I believe a case can be made–indeed a case has been made by others, by historians of Apple and hacker culture–that “Secrets of the Little Blue Box,” a story I wrote for Esquire back in 1971 about “phone phreaks” and the first computer hackers (it was only the second magazine story I’d ever had published) played a crucial role in the careers of the founders of Apple and of a legendary ur-hacker I made famous who went by the name of Captain Crunch.
- Last 7 days
-
slate.com slate.com
-
-
-
An FPGA with the weights in memory and a wire looping output back to input could just sit there, executing SUBLEQ programs. Just a transformer being a transformer being a computer.
大多数人认为计算机需要复杂的CPU架构和操作系统,但作者认为一个简单的FPGA加上循环连接的transformer权重就可以构成一个完整的计算机。这挑战了我们对计算机本质的理解,暗示transformer架构可能比传统CPU更接近计算的本质。
-
-
-
For example, this could bring a five hour (300 minute) time horizon down to a three minute time horizon. But while the time horizons are much shorter, the growth rate is about the same as the METR's main results, with roughly two doublings each year.
作者提到视觉计算机使用任务的时间跨度可能比主要结果缩短40-100倍,但增长率相似,约为每年翻两倍。这一数据点揭示了AI在不同任务领域的能力差异,以及计算机使用任务的特殊挑战,这对理解AI自动化进程的复杂性提供了重要见解。
-
- May 2026
-
glassmanlab.seas.harvard.edu glassmanlab.seas.harvard.edu
-
At the core of this revolution was the ability to flexibly define and execute computer programs—sequences of logical operations executed by a computer.
-
- Apr 2026
-
www.feldera.com www.feldera.com
-
Humans are not a good target for calm technology.
大多数人认为技术的目标应该是让人类更容易使用和理解。但作者提出相反观点:人类不适合作为'平静技术'的目标,因为当前的AI设计要求人类持续监督和互动,这与平静技术的本质相悖。
-
Humans are not a good target for calm technology.
大多数人认为技术应该适应人类的工作方式和认知习惯。但作者认为人类不适合作为'平静技术'的目标,因为人类需要高认知负荷的交互。这一观点挑战了以用户为中心的设计原则,暗示我们应该重新思考人机交互的基本模式。
-
-
mp.weixin.qq.com mp.weixin.qq.com
-
模型能不能承担一部分原本属于机器运行本身的职责。
这是一个极具洞察力的观点,它挑战了我们对AI和计算机关系的传统理解。如果模型能够承担部分机器运行职责,将从根本上改变计算范式,使AI从使用计算机转变为成为计算机本身,这可能是计算领域的下一个重大转变。
-
- Mar 2026
-
glassmanlab.seas.harvard.edu glassmanlab.seas.harvard.edu
-
For example, word predictionusage may not be beneficial if the word suggestions are poorly suited to the individual’s language orif the user can type words faster than the time required to scan and select among word suggestions.
-
The effect of such automation critically dependson how well its design appreciates the actor’s unique capabilities.
-
Text entry can also be seen as a task where different subtasks are shared between the human and the computer (Chapter 20).
a statement that describes a type of user task
-
One example is autocorrect, which automatically corrects typing errors while the user is typing. Another example is the use of word predictions, which allow the user to select a word from a set of word suggestions instead of typing out the word in full.
sentence describing examples of a concept
-
An interactive AI system can possess an objective function it pur-sues when acting, for example, when correcting a character it flags as a typo.
-
- Jan 2026
-
jacobin.de jacobin.de
-
Vielmehr wird in der modernen Gesellschaft erwartet, dass man online präsent ist. Man braucht beispielsweise immer häufiger ein Online-Profil, um sich auf eine Stelle zu bewerben. Andernfalls kann man praktisch nicht am modernen Leben teilhaben.
-
- Dec 2025
-
warburg.sas.ac.uk warburg.sas.ac.uk
-
In 1977, social psychologist James Gibson coined the term “affordance” to denote “action possibilities provided to the actor by the environment”.[2] A decade later, Donald Norman introduced affordances to the field of object design in his well-known book The Psychology of Everyday Things (1988), after which the concept quickly made its way into all corners of the humanities and social sciences, including the study of Human-Computer Interaction (HCI).
-
- Sep 2025
-
-
TDP
TPD is "Thermal Design Power" — the maximum amount of heat that a computer component (like a CPU, GPU or system on a chip) can generate and that its cooling system is designed to dissipate during normal operation.
-
- Apr 2025
-
Local file Local file
-
Just as themachine age transformed an economy of farm laborers and artisansinto one of combine harvesters and assembly lines, so the technology
-
- Feb 2025
-
www.ted.com www.ted.com
-
https://www.ted.com/talks/matt_ridley_when_ideas_have_sex
Here's the reference for TB, from our discussion
-
- Jan 2025
-
groups.csail.mit.edu groups.csail.mit.edu
-
for - paper - Man-Computer Symbiosis - J.C.R. Licklider - 1960 - referred by - Gyuri
-
- Sep 2024
-
dl.acm.org dl.acm.org
-
Shneiderman’s design principles for creativity support tools
Ben Shneiderman's work is deeply influential in HCI; his work has assisted in creating strong connections between tech and creativity, especially when applied to fostering innovation.
his 2007 national science foundation funded report on creativity support tools, led by UMD, provides a seminal overview of the definitions of creativity at that time.
-
Boden’s conception of creativity as “exploration and play”
Margaret Boden, research professor at University of Sussex, has provided pivotal work in the exploration of creativity using interdisciplinary research across music, game, story, physics, and artificial intelligence to explore human creativity in arts, science, and life.
-
-
www.gnu.org www.gnu.org
-
For instance, the AMT functionality in recent Intel processors runs nonfree software that can talk to Intel remotely. Unless disabled, this makes the system disloyal.
-
-
www.codeotaku.com www.codeotaku.com
-
github.com github.com
-
If you'd like another method to do the waiting for you, e.g. Kernel.select, you can use Timers::Group#wait_interval to obtain the amount of time to wait. When a timeout is encountered, you can fire all pending timers with Timers::Group#fire
This is another way of achieving concurrency (progress made while waiting for other things) besides wrapping the timer's sleep in a separate thread like https://github.com/rubyworks/facets/blob/main/lib/standard/facets/timer.rb does.
-
- Jul 2024
-
paddyleflufy.substack.com paddyleflufy.substack.com
-
If a baby born today and a baby born 30,000 years ago were swapped at birth, they would each grow up as normal people in their new cultures.
for - similar to - quote - Ronald Wright - progress trap - computer metaphor
similar to - quote - Ronald Wright - progress trap - computer metaphor - Ronald Wright's famous quote on the computer metaphor really gets to the essence of things - how much of the meta-poly-perma-crisis can be explained by the unprecedented mismatch between the rate of - biological evolution of our species - cultural evolution of our species - Culture is the major and possibly most signficant differentiator between the person alive 50,000 years ago and the one alive today.
reference - quote - Ronald Wright - computer metaphor - https://hyp.is/go?url=https%3A%2F%2Fwww.goodreads.com%2Fwork%2Fquotes%2F321797-a-short-history-of-progress&group=world
-
-
www.goodreads.com www.goodreads.com
-
for - Ronald Wright - computer metaphor - quote - Ronald Wright - computer metaphor
-
- Jun 2024
-
www.geeksforgeeks.org www.geeksforgeeks.org
-
Data structures are an integral part of computers used for the arrangement of data in memory.
