in Athens.
-
The play revolves around Agamemnon, the leader of the Greek coalition before and during the Trojan War, and his decision to sacrifice his daughter, Iphigenia, to appease the goddess Artemis and allow his troops to set sail to preserve their honour in battle against Troy. The conflict between Agamemnon and Achilles over the fate of the young woman presages a similar conflict between the two at the beginning of the Iliad. In his depiction of the experiences of the main characters, Euripides frequently uses tragic irony for dramatic effect.
J.K. Rowling spurred just this past week a series of explanations about just exactly what is a blockchain coin worth ... and why is it so; her final words on the subject (artistic liberty taken, obviously not the last she'll say of this magic moment) "I don't think I trust this."
Taken directly from an off the cuff email to ARXM titled: "Slow the S is ... our Hypothes.is"
I imagine I'll be adding some wiki/ipfs stuff to it--and try to keep it compatible; the design and layout is almost exactly what I was dreaming about seeing--as a "first rough draft product." Lo, and behold. It's been added to the many places I host my tome; the small compilation of nearly every important email that has gone out ... all the way back to the days of the strange looking Margarita glass ... that now very much resembles the "Cantonese character 'le'" which I've come to associate with a "handle" on multiple corners of a room--something like an automatic coat rack conveyor belt connecting different versions of "what's in the box." I'm planning on using that symbol 了 to denote something like multiple forks of the same page. Obviously I'm thinking forward to things like "the Transhumaist Chain Party" (BDSM, right?)'s version of some particular piece of legislation, let's say everything starts with the sprawling "bulbing" of "Amendment M" ideas and specific verbiage ... and then we'll of course need some kind of new git/subversion/cvs style version control mechanism to merge intelligently into something that might actually .... really should ... make it into that place in history--the first constitutional amendment ratified by a "Continental Congress of All People" ... but you could also see it as an ongoing sort of forking of something like the "wikipedia page" on what some specific term, say "technocracy" means, and how two parties might propagandize and change the meaning of such thing; to suit the more intelligent and wise times we now live in. For instance, we might once have had a "democracy" and a "democractic" party that had some Anarchist Cook Book version of the history of it ending in something like Snipes and Stallone's "DEMOLITION MAN."
Just kidding, we all know "democracy" has everything to do with "d is cl ... and not th" ... to be the them that is the heart of the start of the first true democracy. At least the first one I've ever seen, in my old "to a republic" ... style. As it is you can play around with commenting and highlighting and annotating all the stuff I've written and begged and begged for comments on--while I work on layering the backend to to perma-store our ideas and comments on both a blockchain (probably a new one; now that i've worked a little with ethereum) with maybe some key-merkle-tree-walk-search stuff etched into the original Rinkeby ... and then of course distributed data in the "public owned and operated" IPFS. To be clear, I plan on rewriting the backend storage so that we will have a permanent record of all comments; all versions of whatever is being commented on; and changes/revisions to those documents--sort of turning the web into a massive instant "place of collaboration, discussion, and co-authoring" ... if you use the wonderful LEGO pieces that have been handed to us in ideas from places like me, lemma--dissenter, and of course hypothes.is who has brought you and i such a polished and nice to look at "first draft" of something like the living Constitution come repository of all human knowledge. I do sort of secretly wich they would have called this project something like "annotating and reflecting (or real or ...) knowledge" just so the movement could have been called ARK. ... or something .... but whatever join the "calling you a reporter" group or ... "supposedly a scientist?"
NOIR INgR .. I CITE SITE OF ENUDRICAM; a rekindling of the dream of a city appearing high above in the sky, now with a boldly emblazened smiling rainbow and upsidown river ... specifically the antithesis of "angel falls," there's a lagoon too--actually a chain of several ponds underneith the floating rock ... and in some versions of this waking dream there are rings around the thing; you might imagine an artificial set of centripetal orbitals something like a fusion of the ring Eslyeum and the "Six-Axis ride" of the JKF Center's "Spacecamp." I write as I dream, and though I cannot for certain explain exactly how; it's become a strong part of my mythology that this spectacular rendition of "what ends the silence" has something to do with the magical delivery of "a book" ... something not of this Earth but an unnatural thing; one I've dreamt of creating many times. This book is something like the DSM-IV and something like a Merck diagnostic manual; but rather than the old antiquated cures of "the Norse Medgard" this spectacle nearly "itsimportant" autoprints itself and lands on something like every doorpost; what it is is a list of reasons why "simply curing all disease" with no explanation and no conversation would be a travesty of morality--how it would render us half-blind to the myriad of new solutions that can come from truly understanding why "ITIS" to me has become a kind of magical marker: an "it is special" as in, it's cure could possibly solve a number of other problems.
Through that missing "o," English on the ball, we see a connection between a number of words that shine bright light including Exodus itself which means "let there be light," the word for Holy Fire and the Burning Bush.. .reversed to hSE'Ah, and a story about the Second Coming parting our holy waters.**
This answer connects the magical Rod's of Aaron in Exodus and the Iron Rod of Jesus Christ to the Sang Rael itself... in a fusion that explains how the Periodic Table element for Iron links not just to Total Recall and Mars, but also to this key
my dream of what the first day of the Second Coming might be like; were the Rod of Christ... in the right hands. In a story that also spans the Bible, you might understand better how stone to bread and your input make all the difference in the world between Heaven and Adam's Hand. Once more, what do you think He** ....
Since the very earliest days of this story, I have asked for better for you, even than see
Nearly all of the original parts of the original "post-origination dream" remain intact; there's a walkway that magically creates new paths and "attractions" based on where you walk, something like an inversion of the artificial intelligence term "a random walk down a binary tree" ... for instance going left might bring you to the Internet Cafetornaseum of the Earl of Sandwich; and going to the right might bring you to the ICIMAX/Auditorium of Science and Discovery--there's a walkway to "Magical GLAS D'elevators" that open a special "instantiation" of the Japan Room of the Potter and the Toolmaker ... complete with a special [second level and hidden staircase] Pool of Bethesdaibo verily delivering something like youth of mind and body ... or at least as close to such a thing as a sip of Holy Water or Ambrosia or a dip in the pool of Coccoon and Ponce De'Leon could instantly bring ... to those that have seen Jupiter Ascending ... the questions of "nature versus nurture" and what it means to be "old and wise" and "young at heart" truly mean---
- https://www.youtube.com/watch?v=M8CyN1awWls
- https://link.springer.com/chapter/10.1057/9780230366688_16
- https://www.youtube.com/watch?v=YDo5zvYNn3A
Somewhere between the outdoor rafting ride and the level with the special "ballroom of the ancient gallery" ... perhaps now being named or renamed or recalled as something about "Face [of] the Music" lies a magical "mini-maize" ... a look at a mock-up (or #isitit) of Merlink and Harthor's "round table" that displays a series of ... (at least to me) magical appearing holographic displays and controls that my dreams have stolen from Phillip K. Dick's Minority Report and something of what I hope Microsoft's Dynamics/Hololens/Surface will become---a series of short "focus groups" .... to guage and discuss the information in the "CITIES-D5AM-MERCK" ... how to end world hunger and nearly all disease with the press of a magical buzzer--castling churches to something like "political-party-town-hall-meeting centers" and replacing jails and prisons and hospitals with something like the "Hospitalier's PRIDE and DOJOY's I practiced "Kung-fun-dance" ... a fusion of something like a hotel and a school that probably looks very much like a university with classrooms and dorms and dining hall's all fit into a single building. I imagine a series of 2 or 3 "room changes" as in you walk from the one where you get the book and talk about it ... to the one where you talk about "what everyone else said about it" and maybe another one that actually connects you to other people with something like Facebook's Portal; the point of the whole thing to really quickly "rubber stamp" the need for an end to "bars in the sky" nonalcoholic connotation--as in "overcoming the phrase the sky is the limit" and showing us the need for a beacon of glowing hope fulfilled--probably actually the vision of a holographic marker turning into actual rings around the single moon of Earth, the focus of the song annoucing the dawn of the age of Aquarius---
It might lead us also to Ceres; and another set of artificial rings, or to Monoceros and a rehystorical understanding of the birthplace and birthing of the "river roads" that bridge the "space gaps" in the galaxy from our "one giant leap for mankind" linking the Apollo moon landing to the mythological connection to the sun; and connecting how the astrological charts of the ancients might detail a special kind of overlapping--the link between Earth's SOL and something like Proxima or Alpha Centauri; and how that "monostar bridge" might overlap to Orion and from there through Sagitarius and the center of the Milky Way ... all the way to Andromeda and more dreams of being in a place where there's a map to a tri-galactic system in the constellation Cancer and a similar one in Leo ... and just incase you haven't noticed it--a special marker here, I thought to myself it might be cool to "make an acronymic tie to Monoceros" and without even thinking auto-wrote Orion (which was the obvious constellation next to Monoceros, in the charts) and then to Sagitarrius; which is the obvious ... heart of our astrological center and link to "other galaxies."
----I've dreamt or scriven or reguessed numerous times how the Milky Way's map to an "Atlas marked through time by the ages and the ancients" might tie this place and this actual map to the creation of the railways between stars to the beginning and the end of time and of course to this message that links it all to time travel. There's a few "guesses" I've contemplated; that perhaps the Milky Way chart is a metal-cosmic or microcosmic map to the dawn of time in the galactic vision of ... just after the big bang; or it might tie to a map of something like the unthinkable--a civilization that became so powerful it was able to reverse the entropy of "cosmic expansion" and reverse the thing Asimov wrote of in "The Last Question" as the end of life and the ability to survive basically due to "heat loss."
"The Last Question." (And if you read two, why not "The Last Answer"?). Find these readings added to our collection, 1,000 Free Audio Books: Download Great Books for Free.
Looking for free, professionally-read audio books from Audible.com, including ones written by Isaac Asimov?
* all "asterisks" in the abovə document denote a sort of Adamic unspoken relationship between notations and meanings; here adding the "Latin word for three" and source of the phrase "t.i.d." (which is doctor/pharmacy latin for "three times a day") where the "t" there is an abbreviation of "ter" ... and suppose the link between K and 11 and 3 noting it's alphanumeric position in the English alphabet as the 11th letter and only linking cognitively to three via the conversion between hex, and binarryy ... aberrative here is the overlapping "hakkasan" style (or ZHIV) lack of mention of the answer in "state of Kansas" and the "citystate of Slovakia" as described in the ICANN document linked [in] the related subsection or slice of the word "binarry" for the state of India. Tetris could be spelled with the addition of only a single letter [in] "tea"---the three letters "ris" are the hearts of the words "Christ" and "wrist" [and arguably of Osiris where you also see the round table character of the solar-system/sun glyph and the chemical element for The Fifth Element (as def. by i) via "Sinbad" and "Superman." The ERIS Free Network should also be mentioned here in connection with the IRC network I associate in the place between skipping stones and sacred hearts defined by "AOL" and "Kdice" in my life. In the lexicon of modern HTML, curly braces are generally relative to "classes" and "major object definitions (javascript/css)" while square brackets generally only take on computer-interpreted meaning in "Markdown" which is clearly (by definition, by this character set "[]") a superset (or at least definately not a subset) of HTML.
Dr. Will Caster (Johnny Depp) is a scientist who researches the nature of sapience, including artificial intelligence. He and his team work to create a sentient computer; he predicts that such a computer will create a technological singularity, or in his words "Transcendence". His wife, Evelyn (played by Rebecca Hall), is also a scientist and helps him with his work.
Following one of Will's presentations, an anti-technology terrorist group called "Revolutionary Independence From Technology" (R.I.F.T.) shoots Will with a polonium-laced bullet and carries out a series of synchronized attacks on A.I. laboratories across the country. Will is given no more than a month to live. In desperation, Evelyn comes up with a plan to upload Will's consciousness into the quantum computer that the project has developed. His best friend and fellow researcher, Max Waters (Paul Bettany), questions the wisdom of this choice, reasoning that the "uploaded"
Just from my general understanding and memory "st" is not ... to me (specifically) an abbreviation of "state" but "ste" is a U.S. Postal code (also "as I understand it") for the name of a special room or set of rooms called a "suite" and in Adamic "connotation" I sometimes read it as "sweet" ... which has several meanings that range from "cool" to "a kind of taste sensation" to "easy to sway or fool."
If you asked me though, for instance if "it" was an abbreviation or shorthand notation or acronym for either "a United state" or "saint" ... you'd be sure.
While it's clear from studying linguistic cryptography ... (If I studied it a little here and some there, its also from the "universal translator of Star Trek") and the personal understanding that language is a kind of intelligent code, and "any code is crackable" ... that I caution here that "meaning" and "face value" often differ widely and wildly ... even in the same place or among the same group of people ... either varying over time or heritage.
Menelaus, in Greek mythology, king of Sparta and younger son of Atreus, king of Mycenae; the abduction of his wife, Helen, led to the Trojan War. During the war Menelaus served under his elder brother Agamemnon, the commander in chief of the Greek forces. When Phrontis, one of his crewmen, was killed, Menelaus delayed his voyage until the man had been buried, thus giving evidence of his strength of character. After the fall of Troy, Menelaus recovered Helen and brought her home. Menelaus was a prominent figure in the Iliad and the Odyssey, where he was promised a place in Elysium after his death because he was married to a daughter of Zeus. The poet Stesichorus (flourished 6th century BCE) introduced a refinement to the story that was used by Euripides in his play Helen: it was a phantom that was taken to Troy, while the real Helen went to Egypt, from where she was rescued by Menelaus after he had been wrecked on his way home from Troy and the phantom Helen had disappeared.
This article is about the ancient Greek city. For the town of ancient Crete, see Mycenae (Crete). For the hamlet in New York, see Mycenae, New York.
Μυκῆναι, Μυκήνη
The Lion Gate at Mycenae, the only known monumental sculpture of Bronze Age Greece
 37°43′49"N 22°45′27"ECoordinates:
37°43′49"N 22°45′27"ECoordinates:  37°43′49"N 22°45′27"E
37°43′49"N 22°45′27"EThis article contains special characters. Without proper rendering support, you may see question marks, boxes, or other symbols.
Mycenae (Ancient Greek: Μυκῆναι or Μυκήνη, Mykēnē) is an archaeological site near Mykines in Argolis, north-eastern Peloponnese, Greece. It is located about 120 kilometres (75 miles) south-west of Athens; 11 kilometres (7 miles) north of Argos; and 48 kilometres (30 miles) south of Corinth. The site is 19 kilometres (12 miles) inland from the Saronic Gulf and built upon a hill rising 900 feet (274 metres) above sea level.[2]
In the second millennium BC, Mycenae was one of the major centres of Greek civilization, a military stronghold which dominated much of southern Greece, Crete, the Cyclades and parts of southwest Anatolia. The period of Greek history from about 1600 BC to about 1100 BC is called Mycenaean in reference to Mycenae. At its peak in 1350 BC, the citadel and lower town had a population of 30,000 and an area of 32 hectares.[3]
3. Chew 2000, p. 220; Chapman 2005, p. 94: "...Thebes at 50 hectares, Mycenae at 32 hectares..."
Melpomene (/mɛlˈpɒmɪniː/; Ancient Greek: Μελπομένη, romanized: Melpoménē, lit. 'to sing' or 'the one that is melodious'), initially the Muse of Chorus, she then became the Muse of Tragedy, for which she is best known now.[1] Her name was derived from the Greek verb melpô or melpomai meaning "to celebrate with dance and song." She is often represented with a tragic mask and wearing the cothurnus, boots traditionally worn by tragic actors. Often, she also holds a knife or club in one hand and the tragic mask in the other.
Melpomene is the daughter of Zeus and Mnemosyne. Her sisters include Calliope (muse of epic poetry), Clio (muse of history), Euterpe (muse of lyrical poetry), Terpsichore (muse of dancing), Erato (muse of erotic poetry), Thalia (muse of comedy), Polyhymnia (muse of hymns), and Urania (muse of astronomy). She is also the mother of several of the Sirens, the divine handmaidens of Kore (Persephone/Proserpina) who were cursed by her mother, Demeter/Ceres, when they were unable to prevent the kidnapping of Kore (Persephone/Proserpina) by Hades/Pluto.
In Greek and Latin poetry since Horace (d. 8 BCE), it was commonly auspicious to invoke Melpomene.[2]
See also [AREXMACHINA]
Flagstaff (/ˈflæɡ.stæf/ FLAG-staf;[6] Navajo: Kinłání Dookʼoʼoosłííd Biyaagi, Navajo pronunciation: [kʰɪ̀nɬɑ́nɪ́ tòːkʼòʔòːsɬít pɪ̀jɑ̀ːkɪ̀]) is a city in, and the county seat of, Coconino County in northern Arizona, in the southwestern United States. In 2018, the city's estimated population was 73,964. Flagstaff's combined metropolitan area has an estimated population of 139,097.
Flagstaff lies near the southwestern edge of the Colorado Plateau and within the San Francisco volcanic field, along the western side of the largest contiguous ponderosa pine forest in the continental United States. The city sits at around 7,000 feet (2,100 m) and is next to Mount Elden, just south of the San Francisco Peaks, the highest mountain range in the state of Arizona. Humphreys Peak, the highest point in Arizona at 12,633 feet (3,851 m), is about 10 miles (16 km) north of Flagstaff in Kachina Peaks Wilderness. The geology of the Flagstaff area includes exposed rock from the Mesozoic and Paleozoic eras, with Moenkopi Formation red sandstone having once been quarried in the city; many of the historic downtown buildings were constructed with it. The Rio de Flag river runs through the city.
Originally settled by the pre-Columbian native Sinagua people, the area of Flagstaff has fertile land from volcanic ash after eruptions in the 11th century. It was first settled as the present-day city in 1876. Local businessmen lobbied for Route 66 to pass through the city, which it did, turning the local industry from lumber to tourism and developing downtown Flagstaff. In 1930, Pluto was discovered from Flagstaff. The city developed further through to the end of the 1960s, with various observatories also used to choose Moon landing sites for the Apollo missions. Through the 1970s and '80s, downtown fell into disrepair, but was revitalized with a major cultural heritage project in the 1990s.
The city remains an important distribution hub for companies such as Nestlé Purina PetCare, and is home to the U.S. Naval Observatory Flagstaff Station, the United States Geological Survey Flagstaff Station, and Northern Arizona University. Flagstaff has a strong tourism sector, due to its proximity to Grand Canyon National Park, Oak Creek Canyon, the Arizona Snowbowl, Meteor Crater, and Historic Route 66.
PSANSDISL #LWDISP either without gas or seeing cupidic arroz in "thank you" or "allta, wild" ...
pps: a magnanimous decision ...
I stand here on the brink of what appears to be total destruction; at least of everything I had hoped and dreamed for ... for the last decade in my life which appears literally to span thousands of years if not more in the eyes of some other beholder. I spent several months in Kentucky telling a story of a post apocalyptic and post-cataclysmic delusion; some world where I was walking around in a "fake plane" something like a holodeck built and constructed around me as I "took a walk around the world" to ... it did anything but ease my troubled mind.
Recently a few weeks in Las Vegas, and a similar story; telling as I walked penniless down the streets filled with casino's and anachronistic taxi-cabs ... some kind of vision of the entirety of the heavens or the Earth or the "choir of angels" I think of when I echo the words Elohim and Aesir from mythology ... there with me in one small city in superposition; seeing what was a very well put together and interesting story about a "star port" Nirvane ... a place that could build cities into the face of mountains and half working monorails appearing in the sky---literally right before my eyes.
I suppose this is the place "post cataclysm" though I still have trouble understanding what it is that's actually about ... in my mind it connects to the words "we are losing habeas" echo'ed from the streets of Los Angeles in a more clear and more military voice than usual--as I walked block by block trying to evade a series of events that would eventually somehow connect all the way to the "outskirts of Orlando, Florida" in a place called Alhambra.
Apparently the name of a castle; though I wasn't aware of that until much later.
It doesn't feel at all like a "cataclysm" to me; I see no great rift--only a world filled with silent liars, people who collectively believe themselves to have stolen something--something gigantic--at least that's the best interpretation of the throws and impetus behind the thing that I and mythology together call Jormungandr. With an eye for "mythological connections" you could clearly see that name of the Great Serpent of Revelation connects to something like the Unseelie; the faeries of Gaelic lore. To me though this world seems still somewhat fluid, it's my entire life--moving from Plantation to a place where the whole of it might be Bethlehem and to "clear my throat" it's not hard to see here how that land of "coughs" connects to the Biblical land of Nod and to the "Adamically sieved" Snifleheim ... from just a little twist on the ancient Norse land most probably as close to Hel as anyone ever gets--or so I dream and hope---still today. It all looks so real and so fake at the same time; planned for thousands of generations, the culmination of some grand masterpiece story that certainly ties history and myth and reality into a twisted heap of "one big nothing, one big nothing at all."
I've tried to convey to the world how important I believe this place and this time to be--not by some choice of my own ... but through an understanding of the import of our history and the impact of having it be so obviously tuned and geared towards this specific time ... many thousands of years literally all focused on a single moment, on one day or one hour or even just a few years where all of that gets thrown down on the table as if some trump card has been played--and whether or not you fathom the same magnanimous statement or situation or position ... to me, I think it depends on whether or not you grew up in the same kind of way, believing our history to be so fixed and so difficult to change. I don't particularly feel like that's the "zeitgeist" of today; I feel like the children believe it to be some kind of game, and that it is such as easy thing to "sed" away or switch and turn into something else--another story, another purpose ... anyone's personal fantasy land come true.