The importance of data structures (related to memory)
-
- May 2024
-
-
if you look for those in the genome you will not find them 00:05:26 anywhere in the genome
for - comparison - genome coding to computer program
-
- Apr 2024
-
archive.org archive.org
-
Lisa, Apple's demonstration of its leadership,in bringing technology to the knowledge worker.
Use of "knowledge worker" in a 1983 advertisement for the Lisa computer from Apple.
-
Lisa Soul Of A New Machine. Advertisement, 1983. http://archive.org/details/lisa-soul-of-a-new-machine.
-
[Narrator]: The Cluttered Desk, Index Card,file folders, the in-out basket, the calculator.These are the tools of the office professional's past.Since the dawn of the computer age, better machines have always meant bigger and more powerful.But the software could not accommodate the needs of office professionals who are responsiblefor the look, shape and feel of tomorrow.
In 1983, at the dawn of the personal computer age, Apple Inc. in promotional film entitled "Lisa Soul Of A New Machine" touted their new computer, a 16-bit dual disk drive "personal office system", as something that would do away with "the cluttered desk, index cards, file folders, the in-out basket, [and] the calculator." (00:01)
Some of these things moved to the realm of the computer including the messy desk(top) now giving people two messy desks, a real one and a virtual one. The database-like structure of the card index also moved over, but the subjective index and its search power were substituted for a lower level concordance search.
30 years on, for most people, the value of the database idea behind the humble "index card" has long since disappeared and so it seems here as if it's "just" another piece of cluttery paper.
Appreciate the rosy framing of the juxtaposition of "past" and "future" jumping over the idea of the here and now which includes the thing they're selling, the Lisa computer. They're selling the idealized and unclear future even though it's really just today.
Tags
- neologisms
- Apple Computers
- watch
- personal office system
- Bill Atkinson
- John Couch
- Rich Page
- information age
- personal knowledge management
- office supplies
- knowledge workers
- media studies
- past vs. future
- techno-utopianism
- Wayne Rosing
- card index for business
- References
- Lisa (computer)
- Steve Jobs
- intellectual history
Annotators
URL
-
- Dec 2023
-
iopscience.iop.org iopscience.iop.org
-
-
for: AI, Anirban Bandyopadhyay, brain gel, AI - gel computer
-
title: A general-purpose organic gel computer that learns by itself
- author
- Anirban Bandyopadhyay
- Pathik Sahoo
- et al.
- date: Dec. 6, 2023
- publication: IOPScience
-
DOI: 10.1088/2634-4386/ad0fec
-
ABSTRACT
- To build energy minimized superstructures, self-assembling molecules explore astronomical options, colliding ∼10 to 9th power molecules s to power−1. -Thusfar, no computer has used it fully to optimize choices and execute advanced computational theories only by synthesizing supramolecules.
- To realize it,
- first, we remotely re-wrote the problem in a language that supramolecular synthesis comprehends.
- Then, all-chemical neural network synthesizes one helical nanowire for one periodic event. These nanowires self-assemble into gel fibers mapping intricate relations between periodic events in any-data-type,
- the output is read instantly from optical hologram.
- Problem-wise, self-assembling layers or neural network depth is optimized to chemically simulate theories discovering invariants for learning.
- Subsequently, synthesis alone solves classification, feature learning problems instantly with single shot training.
- Reusable gel begins general-purpose computing that would chemically invent suitable models for problem-specific unsupervised learning. Irrespective of complexity,
- keeping fixed computing time and power, gel promises a toxic-hardware-free world.
-
-
-
arxiv.org arxiv.org
-
TOKEN MERGING: YOUR VIT BUT FASTER
-
-
docdrop.org docdrop.org
-
we are certainly special I mean 00:02:57 no other animal rich the moon or know how to build atom bombs so we are definitely quite different from chimpanzees and elephants and and all the rest of the animals but we are still 00:03:09 animals you know many of our most basic emotions much of our society is still run on Stone Age code
-
for: stone age code, similar to - Ronald Wright - computer metaphor, evolutionary psychology - examples, evolutionary paradox of modernity, evolution - last mile link, major evolutionary transition - full spectrum in modern humans, example - MET - full spectrum embedded in modern humans
-
comment
-
insights
- evolutionary paradox of modernity
- modern humans , like all the living species we share the world with, are the last mile link of the evolution of life we've made it to the present, so all species of the present are, in an evolutionary sense, winners of their respective evolutionary game
- this means that all our present behaviors contain the full spectrum of the evolutionary history of 4 billion years of life
- the modern human embodies all major evolutionary transitions of the past
- so our behavior, at all levels of our being is a complex and heterogenous mixture of evolutionary adaptations from different time periods of the 4 billion years that life has taken to evolve.
- Some behaviors may have originated billions of years ago, and others hundred thousand years ago.
- evolutionary paradox of modernity
-
Examples: humans embody full spectrum of METs in our evolutionary past
- fight and flight response
- early hominids on African Savannah hundreds of thousands to millions of years ago when hominids were predated upon by wild predators
- cancer
- normative intercell communication breaks down and reverts to individual cell behavior from billions of years ago
- see Michael Levin's research on how to make metastatic cancer cells return to normative collective, cooperative behavior
- normative intercell communication breaks down and reverts to individual cell behavior from billions of years ago
- children afraid to sleep in the dark
- evolutionary adaptation against dangerous animals that might have hid in the dark - dangerous insiects, snakes, etc, which in the past may have resulted in human fatalities
- obesity
- hunter gatherer hominid attraction to rich sources of fruit. Eating as much of it as we can and maybe harvesting as much as we can and carrying that with us.
- like squirrels storing away for the winter.
- hunter gatherer hominid attraction to rich sources of fruit. Eating as much of it as we can and maybe harvesting as much as we can and carrying that with us.
- fight and flight response
-
-
- Oct 2023
-
images.designworldonline.com.s3.amazonaws.com images.designworldonline.com.s3.amazonaws.com
-
The Sketchpad system, byeliminating typed statements (except for legends) in favor of line draw-ings, opens up a new area of man-machine communication
-
- Sep 2023
-
www.asianefficiency.com www.asianefficiency.com
-
n general, only create new folders if you find yourself repeatedly coming back to save similar files in the same place, only to find that it doesn’t exist yet. You’ll know when it is time to create another level in the hierarchy rather than creating a vast extensive multi-layered tree before you need it.
Just like my book classification system, start broad and go more granular only if need be. Is future-proof and doesn't require buttloads of time.
-
So when you’re naming that phone bill, think about how you might look for it. Probably: By date (I want the January 2023 phone bill) By company (I want the XYZCorp phone bill) By type of document (I want a phone bill)
Naming Scheme should support findability.
-
Easy to File– You don’t want your filing system to be a huge, hierarchical maze. You want it to be fast and easy to save files so your system does not cause friction. Easy to Find – You want your system to make it easy to find the file or folder you need, either by poking through folders or using search. Reusable – Where possible, you want to use re-usable templates and naming conventions, both of which support the previous two goals.
Goals of good organization system for computer files
-
-
www.youtube.com www.youtube.com
-
(~5:00) PARA is suitable for organizing files for deliverables.
Projects => On Top of Mind Areas => Longer Term Commitments Resources => Future Reference (Research Material, current Interests) Archive => Completed or on Hold
Questions: 1. In which project will this be most useful? 2. In which area will be most helpful? 3. Which resource does this belong to? If none of these ( in prioritization order), then the archives.
See Obsidian for example (screenshot)
-
(3:20) A good folder structure must mimic the way one works and make it easy to access the files one needs.
Tags
Annotators
URL
-
- Aug 2023
-
-
Thanks Sascha for an excellent primer on the internal machinations of our favorite machines beyond the usual focus on the storage/memory and indexing portions of the process.
Said another way, a zettelkasten is part of a formal logic machine/process. Or alternately, as Markus Krajewski aptly demonstrates in Paper Machines (MIT Press, 2011), they are early analog storage devices in which the thinking and logic operations are done cerebrally (by way of direct analogy to brain and hand:manually) and subsequently noted down which thereby makes them computers.
Just as mathematicians try to break down and define discrete primitives or building blocks upon which they can then perform operations to come up with new results, one tries to find and develop the most interesting "atomic notes" from various sources which they can place into their zettelkasten in hopes of operating on them (usually by juxtaposition, negation, union, etc.) to derive, find, and prove new insights. If done well, these newly discovered ideas can be put back into the machine as inputs to create additional newer and more complex outputs continuously. While the complexity of Lie Algebras is glorious and seems magical, it obviously helps to first understand the base level logic before one builds up to it. The same holds true of zettelkasten.
Now if I could only get the
printfportion to work the way I want...
-
- Jul 2023
-
www.truthbrush.com www.truthbrush.com
-
Truthbrush
Odd that it doesn't support Windows, so you need a separate OS just to track tooth brushing even if you have a bunch of real computers around.
Tags
Annotators
URL
-
- Jun 2023
-
www.reddit.com www.reddit.com
-
As Chris Aldridge says, for centuries the Zettelkasten approach was the standard and universal method for producing books and articles - until personal computers took over. Nearly every serious work ever published before the 1980s was drafted either with index cards or paper slips, or else with notebooks in a commonplace style. Every writer had their own take on these two options, but that’s what they all used. Then, in a single decade, word processing software took over. These days, most writers use something like Microsoft Word or Google Docs (just try persuading your publisher you’re not giving them a docx file). Scrivener became popular because it critiqued the ‘endless roll of paper’ model and reverted to an index card interface of sorts. But it remained a niche.Today, you either thrive on that word processor model or you don’t. I really don’t, which is why I’ve invested effort, as you have, in researching previous writing workflows, older than the all-conquering PC of the late 1980s and early 90s. At the same time, new writing tools are challenging the established Microsoft way, but in doing so are drawing attention to the fact that each app locks the user into a particular set of assumptions about the drafting and publishing process.The current academic scene is a brutal war to publish or perish. It’s not unusual for a researcher to write or co-write 30-40 peer-reviewed articles per year. General publishing is also frenetic. In the UK, 20 books are published every hour of the day. It all makes Luhmann’s ‘prolific’ output look lazy. Now though, AI is blowing the entire field apart. From now on, prolific writing is what computers do best. There’s no reason not to publish 20,000 books per hour. Soon enough, that will be the output per ‘author’. Where the pieces will eventually land is anyone’s guess. For example, the workflow of the near future might involve one part writing and nineteen parts marketing. Except that AI has got that sewn up too. Meanwhile, until the world ends, I’m just having fun doing my thing.
Before the advent of the computer, the use of a zettelkasten or commonplace book to research was "common place".
What happened with the transition? Perhaps the methodology was lost in the transition, people just dumping things into a word file?
-
-
discussions.apple.com discussions.apple.com
-
You would need to have a phone number in order to create an Apple ID.
Wow, you can't create an Apple ID without assigning yourself a telephone tracking number.
Incredible.
-
- May 2023
-
www.computerhope.com www.computerhope.com
-
Underscore Updated: 05/01/2023 by Computer Hope Alternatively known as a low line, low dash, and understrike, the underscore ( _ ) is a symbol found on the same keyboard key as the hyphen. The picture shows an example of an underscore at the beginning and end of the word "Underscore."
Tags
Annotators
URL
-
-
infomesh.net infomesh.net
-
almost all beginners to RDF go through a sort of "identity crisis" phase, where they confuse people with their names, and documents with their titles. For example, it is common to see statements such as:- <http://example.org/> dc:creator "Bob" . However, Bob is just a literal string, so how can a literal string write a document?
This could be trivially solved by extending the syntax to include some notation that has the semantics of a well-defined reference but the ergonomics of a quoted string. So if the notation used the sigil
~(for example), then~"Bob"could denote an implicitly defined entity that is, through some type-/class-specific mechanism associated with the string "Bob".
-
-
aduros.com aduros.com
-
configuring xterm
Ugh. This is the real problem, I'd wager. Nobody wants to derp around configuring the Xresources to make xterm behave acceptably—i.e. just to reach parity with Gnome Terminal—if they can literally just open up Gnome Terminal and use that.
I say this as a Vim user. (Who doesn't do any of the suping/ricing that is commonly associated with Vim.)
It is worth considering an interesting idea, though: what if someone wrote a separate xterm configuration utility? Suppose it started out where the default would be to produce the settings that would most closely match the vanilla Gnome Terminal (or some other contemporary desktop default) experience, but show you the exact same set of knobs that xterm's modern counter part gives you (by way of its settings dialog) to tweak this behavior? And then beyond that you could fiddle with the "advanced" settings to exercise the full breadth of the sort of control that xterm gives you? Think Firefox preferences/settings/options vs. dropping down to about:config for your odd idiosyncrasy.
Since this is just an Xresources file, it would be straightforward to build this sort of frontend as an in-browser utility... (or a triple script, even).
-
- Mar 2023
-
cocktailpeanut.github.io cocktailpeanut.github.ioDalai1
-
컴퓨터에서 LLAMMA AI를 실행하는 매우 간단한 방법인 Dalai cpp 파일 빌드, github 복제, 파일 다운로드 등을 귀찮게 할 필요가 없음. 모든 것이 자동화 됨
-
- Feb 2023
-
dl.acm.org dl.acm.org
-
Döring, Tanja, and Steffi Beckhaus. “The Card Box at Hand: Exploring the Potentials of a Paper-Based Tangible Interface for Education and Research in Art History.” In Proceedings of the 1st International Conference on Tangible and Embedded Interaction, 87–90. TEI ’07. New York, NY, USA: Association for Computing Machinery, 2007. https://doi.org/10.1145/1226969.1226986.
This looks fascinating with respect to note taking and subsequent arranging, outlining, and use of notes in human computer interaction space for creating usable user interfaces.
-
-
docdrop.org docdrop.org
-
we're running 21st century software on hardware last upgraded fifty thousand years ago or mor
= Ronald Wright quote - "we're running 21st century software on hardware last upgraded fifty thousand years ago or more "
-
-
www.washingtonpost.com www.washingtonpost.com
-
Internet ‘algospeak’ is changing our language in real time, from ‘nip nops’ to ‘le dollar bean’ by [[Taylor Lorenz]]
shifts in language and meaning of words and symbols as the result of algorithmic content moderation
instead of slow semantic shifts, content moderation is actively pushing shifts of words and their meanings
article suggested by this week's Dan Allosso Book club on Pirate Enlightenment
-
-
wordcraft-writers-workshop.appspot.com wordcraft-writers-workshop.appspot.com
-
Wordcraft Writers Workshop by Andy Coenen - PAIR, Daphne Ippolito - Brain Research Ann Yuan - PAIR, Sehmon Burnam - Magenta
cross reference: ChatGPT
-
- Jan 2023
-
-
I attended this live this morning from 9:20 - 10:45 AM
-
-
stackoverflow.com stackoverflow.com
-
I suspect that this is an NP-hard problem. Would you prefer a greedy solution, or a computationally infeasible one?