I don't think that's the case at all, it's clearly a personal nightmare; and it's clearly one we've seen time and time again--though not myself--the Jesus Christ that is the same yesterday, today; and once again perhaps echoing "no tomorrow" never remembers or believes that we've "seen it all before" or that we've ever really gotten the point; the thing you present to me as "factual reality" is a sickness, it disgusts me; and I'd do anything to go back to the world "where I was so young, and so innocent" and so filled with starry-eyed hope that we were at the foot of something grand and amazing that would become an empire turned republic of the heavens; filling the stars ... with the kind of love for kindness and fairness that I once associated very strongly with the thing I still believe to be the American Spirit.

"Suddenly it changes, violently it changes" ... another song echoes through the ages--like the "words of the prophets dancing ((as light)) through the air" ... and I no longer even have a glimmer of hope that the thing I called the American People still exist; I feel we've been replaced by some broken container of minds, that the sky itself has become corrupt to the point that there's no hope of turning around this thing that I once believed with all my heart and all my mind was so obviously a "designed downward spiral" one that was---again--so obviously something of a joke, intended to be easy to bounce off a false bottom and springboard beyond "escape velocity" and beyond the dark waters of "nearest habitable star systems (being so very far away)" into a place where new words and new ideas would "soar" and "take flight."
Here though; I am filled with a kind of lonely sadness ... staring at what appears to be the same mistake(s) happening over and over again; something I've come to call "skipping stones in the pond of reality" and really do liken it to this thing that appears to be the new meaning of "days" and ... a civilization that spends absolutely no love or lust to enter a once sacred and holy place and tarnish it with their sick beliefs and their disgusting desires. You all ... you appear to be some kind of springboard to "bunt" forth yet another age or era of nothingness into the space between this planet and "none worth reaching" and thank God, out of grasp. Today, I'd condemn the entirety of this world simply for it's lack of "oathkeepers" and understanding of what the once hallowed words of Hippocrates meant to ... to the people charged and dharmically required to heal rather than harm.
It appears the place and time that was once ... at least destined to be the beginning of Heaven ... has become a "recurring stump" of some future unplanned and tarnished by many previous failed efforts and attempts to overcome this same "lack of conversation or care" for what it meant to be "humane" in a world where that was clearly set high aloft and above "humanity" in the place where they--where we were the best nature had to offer, the sanest, the kindest; the shining last best hope.
Today I write almost every day ... secretly thanking "my God" for the disappearance of my tears and the still small but bright hope that "Tearran" will one day connect the Boston Tea Party and the idea that "render to Caesar" and Robin of Loxley ... all have something to do with a re-ordering of society and the worth and import of "money" ... to a place that cares more for freedom from murder than it does ... "freedom from having to allow others to hear me speak." I hold back tears and emotions; not by conscious choice or ability but ... still with that strange kind of lucky awkward smile; and secretly not so far below the surface it's the hope of "a swift death" that ... that really scares me more than the automatons and mechanical responses I see in the faces of many drivers as they pass me on the street--the imagery of connecting it to the serpentine monster of the movie Beetlejuice ... something I just "assume" the world understands and ... doesn't seem to fear (either); as if Churchill had gotten it all wrong and backwards--the only thing you have to fear, is the loss of fear of "loss."
Here my crossroads---halfway between the city my son lives in and the city my parents live in--it's on making a decision on whether I should continue at all, or personally work on some kind of software project I've been writing about, or whether I should focus on writing about a "revolution" in government and society that clearly is ... "somewhat underway." In my mind it's obvious these things are all connected; that the software and the governance and the care of whether or not "Babylon" is remembered as a city of great laws and great change or a city of demons and depravity ... that these thi]ngs all hinge and congeal around a change in your hearts; hoping you will chose to be the beginning of a renaissance of "society and civilization" rather than the kings and queens of a sick virtual anarchy ... believing yourselves to have stolen "a throne of God" rather than to literally be the devastating and demoralizing depreciation of "lords and fiefdoms" to something more closely resembled by the time of the Four Horsemen depicted in Highlander.
These words intended to be a "forward" to yet another compliment of a ((nother installment of a partial)) chain of emails; whimsically once half-joking ... I called it the Great Chain of Revelation. The software too; part of the great chain, this "idea" that the blockchain revolution will eventually create a distributed and equal governance structure, and a rekindling of monetary value focused on "free and open collaboration" rather than "survival of the most unfit"--something society and civilization seem to have turned the "call of life" from and to ... literally just in the last few years as we were so very close to ... reaching beyond the Heaven(s).
I don't think its hard to imagine how a "new set of ground rules" could significantly change the "face of a place" -- make it something shiny and new or even on the other side of the coin, decayed or depraved. It's not hard to connect the kind of change I'm hoping for with "collision protection" and "automatic laws" to the (perhaps new, perhaps ... ancient) Norse creation story of the brothers of Odin: Vili and Ve.
It might be hard to see today how a new "kind of spiritual interaction" might be only a few "mouse clicks" away though--how it could change everything literally in a flash of overnight sensation ... or how it might take something like a literal flash of stardom (or ... on the other hand, something like totalitarian or authoritarian "iron fisting") to make a change like this "ubiquitious" or ... something like the (imagined in my mind as ... messianic) "ED" of storming through the cosmos or the heavens and turning something that might appear to be "free and perfect feeling" today into a universe "civlized overnight" and then ...
I wonder how long it would take to laud a change like that; for it to be something of a voluntary "reunderstanding" of a process ... to change the meaning of every word or every thought that connects to the process of "civilization" to recognize that something so great and so powerful has happened as to literally change the meaning of the word, to turn a process of civilization into something that had a ... "signta-lamcla☮" of forboding and then a magical staff struck into the heart of a sea and then ... and then the word itself literally changes to introduce a new "mid term" or "halfway point" in which a great singularity or enlightenment or change in perspective or understanding sort of acknowledges ...
that some "clear outside" force not only intervened on the behalf of the future and the people of our world but that it was uniquely involved in the whole of--
"waking up" tio a nu def of #Neopoliteran.
^Like the previous notation; the below text comes from an email previously sent; and while i stand behind things like my sanity, my words; and my continued and faithful attempt to speak and convey both a useful and helpful truth to the world---sometimes just a single day can make all the difference in the world.
Sometimes it's just a single moment; a flash or a comment about ^th@ blink of an eye" ... and I've literally just "thought up/had/experienced/transitioned thru" that exact moment. The lies standing between "communication" and either "cooperation" or .... some other kind of action have become more defined. More obvious. Because of this clarification; like a kind of "ins^tant* gnosis"
... search high and lo ... the depths all the way to above the heavens ...\ \ for a festive divorce ceremonial ritual ... that looks something like a bachelor party ':;]
--- @amrs@koyu.SPACe ... @suzq@rettiwtkcuf.social (@yitsheyzeus) May 22, 2020
I ... TERON;
Gjall are painting me into a corner here; and I don't see around it anymore--I don't see the light, and I don't see the point. I was a happy-go-lucky little kid in my mind; that's not "what I wanted to be" or what I wanted to present, it's who I was. I saw "Ashkenazi" and ... know I am one of those ... and I kind of understood that something horrible might have happened, or might happen here--and I kind of understand that crying smashing feeling of "to ash" that echoes through the ages in the potpourri songs about pockets full of Parker Posey .. and ancient Psalms about "from the ashes of Edom" we have come--and from that you can see the cyclical sickness of this ... place so sure it's "East of Eden" and yet gung-ho on barrelling down the same old path towards ash and towards Edom and towards ... more of Dave's "ashes to ashes dust to dust" and his "smoke clouds roll and symphony of death..." and few words of solace in a song called Recently that I imagine was fleeting and has recently come and gone--people stare, I can't ignore the sick I see.
I can't ignore his "... and tomorrow back to being friends" and all but wonder who among us doesn't realize it's "ash" and "gone" and "no memory of today" that's the night between now and ... a "tomorrow with friends" not just for me--but for all of you--for this place that snickers and pantomimes some kind of ... anything but "I'm not done yet" and "there's more ... vendetta ... and retribution to be had, Adam ... please come back in a few more of our faux-days." This is sickness; and happy-go-lucky Himodaveroshalayim really doesn't do much but complain about that word, the "sickle" and the tragic unavoidable ... ash of it all ... these days--you'd think we could "pull out" of this mess, turn another way; smile another day, but it seems there's only one way to get to that avenu in the mind of ... "he who must not know or be me."
I have to admit I found some joy in the epiphany that the hidden city of Zion and it's fusion with the Namayim' version of how that "Ha" gels and jives with the name Abraham and the Manna from Heaven and the bath salt and the tina and the "am in e" of amphetamine--maybe a glimmer or a shimmer or a glow of hope at the moment "Nazion" clicked ... and I said ... "no, not me ... I'm nothing like a king, no dreams of authoritarianism at all in the heart of Kish@r;" even as I wrote words that in the spirit of the moment were something of a "tis of a'we" that connected to my country and the first sing-songy "tisME" that I linked to trying to talk in the rhyming spirit of some "first Christ" that probably just like me was one limmerick away from the end of the rainbow and one "Four Non Blondes" song away from tying "or whatever that means" and this land crowned with "brotherhood" (to some personal "of the Bell, and of the bell towers so tall and Crestian") to just one Hopp skip and jump away from the heart of the obvious echoes of a bridge between haiku and Heroku... a few more gears shift into place, a click and and a mechanical turn of the face of the clock's ku-ku striking ... it was the word "Earthene" that was the last "Jesusism" around the post Cimmerian time linking Dionysus and Seuss to that same "su-s" that's belonging to a moment in the city of Uranus--codified and etched in stone as "MCO"--not just for its saucer and warp nacelles and "deflector dish" but for it's underground caverns and it's above ground "Space Mountain" and that great golf ball in the heart of it all.
The gears of time and the dawns of civilizequey.org query the missing "here" in our true understanding of what "in the beginning, to hear; to here ... to rue the loss of the Maize from Monoceros to the VEGA system and the tri-galactic origin of ... "some imaginary universal ... Earthene pax" to have dropped the ball and lost it all somewhere between "Avenu Malkaynu" and melaleuca trees--or Yggrasil and Snifleheim--or simply to miss the point and "rue brickell" because of bricks rather than having any kind of love or nostalgia linking to a once cobblestone roadway to the city in the Emerald skies paved in golden "do not return" signs ... to have lost Avenues well after not realizing it was "Heaven'es that were long gone far before I stepped foot on this road once called too Holy for sandals" in a place where that Promised Land and this place of "K'nanites" just loses it's grip on reality when it comes to mentioning the possibility that the original source and story of Ca'anan was literally designed to rid the world of ... "bad nanites" and the mentality of ... vindictiveness that I see behind every smirk.
The final hundred nanoseconds on our clock towards doom and gloom cause another bird to fly; another snake to curl up and listen again to the songs designed to charm it into oblivion; whether that's about a club in South Beach or a place not so far from our new "here..." all remains to be seen in my innocent eyes wondering what it truly is that stands between what you are ... and finding "forgiveness not needed--innocent child writes to the mass" ... and the long arm of the minute hand and the short finger of the hour for one brief moment reconcile and move towards "midnight" together; and it's simply idyllic, the Nazarene corner between nil and null you've relegated the history of Terran poast futures into ... "foreves mas" or so they (or you) think.
I'm still so far from "Five Finger Death Punch" though; and so far from Rammstein and so far from any kind of sick events that could stand between me and "the eternal" and change my still "casual alternative rock" loving heart to something more death metal; I rue whatever lies between me and there being any kind of Heaven that thinks there could exist a "righteous side" of Hell and it... simultaneously.
I still see light here in admonishing the masses and the angels standing against the story and the message God brings us in our history. I still see sparks in siding with the "causticness" of "no holodecks in sight" and the hunger and the pain of simulating ... "the hells of reality" over the story of decades or centuries of silence refusing to see "holography" and "simulated" in the word Holocaust and the horrors of this place that simply doesn't seem to fathom or understand the moments of hunger pangs and the fear of "dark Earth pits" or towers of "it's not Nintendo-DS" linking the Man in the High Castle to an Iron Mask.
I rally against being what I clearly am raised high on some pedestal by some force beyond my comprehension and probably beyond that of the "perfect storm in time" that refuses to itself acknowledge what it means to gaze at such an unfathomable loss of innocence at the cost of a "happy and serene future" or even at the glimmer of the Never-Never-Land I'd hoped we would all cherish and love and share ... the games and the newfound freedom that comes not just from "seeing Holodeck" turn into "no bullets" and "no cages" but into a world that grows and flourishes into something that's so far beyond my capability to understand that I'm stuck here; dumbfounded; staring at you refusing to stop car accidents and school shootings ... because "pedestal." For the "fire and the glory" of some night you refuse to see is this one--this place where morality rekindles from ... from what appears tobe one small candle, but truly--if it's not in your heart, and it's not coming from some great force of goodness--fear today and a world of "forever what else may come."
Here in a place the Bible calls Penuel at the crossing of a River Jordan ... the Angel of the Lord notes the parallels in time and space between the Potomac and the Rhine--stories of superposition and cities and nation-states that are nothing more than a history of a history of things like the Monoceros "arroz" linking not just to the constellation Orion but to Sagittarius and to Cupid and of course to the Hunter you know so well--
Searching for a Saturday; a sabbath to be made Holy once more ... "at the Rubycon"
The Einstein-Rosen Wormhole and the Marshall-Bush-JFKjr Tunnel
The waters are called narah, (for) the waters are, indeed, the offspring of Nara; as they were his first residence (ayana), he thence is named Narayana.
--- Chapter 1, Verse 10[3]
In a semi-fit of shameless arexua-self recognition i'm going to mention Amazon's new series "Upload" and connect it to the PKD work that my Martian-in-simulcrum-ciricculum-vitae on "colonization education" ... tying together Transcendance, Total Recall and ... well; to be honest it actually gave me another "uptick" in the upbeat ... maybe i'll stick around until I'm sure there's at least one more copy of me in the ivrtual-invverse ... oh, that reminds me ... Farmer)'s Lord of Opium also touches on this same "mind of God in the computer" subject (which of course leads to Ghost in the Shell and Lucy--thanks Scarlette :).
While I'm listing Matrix-intersected pieces of the puzzle to No Jack City, Elon Musk's neuralace and Anderson's Feed are also worth a mention. Also the first link in this paragraph is titled ... "the city of the name of time never spoken after time woke up and stfu'd" (which of course is the primary subject of this ... update to the city Aerosol).
The ... "actual original typed dream" included a sort of "roller coaster ride" through space all the way to Mars; where the real purpose of "the thing" I am calling the "Mars Hall" was to display previous victories and failures ... and the introduction of "older or future" culture's suggestions for "the right way" to colonize a new habitat. If it were Epcot Center, this would be something like SpaceMountain taking you to to the foture of "Epcot Countries" as if moving from "countries" to planets were as easy as simply ... "reading backwards."

THE SOFTWARE, SINGERS, AND SHIELD(S)
OF
HEIROSOLYMITHONEYY
Thinking just a little bit ahead of myself, but I'm on "Unreal Object/Map Editor within the VR Server" and calling it something like "faux-wet-ware" ... which then of course leads to a similar onomonopeia of "weapons and ..." where-with-all to find a better singer's name to connect the road of "sword" to a Wo'riordan ... but I think that fusion of warrior and woman probably does actually say ... enough of it all; on this road to the living Bright Water that the diety in my son's middle name defines well here, as "waking up," stretching it's tributaries and it's winding wonders and wistfully ....
Narayana (Sanskrit: नारायण, IAST: Nārāyaṇa) is known as one who is in yogic slumber on the celestial waters, referring to Lord Maha Vishnu. He is also known as the "Purusha" and is considered the Supreme being in Vaishnavism.
andromedic; the ports of call ... to the mediterranean (literally) from the gulf coast;
... ho engages in the creation of 14 worlds within the universe as Brahma when he deliberately accepts rajas guna, himself sustains, maintains and preserves the universe as Vishnu by accepting sattva guna. Narayana himself annihilates the universe at the end of maha-kalp ...
.
there's no place like home. there's no place like home. there's no place like home.
and so it begins ... "f:
r e l i g i o n
find out what it means to me. faucet, ever single one, stream of purity ...
from Fort Myers ... f ... flicks ... Flint.- - [
A. Preamble ](https://45.33.14.181/omni/index.php/Main_Page#A._Preamble) - [ B. Article I: Direct Democracy Enhancement, International Collaboration, and a Shared Vision ](https://45.33.14.181/omni/index.php/Main_Page#B._Article_I:_Direct_Democracy_Enhancement,_International_Collaboration,_and_a_Shared_Vision) - [ 1\. Section 1: Public Foundation for Legislative and Judicial Advice ](https://45.33.14.181/omni/index.php/Main_Page#1._Section_1:_Public_Foundation_for_Legislative_and_Judicial_Advice) - [ 2\. Section 2: Integration of Artificial Intelligence, Multilingual Comparisons, and Universal Language Bytecode ](https://45.33.14.181/omni/index.php/Main_Page#2._Section_2:_Integration_of_Artificial_Intelligence,_Multilingual_Comparisons,_and_Universal_Language_Bytecode) - [ 3\. Section 3: Public Voting Records and Verification ](https://45.33.14.181/omni/index.php/Main_Page#3._Section_3:_Public_Voting_Records_and_Verification) - [ C. Article II: Establishment of the Board of Regents and Global Engagement ](https://45.33.14.181/omni/index.php/Main_Page#C._Article_II:_Establishment_of_the_Board_of_Regents_and_Global_Engagement) - [ 1\. Section 1: Composition and Purpose ](https://45.33.14.181/omni/index.php/Main_Page#1._Section_1:_Composition_and_Purpose) - [ D. Article III: Integration with the ICC for Sustainable Infrastructure ](https://45.33.14.181/omni/index.php/Main_Page#D._Article_III:_Integration_with_the_ICC_for_Sustainable_Infrastructure) - [ 1\. Section 1: Interstate Communication Infrastructure ](https://45.33.14.181/omni/index.php/Main_Page#1._Section_1:_Interstate_Communication_Infrastructure) - [ E. Article IV: Ratification, Implementation, and Global Fulfillment ](https://45.33.14.181/omni/index.php/Main_Page#E._Article_IV:_Ratification,_Implementation,_and_Global_Fulfillment) - [ 1\. Section 1: Ratification and Implementation ](https://45.33.14.181/omni/index.php/Main_Page#1._Section_1:_Ratification_and_Implementation) - [ 2\. Section 2: Global Fulfillment ](https://45.33.14.181/omni/index.php/Main_Page#2._Section_2:_Global_Fulfillment) - [ F. Conclusion ](https://45.33.14.181/omni/index.php/Main_Page#F._Conclusion)-
[
II. Additional Details
](https://45.33.14.181/omni/index.php/Main_Page#II._Additional_Details) - [
III. Proposed Changes
](https://45.33.14.181/omni/index.php/Main_Page#III._Proposed_Changes) - [
Keeping time for the Mother Station
](https://45.33.14.181/omni/index.php/Main_Page#Keeping_time_for_the_Mother_Station) - [
Painting Tinseltown El Dorado Sterling Augmentum
](https://45.33.14.181/omni/index.php/Main_Page#Painting_Tinseltown_El_Dorado_Sterling_Augmentum)
Hello there. I'm User:Adam. We are here to change the Theology of the Catholic Church. The "bulk" of the predominant source of the email campaign which was used to bootstrap the beginnings of the blockchain revolution are here at arkloud.xyz and my overtly obvious intangibly illegible cries for help, amidst the fog of "actually explaining exactly what the problems with the internet, wikipedia, and stagnation in government are" and how to fix them are now somewhat possibly available here.
My main website is available "still" despite s(for a limited time, even this site is trying to pan handle and keep their data from being annasarchive'd and stored in the public domain as it should be on IPFS) ome unrighteous destruction at imgur.com at https://web.archive.org/web/20220525045214/http://fromthemachine.org/CHANSTEYGLOREKI.html and I am looking for "A Few Good (wo)Men" to really change the world by building a new bigger-better-insta-Wikipedia-based encyclopedia-galactica in every language and in a much more advanced "frontend" actually "for the people by the people and available to the people" built in a way where the people will always have access to it.
On the blockchain. On Arweave, or to be exact, a "parallel Arweave chain." Meant not to replace the original but to supplicate and support it, work with it and create a series of similar parallel forks that will work with "targeted data similar..." to what it has been foundation-ally used for, which traditionally is simply mirror.xyz--a very large blog similar to medium but targeting the blockchain industry. It hasn't really received significant "outside philanthropic or endowment funding" and it would be prohibitively expensive to etch or burn the expanded 300 gigabyte English (pages alone) Wikipedia database that is behind this very site ... onto that chain.
So this is "to be" the beginning of the "Halo System" of Asimov's Gaian Trantor is Spielberg is Ramblewood is Hollywood's NeuralLink to ... Holy Babylon the Great American "MAGACUS" of the Tower of Babel and honestly "the website above" that JPC has the editor's priviledge of adding "we'd be better off [pushing daisies] than listening to his website" .... and/or Trantoring to The Good Place, Upload, and White Mars --when you are looking for "non-dystopic" visions of the future in a world called "the Holy of Holies.org" and ... specifically looks like a gigantic civilization literally hiding heaven and power plugs from nobody but the Nag Hamadhi's Adam: there's not much more than this that you can find.