-
-
docdrop.org docdrop.org
-
how important is the concrete syntax of their language in contrast to
how important is the concrete syntax of their language in contrast to the abstract concepts behind them what I mean they say can someone somewhat awkward concrete syntax be an obstacle when it comes to the acceptance
-
- Dec 2022
-
news.ycombinator.com news.ycombinator.com
-
programs with type errors must still be specified to have a well-defined semantics
Use this to explain why Bernhardt's JS wat (or, really, folks' gut reaction to what they're seeing) is misleading.
-
- Nov 2022
-
theinformed.life theinformed.life
-
Mark: Cathy Marshall at Xerox PARC originally started speaking about information gardening. She developed an early tool that’s the inspiration for the Tinderbox map view, in which you would have boxes but no lines. It was a spatial hypertext system, a system for connecting things by placing them near each other rather than drawing a line between them. Very interesting abstract representational problem, but also it turned out to be tremendously useful.
Cathy Marshall was an early digital gardener!
-
-
-
“In order to talk to each other, we have to have words, and that’s all right. It’s a good idea to try to see the difference, and it’s a good idea to know when we are teaching the tools of science, such as words, and when we are teaching science itself,” Feynman said.
Maths, Logic, Computer Science, Chess, Music, and Dance
A similar observation could be made about mathematics, logic, and computer science. Sadly, public education in the states seems to lose sight that the formalisms in these domains are merely the tools of the trade and not the trade itself (ie, developing an understanding of the fundamental/foundational notions, their relationships, their instantiations, and cultivating how one can develop capacity to "move" in that space).
Similarly, it's as if we encourage children that they need to merely memorize all the movements of chess pieces to appreciate the depth of the game.
Or saying "Here, just memorize these disconnected contortions of the hand upon these strings along this piece of wood. Once you have that down, you've experienced all that guitar, (nay, music itself!) has to offer."
Or "Yes, once, you internalize the words for these moves and recite them verbatim, you will have experienced all the depth and wonder that dance and movement have to offer."
However, none of these examples are given so as to dismiss or ignore the necessity of (at least some level of) formalistic fluency within each of these domains of experience. Rather, their purpose is to highlight the parallels in other domains that may seem (at first) so disconnected from one's own experience, so far from one's fundamental way of feeling the world, that the only plausible reasons one can make to explain why people would waste their time engaging in such acts are 1. folly: they merely do not yet know their activities are absurd, but surely enough time will disabuse them of their foolish ways. 2. madness: they cannot ever know the absurdity of their acts, for "the absurd" and "the astute" are but two names for one and the same thing in their world of chaos. 3. apathy: they in fact do see the absurdity in their continuing of activities which give them no sense of meaning, yet their indifference insurmountably impedes them from changing their course of action. For how could one resist the path of least resistance, a road born of habit, when one must expend energy to do so but that energy can only come from one who cares?
Or at least, these 3 reasons can surely seem like that's all there possibly could be to warrant someone continuing music, chess, dance, maths, logic, computer science, or any apparently alien craft. However, if one takes time to speak to someone who earnestly pursues such "alien crafts", then one may start to perceive intimations of something beyond their current impressions
The contorted clutching of the strings now seems... coordinated. The pensive placement of the pawns now appears... purposeful. The frantic flailing of one's feet now feels... freeing. The movements of one's mind now feels... marvelous.
So the very activity that once seemed so clearly absurd, becomes cognition and shapes perspectives beyond words
-
-
www.quora.com www.quora.com
-
What does 'passing an argument' mean in programming?You have a grinder that will grind anything that you pass on to her. You give her Rice. She grind it. You give her wheat. She grind it. You give her a Justin Bieber song CD. She grind it. She grinds every thing that you hand over to her. In programming, we create function that does the stuff we need. Say add, subtract, multiply or print the stuff that you pass on to it. Then we pass on stuff upon which the function will operate and return us the results. This process of passing the 'stuff' to be processed is referred to as passing an 'argument' in programming. Thank You.
-
-
www.google.com www.google.com
-
An argument is a way for you to provide more information to a function. The function can then use that information as it runs, like a variable. Said differently, when you create a function, you can pass in data in the form of an argument, also called a parameter.
argument and parameter
Tags
Annotators
URL
-
-
www.inkandswitch.com www.inkandswitch.com
-
People should be able to teach their computers the meaning behind their data
-
- Oct 2022
-
en.wikipedia.org en.wikipedia.org
-
https://en.wikipedia.org/wiki/Read%E2%80%93eval%E2%80%93print_loop
aliases: interactive toplevel, language shell
read-eval-print loop (REPL)
-
- Aug 2022
-
roadtoreality.substack.com roadtoreality.substack.com
-
I add mass to each of these… mental clusters? planetary bodies in the Mindscape? by hyperlinking the phrase as I type.
Nothing particular to what's described here, but this gives me an idea for a design of an efficient IME that doesn't require manually adding the brackets or even starting with an a priori intention of linking when you begin writing the to-be-linked phrase. The idea is that you start typing something, realize you want to link it, and then do so—from the keyboard, without having to go back and insert the open brackets—at least not with ordinary text editing commands. Here's how it goes:
Suppose you begin typing "I want to go to Mars someday", but after you type "Mars", you realize you want to link "go to Mars", as this example shows. The idea is that, with your cursor positioned just after "Mars", you invoke a key sequence, use Vim-inspired keys
bandw(orhandlfor finer movements) to select the appropriate number of words back from your current position, and then complete the action by pressing Enter.This should work really well here and reasonably well in the freeform editor originally envisioned for w2g/graph.global.
-
- Jul 2022
-
julian.bearblog.dev julian.bearblog.dev
-
#Software #Hardware #Technology #Programming #Internet #Web Development #Data #Beginner Tutorial #Computer Science #Computers #Engineering
-
-
www.youtube.com www.youtube.com
-
Computer science is the subject that studies what computers can do and investigates the best ways you can solve the problems of the world with them. It is a huge field overlapping pure mathematics, engineering and many other scientific disciplines. In this video I summarise as much of the subject as I can and show how the areas are related to each other. #computer #science #DomainOfScience
-
-
Local file Local file
-
Ben Shneiderman
https://en.wikipedia.org/wiki/Ben_Shneiderman
Originated the treemap within the computer interface.
-
-
en.wikipedia.org en.wikipedia.org
-
His major work in recent years has been on information visualization, originating the treemap concept for hierarchical data.[30]
-
-
Local file Local file
-
An instance may be given of the necessity of the “ separate sheet ” system.Among the many sources of information from which we constructed our bookThe Manor and the Borough were the hundreds of reports on particular boroughsmade by the Municipal Corporation Commissioners in 1835 .These four hugevolumes are well arranged and very fully indexed; they were in our own possession;we had read them through more than once; and we had repeatedly consulted themon particular points. We had, in fact, used them as if they had been our own boundnotebooks, thinking that this would suffice. But, in the end, we found ourselvesquite unable to digest and utilise this material until we had written out every oneof the innumerable facts on a separate sheet of paper, so as to allow of the mechanicalabsorption of these sheets among our other notes; of their complete assortment bysubjects; and of their being shuffled and reshuffled to test hypotheses as to suggestedco-existences and sequences.
Webb's use case here sounds like she's got the mass data, but that what she really desired was a database which she could more easily query to do her work and research. As a result, she took the flat file data and made it into a manually sortable and searchable database.
-
-
gist.github.com gist.github.com
-
5.11 Convert your principles into algorithms and have the computer make decisions alongside you.
5.11 Convert your principles into algorithms and have the computer make decisions alongside you.
-
-
-
lacol.sites.haverford.edu lacol.sites.haverford.edu
-
Adversely, the Topics feature did not seem super helpful which was surprising because I initially thought that this feature would be helpful, but it just did not seem super relevant or accurate. Maybe this is because as a work of literature, the themes of the play are much more symbolic and figurative than the literal words that the play uses. Perhaps this function would work better for text that is more nonfiction based, or at least more literal.
I read your Voyant analysis of Henrik Ibsen's "A Doll's House," and I think we almost pick the same tools that we believe to be crucial for our text analysis. Like you, I mostly visualize my chosen literary work with Cirrus, Terms, Berry, and Trends. I also use links to ?look into how these words are used interdependently to contextualize the story told. I also had difficulty understanding how functions like Topics would benefit my understanding of the texts on a layered and complex level. I checked and thought maybe the problem was with the word count of the document. By default setting, Topics generates the first 1000 words in a document, and A Doll's House has 26210 words. In order to use this tool in the most efficient way possible, you can try to use the Topics slider ( the scroll bar) to adjust the number of topics you want to generate (max is 200). I have read A Doll's House before, so I couldn't speak for those who haven't. However, the clusters of chosen terms hint to me that this fiction deals with bureaucracy and finance via repeated words like "works," "money," and "paper." I can also recognize some words classified as names, so many characters are involved in the story. There is also a vague clue of the story's setting, which is during the winter season, from the repetition of the word "Christmas." It appears that someone is getting angry at someone for their wrongdoings, and this drama occurs in a family. While Topics cannot give me a complete storyline, it gives me a good chunk of puzzles to piece together the core gist of the story. It happened to me when I analyzed Herman Melville's Moby Dick. Words like "whale," "sea," "sailor," and "chase" allowed me to make a reasonable assumption that there was a group of sailors that went after a giant whale in the sea. I still prefer to use other tools, but that was how I utilized Topics for my knowledge of the text. I agree that text with more literal content, like self-help books, would definitely yield better results with Voyant Tools' Topics.
-
- Jun 2022
-
dlsanthology.mla.hcommons.org dlsanthology.mla.hcommons.org
-
Thus flexibility is an important virtue in computer-assisted textual analysis, and testing a project on a subset of texts or methods can avoid wasted effort.
Flexibility has almost become a sought-after characteristics of any projects ever conducted in this world, let alone those that belong to the school of humanities. Any individual or group entering a long-term project should be aware that predicting the outcome of the project is never a part of their project. It's impossible to identify and avoid surprise factors on a long road, but it's definitely possible to have an open mindset that's ready fpr any difficulty coming along the way and for brainstorming solutions that resolve this "shock". In many cases, these unexpected variables are what that renders the project memorable and special and sustainable and valid and reliable. In many cases, changing the initial direction of the project when faced with these unforeseen elements are for the better and produce even better results. Testing out different methods on textual analysis is a particularly great advice for those who are bound to carry a project in the coming future.
-
-
introtcs.org introtcs.org
- May 2022
-
uni-bielefeld.de uni-bielefeld.de
-
In explaining his approach, Luhmann emphasized, with the first stepsof computer technology in mind, the benefits of the principle of “multiple storage”: in the card index itserves to provide different avenues of accessing a topic or concept since the respective notes may be filedin different places and different contexts. Conversely, embedding a topic in various contexts gives rise todifferent lines of information by means of opening up different realms of comparison in each case due tothe fact that a note is an information only in a web of other notes. Furthermore it was Luhmann’s intentionto “avoid premature systematization and closure and maintain openness toward the future.”11 His way oforganizing the collection allows for it to continuously adapt to the evolution of his thinking and his overalltheory which as well is not conceptualized in a hierarchical manner but rather in a cybernetical way inwhich every term or theoretical concept is dependent on the other.
While he's couching it in the computer science milieu of his day, this is not dissimilar to the Llullan combinatorial arts.
-
-
ece.osu.edu ece.osu.edu
-
Robert Fenton, Electrical and Computer Engineering Professor Emeritus, pioneered the technology for the first wave of self-driving cars.
I had Fenton for a class once and during a lecture he asked a question of the class. A student raised his hand and answered. Professor Fenton listened and asked the class "Does anyone else agree that his answer is correct?"
About 85% of the students in the large lecture hall raised their hands.
He paused, shook his head, and said "Well, then I'm afraid you're all going to fail." Then he turned around and went back to writing on the chalkboard.
Tags
Annotators
URL
-
-
www.w3.org www.w3.org
-
The datatype is appended to the literal through a ^^ delimiter.
Were parens taken?
-
- Apr 2022
-
-
In his manuscript, Harrison spoke of machina with respect to his filing cabinet and named his invention ‘Ark of Studies’. In rhetorical culture, ‘ark’ had been a metaphor that, among many others, denoted the virtual store-house that orators stocked with vivid images of memorable topics (res) and words (verba). In Harrison’s manuscript, ‘ark’ instead became a synonym for ‘mechanical’ memory. In turn, in the distinction between natural and artificial memory, consciousness was compelled to leave its place and to shift to the op-posing side.
Thomas Harrison used the word machina to describe his 'Ark of Studies', a filing cabinet for notes and excerpts from other works. This represents part of a discrete and very specific change on the continuum of movement from the ars memoria (artificial memory) to the ars excerptendi (note taking). Within the rhetorical tradition relying on creating memorable images for topics (res) and words (verba) the idea of an ark was often used as a memory palace as seen in Hugh of St. Victor's De arca Noe mystica, or ‘‘The Ark of Noah According to the Spiritual Method of Reading" (1125–30). It starts the movement from natural and artificial memory to a form of external and mechanical memory represented by his physical filing cabinet.
Reference Yates and Carruthers for Hugh of St. Victor.
-
-
runestone.academy runestone.academy
-
An alternative definition for computer science, then, is to say that computer science is the study of problems that are and that are not computable, the study of the existence and the nonexistence of algorithms.
definition of computer science
-
Computer science is the study of problems, problem-solving, and the solutions that come out of the problem-solving process. Given a problem, a computer scientist’s goal is to develop an algorithm, a step-by-step list of instructions for solving any instance of the problem that might arise. Algorithms are finite processes that if followed will solve the problem. Algorithms are solutions.
Computer science definition
-
- Mar 2022
-
www21.in.tum.de www21.in.tum.de
-
Exercises
2.1.b
Counterexample: \(\to := {(a, c), (b, c)}\)
2.3
\(a \to b\) iff \(a\) encodes Turing machine \(M_a\) and \(b\) encodes a valid terminating computation (sequence of states) of \(M_a\).
2.9
Let \(|w|_a := \varphi_a(w)\).
\(\varphi(w) := 3^{|w|_a} 2^{|w|_b}\)
Proof
- Let \(u \to_1 v\). Then \(\varphi(v) = 3^{|v|_a} 2^{|v|_b} = 3^{|u|_a+1} 2^{|u|_b-2} = 3^{|u|_a} 2^{|u|_b} \frac{3}{4} = \varphi(u) \frac{3}{4} < \varphi(u)\).
- Let \(u \to_2 v\). Then \(\varphi(v) = 3^{|v|_a} 2^{|v|_b} = 3^{|u|_a-1} 2^{|u|_b+1} = 3^{|u|_a} 2^{|u|_b} \frac{2}{3} = \varphi(u) \frac{2}{3} < \varphi(u)\).
2.17
No.
Let \(a > b\). Then \([b^n a | n \in [0, 1, \ldots]]\) is an infinite chain according to \(>_{Lex}\).
Note: This exercise completes the discussion of Lemma 2.4.3.