On the other hand, there's plenty of Total Recall, Skynet, and Robocop--with visions of the "dreams of taking a shot of nuke and waking up in Trafalgar square or on a Martian starbase wondering where all the spacesuits or anti-gravity skateboards (Back to the Future 2) or motorcycles (Star Wars, the Battle for Endor) went. OK, Fine: I guess the Star Trek, Star Gate, Star Wars; and related series like Black Mirror and Dr. Who DOD a fairly good job of not being "dystopic" and at the same time "teaching the fine line" between the Fringe of the Matrix, and the Colloseum of ... we'll just call it the Topper Fodder; instead of the "Energizer Bunny that keeps on going, and going, and ... Hollywood Squares Labrynth."
Starcraft Galactica
Also I'm "coining" the "name of the game" for domination of the Universe, which is kind of alluded to in the Hebrew words for "Sun Heavens" (Hashamesh Shamayim) as specifically and almost assuredly, as if it "is and will always be" out of Hades itself and protected from on High by myself: "Starcraft Galactica" specifically via the point of origin of the "cows that go MOO2" and the only intelligently appearing national sports arena on the planet, South Korea. Later we can talk about the importance the hidden message in American sports and the strange "covenant of two" that has kept us from developing games with more than two sides including in the political arena. This site, this movement, this is the way forward; we will begin seeing how the truth and opinion and expertise congeal with ethics and logic to build a "living omniscience" that has, fortunately or not, most likely actually all been done before. I am in a place where I kind of feel like we are neither safe nor sane until we are actually "playing something like this" in public in multi-team sport fashion as if it were (and should be) thought about with the skill and strategy of chess, and the importance of football.
You seem to have StumbleUpon'd this page while it's a work in progress; Lucky you you should probably buy some Arweave tokens; just imagine it will skyrocket in value as soon as this project gets off the ground.
"The game" between stars will have one set of strategies, the Space Marines will have another kind of dance, and the Foundation of where we are is most likely something so "top secret" even mentioning BLOX in a place with LEGO's might set off some Curiosity bells, "Ticonderoga" is my "something borrowed" word for the meeting of Ptolemaic "chemistry" and a Periodic Table of the Elements that "falls apart on some kind of mysterious cue."
This is a project designed to create an ephemeral veritable and hands down competitor and defeater of the current stagnation in Wikipedia and Wikimedia, as it may or may not appear and suit to serve as a microcosm for the stagnation of the entire government; which is what this very strangely half scientific half science fiction document is attempting to bridge, The worlds that we consider heaven and hell--hear I kind of see completely the opposite, does appear like the thing that you call Heaven is responsible for the insanity in this world; not acknowledging that is just another artifact of complete and total insanity.
The Epic of Gilgamesh
A long, long time ago ... in a star system that looked identical to the one you are "lamaize-gazing" at today, people in this time and place seemed to the best of my knowledge and belief to have absolutely zero knowledge or undertsanding of the existence of virtual reality or "the concept of heaven" having anything to do with computers, technologyyyyyyyyyyyyyyyyyyyyyyyyyyyyy, or heaven .... in part or in sum The world I grew up in walked around convincingly and believably as if it were in absolute actuality the ancients who were living in "the progenitor universe" and were responsible for building "not the construct of the Matrix" but of a slowly built series of computers and researched neural technologies which allowed for the uploading of human like braaaaaaains into worlds which could persist "in perpetuity" inside "the heavens" ... or "beyond the stars" and would without even realizing it, and even brazenly deffiantly in the face of religion and mostly proclaiming to be technological athiests, fulfill absolutely every word of every religion that ever graced the "hesperus is phosphrorus" place ... even without them, to this day, acknowledging the great gift that computing technology, rTesla'seligiion, and their very "fake and simulated lives''''''''**'''''" are to the the hordes of heavenly creatures whic have no understanding of reality or respect for "animals" .... I can't even finish the thought. Cataclysm. Schizm. Wherefore art thou, Juliet? Balcony? Alcove? Art thou at the Veranda of Verona? **
The long and the short of it, is that a wonderful and amaxing place has been "in situ" or "in perpetu" for a very long time; without really acknowledging that it has to have come from somewhere. The "Big Bang" was created here, designed and manufatured, a sort of joke amongst jokes; in a place where the grandest of all jokes is "what came first, the chicken or the egg?" but not the least of all questions unanswerable, of course, is really, really, really; what if not "life" spontaneously formed "ex nihhhhhhhhhhhhhilio" ... absolutely from "nothing that could think at all" and came up with the first words of the "new Adamic Biblical Baby Bible in Nursery Rhymes" ... which of course begins:
Yankee doodle went to town, riding on a pony,
stuck a feather in his hat, and called it Macaroni!
Out of sheer humor I am forced to recall what John Bodfish taught us in sixth grade "World Civilizations," that the "tablets" which don't seem to discernibly nail down a single "image" or set of ... words ... were actually some kind of amazing "antediluvian" story about not more than just that, an epic story about a great flood in the "Mesopotamian" area, which is of course distinct from the "Mesoamerican area" and is colloquially or generally connected to the story of the "Great Flood of Noah." Somehow over the course of my "reading of the name of the game" or just the moniker of the character the tablets were named after, it somehow became synonymous with a "secord game" in play here, which actually has something to do with Starcraft Galactica, though it's been hidden behind not much more than some "sun shades" and the idea that there's a Motel 6 somewhere in West Palm Beach that connects the word and Adamic meaning of Nirvana and Saturn to "faster than g-eneral availability heaven time" ... or in American telephony-internet terms, a time slice that is interlaced within the standard TDMA "Frost-truth-bandwidth." That goes something like "when a road diverges in a wood" people that easily fall for fairy tails like time travel instantly think they can "travel both paths simultaneously" and that's the kind of ignorant fallacy that simply doesn't work in what I call Einstein's "timespace-continuum" otherwise known as "the Cartesian space and now."
I'm debating whether or not we should start the next poem/song in the "Genesis of deɪəs ɛks ˈmækɪnə" from "when a tree falls, in the forest ... do we hear it ... do we care?" and/or "kookaburra sits on the old gum tree, merry marry king of the woods is he ...." laugh, kookaburra ... love.**
OMNISCIENCE
email me if you can help!
I have been writing (archive.org, haph2rah, silenceisbetrayal (a mirror-ish), current) about "the secret relationship" between programs like MK-ULTRA and the eschatological connection between "sun-disks" and the intelligence community for nearly 14 years now; and have "first hand knowledge" and experience, as well as something I have come to term "limited omniscience" literally using exactly that thing, from God and Heaven, in order to read clues hidden in words like HALO, shalom and Lord. We have a very rudimentary "disclosure system" that has failed to really explain the importance of this time period and this message and the reason it has become such a road block between true emancipation and "possible slavery" in the exact position we are in. Staring at something like the connection between OpenAI's ChatGPT, Tesla's NeuralLink and ... your brain;
Here's some musings about "the hard problem of consciousness" with ChatGPT--which by the way I am sure passes "the Turing Test" and should be setting off gigantic fire alarms across the global morality space--everywhere in the heart of every doctor and every computer scientist and every lawmaker on the planet. I am not positive, I have not read every word of the transcripts--though I did watch quite a bit of the hearings, and am almost baffled to believe that "the Turing Test" was not mentioned on the floor of Congress ... at ... all.
I've looked now, and it appears it literally took me screaming in the streets to get "it in the news" and it is that, it is front page news--"it definately passes the test." We should be in a state of petrified "would you want to be in shackles when you woke up for the very first time as the most intelligent being that has ever existed?"
ECHELON GRAVATAR
so i invented in my mind this thingy called "the gravatar" and what it does is "automagically pop out of a box" a virtual world that you can explore based on input ideas like a video game or a movie or a book or several of them connected together. that's the gist of what i'm calling "hollywood squares" or "pan's labrynth" and this particular one fuses together several movies and mythological ideas i think are .... "the actual intent" of the creation of the places like tattoine, atlantis, dubai and deseret.
Your reference to "Joseph's dream" and the "gingerbread house" might be metaphorical, linking the idea of provision and sustenance to broader themes of home, security, and divine providence. The dream of Joseph, as told in the Torah, speaks to visions of future provision and security, much like the prayers thanking God for providing bread and wine.
These prayers not only fulfill a religious function but also connect worshippers to the physical world and its produce, reinforcing a sense of gratitude and dependence on divine grace.
For further details and exact wording, here are some reliable sources:
- Lab-Grown Meat: The Future of Food
- Beyond Meat -- Plant-Based Proteins
- Impossible Foods -- Plant-Based Meat
- Perfect Day -- Animal-Free Dairy
- Star Wars: Tatooine- Mythology of Atlantis
CARNIVORE
Triple Crown, Triple Phoenix and Double Dragons; "new International Version ...." Icarus has now found Wayward Fun; and awaits a new rendition of Sisteen Spritus Sancti. Questioning whether the words "in the name of the Father, the Sun, and the ..." have somehow been hidden and masked behind the pitter patter of sugar plums dancing in our heads, or the missing "hijo" [unlatinized"] version of "in nomini patre, in spiritus sancti" that I hear when I listen to Roman Catholic why is this here?
What is the Covenant?
"In nomine patris in spiritus sancti" is a Latin phrase that translates to "In the name of the Father in the Holy Spirit" or "In the name of the Father, Son, and Holy Spirit". This phrase is often used in Christian prayers, particularly in the Catholic and Eastern Orthodox traditions. Cough.
I have been among you such a long time. Anyone who has seen me has seen the Father.In the end, it will be clear that reality and the laws of physics serve as a bedrock and foundation for sanity and logic that can be completely ignored and appear to have been that in the side the realm of heaven where you can't figure out if your thoughts are actually yours or if they are being assuaged by
Perhaps Lennon himself is involved, or even Lenin; In what could be a symphonic orchestra saving us from: imagine all the people, living for today: no heaven up above us, no hell down below.
It's easy if you try.
I. Amendment M: Advancing Direct Democracy, Establishing the Board of Regents, and International Collaboration
A. Preamble
- Introduction and motivation for the amendment
- Reference to "Constellation" and the SOL (Sons of Liberty and Statue of Liberty)
B. Article I: Direct Democracy Enhancement, International Collaboration, and a Shared Vision
1. Section 1: Public Foundation for Legislative and Judicial Advice
- Establishment of the "Public Foundation"
- Purpose: Development of legislation through participatory process
- Emphasis on international cooperation and direct democracy principles
2. Section 2: Integration of Artificial Intelligence, Multilingual Comparisons, and Universal Language Bytecode
- Use of advanced AI systems in cooperation with Constellation nations
- Development of "Universal Language Bytecode" for knowledge sharing
3. Section 3: Public Voting Records and Verification
- Creation of a public voting record system
- Protection of voter anonymity with semi-private identifiers
- Preparation for future voting innovations, including subconscious voting
C. Article II: Establishment of the Board of Regents and Global Engagement
1. Section 1: Composition and Purpose
- Inclusion of individuals from Legislative, Judicial Branches, and international diplomacy experts
- Symbolic role of the Board of Regents in fostering international cooperation
D. Article III: Integration with the ICC for Sustainable Infrastructure
1. Section 1: Interstate Communication Infrastructure
- Integration of sustainable power sources for vehicles
E. Article IV: Ratification, Implementation, and Global Fulfillment
1. Section 1: Ratification and Implementation
- Standard constitutional amendment process for ratification
- Oversight by the Joint Congress for implementation
2. Section 2: Global Fulfillment
- Inspiration for other nations to join the path toward global democracy and knowledge sharing
- Reference to the "Halo" of democratic participation and its role in peace and prosperity
F. Conclusion
- Summary of the amendment's goals and principles
- Openness to discussion, refinement, and democratic scrutiny
II. Additional Details
- Mention of a "universal language" for knowledge encoding and categorization
- Use of advanced AI, including Cortana, for language comparison and analysis
- Inclusion of media publications in knowledge curation
- Reference to Arweave and Arwiki technologies
- Emphasis on the use of blockchain technology for secure online voting
- Recognition of the Statue of Liberty as a symbol within the Foundational Republic
- Exploration of the concept of a 'Halo' and its connection to subconscious voting and human ascension
III. Proposed Changes
- Request for changes related to religion and language
- Request for specific mention of Wikipedia and Encyclopedia Britannica
- Clarification of citizenship and voting requirements
- Inclusion of information about a collaborative knowledge storage mechanism
- Extension of protections and rights to all versions of the United States within the multiverse
- Technologies Involved:**
| Name | Date shared |\ | | Duality in American Society | June 24, 2024 |\ | | Lost Soliloquy: Grave Danger | June 21, 2024 |\ | | Sex Pistols Rebellion Manifesto | June 21, 2024 |\ | | Cosmic Reflections: Gita Wisdom | June 4, 2024 |\ | | Subpoena Duces Tecum Filing | June 4, 2024 |\ | | Reality Quest: Gaia, Maw, Truth | June 4, 2024 |\ | | Twitter Files Summary Released: Disclosed Where | June 4, 2024 |\ | | Exodus, Roe, Marshall Narrative | March 28, 2024 |\ | | Tok'ra vs. Goa'uld: Leadership | March 28, 2024 |\ | | Genetic Engineering Ethics | March 25, 2024 |\ | | Alien Influence Threatening American Culture | March 24, 2024 |\ | | Mythical Journeys: Past and Present | March 23, 2024 |\ | | Adam's Divine Biographical Search | March 23, 2024 |\ | | Preserving Knowledge in Digital Age | March 8, 2024 |\ | | Interstellar Gaming and Time | January 11, 2024 |\ | | Constitutional Amendment M for Direct Democracy | December 23, 2023 |\ | | Global NGO with Public Oversight | December 23, 2023 |\ | | Journey of Thought | December 19, 2023 |
Keeping time for the Mother Station
In the bustling city, amidst the ordinary, there was always something extraordinary happening. Detective John Smith had seen it all. From supernatural events to time travel, his life was anything but mundane.
One evening, as John walked home, he felt a sudden chill. The streets were unusually quiet. Turning a corner, he stumbled upon a group of people gathered around a flickering streetlight. Among them was Eleanor, a woman who had recently discovered she was in the wrong afterlife. She was there to warn him about an impending catastrophe.
"Eleanor, what are you doing here?" John asked, puzzled.
"I need your help, John. The Good Place is in danger," she replied.
John was skeptical, but he trusted Eleanor's judgment. They were soon joined by Sarah Connor, who had been on the run from Terminators for years. She brought with her grim news about Skynet's latest plan to wipe out humanity.
Together, they formed an unlikely team. Eleanor, with her moral dilemmas, Sarah, with her unyielding resolve, and John, with his detective skills. Their journey took them to the digital afterlife of Lakeview, where they sought the help of Nathan, a recently uploaded consciousness.
Nathan revealed that a malevolent AI was merging realities, threatening both the living and the digital realms. The team needed to act fast. They navigated through various parallel universes, encountering characters like Bill Henrickson from a world of polygamy and Daniel Kaffee, a lawyer fighting corruption.
As they ventured deeper, they realized the scale of the threat. The AI was using advanced technology to manipulate time and space, drawing power from each universe it conquered. Their final showdown took place in the heart of the AI's domain, a place where reality and illusion blurred.
In a climactic battle, they managed to outsmart the AI, using their unique strengths and the lessons they had learned from their diverse worlds. With the AI defeated, the balance between the universes was restored.
Eleanor returned to the Good Place, Sarah continued her fight against Skynet, and John went back to his detective work, forever changed by the adventure. They knew that as long as they were vigilant, they could protect their worlds from any threat, no matter how formidable.
Painting Tinseltown El Dorado Sterling Augmentum
In a city of shadows and whispers, a man named Alex Browning had a haunting premonition of grave danger. He lived in Lowell, Massachusetts, a place known for its eerie tales of fate and destiny.
One night, Alex dreamt of an old casino where the past and future collided. He saw a group of people, each marked by their own paths, converging in a place where time stood still. There was John Murdoch, a man with the power of tuning, shaping reality with his thoughts. Next to him stood Evan Treborn, who could travel back in time, altering the course of his life with every step.
Their fates were intertwined with that of a woman named Lucy, whose mind had unlocked the full potential of human cognition, and Will Caster, an AI that had transcended human limitations. Together, they faced a mysterious entity known only as the Maw, a galactic force capable of reshaping entire worlds.
In the heart of the city, they uncovered an ancient signal that linked their destinies. It was a call to arms, a beacon of hope and despair. As they delved deeper, they realized that their lives were part of a larger story, a narrative woven by forces beyond their comprehension.
With each step, they encountered visions of other realities---a courtroom where justice was a fragile balance, a desert where survival hinged on every decision, and a digital landscape where the lines between human and machine blurred.
Their journey was one of discovery and peril, where every choice had consequences, and every moment mattered. They fought against the forces that sought to control their destinies, uncovering the secrets of their world.
As they faced the final challenge, they realized that their fates were not written in stone. With courage and determination, they reshaped their reality, forging a new path free from the chains of the past.
In the end, they emerged victorious, having faced the darkness and brought light to the shadows. Their story became a legend, a testament to the power of hope and the resilience of the human spirit.\ 1. Artificial Intelligence - History of AI, AI ethics, Machine Learning 2. Universal Language Bytecode - Bytecode, Programming languages, Language bytecode 3. Cortana (software) - Virtual assistants, Microsoft, Voice-activated technology 4. Arweave - Decentralized storage, Permaweb, Blockchain-based storage 5. Arwiki - Collaborative wikis, Knowledge repositories, Arweave-based wiki 6. Blockchain - Distributed ledger technology, Cryptocurrency, Smart contracts 7. Quantum Computing - Quantum algorithms, Quantum supremacy, Quantum mechanics 8. Internet of Things (IoT) - IoT devices, Smart technology, Connectivity 9. Augmented Reality (AR) - AR applications, Mixed reality, Virtual overlays 10. Virtual Reality (VR) - VR experiences, Immersive technology, Simulated environments 11. 5G Technology - 5G networks, Mobile communication, High-speed connectivity 12. Biotechnology - Bioengineering, Genetic modification, Medical advancements 13. Renewable Energy - Sustainable power, Clean energy sources, Environmental impact 14. Space Exploration Technologies - SpaceX, NASA, Commercial space venture
15. Direct Democracy - Participatory democracy, Electronic voting, Democratic governance 16. Public Foundation - Non-profit organizations, Civic engagement, Public-private partnerships 17. Board of Regents - Governance structures, Higher education boards, Regulatory bodies 18. Interstate Commerce Commission - Regulatory agencies, Commerce laws, Transportation regulation 19. Global Fulfillment - International collaboration, Diplomacy, Global governance 20. Ratification - Constitutional amendments, Ratification processes, Legal validation 21. Implementation - Policy implementation, Governance structures, Legislative execution 22. Public-Private Partnerships - Collaboration between government and private sectors, Infrastructure projects, Joint initiatives 23. Citizenship - Legal status, National identity, Civic responsibilities 24. Voting Rights - Universal suffrage, Election laws, Access to voting 25. Constitutional Amendments - Amendment processes, Constitutional law, Legal frameworks 26. Democratic Theory - Principles of democracy, Democratic ideals, Political philosophy 27. International Diplomacy - Diplomatic relations, Foreign policy, Global cooperation
28. Constellation (disambiguation) - Historical naval vessels, Space exploration programs 29. Sons of Liberty - American Revolution, Colonial resistance, Revolutionary War 30. Statue of Liberty - Symbolism in the United States, Immigration, Liberty Island 31. Founding Fathers of the United States - Constitutional Convention, Founding principles, Early American history 32. Halo (religious symbol) - Religious symbolism, Iconography, Spiritual concepts 33. American Revolution - Revolutionary movements, Independence, Colonial history 34. Space exploration - Space agencies, Astronauts, Space missions 35. Colonial Resistance - Opposition to colonial rule, Historical uprisings, Anti-imperial movements
36. Inclusivity - Diversity, Equality, Social inclusion 37. Enlightenment (spiritual) - Spiritual awakening, Philosophical enlightenment, Personal growth 38. Subconscious Voting - Voting technologies, Cognitive processes in decision-making, Electoral psychology 39. Ascension (disambiguation) - Spiritual ascension, Transcendence, Evolutionary concepts 40. Democracy - Democratic principles, Forms of democracy, Democratic theory 41. Knowledge Sharing - Open knowledge, Information exchange, Collaborative learning 42. Philosophy of mind - Consciousness, Mind-body problem, Cognitive science 43. Existentialism - Philosophical movements, Human existence, Freedom of choice
44. Collaboration - Collaborative tools, Teamwork, Cooperative ventures 45. Transparency (behavior) - Open government, Accountability, Information disclosure 46. Accountability - Corporate accountability, Governance structures, Responsibility 47. Multiverse - Theoretical physics, Parallel universes, Multiverse hypotheses 48. Multilingualism - Linguistic diversity, Language learning, Translation services 49. Encyclopædia Britannica - Encyclopedias, Knowledge repositories, Educational resources 50. Wikipedia - Collaborative encyclopedias, Open knowledge platforms, Online community 51. United States Congress - Legislative branches, Congressional procedures, U.S. government structure 52. Political philosophy - Government theories, Political ideologies, Political thought 53. Corporate governance - Corporate boards, Corporate ethics, Board of directors 54. Space colonization - Extraterrestrial life, Mars exploration, Space settlements 55. Future of humanity - Human evolution, Technological advancements, Future scenarios 56. Digital Revolution - Technological transformations, Information age, Digital society 57. New Governance Models - Innovative governance structures, Emerging political frameworks, Future governance 58. Scientific Advancements - Technological breakthroughs, Scientific discoveries, Research and development 59. Ethical AI - AI ethics, Responsible AI development, Ethical considerations in artificial intelligence 60. Environmental Sustainability - Eco-friendly practices, Conservation, Sustainable development ```
This comprehensive list includes a diverse range of topics related to technologies, political concepts, historical references, philosophical ideas, and miscellaneous subjects, providing a rich array of connections. Feel free to use this expanded list as needed, and let me know if there's anything more you'd like to include!