4.2
Let \(s, t\) be terms. Run BFS from \(s\) using \(\leftrightarrow^E\). If \(t\) is encountered, conclude that \(s \approx_E t\). If the BFS finishes enumerating the equivalence class without encountering \(t\), conclude that \(\lnot s \approx_E t\).
4.4
Let \(x \in Var(r) \setminus Var(l)\). Let \(p\) be a position of \(x\) in \(r\).
Infinite chain:
- \(t_0 = x\)
- \(t_{i+1} = r[t_i]_p\)
4.18
- a
- Unifier: \({x \to h(a), y \to h(a)}\)
- Matcher: \({x \to h(a), y \to x}\)
- b
- Unifier: Unsolvable
- Matcher: \({x \to h(x), y \to x}\)
- c
- Unifier: \({x \to h(y), z \to b}\)
- Matcher: Unsolvable
- d
- Unifier: Unsolvable
- Matcher: Unsolvable
5.2
Counterexample TRS \(R\):
- \(a \to b\)
- \(b \to b\)
-
-
www.reseau-canope.fr www.reseau-canope.fr
-
En somme, les études sur la communication des élèves atteints d’autisme permettent de mettre en évidence l’importance d’un contexte riche en stimulations appropriées (sons et images), mais également une évidente « stabilité » de l’information à décoder, le suivi des émotions des personnages, le rôle de l’imitation dans les apprentissages. Ces résultats encouragent donc l’usage d’outils informatiques adéquats pour améliorer la communication sociale chez les enfants atteints d’autisme.
L'association de deux sujets qui n'ont pas de corrélation vérifiéé, revient dans la conclusion en contradiction avec la conclusion de l'étude de Ramdoss, S et al.
-
Nous allons montrer par une courte analyse de quelques études l’impact du travail éducatif informatisé dans l’apprentissage de la communication sociale chez des enfants atteints d’autisme.
En contradiction avec l'hypothèse :
Results suggest that CBI should not yet be considered a researched-based approach to teaching communication skills to individuals with ASD. However, CBI does seem a promising practice that warrants future research. Les résultats suggèrent que le CBI ne devrait pas encore être considéré comme un approche fondée sur la recherche pour enseigner les compétences en communication aux personnes ayant Troubles du Spectre Autistique. Cependant, le CBI semble être une pratique prometteuse qui justifie des recherches futures.
Tags
- Ramdoss, S., Lang, R., Mulloy, A., Franco, J., O’Reilly, M., Didden, R., & Lancioni, G. (2010b). Use of Computer-Based Interventions to Teach Communication Skills to Children with Autism Spectrum Disorders : A Systematic Review. Journal of Behavioral Education, 20(1), 55‑76. https://doi.org/10.1007/s10864-010-9112-7
- Ramdoss, S., Lang, R., Mulloy, A., Franco, J., O’Reilly, M., Didden, R., & Lancioni, G. (2010a). Use of Computer-Based Interventions to Teach Communication Skills to Children with Autism Spectrum Disorders : A Systematic Review. Journal of Behavioral Education, 20(1), 55‑76. https://doi.org/10.1007/s10864-010-9112-7
Annotators
URL
-
-
Tags
Annotators
URL
-
- Feb 2022
-
en.wikipedia.org en.wikipedia.org
-
niklas-luhmann-archiv.de niklas-luhmann-archiv.de
-
9/8g Hinter der Zettelkastentechnik steht dieErfahrung: Ohne zu schreiben kann mannicht denken – jedenfalls nicht in anspruchsvollen,selektiven Zugriff aufs Gedächtnis voraussehendenZusammenhängen. Das heißt auch: ohne Differenzen einzukerben,kann man nicht denken.
Google translation:
9/8g The Zettelkasten technique is based on experience: You can't think without writing—at least not in contexts that require selective access to memory.
That also means: you can't think without notching differences.
There's something interesting about the translation here of "notching" occurring on an index card about ideas which can be linked to the early computer science version of edge-notched cards. Could this have been a subtle and tangential reference to just this sort of computing?
The idea isn't new to me, but in the last phrase Luhmann tangentially highlights the value of the zettelkasten for more easily and directly comparing and contrasting the ideas on two different cards which might be either linked or juxtaposed.
Link to:
- Graeber and Wengrow ideas of storytelling
-
Shield of Achilles and ekphrasis thesis
-
https://hypothes.is/a/I-VY-HyfEeyjIC_pm7NF7Q With the further context of the full quote including "with selective access to memory" Luhmann seemed to at least to make space (if not give a tacit nod?) to oral traditions which had methods for access to memories in ways that modern literates don't typically give any credit at all. Johannes F.K .Schmidt certainly didn't and actively erased it in Niklas Luhmann’s Card Index: The Fabrication of Serendipity.
-
-
github.com github.com
Tags
Annotators
URL
-
-
bugs.ruby-lang.org bugs.ruby-lang.org
-
"Context" manipulation is one of big topic and there are many related terminologies (academic, language/implementation specific, promotion terminologies). In fact, there is confusing. In few minutes I remember the following related words and it is good CS exam to describe each :p Thread (Ruby) Green thread (CS terminology) Native thread (CS terminology) Non-preemptive thread (CS terminology) Preemptive thread (CS terminology) Fiber (Ruby/using resume/yield) Fiber (Ruby/using transfer) Fiber (Win32API) Generator (Python/JavaScript) Generator (Ruby) Continuation (CS terminology/Ruby, Scheme, ...) Partial continuation (CS terminology/ functional lang.) Exception handling (many languages) Coroutine (CS terminology/ALGOL) Semi-coroutine (CS terminology) Process (Unix/Ruby) Process (Erlang/Elixir) setjmp/longjmp (C) makecontext/swapcontext (POSIX) Task (...)
-
-
-
To satisfy the architecture of a modern process, a space sepa-rate from the usual library business is furnished, a catalog room or working memory for a central bibliographic unit. In this CBU, the program pro-cesses data contributed by various paths.
Note here how the author creates the acronym CBU out of central bibliographic unit as a means of creating a connection to computer jargon like CPU (central processing unit). I suspect that CBU was not an acronym used at the time.
bacrkonym?
-
-
en.itpedia.nl en.itpedia.nl
-
The different types of software packages
Computer_software controls the physical parts of the machine so that these parts know how to work together. That's where it starts, and there are many types of software in circulation.

-
- Jan 2022
-
psyarxiv.com psyarxiv.com
-
Budak, C., Soroka, S., Singh, L., Bailey, M., Bode, L., Chawla, N., Davis-Kean, P., Choudhury, M. D., Veaux, R. D., Hahn, U., Jensen, B., Ladd, J., Mneimneh, Z., Pasek, J., Raghunathan, T., Ryan, R., Smith, N. A., Stohr, K., & Traugott, M. (2021). Modeling Considerations for Quantitative Social Science Research Using Social Media Data. PsyArXiv. https://doi.org/10.31234/osf.io/3e2ux
-
-
blog.jim-nielsen.com blog.jim-nielsen.com
-
-
Here, the card index func-tions as a ‘thinking machine’,67 and becomes the best communication partner for learned men.68
From a computer science perspective, isn't the index card functioning like an external memory, albeit one with somewhat pre-arranged linked paths? It's the movement through the machine's various paths that is doing the "thinking". Or the user's (active) choices that create the paths creates the impression of thinking.
Perhaps it's the pre-arranged links where the thinking has already happened (based on "work" put into the system) and then traversing the paths gives the appearance of "new" thinking?