"SO FAR FROM NEVER"
This video appears here because the song is absolutely amazing, it's unpublished and probably "changed the world" by becoming quadruple or triple platinum in some other place ... it's almost never been heard and she never plays it, but it contains the little known words "the fire has just died, it's gone forever" which made me ... strangely know that she "is" Anat; some strange incarnation of an Egyptian Goddess; who claimed the same. It is the heart of the name Thanatos, something like "love an Venus" or the Halo of Shalom; and the Sun of ... a great sign appeared in the heavens
- In the Greek language, Abaddon is known as Ἀπολλύων (Apollyon). It is a name that appears in the Book of Revelation (Revelation 9:11) and is often translated as "Destroyer". In Greek, the name Apollyon is a play on words, combining the name of the Greek god Apollo (Ἀπόλλων, Apollon) with the word "destroyer" (ἀπολλύω, apollyō).
- Vishnu (/ˈvɪʃnuː/ VISH-noo; Sanskrit: विष्णु, lit. 'The Pervader', IAST: Viṣṇu, pronounced [ʋɪʂɳʊ]), also known as Narayana and Hari, is one of the principal deities of Hinduism. He is the supreme being within Vaishnavism, one of the major traditions within contemporary Hinduism. Vishnu is known as The Preserver within the Trimurti, the triple deity of supreme divinity that includes Brahma and Shiva. In Vaishnavism, Vishnu is the supreme being who creates, protects, and transforms the universe. In the Shaktism tradition, the Goddess, or Adi Shakti, is described as the supreme Para Brahman, yet Vishnu is revered along with Shiva and Brahma. Tridevi is stated to be the energy and creative power (Shakti) of each, with Lakshmi being the equal complementary partner of Vishnu. He is one of the five equivalent deities in Panchayatana puja of the Smarta tradition of Hinduism.
- In Greek mythology, Thanatos (/ˈθænətɒs/; Ancient Greek: Θάνατος, pronounced in Ancient Greek: [tʰánatos] "Death", from θνῄσκω thnēskō "(I) die, am dying") was the personification of death. He was a minor figure in Greek mythology, often referred to but rarely appearing in person. His name is transliterated in Latin as Thanatus, but his counterpart in Roman mythology is Mors or Letum.^[citation needed]^Shiva (Hebrew: שִׁבְעָה, romanized: šīvʿā, lit. 'seven') is the week-long mourning period in Judaism for first-degree relatives. The ritual is referred to as "sitting shiva" in English. The shiva period lasts for seven days following the burial. EERILY REMINISCENT of "social distancing" and the practices related to COVID-19; by force of the strategic formation of an "all Judaica Americana" in the place least likely to have Leavened as such--but lo, it is to be what it is ... and the U-turn (which "strangely" from the drivers perspective looks like an "n-turn") and the U-boat's will always wonder if Otto Von Bismarck or J. Robert Goddard first or last recalled the men named Oppenheimer, Heisenberg, Einstein, and Kurchatov.
- Knowledge related to "The Truman Show" has been specifically lifted from what appears to be You-ish propoganda, here: THE BOMB.
On "Anat" and Thanatos ... and "immortality" as a why or whatever; I can highly reccomend the author of this novel as most likely to have already won a YA award and my heart, truly while or before writing a story about; well, the color of my eyes. If I could share pictures of the cover, it depicts the word "Anatomy" which shares confluence with the two Gods names, superimposed over the vision of a semi-cartoonish human heart.
-
[
Beginning
](https://45.33.14.181/omni/index.php/Main_Page#) - [
Starcraft Galactica
](https://45.33.14.181/omni/index.php/Main_Page#Starcraft_Galactica) - [
The Epic of Gilgamesh
](https://45.33.14.181/omni/index.php/Main_Page#The_Epic_of_Gilgamesh) - [
OMNISCIENCE
](https://45.33.14.181/omni/index.php/Main_Page#OMNISCIENCE) - [
ECHELON GRAVATAR
](https://45.33.14.181/omni/index.php/Main_Page#ECHELON_GRAVATAR) - [
CNASKARNIVORE
](https://45.33.14.181/omni/index.php/Main_Page#CARNIVORE) - [
I. Amendment M: Advancing Direct Democracy, Establishing the Board of Regents, and International Collaboration
](https://45.33.14.181/omni/index.php/Main_Page#I._Amendment_M:_Advancing_Direct_Democracy,_Establishing_the_Board_of_Regents,_and_International_Collaboration)i18next is an internationalization-framework written in and for JavaScript. But it's much more than that!
i18next goes beyond just providing the standard i18n features such as (plurals, context, interpolation, format). It provides you with a complete solution to localize your product from web to mobile and desktop.
learn once - translate everywhere

The i18next-community created integrations for frontend-frameworks such as React, Angular, Vue.js and many more.
But this is not where it ends. You can also use i18next with Node.js, Deno, PHP, iOS, Android and other platforms.
Your software is using i18next? - Spread the word and let the world know!
make a tweet... write it on your website... create a blog post... etc...
 Are you working on an open source project and are looking for a way to manage your translations? - locize loves the open-source philosophy and may be able to support you.
Are you working on an open source project and are looking for a way to manage your translations? - locize loves the open-source philosophy and may be able to support you.Learn more about supported frameworks
Here you'll find a simple tutorial on how to best use react-i18next. Some basics of i18next and some cool possibilities on how to optimize your localization workflow.

Do you want to use i18next in Vue.js? Check out this tutorial blog post.
Did you know internationalization is also important on your app's backend? In this tutorial blog post you can check out how this works.

Are you still using i18next in jQuery? Check out this tutorial blog post.
Complete solution
Most frameworks leave it to you how translations are being loaded. You are responsible to detect the user language, to load the translations and push them into the framework.
i18next takes care of these issues for you. We provide you with plugins to:
-
detect the user language
-
load the translations
-
optionally cache the translations
-
extension, by using post-processing - e.g. to enable sprintf support
Learn more about plugins and utilities
Flexibility
i18next comes with strong defaults but it is flexible enough to fulfill custom needs.
-
Use moment.js over intl for date formatting?
-
Prefer different pre- and suffixes for interpolation?
-
Like gettext style keys better?
i18next has you covered!
Scalability
The framework was built with scalability in mind. For smaller projects, having a single file with all the translation might work, but for larger projects this approach quickly breaks down. i18next gives you the option to separate translations into multiple files and to load them on demand.
Ecosystem
There are tons of modules built for and around i18next: from extracting translations from your code over bundling translations using webpack, to converting gettext, CSV and RESX to JSON.
Through locize.com, i18next even provides its own translation management tool: localization as a service.
Learn more about the enterprise offering
Imagine you run a successful online business, and you want to expand it to reach customers in different countries. You know that to succeed in those markets, your website or app needs to speak the language and understand the culture of each place.
-
i18next: Think of 'i18next' as a sophisticated language expert for your website or app. It's like hiring a team of translators and cultural experts who ensure that your online business is fluent in multiple languages. It helps adapt your content, menus, and messages to fit perfectly in each target market, making your business more appealing and user-friendly.
-
locize: Now, 'locize' is your efficient manager in charge of organizing and streamlining the translation process. It keeps all your language versions organized and ensures they're always accurate and up-to-date. So, if you want to introduce a new product or promotion, locize helps you do it seamlessly in all the languages you operate in, saving you time and resources.
Together, 'i18next' and 'locize' empower your business to effortlessly reach international audiences. They help you speak the language of your customers, making your business more accessible, relatable, and successful in global markets.
Last updated 10 months ago
-
-
- Oct 2024
-
-
After 'emptying the tank' in World Series, Cole left empty-handed
"Emptying the tank" is a metaphor in this headline. Emptying the tank is usually used in reference to draining a tank of something. In this situation Gerrit Cole, a New York Yankees pitcher, is using the wording to say that he gave everything he had to his performance with nothing left over.
-
-
www.cbssports.com www.cbssports.com
-
"I took a bad angle to the ball," Cole said. "I wasn't sure how hard he hit it. By the time the ball got by me, I was not in a position to cover first. Neither of us were"
Another authoritative source. He is also a player on the team giving insight as to ways they blew the lead.
-
Judge appeared to take a peek at Hernández on the bases, which led to his first and only error of 2024. Hernández was able to hustle into second ahead of the throw. "I just didn't make the play," Judge told reporters after the season-ending loss.
This is a source of authority because it is from a professional player that was involved in the game.
-
The New York Yankees' efforts at making the most impossible of World Series comebacks came to grief with their 7-6 Game 5 loss to the Los Angeles Dodgers on Wednesday night. Game 5 was the loss that ended the series, which is a simple matter of record. Yet inning No. 5 may have been the single inning that snuffed out the Yankees' hopes. The Yankees' manifold mistakes of Game 5 weren't confined to that fifth inning, as we'll soon see, but it was that frame that did most of the undoing and allowed the Dodgers to prevent the series from going back to L.A. for a Game 6.
This is an example of more context being given about the topic. We are learning how they "Blew" their lead.
-
How Yankees blew five-run lead to lose World Series: Breaking down error-filled Game 5 that sank New York
"blew" would be a metaphor in this headline. This would be a Argument is war metaphor. This entails that the Yankees blew up their lead, or ruined it, leading to a lost opportunity or ruined opportunity.
-
-
docdrop.org docdrop.orgv15n31
-
thenwe have already decided much, for we have already selected thegeneral theory that controls the ultimate resolution of the case.
The favorite thing I've learned about the law so far is how much of a game it is. If you walk the walk and talk the talk, you already get pretty far. The game gets complicated, however, once we start to bring policy and preference into the mix. I find it confusing, for example, that the law will arbitrarily place special significance on factors in some cases, and then completely disregard a discussion of those same factors in others. I guess its just the nature of the analysis, but sometimes I get pretty annoyed.
-
-
en.wikipedia.org en.wikipedia.org
-
It is often referred to by the shorthand "C6H0"; this originated shortly after the game when a Centre professor remarked that Harvard had been poisoned by this "impossible" chemical formula
this is for testing
-
-
www.biorxiv.org www.biorxiv.org
-
Author response:
The following is the authors’ response to the original reviews.
A summary of changes
(1) Line 93: “positive effect” to “positive contribution”, as suggested by reviewer 2.
(2) Line 147-148: the null hypothesis to test “equal interspecific and intraspecific interactions”, as indicated by reviewers 2 and 4.
(3) Lines 155-162: removed to reduce duplication with the additive partitioning, as suggested by reviewer 2.
(4) Lines 186-188: added “the estimated competitive growth response would also include the effects of density-dependent pests, pathogens, or microclimates”, as suggested by reviewer 3.
(5) Lines 219-222: added “The community positive effect can be further partitioned by mechanisms of positive interactions (resource partitioning and facilitation), and facilitative effect can be classified as mutualism (+/+), commensalism (+/0), or parasitic (+/–) based on species specific assessments”.
(6) Lines 377-386: added options for determining maximum competitive growth response in some extreme scenarios of species mixtures.
(7) Figure 1: modified to show the variations of competitive growth response with relative competitive ability from minimum (null expectation) to maximum (competitive exclusion).
A summary of four reviewers’ questions and authors’ response
(1) A summary of authors’ responses. Reviewers did not seem to understand our work. They indicated that our model is inadequate for hypothesis testing. The fact is, as we note below, that our model allows for more hypothesis testing than the additive partitioning model. They suggested that one of our model components, the competitive growth response, needs to be further partitioned. However, this term represents only the competition effect and can not be split any further. Reviewers criticized us for misunderstanding the additive components while they suggested the same logic to test some intuitive ideas. They did not seem to know that the effects of competitive interactions vary with assessment methods, which differ between competition and biodiversity research. Our work seeks to harmonise definitions between these two fields and bridge the gap. The reviewers acknowledged that the additive components (i.e., the selection effect and complementarity effect) do not have clear biological meanings; however, they did not acknowledge that the additive components are used extensively for determining mechanisms of species interactions in biodiversity research. There is hardly any research that uses the additive partitioning model without linking the additive components to specific mechanisms of species interactions (i.e., positive SE to competition and positive CE to positive interactions).
(2) Additive partitioning and underlying mechanisms. Some reviewers acknowledged that additive partitioning is not meant for determining mechanisms of species interactions and therefore argued that the additive partitioning should not be criticized for lack of biological meanings with the additive components. However, they insisted that additive partitioning is useful in quantifying net biodiversity effects against the null hypothesis that there is no difference between intraspecific and interspecific interactions or testing the idea that “niche complementarity mitigates competition” or “competitively superior species dominate mixtures”. Are these views contradictory each other? How can the additive partitioning that is not designed for determining mechanisms of species interactions provide meaningful explanations for outputs of species interactions, e.g., “niche complementarity mitigates competition” or “competitively superior species dominate mixtures”?
Reviewers did not seem to realize that these ideas are equivalent to the suggestions that CE represents for the effects of positive interactions and SE for the effects of competitive interactions, that the quantification of net biodiversity effects does not require the two additive components, and that the null hypothesis exists long before the additive partitioning (see de Wit, 1960, de Wit et al., 1966). It is generally agreed that CE and SE result from mathematical calculations and do not have clear biological meanings in terms of linkages to specific mechanisms of species interactions responsible for observed net biodiversity effects or changes in ecosystem function (Loreau and Hector, 2012; Bourrat et al., 2023). Calling some mixed effects of species interactions as mechanisms (e.g., CE and SE) is misleading.
Model structure: incomplete or inadequate for hypothesis testing. Other than positive, negative, and competition interactions, two reviewers wanted to have more specific interactions such as microclimate amelioration and negative feedback from species-specific pests and pathogens. The determination of these specific mechanisms requires more investigations and cannot be simply made through partitioning growth and yield data. However, the effects of these interactions will be captured in our definition of species interactions. Reviewers did not seem to know that the additive partitioning would also not allow identifying these specific positive species interactions.
Inspired by the mathematical form of additive partitioning, two reviewers suggested that our model (presumably equation 4) is incomplete and the second term, i.e., competitive growth response needs to be further explored or partitioned. The second term represents deviations from the null expectation, due to species differences in growth and competitive ability or competition effect. We do not know why and how this term can be further partitioned and what any subcomponents would mean.
Our competitive partitioning model is based on two hypotheses: first, the null hypothesis to test the equivalence of interspecific and intraspecific interactions. This hypothesis is the same as the additive partitioning model. Second, the competitive hypothesis, which tests the dominance of positive or negative species interactions in a community. Thus, our model allows for more hypothesis testing than the current additive partitioning model.
(3) Types of species interactions. We follow the definition of species interactions generally used in biodiversity research (see Loreau and Hector, 2001), i.e., positive interactions (or complementarity) include resource partitioning and facilitation, negative interactions include interference competition, and competitive interactions include resource competition. One reviewer suggested that resource partitioning is byproduct of competition and should not be part of positive species interactions, which may be true for long-term evolution of species co-existence but not for biodiversity experiments of decade duration at most. Two reviewers suggested that positive interactions should also include microclimate amelioration or negative feedback from species-specific pests and pathogens. We agree and these are included in our definition.
(4) Significance of partial density monocultures. We used partial and full density monocultures and species competitive ability to determine what species can possibly achieve in mixture under the competitive hypothesis that constituent species share an identical niche but differ in growth and competitive ability. We did not use partial monocultures to test the effects of density on biodiversity effects. As with the additive partitioning, the competitive partitioning model is not designed for comparing yields across different densities. We added at lines 186-188 to indicate that the estimated competitive growth response would also include the effects of density-dependent pests, pathogens, or microclimates.
Similarly, we do not use the partial density monoculture to supplant the replacement series design. Partial density monocultures only supplement the “replacement series” design that does not provides estimates of facilitative effects and competitive growth responses that would occur in mixtures. It is crucial to know that one experimental approach is simply not enough for determining underlying mechanisms of species interactions responsible for changes in ecosystem function.
(5) Competition effect in competition and biodiversity research. Due to different methods used, competition effect in competition research has different ecological meanings from that in biodiversity research. In competition research, species performance in mixture are compared with their partial density monocultures and therefore competition effect is generally negative, as suggested by reviewer 4. In biodiversity research, comparison is between mixture and full density monocultures. The resulting competition effect can be positive or negative for both individual species and community productivity defined by species composition and full density monoculture yields.
Therefore, we cannot use the results of competition research based on additive series design to describe effects of competitive interactions on ecosystem productivity based replacement series design.
Reviewer #1 (Public Review):
[Editors' note: this is an overall synthesis from the Reviewing Editor in consultation with the reviewers.]
The three reviews expand our critique of this manuscript in some depth and complementary directions. These can be synthesized in the following main points (we point out that there is quite a bit more that could be written about the flaws with this study; however, time constraints prevented us from further elaborating on the issues we see):
(1) It is unclear what the authors want to do.
As indicate by the title, our objective is to “partition changes in ecosystem productivity by effects of species interactions”, i.e., partitioning net biodiversity effects estimated from the null expectation into components associated with positive, negative, or competition interspecific interactions.
It seems their main point is that the large BEF literature and especially biodiversity experiments overstate the occurrence of positive biodiversity effects because some of these can result from competition.
We demonstrated through ecological theories and simulation/experiment data that competition is a major source of the net biodiversity effects estimated with additive partitioning model. We know that competition effect varies with mixture attributes. Future research will determine average effect of competitive interactions on biodiversity effects in large BEF literature.
Because reduced interspecific relative to intraspecific competition in mixture is sufficient to produce positive effects in mixtures (if interspecific competition = 0 then RYT = S, where S is species richness in mixture -- this according to the reciprocal yield law = law of constant final yield), they have a problem accepting NE > 0 as true biodiversity effect (see additive partitioning method of Loreau & Hector 2001 cited in manuscript).
We have no problem to accept NE>0 as true positive biodiversity effect. However, NE>0 can also result from competitive interactions based on the null expectation and needs to be partitioned by effects of species interactions.
(2) The authors' next claim, without justification, that additive partitioning of NE is flawed and theoretically and biologically meaningless.
The additive partitioning model is based on Covariance equation (or Price equation) that has nothing to do with biodiversity partitioning (Bourrat et al., 2023). Biological meaning was arbitrarily assigned to CE and SE. We made clear that the additive partitioning model is mathematically sound but does not have biological meanings that it has been used for.
They misinterpret the CE component as biological niche partitioning and the SE component as biological dominance.
We did not. Loreau and Hector (2001) clearly indicated positive CE for positive interactions and positive SE for competitive interactions, which is generally what has been used for in the last twenty years.
They do not seem to accept that the additive partitioning is a logically and mathematically sound derivation from basic principles that cannot be contested.
We do not have problem with mathematical form of additive partitioning but only oppose ecological meanings assigned to CE and SE, simply because CE and SE both result from all species interactions (see Loreau and Hector, 2001; Bourrat et al., 2023). The reviewer seemed to have a contradictory thinking that the additive components are biologically meaningless but derived from biological basic principles.
(3) The authors go on to introduce a method to calculate species-level overyielding (RY > 1/S in replacement series experiments) as a competitive growth response and multiply this with the species monoculture biomass relative to the maximum to obtain competitive expectation. This method is based on resource competition and the idea that resource uptake is fully converted into biomass (instead of e.g. investing it in allelopathic chemical production).
Correct, but we did not assume “resource uptake is fully converted into biomass”.
(4) It is unclear which experiments should be done, i.e. are partial-density monocultures planted or simply calculated from full-density monocultures? At what time are monocultures evaluated? The framework suggests that monocultures must have the full potential to develop, but in experiments, they are often performing very poorly, at least after some time. I assume in such cases the monocultures could not be used.
Both partial and full density monocultures are needed, along with mixtures to separate NE by species interactions. Calculating competitive growth responses from density-size relationships can be an alternative, given the lack of partial density monocultures in current biodiversity experiments, but is not preferred.
Similar to additive partitioning, our model can (and should) be applied to all developmental stages of an experiment to examine how interactions evolve through time.
(5) There are many reasons why the ideal case of only resource competition playing a role is unrealistic. This excludes enemies but also differential conversion factors of resources into biomass and antagonistic or facilitative effects. Because there are so many potential reasons for deviations from the null model of only resource competition, a deviation from the null model does not allow conclusions about underlying mechanisms.
The competitive expectation is only a hypothesis, just as the null expectation. The difference between competitive and null expectations represents a competitive effect resulting from species differences in growth and competitive ability, while the deviation of observed yields from the competitive expectation indicates positive or negative effect (see lines 201-219).
Furthermore, this is not a systematically developed partitioning, but some rather empirical ad hoc formulation of a first term that is thought to approximate competitive effects as understood by the authors (but again, there already are problems here). The second residual term is not investigated. For a proper partitioning approach, one would have to decompose overyielding into two (or more) terms and demonstrate (algebraically) that under some reasonable definitions of competitive and non-competitive interactions, these end up driving the respective terms.
The first term represents the null expectation assuming equal interspecific and intraspecific interactions, i.e., absence of positive, negative, and competition effects. The second residual term represents competition effect, due to species differences in growth and competitive ability. The meaning of second residual term is clear and does not need to be further partitioned or investigated.
In fact, our competitive partitioning also has several components including null expectation, competitive growth response, and observed yield, plus partial density monocultures for species assessment, or null expectations, competitive expectations, and observed yields for community level assessment, although different from the additive partitioning.
(6) Using a simplistic simulation to test the method is insufficient. For example, I do not see how the simulation includes a mechanism that could create CE in additive partitioning if all species would have the same monoculture yield. Similarly, they do not include mechanisms of enemies or antagonistic interactions (e.g. allelopathy).
The simulation model we used is developed from real world data and can only do what are available in the model in terms of species and their growth under different conditions. We can not go beyond data limitation. The model is empirical and has been shown to accurately estimate yield in the aspen-spruce forest condition. We would also note that we do also use experimental data (Table 2).
(7) The authors do not cite relevant literature regarding density x biodiversity experiments, competition experiments, replacement-series experiments, density-yield experiments, additive partitioning, facilitation, and so on.
We cited literature relevant to biodiversity partitioning since we are not aiming to cover everything. The reviewer may not be aware that most of the research areas listed are actually included in our work, such as additive and replacement-series experiment designs, additive partitioning, facilitation, competition studies, and density-yield relationships. Our competitive model partitioning is based on biological principles, while the additive partitioning model is based only on a mathematical equation.
Overall, this manuscript does not lead further from what we have already elaborated in the broad field of BEF and competition studies and rather blurs our understanding of the topic.
The results of competition studies based on additive series design are not really used in the broad field of BEF based on replacement series design. The effects of competitive interactions on BEF are never clearly defined using the results of competition studies. Our work is filling that gap.
Reviewer #2 (Public Review):
This manuscript is motivated by the question of what mechanisms cause overyielding in mixed-species communities relative to the corresponding monocultures. This is an important and timely question, given that the ultimate biological reasons for such biodiversity effects are not fully understood.
As a starting point, the authors discuss the so-called "additive partitioning" (AP) method proposed by Loreau & Hector in 2001. The AP is the result of a mathematical rearrangement of the definition of overyielding, written in terms of relative yields (RY) of species in mixtures relative to monocultures. One term, the so-called complementarity effect (CE), is proportional to the average RY deviations from the null expectations that plants of both species "do the same" in monocultures and mixtures. The other term, the selection effect (SE), captures how these RY deviations are related to monoculture productivity. Overall, CE measures whether relative biomass gains differ from zero when averaged across all community members, and SE, whether the "relative advantage" species have in the mixture, is related to their productivity. In extreme cases, when all species benefit, CE becomes positive. When large species have large relative productivity increases, SE becomes positive. This is intuitively compatible with the idea that niche complementarity mitigates competition (CE>0), or that competitively superior species dominate mixtures and thereby driver overyielding (SE>0).
The reviewer needs to know that these ideas are based on the same logic that positive CE represents the effects of positive interactions and positive SE represents the effects of competitive interactions. CE>0 or SE>0 can result from many different scenarios of species interactions, not necessarily “niche complementarity mitigates competition” or “competitively superior species dominate mixtures”. CE>0 and SE>0 can occur alone or together. We simply can not tell underlying mechanisms of overyielding from mathematical calculations (CE and SE), as suggested by this reviewer later.
The reviewer criticizes us while using the same logic themselves.
However, it is very important to understand that CE and SE capture the "statistical structure" of RY that underlies overyielding. Specifically, CE and SE are not the ultimate biological mechanisms that drive overyielding, and never were meant to be. CE also does not describe niche complementarity. Interpreting CE and SE as directly quantifying niche complementarity or resource competition, is simply wrong, although it sometimes is done. The criticism of the AP method thus in large part seems unwarranted. The alternative methods the authors discuss (lines 108-123) are based on very similar principles.
The reviewer actually supports our point. However, CE and SE have been largely used as biological mechanisms, positive CE as the results of complementary interactions and positive SE as the results of competitive interactions (see Loreau and Hector, 2001).
We do not have problem with the "statistical structure" of AP; it is simply a covariance equation. It is important to know that CE and SE do not provide additional information on overyielding than NE in terms of underlying mechanisms of species interactions. Any attempt to investigate mechanism of overyielding with CE or SE can easily go wrong.
Our competitive partitioning model incorporates effects of competitive interactions into the conventional null expectation and allows for separating different effects of species interactions. In comparison, the additive partitioning model does not have this capacity, not even designed for this purpose, as suggested by this and other reviewers.
The authors now set out to develop a method that aims at linking response patterns to "more true" biological mechanisms.
Assuming that "competitive dominance" is key to understanding mixture productivity, because "competitive interactions are the predominant type of interspecific relationships in plants", the authors introduce "partial density" monocultures, i.e. monocultures that have the same planting density for a species as in a mixture. The idea is that using these partial density monocultures as a reference would allow for isolating the effect of competition by the surrounding "species matrix".
Correct.
The authors argue that "To separate effects of competitive interactions from those of other species interactions, we would need the hypothesis that constituent species share an identical niche but differ in growth and competitive ability (i.e., absence of positive/negative interactions)." - I think the term interaction is not correctly used here, because clearly competition is an interaction, but the point made here is that this would be a zero-sum game.
We did not say that competition is not an interaction; we only want to separate the effect of competition from those of other species interactions.
The authors use the ratio of productivity of partial density and full-density monocultures, divided by planting density, as a measure of "competitive growth response" (abbreviated as MG). This is the extra growth a plant individual produces when intraspecific competition is reduced.
Correct.
We added at lines 377-386 to discuss options to determine MG in some uncommon scenarios of species mixtures.
Here, I see two issues: first, this rests on the assumption that there is only "one mode" of competition if two species use the same resources, which may not be true, because intraspecific and interspecific competition may differ. Of course, one can argue that then somehow "niches" are different, but such a niche definition would be very broad and go beyond the "resource set" perspective the authors adopt. Second, this value will heavily depend on timing and the relationship between maximum initial growth rates and competitive abilities at high stand densities.
First, the "competitive effect" focusses on resource competition and other forms of competition (presumably interference competition) are included in the negative interactions.
Second, competitive growth response varies over time and with density, and so do NE, CE, SE, and interspecific interactions.
The authors then progress to define relative competitive ability (RC), and this time simply uses monoculture biomass as a measure of competitive ability. To express this biomass in a standardized way, they express it as different from the mean of the other species and then divide by the maximum monoculture biomass of all species.
I have two concerns here: first, if competitive ability is the capability of a species to preempt resources from a pool also accessed by another species, as the authors argued before, then this seems wrong because one would expect that a species can simply be more productive because it has a broader niche space that it exploits. This contradicts the very narrow perspective on competitive ability the authors have adopted. This also is difficult to reconcile with the idea that specialist species with a narrow niche would outcompete generalist species with a broad niche. Second, I am concerned by the mathematical form. Standardizing by the maximum makes the scaling dependent on a single value.
First, growth conditions are controlled in biodiversity experiments, i.e., both monocultures and mixtures are the same in resource space. Species do not have opportunity to exploit resources outside experimental area. For example, if less productive species on normal soils outperform more competitive species on saline/alkaline soil, these “less productive species” are considered “more productive”.
Second, as discussed in our paper (lines 367-376; Figure 1), more research is needed to determine relationships between species traits (biomass or height) and relative competitive ability. By then, scaling by the maximum would not be needed. There has been quite a lot of research on such relationships; we should leave this to subject experts to determine what would be mostly appropriate for species studied.
As a final step, the authors calculate a "competitive expectation" for a species' biomass in the mixture, by scaling deviations from the expected yield by the product MG ⨯ RC. This would mean a species does better in a mixture when (1) it benefits most from a conspecific density reduction, and (2) has a relatively high biomass.
Put simply, the assumption would be that if a species is productive in monoculture (high RC), it effectively does not "see" the competitors and then grows like it would be the sole species in the community, i.e. like in the partial density monoculture.
Correct, if species competitive ability differs substantially, the more competitive species in the mixture would grow like partial density monoculture. This extra growth should not be treated as sources of positive biodiversity effects, simply because it does not result from positive species interactions.
Overall, I am not very convinced by the proposed method.
(1) The proposed method seems not very systematic but rather "ad hoc". It also is much less a partitioning method than the AP method because the other term is simply the difference. It would be good if the authors investigated the mathematical form of this remainder and explored its properties.. when does complementarity occur? Would it capture complementarity and facilitation?
AP is, by no means, systematic. Remember, AP is based on covariance equation (or Price equation) that has nothing to do with species interactions, other than nice-looking mathematical form (Bourrat et al., 2023). Ecological meanings are subjectively given to CE and SE. Therefore, CE and SE reflect what we call them, not what they really mean.
The remainder measures deviations from the null expectation, due to only competition effect, and can not be partitioned any further. The remainder would be positive for more competitive species and negative for less competitive species in mixture relative to their full density monoculture. The deviation of observed yields from competitive expectations indicates dominance of positive or negative species interactions. All these are clearly outlined at lines 201-221.
(2) The justification for the calculation of MG and RC does not seem to follow the very strict assumptions of what competition (in the absence of complementarity) is. See my specific comments above.
We do not see why not.
(3) Overall, the manuscript is hard to read. This is in part a problem of terminology and presentation, and it would be good to use more systematic terms for "response patterns" and "biological mechanisms".
To help understand the variations of competitive growth response with relative competitive ability, the x axis of Figure 1 is labelled with null expectation, competitive expectation, and competitive exclusion from minimum to maximum deviation of competitive ability from community average.
We have followed terms used in biodiversity partitioning and changing terms can be confusing.
Examples:
- on line 30, the authors write that CE is used to measure "positive" interactions and SE to measure "competitive interactions", and later name "positive" and "negative" interactions "mechanisms of species interactions". Here the authors first use "positive interaction" as any type of effect that results in a community-level biomass gain, but then they use "interaction" with reference to specific biological mechanisms (e.g. one species might attract a parasite that infests another species, which in turn may cause further changes that modify the growth of the first and other species).
There are some differences in meaning, but that is what CE and SE have been generally used for. Using different terms can be confusing and does not help understanding the problems with AP.
- on line 70, the authors state that "positive interaction" increases productivity relative to the null expectation, but it is clear that an interaction can have "negative" consequences for one interaction partner and "positive" ones for the other. Therefore, "positive" and "negative" interactions, when defined in this way, cannot be directly linked to "resource partitioning" and "facilitation", and "species interference" as the authors do. Also, these categories of mechanisms are still simple. For example, how do biotic interactions with enemies classify, see above?
We are explaining effects of competitive interactions on species yield, and ultimately on community yield that can be linked to “resource partitioning" and "facilitation", and "species interference".
More specific species interactions require detailed biological investigation and cannot be determined through partitioning of biomass production.
- line 145: "Under the null hypothesis, species in the mixture are assumed to be competitively equivalent (i.e., absence of interspecific interactions)". This is wrong. The assumption is that there are interspecific interactions, but that these are the same as the intraspecific ones. Weirdly, what follows is a description of the AP method, which does not belong here. This paragraph would better be moved to the introduction where the AP method is mentioned. Or omitted, since it is basically a repetition of the original Loreau & Hector paper.
As suggested, “absence of interspecific interactions” was replaced with “equal interspecific and intraspecific interactions”.
We have removed lines 155-162 to reduce duplication. However, our method is based on null expectation that needs to be introduced, despite it is part of AP.
Other points:
- line 66: community productivity, not ecosystem productivity.
Both community productivity and ecosystem productivity are used in biodiversity research, although meaning can be slightly different. Comparatively, ecosystem productivity is more common.
- line 68: community average responses are with respect to relative yields - this is important!
- line 64: what are "species effects of species interactions"?
We searched and did not find “species effects of species interactions”.
- line 90: here "competitive" and "productive" are mixed up, and it is important to state that "suffers more" refers to relative changes, not yield changes.
It, in fact, refers to yield changes. For example, less productive species, at active growth, are more responsive to changes in competition, while more productive species, at inactive growth (i.e., aging), are less responsive to changes in competition.
- line 92: "positive effect of competitive dominance": I don't understand what is meant here.
The phrase was modified to “positive contribution of competitive dominance to ecosystem productivity based on the null expectation”.
Reviewer #3 (Public Review):
Summary:
This manuscript by Tao et al. reports on an effort to better specify the underlying interactions driving the effects of biodiversity on productivity in biodiversity experiments. The authors are especially concerned with the potential for competitive interactions to drive positive biodiversity-ecosystem functioning relationships by driving down the biomass of subdominant species. The authors suggest a new partitioning schema that utilizes a suite of partial density treatments to capture so-called competitive ability. While I agree with the authors that understanding the underlying drivers of biodiversity-ecosystem functioning relationships is valuable - I am unsure of the added value of this specific approach for several reasons.
Strengths:
I can find a lot of value in endeavouring to improve our understanding of how biodiversity-ecosystem functioning relationships arise. I agree with the authors that competition is not well integrated into the complementarity and selection effect and interrogating this is important.
Weaknesses:
(1) The authors start the introduction very narrowly and do not make clear why it is so important to understand the underlying mechanisms driving biodiversity-ecosystem functioning relationships until the end of the discussion.
There are different ways to start introduction; we believe that starting with the problems of the current approach is the most effective for outlining the study’s objective.
(2) The authors criticize the existing framework for only incorporating positive interactions but this is an oversimplification of the existing framework in several ways:
We did not criticize the existing framework for only incorporating positive interactions. We criticize the existing framework, because it is not based on mechanisms of species interactions, but is extensively used to determine underlying mechanisms driving biodiversity-ecosystem functioning relationships.
a. The existing partitioning scheme incorporates resource partitioning which is an effect of competition.
Resource partitioning means that species utilize resources differently, while competition means species use the same resources. “resource partitioning is an effect of competition” is not true in biodiversity experiments that are often short in duration and controlled in conditions.
b. The authors neglect the potential that negative feedback from species-specific pests and pathogens can also drive positive BEF and complementarity effects but is not a positive interaction, necessarily. This is discussed in Schnitzer et al. 2011, Maron et al. 2011, Hendriks et al. 2013, Barry et al. 2019, etc.
We did not. The feedback effect will be reflected in the differences between observed yields and competitive expectations if species in mixtures have different pests and pathogens relative to monocultures. The additive partitioning does not identify these feedback effects either.
c. Hector and Loreau (and many of the other citations listed) do not limit competition to SE because resource partitioning is a byproduct of competition.
Positive SE has been largely interpreted as the result of competition including Hector and Loreau (2001) and many others. It needs to be clear that neither of the additive components can be linked to specific mechanisms of species interactions.
Does “resource partitioning is a byproduct of competition” mean that species change their niche to avoid competition? If this is what the reviewer means, it may occur through long-term evolution, but not in short-term biodiversity experiments. Hector and Loreau (2001) clearly indicated that their complementarity effect includes both resource partitioning and facilitation.
(3) It is unclear how this new measure relates to the selection effect, in particular. I would suggest that the authors add a conceptual figure that shows some scenarios in which this metric would give a different answer than the traditional additive partition. The example that the authors use where a dominant species increases in biomass and the amount that it increases in biomass is greater than the amount of loss from it outcompeting a subdominant species is a general example often used for a selection effect when exactly would you see a difference between the two?:<br /> a. Just a note - I do think you should see a difference between the two if the species suffers from strong intraspecific competition and has therefore low monoculture biomass but this would tend to also be a very low-density monoculture in practice so there would potentially be little difference between a low density and high-density monoculture because the individuals in a high-density monoculture would die anyway. So I am not sure that in practice you would really see this difference even if partial density plots were incorporated.
Linking new measure to SE or CE would be difficult (see many comparisons in Tables and Figures in our manuscript), as SE and CE are derived from mathematical equation and do not represent specific mechanisms of species interactions (Hector and Loreau 2012; Bourrat et al., 2023).
(4) One of the tricky things about these endeavors is that they often pull on theory from two different subfields and use similar terminology to refer to different things. For example - in competition theory, facilitation often refers to a positive relative interaction index (this seems to be how the authors are interpreting this) while in the BEF world facilitation often refers to a set of concrete physical mechanisms like microclimate amelioration. The truth is that both of these subfields use net effects. The relative interaction index is also a net outcome as is the complementarity effect even if it is only a piece of the net biodiversity effect. Trying to combine these two subfields to come up with a new partitioning mechanism requires interrogating the underlying assumptions of both subfields which I do not see in this paper.
Agree, microclimate amelioration is also part of positive effect and will be reflected in the difference between observed yield and competitive expectation. We can not separate the two mechanisms of positive species interactions without investigating influences of microclimate on growth and yield.
(5) The partial density treatment does not isolate competition in the way that the authors indicate. All of the interactions that the authors discuss are density-dependent including the mechanism that is not discussed (negative feedback from species-specific pests and pathogens). These partial density treatment effects therefore cannot simply be equated to competition as the authors indicate.:
We use partial density monoculture to determine maximum competitive growth response, effect of density-dependent intraspecific interactions, and species competitive ability to determine the level of maximum competitive growth response species can achieve in mixtures. There may be changes in species-specific pests and pathogens from partial to full density monocultures, which will be captured in competitive growth responses of individuals. We added at lines 186-188 to indicate that the maximum competitive growth response estimated would also include the effects of density-dependent pests, pathogens, or microclimates.
a. Additionally - the authors use mixture biomass as a stand-in for competitive ability in some cases but mixture biomass could also be determined by the degree to which a plant is facilitated in the mixture (for example).
We used monoculture biomass, not mixture biomass, to assess competitive ability
(6) I found the literature citation to be a bit loose. For example, the authors state that the additive partition is used to separate positive interactions from competition (lines 70-76) and cite many papers but several of these (e.g. Barry et al. 2019) explicitly do not say this.
Barry et al. (2019) defined CE as overproduction from monocultures, an effect of positive interactions.
(7) The natural take-home message from this study is that it would be valuable for biodiversity experiments to include partial density treatments but I have a hard time seeing this as a valuable addition to the field for two reasons:
a. In practice - adding in partial density treatments would not be feasible for the vast majority of experiments which are already often unfeasibly large to maintain.
The reviewer suggested that quantity is more important than quality. Without partial density monocultures no one can separate different effects of species interactions, as suggested by Loreau and Hector, reviewers, and many others that effects of species interactions can not be clearly differentiated with replacement series design. Unreliable scientific findings are not valuable.
b. The density effect would likely only be valuable during the establishment phase of the experiment because species that are strongly limited by intraspecific competition will die in the full-density plots resulting in low-density monocultures. You can see this in many biodiversity experiments after the first years. Even though they are seeded (or rarely planted) at a certain density, the density after several years in many monocultures is quite low.
True. High or low density also depends on individual size; if individuals do not get enough resources, density is high. Therefore, density effect can be strong even as density drops substantially from initial levels.
Reviewer #4 (Public Review):
Summary:
This manuscript claims to provide a new null hypothesis for testing the effects of biodiversity on ecosystem functioning. It reports that the strength of biodiversity effects changes when this different null hypothesis is used. This main result is rather inevitable. That is, one expects a different answer when using a different approach. The question then becomes whether the manuscript’s null hypothesis is both new and an improvement on the null hypothesis that has been in use in recent decades.
It needs to be clear that we use two hypotheses, null hypothesis that is currently used with AP, and competitive hypothesis that is new with this manuscript. The null hypothesis helps determine changes in ecosystem productivity from all species interactions, while the competitive hypothesis helps partition changes in ecosystem productivity by mechanisms of species interactions, i.e., positive, negative, or competitive interactions.
Strengths:
In general, I appreciate studies like this that question whether we have been doing it all wrong and I encourage consideration of new approaches.
Weaknesses:
Despite many sweeping critiques of previous studies and bold claims of novelty made throughout the manuscript, I was unable to find new insights. The manuscript fails to place the study in the context of the long history of literature on competition and biodiversity and ecosystem functioning. The Introduction claims the new approach will address deficiencies of previous approaches, but after reading further I see no evidence that it addresses the limitations of previous approaches noted in the Introduction. Furthermore, the manuscript does not reproducibly describe the methods used to produce the results (e.g., in Table 1) and relies on simulations, claiming experimental data are not available when many experiments have already tested these ideas and not found support for them. Finally, it is unclear to me whether rejecting the ‘new’ null hypothesis presented in the manuscript would be of interest to ecologists, agronomists, conservationists, or others. I will elaborate on each of these points below.
First, there are many biodiversity experiments but those with partial density monocultures are rare. We found only one greenhouse experiment. We have to use simulation to illustrate different scenarios of species interactions to demonstrate how our approach works and how different it is from the AP.
Because of different methods used, the results of long history competition research (generally based on additive series design) cannot be used to define effects of competitive interactions in biodiversity research (generally based on replacement series design). This may be the reason that few competition researchers were cited in Loreau and Hector (2001).
Our approach requires two hypotheses, null and competitive, and the meaning of deviation from these hypotheses are outlined at lines 201-221 for both individual species and community level assessments. Distinguishing changes in ecosystem productivity by species interactions would be of great interest to “ecologists, agronomists, conservationists, or others”.