How does this relate to other systems which can be thought of as thinking from a complexity perspective? Bacteria perhaps? Groups of cells acting in concert? Groups of people acting in concert? Cells seeing out food using random walks? etc?
From this perspective, how can we break out the constituent parts of thought and thinking? Consciousness? With enough nodes and edges and choices of paths between them (or a "correct" subset of paths) could anything look like thinking or computing?
-
- Dec 2021
-
-
Jacob Leupold, Theatrum machinarum. Theatrum arithmetico-geometricum, Das ist: Schau-Platz der Rechnen- und Meß-Kunst, vol. 7 (Leipzig, 1727)
Reference that discusses calculating machines and information processors.
-
It is telling that during the same period in which Harrison invented his Ark of Studies, the first calculating machines were tested in Europe: the famous cista mathematica by Athanasius Kircher, the or-ganum mathematicum by Kaspar Schott, and the cistula by Gottfried Wilhelm Leibniz.
Keep in mind that Leibniz actually had a version of Harrison's cabinet in his possession. (cf. Paper Machines)
-
Through an inner structure of recursive links and semantic pointers, a card index achieves a proper autonomy; it behaves as a ‘communication partner’ who can recommend unexpected associations among different ideas. I suggest that in this respect pre-adaptive advances took root in early modern Europe, and that this basic requisite for information pro-cessing machines was formulated largely by the keyword ‘order’.
aliases for "topical headings": headwords keywords tags categories
-
In § 3, I explain that to have a life of its own, a card index must be provid-ed with self-referential closure.
In order to become a free-standing tool, the card index needed to have self-referential closure.
This may have been one of the necessary steps for the early ideas behind computers. In addition to the idea of a clockwork universe, the index card may have been a step towards early efforts at creating the modern computer.
-
-
en.wikipedia.org en.wikipedia.org
-
computer engineering, microarchitecture, also called computer organization and sometimes abbreviated as µarch or uarch, is the way a given instruction set architecture (ISA) is implemented in a particular processor.[1] A given ISA may be implemented with different microarchitectures;[2][3] implementations may vary due to different goals of a given design or due to shifts in technology.[4]
Microarchitecture (µarch) What Does Microarchitecture (µarch) Mean? Microarchitecture, abbreviated as µarch or uarch, is the fundamental design of a microprocessor. It includes the technologies used, resources and the methods by which the processor is physically designed in order to execute a specific instruction set (ISA or instruction set architecture). Simply put, it is the logical design of all electronic components and data paths present in the microprocessor, laid out in a specific way that it allows for optimal execution of instructions. In academe this is called computer organization.
Advertisement
Techopedia Explains Microarchitecture (µarch) Microarchitecture is the logical representation of how a microprocessor is designed so that the interconnections between components – the control unit, the arithmetic logic unit, registers and others – interact in an optimized manner. This includes how buses, the data pathways between components, are laid out to dictate the shortest paths and proper connections. In modern microprocessors there are often several layers to deal with complexity. The basic idea is to lay out a circuit that could execute commands and operations that are defined in an instruction set.
A technique that is currently used in microarchitecture is the pipelined datapath. It is a technique that allows a form of parallelism that is applied in data processing by allowing several instructions to overlap in execution. This is done by having multiple execution pipelines that run in parallel or close to parallel.
Execution units are also a crucial aspect of microarchitecture. Execution units perform the operations or calculations of the processor. The choice of the number of execution units, their latency and throughput is a central microarchitectural design consideration. The size, latency, throughput and connectivity of memories within the system are also microarchitectural decisions.
Another part of a microarchitecture is system-level design. This includes decisions on performance such as level and connectivity of input, as well as output and I/O devices.
Microarchitectural design pays closer attention to restrictions than capability. A microarchitecture design decision directly affects what goes into a system; it heeds to issues such as:
Performance Chip area/cost Logic complexity Ease of debugging Testability Ease of connectivity Power consumption Manufacturability A good microarchitecture is one that caters to all of these criteria.
-
-
en.wikipedia.org en.wikipedia.org
-
In general, an ISA defines the supported instructions, data types, registers, the hardware support for managing main memory, fundamental features (such as the memory consistency, addressing modes, virtual memory), and the input/output model of a family of implementations of the ISA.
Instruction Set Architecture defines all logical steps (performed by their corresponding digital logical design hardware) which realizing all computing tasks facilitating our life.
-
- Nov 2021
-
www.amazon.com www.amazon.com
-
What is Amazon Renewed? Amazon Renewed is your trusted destination for a huge selection of smartphones, computers, video games, power tools, and even more products that work and look like new and are backed by the Amazon Renewed Guarantee.
refurbished
-
-
-
Buy Refurbished Computers & More
Computer recycling
-
-
drive.google.com drive.google.com
-
2018wave of ICILS (International Computer and Information Literacy Study)
2018 wave of ICILS (International Computer and Information Literacy Study)
-
-
psyarxiv.com psyarxiv.com
-
Hoffman, R., Mueller, S., Klein, G., & Litman, J. (2021). Measuring Trust in the XAI Context. PsyArXiv. https://doi.org/10.31234/osf.io/e3kv9
-
- Sep 2021
-
www.nngroup.com www.nngroup.com
-
A mental model is what the user believes about the system at hand.
“Mental models are one of the most important concepts in human–computer interaction (HCI).”
— Nielsen Norman Group
-
- Aug 2021
-
www.standard.co.uk www.standard.co.uk
-
Waddell, Lily. “Double-Jabbed May Miss Holidays If NHS Errors Mean Records Don’t Save,” July 21, 2021. https://www.standard.co.uk/news/uk/uk-travel-news-vaccine-passport-holidays-covid-b946848.html.
-
- Jul 2021
-
www.juduo.cc www.juduo.cc
-
中低端3.0顯示卡插到 2.0主機板上 沒什麼問題!PCI-E是一個序列介面標準,分1.0,2.0,3.0每個版本之間的區別只是頻寬不同,也就是速度差異,他們向下相容,也就是3.0相容2.0相容1.0後面的X16的意思是16個通道,因為他是序列匯流排,所以顯示的就是多少倍。現行的有X1 X4 X8 X16比較常見,從效能影響來說,如果你的是PCI-E 2.0 X16的介面那麼頻寬已經足以滿足現在的顯示卡使用了,所以基本沒有效能損失,如果是中低端的顯示卡PCI-E 1.0 X16都不會有任何效能損失。最新的主機板都是PCI-E 3.0的了,但是其實根本用不上,除非發燒級雙核心顯示卡才會用到如此高的頻寬。現在PCI-E 3.0 / 2.0的顯示卡 插到主機板的 PCI-E 3.0 X16 或 PCI-E 2.0 X16插槽上, 基本上看不出有什麼影響,效能影響微乎其微,除了那些最頂級的顯示卡以外。反倒是假如 把顯示卡插入了主機板的 PCI-E 2.0 X4 插槽的話,顯示卡效能會降低20%左右。所以顯示卡是2.0 還是3.0 這個無所謂,關鍵還是主機板是 X16倍速、還是X4倍速。
Tags
Annotators
URL
-
- Jun 2021
-
www.khanacademy.org www.khanacademy.org
-
Running time is asymptotically tight bound. "Asymptotically" because it matters for only large values of nnn. "Tight bound" because we've nailed the running time to within a constant factor above and below.
-
Running time has lower bound and upper bound once the number of computations get large enough.
-
Computation takes time to run. The notation used for running time of computations is Big-Theta.