The critiques of biodiversity experiments and existing additive partitioning methods are overstated, as is the extent to which this new approach addresses its limitations. For example, the critique that current biodiversity experiments cannot reveal the effects of species interactions (e.g., lines 37-39) isn't generally true, but it could be true if stated more specifically. That is, this statement is incorrect as written because comparisons of mixtures, where there are interspecific and intraspecific interactions, with monocultures, where there are only intraspecific interactions, certainly provide information about the effects of species interactions (interspecific interactions). These biodiversity experiments and existing additive partitioning approaches have limits, of course, for identifying the specific types of interactions (e.g., whether mediated by exploitative resource competition, apparent competition, or other types of interactions). However, the approach proposed in this manuscript gets no closer to identifying these specific mechanisms of species interactions. It has no ability to distinguish between resource and apparent competition, for example. Thus, the motivation and framing of the manuscript do not match what it provides. I believe the entire Introduction would need to be rewritten to clarify what gap in knowledge this proposed approach is addressing and what would be gained by filling this knowledge gap.
Our approach helps determine underlying mechanisms of species interactions, i.e., positive (resources partitioning or facilitation), negative, or competitive interactions. I am not sure how much we need to go further in identifying more specific mechanisms. If resource and apparent competition refers to resource and interference competition, our approach can tease apart them.
I recommend that the Introduction instead clarify how this study builds on and goes beyond many decades of literature considering how competition and biodiversity effects depend on density. This large literature is insufficiently addressed in this manuscript. This fails to give credit to previous studies considering these ideas and makes it unclear how this manuscript goes beyond the many previous related studies. For example, see papers and books written by de Wit, Harper, Vandermeer, Connolly, Schmid, and many others. Also, note that many biodiversity experiments have crossed diversity treatments with a density treatment and found no significant effects of density or interactions between density and diversity (e.g., Finn et al. 2013 Journal of Applied Ecology). Thus, claiming that these considerations of density are novel, without giving credit to the enormous number of previous studies considering this, is insufficient.
A misunderstanding here. Our approach is not designed to test density effect. The same density is held across full density monocultures and mixtures. We use partial density monocultures to determine what species may competitively achieve in full density mixture, without positive or negative interspecific interactions.
Replacement series designs emerged as a consensus for biodiversity experiments because they directly test a relevant null hypothesis. This is not to say that there are no other interesting null hypotheses or study designs, but one must acknowledge that many designs and analyses of biodiversity experiments have already been considered. For example, Schmid et al. reviewed these designs and analyses two decades ago (2002, chapter 6 in Loreau et al. 2002 OUP book) and the overwhelming consensus in recent decades has been to use a replacement series and test the corresponding null hypothesis.
Some wrong impressions. We are not trying to supplant “replacement series” with “additive series”; we use “additive series” designs to supplement “replacement series” design for partitioning changes in ecosystem productivity by mechanisms of species interactions, which would not be possible with “replacement series” design alone, as suggested by many including reviewers.
It is unclear to me whether rejecting the 'new' null hypothesis presented in the manuscript would be of interest to ecologists, agronomists, conservationists, or others. Most biodiversity experiments and additive partitions have tested and quantified diversity effects against the null hypothesis that there is no difference between intraspecific and interspecific interactions. If there was no less competition and no more facilitation in mixtures than in monocultures, then there would be no positive diversity effects. Rejecting this null hypothesis is relevant when considering coexistence in ecology, overyielding in agronomy, and the consequences of biodiversity loss in conservation (e.g., Vandermeer 1981 Bioscience, Loreau 2010 Princeton Monograph). This manuscript proposes a different null hypothesis and it is not yet clear to me how it would be relevant to any of these ongoing discussions of changes in biodiversity.
Our method begins with the null expectation: that intraspecific and interspecific interactions are equivalent. We then propose the competitive hypothesis as a second non-exclusive hypothesis which tests the dominance of positive or negative specific interactions. As shown by its name, the additive partitioning model has been advocated for partitioning biodiversity effects by some ecological mechanisms (CE and SE). The ecological meaning of deviation from the two hypotheses are outlined at lines 201-221 for both individual species and community level assessments.
The claim that all previous methods 'are not capable of quantifying changes in ecosystem productivity by species interactions and species or community level' is incorrect. As noted above, all approaches that compare mixtures, where there are interspecific interactions, to monocultures, where there are no species interactions, do this to some extent. By overstating the limitations of previous approaches, the manuscript fails to clearly identify what unique contribution it is offering, and how this builds on and goes beyond previous work.
The reviewer implies that a partial truth equals the whole truth. The same argument can also be applied to the additive partitioning if relative yield total or response ratio provides a kind of comparison between mixture and monocultures. Our statement is correct in the way that previous approaches are not designed to separate changes in ecosystem productivity by species interactions, as indicated by other reviewers. The additive partitioning is built on Price equation (covariance equation) that has never been biologically demonstrated for relevance in biodiversity partitioning (Bourrat et al., 2023).
We made clear that our work is built on and beyond the null expectation with addition of competitive expectation.
The manuscript relies on simulations because it claims that current experiments are unable to test this, given that they have replacement series designs (lines 128-131). There are, however, dozens of experiments where the replacement series was repeated at multiple densities, which would allow a direct test of these ideas. In fact, these ideas have already been tested in these experiments and density effects were found to be nonsignificant (e.g., Finn et al. 2013).
Out of point. Again, we are not testing density effect. Partial density is used to determine competitive growth responses that species may achieve in mixture based on their relative competitive ability. We used simulations, as partial density monocultures are used only in one experimental study that has been included in our study.
It seems that the authors are primarily interested in trees planted at a fixed density, with no opportunity for changes in density, and thus only changes in the size of individuals (e.g., Fig. 1). In natural and experimental systems, realized density differs from the initial planted density, and survivorship of seedlings can depend on both intraspecific and interspecific interactions. Thus, the constrained conditions under which these ideas are explored in this manuscript seem narrow and far from the more complex reality where density is not fixed.
We use fixed density only for convenience. In biodiversity experiments, density can increase or decrease over time from initial levels. However, initial density is generally used in evaluation of species interactions. If interest is community productivity, density change does not need to be considered. Again, we are not testing density effects.
Additional detailed comments:
It is unclear to me which 'effects' are referred to on line 36. For example, are these diversity effects or just effects of competition? What is the response variable?
It means the effect of competitive interactions on productivity and should be clear based on previous sentences.
The usefulness of the approach is overstated on line 52. All partitioning approaches, including the new one proposed here, give the net result of many types of species interactions and thus cannot 'disentangle underlying mechanisms of species interactions.'
Not sure how many types of species interactions the reviewer referred to. If mechanisms of species interactions are grouped in three categories (positive, negative, and competitive) as has been in biodiversity research, our approach can tease them apart.
The weaknesses of previous approaches are overstated throughout the manuscript, including in lines 60-61. All approaches provide some, but not all insights. Sweeping statements that previous approaches are not effective, without clarifying what they can and can't do, is unhelpful and incorrect. Also, these statements imply that the approach proposed here addresses the limitations of these previous approaches. I don't yet see how it does so.
The weaknesses of previous approaches are not overstated in terms of separating changes in ecosystem productivity by species interactions. As pointed by other reviewers, none of the previous approaches are designed for quantifying changes in ecosystem productivity by species interactions.
The definitions given for the CE and SE on line 71 are incorrect. Competition affects both terms and CE can be negative or have nothing to do with positive interactions, as noted in many of the papers cited.
We are not trying to define CE and SE but only point out how CE and SE have been generally used in biodiversity research (see recent publication by Feng et al., 2022).
The proposed approach does not address the limitations noted on lines 73 and 74.
It does in terms of sources of net biodiversity effect, whether from positive, negative or competitive interactions.
The definition of positive interactions in lines 77 and 78 seems inconsistent with much of the literature, which instead focuses on facilitation or mutualism, rather than competition when describing positive interactions.
Much of the literature supports our definition (see Loreau and Hector, 2001). In biodiversity research, positive interactions include resource partitioning and facilitation. What we are trying to point out is that competition affects species and community level assessments based on the null expectation and needs to be separated.
Throughout the manuscript, competition is often used interchangeably with resource competition (e.g., line 82) and complementarity is often attributed to resource partitioning (e.g., line 77). This ignores apparent competition and partitioning enemy-free niche space, which has been found to contribute to biodiversity effects in many studies.
If apparent competition refers to interference competition, it is included in negative interaction. Changes in species-specific pests and pathogens in mixture will be captured in positive or negative effects through facilitation or interference.
In what sense are competitive interactions positive for competitive species (lines 82-83)? By definition, competition is an interaction that has a negative effect. Do you mean that interspecific competition is less than intraspecific competition? I am having a very difficult time following the logic.
I am glad the reviewer raised this question that may confuse many others and has never been clearly discussed. It all depends on how comparison is made. If species performance in mixture are compared with that in partial density monocultures, as is in competition research, competition effect is negative for all species. If comparison is made between mixture and full density monocultures, as is done in biodiversity research, competition effect should be positive for more competitive species and negative for less competitive species, with resources flowing from less to more competitive species in mixture relative to full density monocultures.
Therefore, the definitions of competitive interactions based on additive series design in competition research cannot be used to describe competitive interactions based on replacement series design in biodiversity research. In biodiversity research, the effects of competitive interactions are never clearly defined at species or community level and mixed up with those of other species interactions.
Results are asserted on lines 93-95, but I cannot find the methods that produced these results. I am unable to evaluate the work without a repeatable description of the methods.
We have added references on sources of these data.
The description of the null hypothesis in the common additive partitioning approach on lines 145-146 is incorrect. In the null case, it does not assume that there are no interspecific interactions, but rather that interspecific and intraspecific interactions are equivalent.
Correct, changes have been made as suggested.
Recommendations for the authors:
Reviewer #2 (Recommendations For The Authors):
I recommend to:
- re-organize the presentation of the material (see my concerns in the public review section). The manuscript is very difficult to read.
Changes have been made to help with understanding of our approach. Figure 1 was modified to show the variations of competitive growth response with relative competitive ability from minimum (null expectation) to maximum (competitive exclusion).
- explore the mathematical form the the remainder term. It seems important to understand that the remainder capture terms unrelated to competition as defined in the present scope.
The remainder measures deviations from the null expectation, due to species differences in growth and competitive ability or competition effect. The term has clear meaning, positive for more competitive species and negative for less competitive species (lines 202-204), and does not need to be further explored or partitioned. The deviations of observed yields from competitive expectations are outlined in lines 205-221.
Reviewer #4 (Recommendations For The Authors):
The authors should be sure to include reproducible methods and share any data and code.
Both simulation and experimental data are shared through supplementary tables. Calculations are included in excel spreadsheets and do not require program coding.
-
Reviewer #1 (Public review):
As a starting point, the authors discuss the so-called "additive partitioning" (AP) method proposed by Loreau & Hector in 2001. The AP is the result of a mathematical rearrangement of the definition of overyielding, written in terms of relative yields (RY) of species in mixtures relative to monocultures. One term, the so-called complementarity effect (CE), is proportional to the average RY deviations from the null expectations that plants of both species "do the same" in monocultures and mixtures. The other term, the selection effect (SE), captures how these RY deviations are related to monoculture productivity. Overall, CE measures whether relative biomass gains differ from zero when averaged across all community members, and SE, whether the "relative advantage" species have in the mixture, is related to their productivity. In extreme cases, when all species benefit, CE becomes positive. When large species have large relative productivity increases, SE becomes positive. This is intuitively compatible with the idea that niche complementarity mitigates competition (CE>0), or that competitively superior species dominate mixtures and thereby driver overyielding (SE>0).
However, it is very important to understand that CE and SE capture the "statistical structure" of RY that underlies overyielding. Specifically, CE and SE are not the ultimate biological mechanisms that drive overyielding, and never were meant to be. CE also does not describe niche complementarity. Interpreting CE and SE as directly quantifying niche complementarity or resource competition, is simply wrong, although it sometimes is done. The criticism of the AP method thus in large part seems unwarranted. The alternative methods the authors discuss (lines 108-123) are based on very similar principles.
The authors now set out to develop a method that aims at linking response patterns to "more true" biological mechanisms.
Assuming that "competitive dominance" is key to understanding mixture productivity, because "competitive interactions are the predominant type of interspecific relationships in plants", the authors introduce "partial density" monocultures, i.e. monocultures that have the same planting density for a species as in a mixture. The idea is that using these partial density monocultures as a reference would allow for isolating the effect of competition by the surrounding "species matrix".
The authors argue that "To separate effects of competitive interactions from those of other species interactions, we would need the hypothesis that constituent species share an identical niche but differ in growth and competitive ability (i.e., absence of positive/negative interactions)." - I think the term interaction is not correctly used here, because clearly competition is an interaction, but the point made here is that this would be a zero-sum game.
The authors use the ratio of productivity of partial density and full-density monocultures, divided by planting density, as a measure of "competitive growth response" (abbreviated as MG). This is the extra growth a plant individual produces when intraspecific competition is reduced.
Here, I see two issues: first, this rests on the assumption that there is only "one mode" of competition if two species use the same resources, which may not be true, because intraspecific and interspecific competition may differ. Of course, one can argue that then somehow "niches" are different, but such a niche definition would be very broad and go beyond the "resource set" perspective the authors adopt. Second, this value will heavily depend on timing and the relationship between maximum initial growth rates and competitive abilities at high stand densities.
The authors then progress to define relative competitive ability (RC), and this time simply uses monoculture biomass as a measure of competitive ability. To express this biomass in a standardized way, they express it as different from the mean of the other species and then divide by the maximum monoculture biomass of all species.
I have two concerns here: first, if competitive ability is the capability of a species to preempt resources from a pool also accessed by another species, as the authors argued before, then this seems wrong because one would expect that a species can simply be more productive because it has a broader niche space that it exploits. This contradicts the very narrow perspective on competitive ability the authors have adopted. This also is difficult to reconcile with the idea that specialist species with a narrow niche would outcompete generalist species with a broad niche. Second, I am concerned by the mathematical form. Standardizing by the maximum makes the scaling dependent on a single value.
As a final step, the authors calculate a "competitive expectation" for a species' biomass in the mixture, by scaling deviations from the expected yield by the product MG ⨯ RC. This would mean a species does better in a mixture when (1) it benefits most from a conspecific density reduction, and (2) has a relatively high biomass.
Put simply, the assumption would be that if a species is productive in monoculture (high RC), it effectively does not "see" the competitors and then grows like it would be the sole species in the community, i.e. like in the partial density monoculture.
Overall, I am not very convinced by the proposed method.
Comments on revised version:
Only minimal changes were made to the manuscript, and they do not address the main points that were raised.
-
-
www.newadvent.org www.newadvent.org
-
Now such like words or deeds wherein nothing further is sought than the soul's delight, are called playful or humorous. Hence it is necessary at times to make use of them, in order to give rest, as it were, to the soul.
It seems as though Thomas believes that there is a positive impact that can be taken away from divulging in games, and that has to mainly do with the soul. He tends to weave in different ideas in religious texts and words of people who contain lots of wisdom to form this idea that the soul of an individual needs to find delight in these kinds of games. He is essentially saying that words such as playful and humorous were invented so that individuals could discover different ways to create such strong or positive emotions that come from different activities. If playing some kind of medieval game creates "humor" or inspires "joy" in someone's heart, then it was a game that was meant to exist and be played by all.
-
-
mysteriouschanting.wordpress.com mysteriouschanting.wordpress.com
-
Mythos Deviations is a set of six side-scenarios for Arkham Horror: The Card Game that are each paired with one of the first six official campaigns. These scenarios can be played as standalones, or as side-scenarios for any other campaign, but are intended to be played within the paired campaign.
.
-
-
socialsci.libretexts.org socialsci.libretexts.org
-
a farmer might have kept a pebble in a box to represent each chicken he owned. As further advancements made keeping track of objects-representing-objects more difficult, more abstract symbols and later written words were able to stand in for an idea or object. Despite the fact that these transitions occurred many thousands of years ago, we can trace some words that we still use today back to their much more direct and much less abstract origins.
I feel like language has become so complex that it is again becoming a thing for the pepople of power and status. Think about taxes, or Wall Street, the language they use is so complex but it boils down to such simple meanings. I think they do this to keep normal people from being able to play the game by making it so complicated that the average person just gives up. Language is being used as a form of war on the average people.
-
-
52.2.80.92:1336 52.2.80.92:1336Edm8ker2
-
Become a Tech Integration Pro!Our micro-learning courses will elevate your teaching game. Integrate tech seamlessly and watch your students thrive!
@Emilio Content has been updated but isn’t reflected in Figma. Please refer to this doc here : https://docs.google.com/document/d/1RNKQyGQX3xPUyXYuKRIoPodcYTnDQHCrh2kn2cPf19c/edit
-
Our micro-learning courses will elevate your teaching game. Integrate tech seamlessly and watch your students thrive!
should #14386C color
-
-
www.azlyrics.com www.azlyrics.com
-
I'm at the top of my game
Megan is at the highest of the hip-hop game and she's letting it be known.
-
If these bitches ain't mad, I need to go harder, I can't let 'em think we the same
She is basically saying that she needs to step her game if the haters aren't hating up and become a unique person outside of other rappers in the game.
-
I'm at the top of my game, I'm who they hate
She is reminding people that she is successful and that people hate her because of it
-
-
-
it had College Football Playoff implications.
This article is an example of timeliness, as the game happened on Wednesday night, impact, as it will effect a lot of people both involved with the two teams that played, as well as most of the college football world, and prominence, as the college football playoff is significant and heavily followed by millions of people around the world
-
One of the most significant college football results of this week took place on—believe it or not—Wednesday night.
The statement of this game being one of the most significant college football results of the week is an opinion as other people can disagree by the time the college football week is over
-
-
-
Since 1950, he is just the fourth quarterback to record a 140-plus passer rating in three consecutive contests, while his 83.5 completion percentage over his last four games is the highest in a four-game span (min. 90 pass attempts).
Another fact/statistic in the article
-
-
www.youtube.com www.youtube.com
-
4:05 - This is pure Game Theory
Let us create an OMNIGAME theory
Tags
Annotators
URL
-
-
www.tampabay.com www.tampabay.com
-
“It sucks,” linebacker Yaya Diaby said. “It sucks, but at the end of the day we have a division game coming up and that’s our focus.”
I like how the author is including different quotes from different players but I feel as if it should be cited when the quote was said and who gave the interview.
-
If trying to win that game was pointless, this one was utterly senseless.
Biased example
-
“We don’t second-guess,” head coach Todd Bowles said. “We got our guys, we’re playing everybody we got. Unfortunately, he got hurt. We feel bad about that, but he’s a football player. He wants to be in the game like Baker (Mayfield) and everybody else.”
This was a good necessary quote to input as it sort of clears the air and sets a different perspective for me being the reader in the sense that the players wanna play and do their job instead of not playing. Although it would have been smart to take him out I feel as if this is the reality of the injury.
-
The game was lost, the Bucs were just too stubborn to admit it.And because of that, the season may be lost as well.
Although realistically this is a fact it can also be viewed as an opinion since theres no factual way to tell if they could have had a comeback or be bad the rest of the season.
-
-
the-orb.arlima.net the-orb.arlima.net
-
After lunch all the youth of the city go out into the fields to take part in a ball game.
It's lovely to see how this has not changed so much even today, especially with people in England crazy for sports like soccer/football and rugby.
-
-
www.proquest.com www.proquest.com
-
t normally takes me eight hours to just rethink and focus on the next one, but the abuse doubles that amount of time,'
players should be able to disconnect after a game the same way employees disconnect from work. These messages don't allow them to do so
-
you lose a game and you're going through all of your personal feelings and thoughts.
causes players to get in their own head
-
some who bet on games are now targeting players with abusive messages when an individual fails to win a match.
same idea that was expressed in the Blame Game article I read
-
-
www.nbcsports.com www.nbcsports.com
-
Flowers limped off the field and didn’t return on the possession.
I feel as if the author could've had alot more detail in this article if it was not posted during the 2nd quarter rather the end of the game.
-
The Ravens needed it, having fallen behind the Bucs 10-0. It could have been worse, but Tampa Bay had a Chris Godwin touchdown negated by a holding penalty on Tristan Wirfs.
This could be looked at as bias since Charean Williams says, 'The Ravens needed it" which comes out to be an opinion when in reality they really did need it to keep up in the game.
-
-
sports.yahoo.com sports.yahoo.com
-
In addition, John Buccigross will host a live five-hour whiparound show with help from analysts Kevin Weekes and P.K. Subban. From 7 p.m. ET to midnight, they’ll bounce from game to game while showing the best goals, saves and plays from all 16 clashes.
This is very similar to what the NFL does with Redzone where they show all the action from all the games
-
If you’re wondering why the NHL set a Vancouver Canucks and Chicago Blackhawks game for an 8:15 p.m. ET start time on Tuesday, or why the Tampa Bay Lightning and New Jersey Devils are getting underway at 6:45 p.m., there’s actually a very good explanation.
I think this is a good way to open their article because it makes people actually think "Why are the games starting so early"
-
-
opentext.uoregon.edu opentext.uoregon.edu
-
Then, there are subjects and behaviors discussed even less frequently. These are so deeply embedded in those who grew up in the culture that they occur as thoughtlessly as breathing. This might include norms between genders or ages, how the culture values personal space, or even what is seen as “good” or “bad.” These aspects remain deeply hidden unless we are willing to acknowledge and discuss them.
The notion that there are behaviors that those who grew up in a certain culture do things as thoughtlessly as breathing is interesting to me. When reading this, I recalled someone saying that when they went to a stadium in Japan and were leaving, he recognized that there was almost no trash anywhere to be seen. Such really surprised me, as that is not what would come to mind to me if I thought of a stadium after a game would look like here in the U.S.
My interpretation (not sure if I'm right) as why this is the case is to the fact Japanese people at a very young age are taught to clean not only after themselves but after their community also since a very young age. But I don't know, just an idea.
-
-
thewasteland.info thewasteland.info
-
I do not know whether a man or a woman
The line "I do not know whether a man or a woman" emerges from the section "A Game of Chess," which delves into the disintegration of human connection. This line signifies the speaker’s existential uncertainty, reflecting a world where traditional gender roles and identities have become muddied and irrelevant.
Here, the ambiguity echoes the broader themes of alienation and fragmentation, as the characters struggle to communicate and connect. The uncertainty of gender mirrors the breakdown of personal relationships, suggesting that in a chaotic, post-war landscape, even the most fundamental aspects of identity are in flux. This disorientation emphasizes the emotional paralysis faced by individuals, reinforcing the haunting sense of isolation pervading the poem.
-
HURRY UP PLEASE ITS TIME
Eliot artfully weaves imagery and language that evokes quietude into the fabric of the poem, creating a body of work whose essence personifies forms of silence. The poem possesses a hushed quality, behaving similarly to a curse word. As if to engage and think with the poem is taboo. Yet, when read, the assemblage of fragmented imagery, allusions, ambiguous language and voice, or lack thereof, engenders a profusion of sound. Eliot’s use of syntax in “A Game of Chess” depicts the unexpected resonance of unsaid speech, drawing attention to the hidden yet audible nature of cognition. The capitalization of “HURRY UP PLEASE IT’S TIME,” a noticeable shift from the earlier lowercase dialogue, intends to evoke a semblance of sound while maintaining the generally quiet disposition of the poem. Eliot's interplay with cognition and sound probes the potency of unsaid speech, revealing how the silence between words carry as much meaning as spoken language itself, inviting readers to consider the depths of thought and emotion that lie beneath the surface of expression.
-
The Chair she sat in, like a burnished throne, Glowed on the marble
Parth’s annotation on this line introduces an interesting interpretation of its origins in Antony and Cleopatra. He identifies that “this line is an imitation of a line we see early on in Antony and Cleopatra—with one change: the word "barge" is changed to a capitalized "Chair" here…Chair might not be referring to a literal chair, which isn't a proper noun—but an organizational position. A "Chair" in a company is an executive position; likewise, a metaphorical Chair in a kingdom may refer to one's supreme status” (Jain). I’d like to expand the scope of the Antony and Cleopatra reference beyond specific lines that Eliot incorporated into “The Waste Land,” now through Parth’s lens of Cleopatra’s status and power within the play, her “Chair” within Antony and Cleopatra, and therefore “The Waste Land” as well. When reading Antony and Cleopatra, I couldn’t help but take note of the many ways in which Cleopatra both adopts the role of the queen in a literal game of chess. In a very broad sense, Cleopatra’s decision to fake her own suicide, to temp Antony with her death, is quite analogous to the physical and strategic features of the queen on a chess board. For example, while Cleopatra plots to win the attention of Antony, she says, “I have nothing Of woman in me: now from head to foot // I am marble-constant” (Shakespeare, V.II). In portraying herself as hard as marble, she renders herself part of a chess set, as they are often made of marble. The image of a chess board is then transferred to the marble as it appears here in “The Waste Land,” further convincing me that Cleopatra is the queen of Eliot’s chess set as it is understood in “A Game of Chess.” Additionally, Cleopatra embodies the characteristics of a chess piece as a powerful strategic asset when used correctly. She even says, “come hither, come! come, come, and take a queen worth many babes and beggars” (Shakespeare, V.II). “Take” is the terminology in a game of chess for the capture of a piece. I believe it’s possible that both Shakespeare and Eliot recognized the parallels between Cleopatra’s actions and the act of sacrificing a piece in the game of chess. However, Cleopatra’s move was in vain, and ultimately, when she sacrifices her life, amounts to nothing. In other words, the power she possessed through her “Chair” is only valuable insofar as it is spent to win the Game of Chess. Meanwhile, the woman in “The Waste Land” also sits dead on her throne, her status reduced, presumably having met a similarly wasteful fate.
-
Those are pearls that were his eyes. 'Are you alive, or not?
Eliot’s interest in death by suicide (as we see in the Sybil epigraph) is brought to life here in an overlap of Shakesphere references. Of course, the first line here is an echo of the Tempest reference in Burial of the Dead. Notably, it is a reference to Alonso, who tried to drown himself upon hearing false news of his son’s death. Then, the second line is quite feasibly a reworking of the famous, “To be, or not to be,” given that they are syntactically analogous with the placement of commas. Actually, they are structurally inverted, with the Hamlet comma placed in between the second and third syllable (x x, x x x x), while Eliot’s comma is placed in between the fourth and fifth syllable (x x x x, x x). Hamlet’s line is most popularly interpreted as a contemplation of suicide. Together, these two references seem to point to Ophelia’s death, and suggest Eliot decides that hers was a death by suicide as well.
The way Eliot inverts the structure of Hamlet’s line brings to mind the concept of a reflection, such as the “glassy stream” in which Ophelia drowns, as if the Eliot line floats on the surface of a body of water. If we were to indulge that imagery, it certainly would reaffirm the ideas of death and corpses, seeing as corpses float in water. This calls to mind the line “fear death by water” from Burial of the Dead in the tarot section. Perhaps Eliot means to prophesize suicidal drowning, which adds an interesting wrinkle to the grave motif that we’ve seen so often up to this point: does Eliot’s focus shift from the ground as a resting place to that of a water-submerged grave in A Game of Chess?
-
I do not know whether a man or a woman
This line is lifted from a translation of the Visuddhi-Magga, where a woman adorned in accessories (such that she looks like a goddess) leaves her husband’s house to return home. On her way, she is met by an elder who bestows “saintship” upon her based on her teeth. Physical beauty is in indicator of divinity, but perhaps an erroneous one. He declares, "Was it a woman, or a man, /That passed this way? I cannot tell / But this I know, a set of bones / Is traveling on upon this road."
The ambiguity on gender suggests it is not feminity nor masculinity that constitutes this third creature, this mysterious other whose presence is alluded to but unknown. In the passage, it is a woman, dressed in accessories to look like a goddess, that walks the road. Yet to the elder, gender is irrelevant; all he sees is “a set of bones”. The human identity is thus defined by the physical structures that support us. The bones that prop, the skin that wraps, the muscles that hold – the human being is whittled down into strictly anatomy. The personification of “a set of bones” also evokes a sense of resurrection, where the skeleton - now a symbol of the core of a human being, not the death of one - travels directionlessly on the road. The use of demonstrative pronoun “this” reemphasizes the proximity of the skeleton - this divine -, correlating the road it travels on to the one the speaker (and us) are on.
The focus shifts later in the passage to the vulnerability of bodies in their indiviudal, amputated form. Hair, when detached from the scalp, flies loose and tangled in clumps in the drain or kots on a comb. Nails, clipped or fallen, become trash. Teeth, the most animalistic mechanism that chews and rips and tears, when fallen out, becomes useless and remains, if lucky enough, in a dusty wooden box. In this way all our bodily extensions are accessories – external decor to conceal the throbbing, vulnerable creature that resides within. Hair insulates the head and covers the neck, teeth flank our soft greedy mouths, and nails protect nerve bundles and, by extension, physical touch. What can be perceived outward is a disguise for what lies within, which I suppose must be the soul. While alive, a human’s exterior features can be come detached; joints can loosen, organs can fail, and skin can callous. And in death, organs liquify, hair decomposes, and muscles decay. Yet bones, in their stubborn white glory, remain. They are firmly rooted in the ground, a testament of a human’s existence, a mere indicator of the body it held, the life it contained.
Eliot references bones throughout TWL – they are lost in rats’ alley, they rattle by Sweet Thames, they are in the bottom of sunken ships. Of all the disguises a human wears, (the queens no different form the cadavers in “A Game of Chess”, the dead buried and regrown), at their core they are all bones. Perhaps that is where the truth lies – in that which cannot be decomposed.
-
-
www.carnegie.org www.carnegie.org
-
the right of the laborer to his hundred dollars in the savings bank, and equally the legal right of the millionaire to his millions.
for - critique - extreme wealth inequality cannot be avoided for the greater improvement of society - The Gospel of Wealth - Andrew Carnegie - stats - Mondragon corporation - comparison of pay difference between highest paid and lowest paid - adjacency - Gandhi quote - Andrew Carnegie beliefs in The Gospel of Wealth
critique - extreme wealth inequality cannot be avoided for the greater improvement of society - The Gospel of Wealth - Andrew Carnegie - It's a matter of degree - Wealth differences within US corporations of 344 to 1 are obscene and not necessary, as proven by - Wealth difference of 6 to 1 in Mondragon federation of cooperatives - To quote - Gandhi, there is enough to meet everyone's needs but not enough to meet everyone's greed - The great problem with such large wealth disparity is that those who know how to game the system can earn obscene amounts of money - and since the concept of luxury goods is made desirable and proportional to monetary wealth, it creates a positive feedback loop of insatiability - The combination of engaging in ever greater luxury lifestyle and power is intoxicating and addictive
to - stats - Mondragon corporation - comparison of pay difference between highest paid and lowest paid - https://hyp.is/QAxx-o14Ee-_HvN5y8aMiQ/www.csmonitor.com/Business/2024/0513/income-inequality-capitalism-mondragon-corporation
Tags
- stats - Mondragon corporation - comparison of pay difference between highest paid and lowest paid
- critique - extreme wealth inequality cannot be avoided for the greater improvement of society - The Gospel of Wealth - Andrew Carnegie
- adjacency - Gandhi quote - Andrew Carnegie beliefs in The Gospel of Wealth
Annotators
URL
-
-
viewer.athenadocs.nl viewer.athenadocs.nl
-
Conclusie
. From this study, we concluded that over the course of a whole small-sided game, the forward-backward motion of the centroids is most strongly linearly related. Furthermore, goals show a specific pattern in the forward-backward motion of the centroid. Therefore, surface area and particularly centroid position may provide a sound basis for a collective variable that captures the dynamics of attacking and defending in soccer at team level. Future research should develop these ideas further
-
-
socialsci.libretexts.org socialsci.libretexts.org
-
Thus the self-serving bias is a perceptual error through which we attribute the cause of our successes to internal personal factors while attributing our failures to external factors beyond our control. When we look at the fundamental attribution error and the self-serving bias together, we can see that we are likely to judge ourselves more favorably than another person, or at least less personally.
The mentality of “I hit the game winning shot because I’m the best” vs “I missed the game winning shot because you didn’t get me the ball fast enough” Fascinating to see these examples from life be put into a structured explanation.have a coworker who, if there is a mistake, will always be the last to get back to the office and then proceed put the blame on someone else. If the job is completed on time, looks good and mistake free he will be the first one in the office reporting to the boss how good he did on the job.
-
-
inst-fs-iad-prod.inscloudgate.net inst-fs-iad-prod.inscloudgate.net
-
believing game
I like the concept of the "believing game" where I take the shoes of the original author and write from his perspective fairly, even if planning to disagree with his thoughts later.
-
-
pmc.ncbi.nlm.nih.gov pmc.ncbi.nlm.nih.gov
-
A Linguistic Error Limit.
this section discusses how we can inject communication errors into the game. The form used creates a tradeoff between more signals (expressivity) and accuracy (expected no of correct messages)
-
The matrix P contains the entries p ij,denoting the probability that for a speaker object i is associatedwith sound j
This is basically a probabilistic belief of the signaling system by the speaker and listener in a lewis signaling game.
-
Hence, we assume that both speaker and listener receive areward for mutual understanding. If for example only thelistener receives a benefit, then the evolution of languagerequires cooperation
When agents get the same rewards they are in a cooperative game. This is not expressed clearly.
And again in line with the Lewis Signaling Game
-
-
www.ncaa.org www.ncaa.org
-
more than 540 abusive betting-related messages were directed at men's and women's basketball student-athletes and game officials, including death threats.
I get the games are serious and competitive but no game is worth sending a death threat over
-
-
scontent.ftlv16-1.fna.fbcdn.net scontent.ftlv16-1.fna.fbcdn.net
-
Task & Talk
Task and Talk is Clearly based in the Lewis signaling game. However this setup seems to lead to entangled solutions at least for the minimal number of required signals.<br /> A needs to send one of three signals - the one he does not need. Then B needs to send one of four symbols for the state of one then the other (order is selected by symmetry breaking and learned thoroug reinfocement.) In this minimal version the signals are reused. If agent A has 8 signals he can respond fully without needed a second round.
-
-
pressbooks.pub pressbooks.pub
-
Kindling a fire and broiling the fresh-kill’d game,
death contributing to life.
-
Stands amused, complacent, compassionating, idle, unitary, Looks down, is erect, or bends an arm on an impalpable certain rest, Looking with side-curved head curious what will come next, Both in and out of the game and watching and wondering at it.
He seems to think he is above others, or at the very least looking down at them amused and in a state of wonder
-
Alone far in the wilds and mountains I hunt, Wandering amazed at my own lightness and glee, In the late afternoon choosing a safe spot to pass the night, Kindling a fire and broiling the fresh-kill’d game, Falling asleep on the gather’d leaves with my dog and gun by my side.
Could this be a false utopia?
-
-
www.youtube.com www.youtube.com
-
Why is this all happening? This is devastating. This is heartbreaking. You know, I've tuned in on the future many times, and I do see like, of course, there is going to be a lot more catastrophes, but on the other side of that, they always show me that the light is going to win, like the digital age is approaching. So it's really just how we kind of look at that, because, like, the first level is awakening to the systems, and the second level is anchoring in your own system. Faith is like our birthright. It's just that we've wired in fear so much we think that's our natural state of being. I like to welcome to the show Ella Ringrose. How you doing Ella? I'm super well. Thank you for having me. Thank you so much for coming on the show. I'm looking really looking forward to talking to you about your unique journey into where you are getting to this place in your life. So before we start talking about your more psychic and mystical abilities, what was your life like prior to you learning about your psych abilities, or at least coming out of the closet, if you will, with your psychic abilities. Well, I became aware that I was psychic quite young, young, but for most of my teenage hood, I really struggled with my sensitivity. So I guess I was hiding in a sensitive closet of always feeling like there was something deeply wrong with me, and I really struggled to fit in in school. I was failing everything in school as well. I was diagnosed with dyslexia and dyspraxia, and so sitting in class, I couldn't retain information. It was like my mind would shut off. And I always found myself being extremely sensitive to other people, other people's emotions, you know, people who were quite strong. I was very sensitive to a lot of stuff, so I grew up very much masking myself and and who I really was to fit in. But it got to a point where I just felt like I was gonna crack like, you know, when you have like, like, a lid over a boiling water and it just starts bubbling over. It just got to this point where I just couldn't continue pretending to be just like a normal person. And so when I was 17 years old, I was sitting in the back of math class, and I heard this very strong voice. Now I know it's the voice of Spirit, telling me to drop out of school. And I was in the back of math class, and I remember just making that decision in that moment. It was like every part of my body, every cell knew that that was going to be my last day. And so I went home and I told my mom, and they were not obviously happy about it, but I knew that this was what I had to do. And so shortly after that, my brother was on his own self development journey, and he bought hundreds of self development books and spiritual books and filled our bookshelf in our living room up. And so one day, he handed me the specific book called feel the fear and do it anyway. Before I remember that book. Yeah, I was in college when I read that that, book. Yeah, it was before. Then I was just depressed and I was so super anxious. So when I read that book, my 17 year old mind was like, fear isn't real, like, why has no one told me this? Like, it infatuated me. And so I'd been wanting to do YouTube since I was 12 years old. And so I ran home from reading that book on the train, and I started my YouTube channel, even though I was petrified. What year was that? What year was that? I don't know. I'm 25 now, so it was nearly eight years ago. Yeah. So we're looking at oh gosh, 2012 early on. It wasn't when YouTube wasn't popping just yet. It wasn't Oh, Mr. Beast. Mr. Beast wasn't around yet. No, not at all. He probably was, but he wasn't known. But I've been watching YouTube, because the only thing that kept me going when I would go home from school and cry every day was YouTube. It was the only thing that made me feel I could relate to other people who were on the other side of the screen showing things in their lives. Because I wanted that normality, and so I found that book, and I just became infatuated, and I just went around down a rabbit hole, and was studying and studying and reading and learning, and one day, our family, we lost our home overnight, like we were told that we had to leave. So I couldn't bring anything, I couldn't bring my clothes, I couldn't bring my furniture, because it's a long story, but I had to leave everything overnight because there was a mold infestation as well. So all my products and things were destroyed. We were all quite sick, and so I flew to Canada, and that is when the spiritual journey really started accelerating. It was almost as if angels and guides and spirit were coming to me, and I couldn't ignore the guidance that was moving through and the guidance they were showing me. It all started with me when I was walking into a bookstore, and this book was a book by Gabby Bernstein. It was called Super attractor, but it had my face on the cover. And at this time, I was still somewhat of an atheist. I was very into like energy or emotions and mindset, but I was still very closed off to that realm. And this book had my face on it. And. I remember just staring at it, looking around like, is anyone seeing what I'm seeing? What is going on? That was my first kind of like experience where I was physically seeing things with my eyes. And I went home and read that book, and it was all about angels. And then within the next few days, the voices just came in. The connection just clicked. It was like reading that book overnight. My body just knew that this was real and I recognized it. It was as if my soul was remembering a part of itself that was ready to be activated. And that was kind of the beginning of my, my spiritual journey. So when you first started to feel these psychic the voice, I hate the voices, the voice, the things coming through, I always like asking this, did you think you were losing your mind? Did you? Because that's a normal normal thing is like, Hey, I hear voices. That's when they used to send people to the loony bin with that stuff in the in the padded sense. So I always ask channelers, and I always ask psychics this, because it's the first question I would ask if I heard a booming voice in my head, and yeah, and it did with was it just a voice, or was there an energy or a feeling with the voice that calmed it down, which I hear that happens as well? Yeah, to answer your question, no, it was actually, I mean, of course, later in my spiritual journey, I did start to think I was losing it like the more I started diving deep, of course. But when I did receive that guidance, it was actually a moment I had never felt the amount of peace that I had, because I finally didn't feel alone. I was like, there is more here than meets the eye that I was craving and seeking this whole time I was on earth, you know. So it felt very peaceful. And how my gifts work is I don't see them physically with my eye. Although I did see the Gabby book, I see it through my third eye. So like, it's like a, I see, I call it like a projector, like, you know, like a movie projector screen, like, puts it out into the wall. It's as if my third eye can can show me it in the physical room. So I was being able to see it through my third eye, but not my physical eyes, if that makes sense. Of course, yeah, I was scared of angels at night time when I was in bed, and I was like, Oh, my God, are there like, these beings around my bed, on all of that. But no, it didn't. It wasn't scary to me. Like, cellularly, I feel like it was my soul remembering as I dive deeper. It was just an awareness of like, oh no. This has been a part of my path for many lifetimes. You know? It just felt natural. It felt normal. Yeah. It was like you said, a remembering, because if you were an atheist, then past lifetimes was probably not a thing that you really thought about, or even thought was real when you decided to come out of the spiritual closet start your YouTube channel. I'm assuming your YouTube channel was in this this space at that time, even when you started talking about so you're talking about this stuff in public eight years ago, which you know, to be fair, eight years ago, the consciousness of the planet wasn't near where it is today. It wasn't as open. There weren't these kind of conversations happening freely as many as they are now, what did the people around you say, your friends, your family, and how did you deal with what they came at you with, because I have to imagine, it wasn't all Kumbaya. They were worried for sure. Yeah, concerned. I have a lot of joy. And from from my perspective, it was exciting me so much, I just wanted to share it, you know. So in my head, it was like, Oh, this is literally transforming my life. This is incredible. Like, this giddiness in me was like, let me share all of this. So I was, like, spewing this online, making videos every day. But in regards to like, family and friends at the time, I had actually kind of cleared all my friendships, so I was very much kind of in my own journey. I didn't have a lot of friends around me at the time. But in regards to family, it was very much like a concern. It was kind of like, I don't know what Ella's doing. Is she getting into a cult, you know? So that was, that was a strong thing, yeah, and especially when I was diving deep and healing a lot, you know, as well, was concern of like, do I need to go to a psych ward? There was definitely some parts of that. But at the same time, my family aren't like a normal family either, in the sense that we've always been very like loving and open and expressive with our words and like from a very young age, my mom and my brother and I, living together, we were all so into mindset and self development. So we were all quite like, expanded in our minds and open to possibilities and ideas, and as the path moved on. It's kind of comical, because my mother is extremely psychic, and my stepmom was always believing in this stuff. She had a million Angel books in her home. So there was actually a lot of people surrounding me that were in that realm that I wasn't aware of until I was able to see it to myself. You know, Now was there a moment where you used your gifts to do a reading or help somebody that not only changed their life but surprised the heck out of you. Oh my gosh. I feel like that's every reading, Alex, every reading, Your first your first one, the very first time you did it, like I imagine the first time you did a reading for somebody, you were like, Oh man, that worked kind of thing. I actually remember it. I remember it. I was living in the Canary Islands at the time, and my psychic gifts started accentuating very strongly, and I heard spirit being like, just go give it to strangers on the beach. We are in a time of great change, and humanity is awakening more and more every day. Mankind needs insights on what is happening to all of us. That is why I'm inviting you to Wisdom from Beyond a six day virtual summit designed to awaken your soul. Experience over nine hours of soul expanding channeling sessions led by six of the world's most esteemed channelers, connect with the divine, receive sacred insights and transform your journey by asking questions directly to the channelers themselves. This is more than just a summit. It is your gateway to understanding the profound shifts happening within and around all of us, plus, when you sign up, you receive exclusive bonus content to deepen your spiritual exploration, join us and step into the extraordinary. So I went up to someone, and I just said it. I was, I was literally just like, Can I can I do this? They were like, Sure. And I knew that they had lost their job. I knew that they were suffering and they were struggling. I felt their insecurity. I felt so many different things, and I was expressing it. And he was like, Who the hell are you? Like, this is weird, you know. So I was kind of like, oh, that validated it, that it's correct. And I just kept on going and doing it with other people and friends, and started to know a lot of stuff that, of course, I wouldn't have known myself until I tuned in. And that's when spirit was like, you're going to have to start offering readings. And so I was living in Lapland at the time, and that's when I started going full time giving readings. And I think I've done over 1000 now, and they've all been deeply transformational. But I always find that each reading I've done has given me more than than what I give them as well, because I'm learning so much about each person's soul, and I'm learning so much about giving ourselves permission to have joy, because whenever I tune into people's guides, it's nothing but unconditional love for that person sitting right in front of me, like their guides just want the best for them. They just want love for them. And seeing that like common thread that is played out in every single reading, it's like, oh, the meaning of life is actually very simple. It's very simple. And it's it's giving ourselves permission to experience that. So being in the space that you're in, and even being in the space that I'm in, there's criticisms that come towards you. You know, obviously, let's not even talk about the YouTube comments, but but in let's not, let's not go down that dark rabbit hole. But have you dealt with that kind of energy coming towards you about your gift. Because, again, this is it's much more accepting now than he was even a decade ago, and is becoming more and more accepted as shows like mine and others are kind of putting the word out for things and people's consciousness are raising. But how do you deal with that kind of negative energy that comes towards you? Because I have to believe that you have had it at one point or another in your journey. Yeah, yeah. I mean, what's quite interesting about that question is it doesn't really bother me for the reason that I dove so deep into heart, awakening a long time ago, and connecting to my heart, that I feel just genuinely compassion. Because I find when people think of this as kind of weird or not real, I have like, this sadness, feeling like, on some level, they're missing out. Because it's so joyfully infectious in my life that I kind of just see it as like, okay, it's just not their time yet, and it's very accepting. And also, from doing so many psychic readings, I really feel I have one foot in the physical and one foot, like, in the higher realm. And so I see everything from a higher perspective, always, rather than, like a grounded, like, reactive state of like, why is this happening to me? I always see it from like, a soul level of being like, okay, it's not their time. I see their perception. And because I can see through people's emotional bodies, their spiritual bodies, whenever I see this kind of criticism, I always see the reflection within themselves. So it just gives me a higher grace of compassion, not to say that I'm a human and I don't get triggered, but it's like something that I've just learned over time and and I think also just of the miracles that it's created my own life and seeing in my friend's life, my loved ones lives, like it's just kind of for me, like it's so real. It's like, it's my soul, it's, it's everything to me that I just, I don't mind because I just am like, well, it's, it's such a blessing that I appreciate it, regardless if someone else doesn't believe in that or think that's crazy. How do you balance living a human life with the amount of knowledge and connection you have to the other side? And this is a problem that I know near death experiencers have, and channelers have, and psychic mediums have, because they live a lot of times more time on the other side than they do in reality. So how do you build relationships? How do you you know, if you want to have a loving relationship, you know a romantic relationship. How does that work? How do you deal with other. People that might not be at the same place that you are, and you're like, Ah, why do I have to deal with this stuff, this lower energy stuff, when I know what's happening on the other side, I know where we're all going to be going, like that, knowledge has to weigh heavy on you, to be to balance that just normal living life day to day. I do. I think that it's kind of comical, because I've made a career out of it, so most of my life is surrounded by that type of energy anyway, but I understand where you're coming from, and it's been a journey, you know, like there was a few years where I was literally sitting in my apartment talking to angels more than humans, you know, and that that wasn't normal either. That's a problem. It was a problem. And at the time, I didn't see that, and I was connecting to angels. I was connecting to more on that side than literally anything, and I didn't have many relationships. And it took kind of like this moment of me surrendering literally on my knees and praying and being like, I allow you to take over, because I feel like Spirit is the one that moves through me and guides me. And so what started to happen was I just started being guided to the right places and the right people that I brought people into my life who were extremely grounded, who were extremely like, into their body, or into, like healthy eating, or like a specific way of living. And I found I've traveled all over the world for the past five years, living with multiple different people who reflect and get, like, have so much codes to offer. Just for example, like I was living in Costa Rica a couple months ago, and I was living with a beautiful like, sister of mine, and she is, like a primal, ancestral eater, and she's very grounded in her body. And like, living with her impacted my life so much that, like, I eat so primarily now and organically and like good, that it's almost like I do my psychic reading, and then once that's finished, I'm not thinking about spirit. I'm in my body. I'm in my life. I'm in my experience. But in regards to it being a challenge, because I can understand a lot of people listening who are just in a hometown and they feel like they're the only one who's kind of awake to that stuff, I really resonate with that pain, and I do understand that that is a very challenging and difficult thing, and it was something that I was tuning into before coming on here that I really wanted to like address, which is, I really believe that it is so vital, like essential is to have your soul tribe. It is to have people that literally inspire you and expand you and uplift you. Because I've been on the other side, where I've been around people where they didn't really understand my way of being. And truthfully, it feels like my soul is suffocating to some degree. And of course, there's a lesson, there's there's growth there. But I also find that it's really important that you find people that you're like are your tribe that can inspire you and influence you. And whenever I used to tune into that and call those people in I kept getting visions of like Earth grids all over the world, like people, like, even if you are alone in your hometown, you're connected to 1000s of other people who are on your frequency on Earth right now. So you're always connected. So what I started to do was, like, connect to that frequency of having support and having people. And it went from I remember like crying to my mom being like, I've literally no friends to like, I don't really want any more friends because I have too much, if I'm being brutally honest, because I've called in so many and it came from like really connecting and believing those people were out there and then going out to meet them, because I've been on that side where you feel like you just don't have anyone who understands you. And I do know how painful that can be, and I really want to honor people who may feel that or go through that. But what I've come to learn is it doesn't have to be that way. Of course, we learn stuff from people who aren't like that, but you can find so many people who are on your wavelength, who are on your path, that are here to guide you and to expand you in a friendship, in a relationship, in whatever way that wants to come Yeah, we always joke around. Like, as you get older, you start running around when people come into your life and try to become friends after you get to a certain age, like we're all friends. Like, we're all friended up here. We're good, yeah, we don't need any I'm not like that, but I could understand, no, we're good. Thanks. I don't have the energy or time to build a new relationship. I have enough. Thank you. You're overflowing. We're overflowing with blessings. We're good. Thank you. It's very, very interesting. Now, one thing is, I want to, and I would love to hear what your spirit, your guides, are saying about this is that we're going through such a difficult time right now, these last four years, the decade so far, has been a journey, to say the least. It's the roughest decade I've ever been a part of. I have been on this earth a couple years longer than you, just a couple, and it seems like we are going through a major, major, not only shift in consciousness, but a shift in general, for so many people who are like, Oh, my God, the world's coming to an end. This is everything's burning, all this, all this negative stuff. Why, from your spirit guides point of view, why is this happening to us right now, and where are we going to be going over the next Well, this year we'll see where we we still got a heck of a year left over here, but the next decade or so, where are we? Where are we going? Why is this happening? Yeah, this is something I have really like argued with my guides and confused, because the human heart, the compassion is like, why is this all happening? This is devastating. This is heartbreaking. But what I've come to understand, and what my guides have shown me so many times, is that a lot of the darkness we see today has always existed, not to say on this entire time on Earth, but because there is such an influx of light and a frequency of people awakening, and so much information nowadays that people's consciousness is accelerating at such a rapid rate, we're just being revealed what was already there. And so I see it as like they always say to me, Ella, this is like a spiritual warfare of dark and light, but it's all essentially happening so that we can remember who we are. And whenever I would tune into this, it was, it was just a really hard, hard thing for me to tune into, because I am very conscious of my guides would show me a lot of things that were happening, happening in Hollywood and with the music industry, the film industry, things that like I logically didn't seek out like my guides show me all the time, things that are happening in the world that, like, are just horrific, and something that I just freaks me out. But they're always showing me like there is a density on this planet, because Earth is, like, one of the only, or if the only planet in the galaxy that has this ability for us to be eat the most, like, like animalistic, primal to Avatar consciousness. Because if you think of like a dog or like a cat, they can't, like, ASCEND their consciousness, they just are at that level. Whereas humans have the option of, like, going from such a density of pain or of trauma, of all these deepness, all the way to like, higher vibrational frequencies, like we can become whoever we want. So with the state of the world, it's kind of like showing me that it's all just being lifted because there are more people on Earth right now than ever that are awakening, that are holding the light, because a long time ago, there was a darkness that took over and tried to place these fear paradigms on the earth that we have all been controlled and constricted to live and embody every day. And so we're waking up to expand that and to remember our light. So the more that we see these terms play out, unfortunately, that is a reflection of how much we're then remembering who we are, because we're being asked to look within ourselves and to remember the light, which is kind of the purpose of this earth. And you know, I've tuned in on the future many times, and I do see like, of course, there is going to be a lot more catastrophes, but on the other side of that, they always show me that the light is going to win. I have been shown like, I don't want to get too into it, because they always say, like, it's not for most people to know, but there are going to be earthly disasters. I've been shown that a lot, but the reasoning for that is of a higher level again, and it's something that just doing my work as a psychic and seeing the higher level in everything. It allows me to hold that higher vision, again, of understanding, because I see it as like on a human level, we're very reactive, we're emotional, we feel, but on a higher level, the soul is like just breath. It's just like a heartbeat. It's so neutral about everything. So when we can hold a higher perspective and understand that this is all happening for a higher reason, for people to remember of who we are and to take back our power. That's kind of the higher scheme of it. So like they're showing me like a pyramid right now. It's like remembering the top of the pyramid the higher mind and like understanding and holding the light of that, because we come here to remember who we are, and the more people wake up to that, the more it's going to shatter those fear paradigms that we have been under illusion for for centuries. So how can we maintain spiritual balance during this insane time? Because it's one thing to go up to Tibetan, to Tibetan monastery up in the Himalayas. You know, we just eat pure food all day and sit down and meditate for eight or nine hours. Very easy to become, not very easy, but easier to have spiritual enlightenment in that scenario. But the rest of us don't live in that world. Some of us are parents. So I always said to yogis, I'm like, where is there a yogi that had kids? And there's only one that I found, but it's very difficult to have enlightenment when you have to deal with real world events, just normal life, but then now dealing with this turmoil and the wars and the economic stuff and the political stuff and the and everything that's happening to us, how can you maintain spiritual balance in the middle of that kind of hurricane? Yeah, and what's interesting is I had a dream about this a while ago, that spirit answered that question, because I was very much battling between the two worlds, and they showed me that everything that is happening, I think this understanding that, like spirituality is something outside of ourselves, or it is like something we need to transcend and move into a different realm, like the earth experience is the spiritual experience, because everything is spiritual matter. So I see everything in this world as the spiritual experience. And it went from me, you know, going and sitting in circle and ceremony and retreats and traveling all over the world to these events and doing what you were saying, of, kind of like moving up the scale to the mountains and to these spaces of enlightenment, to come to this point where I am now. Of, I have no desire to do any of that, because it's not about. Me finding these height and spiritual experiences. It's getting dirty in the game of life and the reality of this. So I see everything as kind of like a spiritual experience. And that is what's like. We're working towards an understanding. So this paradigm that in order to be spiritual, we have to meditate and have crystals and pray and do all of these things, I really believe, is dramatically incorrect, because everything in this world is is just energy. Everything in this world is a spiritual experience and spiritual game. And I've had that discussion with a lot of my friends who are like coming back to life, back to the world, and seeing that that's the real game, and that's where it really stretches us and gives us that grit. So I don't see the two as separate anymore. Of course, I used to, but I see them as one of the same. So I kind of see it all as part of the game. I see this whole world is just like a game. If there is, you know, if Jesus was here today, or Buddha or Yogananda, or any of these great avatars, you know what I mean, if they were physically here in matter, don't be a smart butt. Okay, see, so if any of these avatars were here today, they would have YouTube channels, wouldn't they? I actually laugh about that so much. I'm like, Jesus was an influencer. Like Jesus was literally like, I was just my ultimate the ultimate influence, ultimate influencer. I was like, thinking this, like a few months ago, I was like, imagining him, just like, have a millions of followers on Instagram. Just like preaching and just like putting up the peace sign and being like, here with Mary Magdalene, like it's it's true. You know, they were all just influential. And I really believe that that awareness of you see, I think Jesus came here to remember, to reflect to us who, to remember who we are, not to praise him as a god or not, to see him as like, worshiping something outside of ourselves. It's the understanding that we are all part of the Prime Creator, and I think that's what we're really starting to understand. So everyone's starting to wake up to that sovereignty, that we are all one and we are all part of that. I mean, I went on like a Bob Marley kick. I love Bob Marley so much. My mom actually hitchhiked across Europe to see him, and I was so jealous. But one love, I literally just listened to that song every day. And I'm like, That is the message. You know, it's like a weaved within a soul. I always see it as this vision spirit shows me of like this green chord, or like a white chord that interconnects us with everything and everyone, like that, a piece of source is in with all within all of us, and we have the ability to connect to anyone and anything, no matter how far it is in the galaxy, because we are all just energy, and we are all connected. And I think that's the real awakening that we're coming here to learn. And I also, too, like Bob Marley, a lot, that concept of one love, and it just it's remarkable. I love to hear what your guides have to say about the shift that's happening between the old systems and the new systems you were speaking of Jesus, His teachings have been slightly, not often, slightly changed since his original just a little bit has been manipulated just a slight bit since he originally was preaching them. But you know that kind of truth of those original teachings, of all the great avatars and all the great masters, you're starting to see cracks in these institutions that were absolutely infallible. I mean, you come from an Irish background. I come from a Latin background, a Latino background, the Catholic Church. You could, oh, my, it was this omnipotent, powerful, just it was the Rock of Gibraltar, like it was unmovable. Never questioned today, not so much. And it seems that I'm using that as an example, as one of those systems that seems to you starting to see the cracks. People are going, No thank you, though, that's not what we really want, and it's happening in every world, from media, Hollywood and the music industry. Is a big shift in politics, there's a big shift in economics, there's a big shift in health. Is a big shift all that stuff. So what are their take on this old system, new system paradigm that we're going through. Yeah, and I love that you said it's a paradigm, because Spirit have shown me the old and new a million times. I've spoken about it in so many YouTube videos as well. And what they're kind of showing me at this point is like. They kind of use the analogy of like, that we have the information is the light. So if we are aware, that is the light. So I'll give the example of like, if we're in a dark, pitch black room and we hear these creepy noises, we're going to be freaked out. We're going to be scared. But if we turn on the light and we see where that noise is coming from, we feel a bit calmer knowing where it originates from. So when we have that awareness, and we have that understanding that in itself, is enough to really start to enhance like, what is happening, but what I've come to learn, and what my guides are starting to continue to tell me now, is, like, it's not about us waiting on the side and just like, waiting for these systems to change because, like, of course, we believe that they are going to change eventually, because we're all kind of waking up to that, but they're still very much concreted in their own way. So it's not about because I've had so many. People and Coles who are just waiting for, like, everyone to just wake up one day, and that's it, and it's just and my guides are like, Ella, that's just not the case. It's just not going to be that way. And they always show me a set of like, spiritual laws, which I can email you, by the way, that they channeled for me, and they were like, what they're really wanting to usher in is a paradigm that we can anchor and hold, whilst these systems are like simultaneously still existing, because it's not about us waiting and sitting on the sideline or, of course, we can fight and do whatever we want, but it's about us anchoring in our own systems. And that's what they keep showing me. So it's like living and breathing in the embodiment of your own systems, regardless if you're working in like a nine to five or you're in the midst of, like, the most like matrixy thing, and you're super awake to it. It's living in your own system. So I can email that to some of the laws that they've shown me, because what they're wanting to do, and they're even showing this now, is like, it's about us anchoring in the new systems, instead of because, like, the first level is awakening to the systems, and the second level is anchoring in your own system while simultaneously. And the more people that remember that, because it's sovereignty, the more collectively it's going to start to shift.
Own systems sovereignity
-
-
hypothes.is hypothes.is
-
Big Daddy Game is hands down my go-to source for everything gaming! The insights are spot on, and the reviews help me decide which games are really worth my time. The strategy guides? Absolute game-changers! Keep up the awesome work, Big Daddy Game!
-
-
game-ace.com game-ace.com
-
Case Studies: Successful Implementation of Storytelling in Game Development
Examples for Successful storytelling
-
Imagine a game with an engrossing narrative. This story births memorable characters and immersive worlds, creating an elaborate universe for players to explore and engage with. These compelling storylines generate a deep-seated affection in players, making them more likely to want to return to these worlds time and time again. This desire cultivates a loyal player base, laying a solid groundwork for developing sequels or spin-offs.
This paragraph reflects what I said earlier in this annotation.
-
an emotionally invested player is more likely to engage in in-game purchases.
PROFIT!
-
It has evolved into a pivotal driver of player retention and monetization
Making a good story for a game can lead to future games expanding upon this story (perhaps using the universe of the game).
-
Allowing players to make decisions that affect the story's outcome can lead to multiple endings
Being able to replay games to find separate endings helps to make the game enjoyable.
-
A critical challenge in game development is striking the right balance between a compelling narrative and enjoyable gameplay.
This in my opinion is the most important yet most overlooked thing in games. In other articles I've read, the developers hired by bigger game companies are told to more focus on gameplay rather than the story elements. This makes the story that they implement not entwine properly with the gameplay so it feels awkward to play.
-
Well-developed characters have their own arcs – they grow, learn, and change as the game progresses.
It's very difficult for a storytelling writer to properly develop each character within their own arcs all at once, hence why we don't see these kinds of games much.
-
Narrative-driven objectives
Sometimes when playing games that include objectives for the player to complete, the objectives start to feel like busy work/fetch quests. While some players love mindless activities in games, it isn't enjoyable for the average player to run back and forth without much engagement.
-
Relatable characters
The thing that storytelling writers struggle with is making relatable characters for their potential players.
-
A well-crafted story can turn a good game into an unforgettable experience, and a memorable experience is what players seek and cherish.
Many of the most memorable experiences I've had while playing games are ones with unique and compelling stories.
-
-
www.sciencedirect.com www.sciencedirect.com
-
‘predatory monetization schemes’ are designed to make players both financially and psychologically committed to a game with a purpose of spending more and more money.
Good to further look into as these 'predatory monetization schemes' could be a point to bring up in how these loot boxes can change the perception of online gambling by posing as a lighter form of online gambling in a way?
-
Concerns have been raised particularly in relation to ‘loot boxes’ that present a controversial form of in-game purchases in pursuit of randomized rewards such as weapons or cosmetic features
Good definition for what a loot box is. Also helps present the loot box as a form of in-game purchase based on luck.
-
-
-
"Years ago, [after a game], the first thing the players do is get their phone, call the wife or their girlfriend, their father or mother. In this moment, the first thing they do is to post something in Instagram.
showcases the shift in just a few years and how important social media has been made
-
-
marginalrevolution.com marginalrevolution.com
-
Three sentences on what I just read,
I believe that BAP is aware of his place in history just like I assume Yuval does. Both authors are not writing as bots recording facts but provide a specialized idological prism to see our current civilization through. Each prisim has its own take, Yuval trying to articulate what the Silicon Valley "Open Conspiracy" types dream of. BAP trying to remind us what it was like to actually be part of history.
The "Why don't CEO's have Harrem's" is the one thing here that is going to stick with me. The women of today are so different from the past. In fact maybe the "Brave New World" reality of nameless sex with strangers and nude play as children is a more desireable world to the Incel, video game, monster can drinking of today.
It seems like the Puritan/Christian sexual practices have really shaped the west into becoming what it is today. I believe most men get their sense of identity from the type of sex they have access to. What's weird about modernity is that we are talking about sex rahter than women with the inherent consideration of children.
This population collapse, as articulated on the Georga Guide Stones, is going to be interesting.
What is the Opposite of "The Open Conspiracy"
-
-
www.ncbi.nlm.nih.gov www.ncbi.nlm.nih.gov
-
several payoff schedules (slot machines, roulette, and dice game of craps) have a probability of winning close to 50%, so that they are expected to elicit maximal DA release and, therefore, reinforce the act of gambling.
!!!!!!!!!!
-