-
- Apr 2021
-
-
Tollefson, J. (2021, April 16). The race to curb the spread of COVID vaccine disinformation. Nature. https://www.nature.com/articles/d41586-021-00997-x?error=cookies_not_supported&code=0d3302c0-59b3-4065-8835-2a6d99ca35cc
-
-
www.gcu.edu www.gcu.edu
-
Programming is using a language that a machine can understand in order to get it to perform various tasks. Computer programming is how we communicate with machines in a way that makes them function how we need.
-
Earning a computer programming degree can help you innovate and create solutions for a global society.
Can talk about how this applies to other areas/problem-solving/impact on world.
-
-
web.stanford.edu web.stanford.edu
-
OpenCV Android Application Programming with OpenCV Mastering OpenCV with Practical Computer Vision Projects Practical OpenCV Learning OpenCV
sách hay vọc OpenCV trên C++ và Java (Nhúng và di động)
-
- Mar 2021
-
www.mollymielke.com www.mollymielke.com
-
As the Victoria and Albert Museum present in A History of Computer Art,
-
-
arxiv.org arxiv.org
-
Kozlowski, Diego, Jennifer Dusdal, Jun Pang, and Andreas Zilian. ‘Semantic and Relational Spaces in Science of Science: Deep Learning Models for Article Vectorisation’. ArXiv:2011.02887 [Physics], 5 November 2020. http://arxiv.org/abs/2011.02887.
-
-
en.wikipedia.org en.wikipedia.org
-
Some believe that computing and internetworking concepts and skills underlie virtually every important aspect of LIS, indeed see LIS as a sub-field of computer science!
-
- Feb 2021
-
en.wikipedia.org en.wikipedia.org
-
hilton.org.uk hilton.org.uk
-
violates our expectation that hard things should be technical
-
-
www.quora.com www.quora.com
-
So the hard and unsolvable problem becomes: how up-to-date do you really need to be?
-
After considering the value we place, and the tradeoffs we make, when it comes to knowing anything of significance, I think it becomes much easier to understand why cache invalidation is one of the hard problems in computer science
the crux of the problem is: trade-offs
-
the 2 hardest problems in computer science are essentially the 2 hardest problems of life in general, as far as humans and information are concerned.
-
The non-determinism is why cache invalidation — and that other hard problem, naming things — are uniquely and intractably hard problems in computer science. Computers can perfectly solve deterministic problems. But they can’t predict when to invalidate a cache because, ultimately, we, the humans who design and build computational processes, can’t agree on when a cache needs to be invalidated.
-
Sometimes humorously extended as “cache invalidation, naming things, and off-by-one errors.”
Tags
- where it shines / best application
- good analogy
- cache invalidation is hard
- good point
- main/key/central/essential/core thing/point/problem/meat
- computers
- nondeterministic
- good question
- generalized explanation
- trade-offs
- how good/perfect does it really need to be?
- knowledge
- hard things in computer science
- difficult/hard problem
- funny
- good explanation
- deterministic
- life in general
Annotators
URL
-
-
www.computers.wtf www.computers.wtf
-
There’s only one hard thing in Computer Science: human communication. The most complex part of cache invalidation is figuring out what the heck people mean with the word cache. Once you get that sorted out, the rest is not that complicated; the tools are out there, and they’re pretty good.
-
- Jan 2021
-
hypothes.is hypothes.is
-
I came across this article about the tension between computer drawing and hand drawing in architecture when I replied to an annotation by another user @onion - very interesting read and I would be curious to see this issue revisited in another ten years...how may opinions have changed?
-
- Sep 2020
-
macwright.com macwright.com
-
There was a time when we could install applications, give some sort of explicit agreement that something would run on our computers and use our hardware. That time is ending,
The end seems perilously close at hand for personal computing, but, imo, as much as anything that is because users now expect to compute to have impact & effect far beyond the beige box.
Open source has many amazing things, but in terms of ways to get user's digital stuff online & available & circulating, there have been precious few compelling attempts. I'd call out in particular RemoteStorage spec, & the newer SOLID specs from MIT & TBL.
-
-
www.scientificamerican.com www.scientificamerican.com
-
448-page preprint paper
how can he expect people to read that with scrutiny?
-
-
psyarxiv.com psyarxiv.com
-
Yang, Scott Cheng-Hsin, Chirag Rank, Jake Alden Whritner, Olfa Nasraoui, and Patrick Shafto. ‘Unifying Recommendation and Active Learning for Information Filtering and Recommender Systems’. Preprint. PsyArXiv, 25 August 2020. https://doi.org/10.31234/osf.io/jqa83.
Tags
- exploration-exploitation tradeoff
- experimental approach
- parameterized model
- AI
- is:preprint
- lang:en
- recommender system
- recommendation accuracy
- machine learning
- predictive accuracy
- algorithms
- computer science
- cognitive science
- active learning
- Internet
- artificial intelligence
- information filtering
Annotators
URL
-
- Jun 2020
-
arstechnica.com arstechnica.com
-
Plenty of journalists, attorneys, and activists are equally if not more threatened by so-called evil maid attacks, in which a housekeeper or other stranger has the ability to tamper with firmware during brief physical access to a computer.
-
-
-
Jazayeri, A., & Yang, C. C. (2020). Motif Discovery Algorithms in Static and Temporal Networks: A Survey. ArXiv:2005.09721 [Physics]. http://arxiv.org/abs/2005.09721
-
- May 2020
-
arxiv.org arxiv.org
-
Katz, D. M., Coupette, C., Beckedorf, J., & Hartung, D. (2020). Complex Societies and the Growth of the Law. ArXiv:2005.07646 [Physics]. http://arxiv.org/abs/2005.07646
-
-
boardgamegeek.com boardgamegeek.com
-
www.annualreviews.org www.annualreviews.org
-
Edelmann, A., Wolff, T., Montagne, D., & Bail, C. A. (2020). Computational Social Science and Sociology. Annual Review of Sociology, 46(1), annurev-soc-121919-054621. https://doi.org/10.1146/annurev-soc-121919-054621
-
-
-
What's terrible and dangerous is a faceless organization deciding to arbitrarily and silently control what I can and can not do with my browser on my computer. Orwell is screaming in his grave right now. This is no different than Mozilla deciding I don't get to visit Tulsi Gabbard's webpage because they don't like her politics, or I don't get to order car parts off amazon because they don't like hyundai, or I don't get to download mods for minecraft, or talk to certain people on facebook.
-
They don't have to host the extension on their website, but it's absolutely and utterly unacceptable for them to interfere with me choosing to come to github and install it.
-
I appreciate the vigilance, but it would be even better to actually publish a technical reasoning for why do you folks believe Firefox is above the device owner, and the root user, and why there should be no possibility through any means and configuration protections to enable users to run their own code in the release version of Firefox.
Tags
- software freedom
- digital rights
- censorship
- Orwellian
- empowering individual users
- the owner of a device/computer should have freedom to use it however they wish
- bypassing technical constraints
- good point
- empowering people
- allowing security constraints to be bypassed by users
- balance of power
Annotators
URL
-
-
-
Wahn, B., & Kingstone, A. (2020, April 30). Sharing task load with artificial – yet human-like – co-actors. https://doi.org/10.31234/osf.io/2am8y
-
- Apr 2020
-
docs.google.com docs.google.com
-
www.ebay.com www.ebay.com
-
www.ardanlabs.com www.ardanlabs.com
-
If the word “share” doesn’t come out of your mouth, you don’t need to use a pointer
key point
-
The benefit of passing data “by value” is readability. The value you see in the function call is what is copied and received on the other side
no hidden cost, eg., memory growth on the heap or pauses during garbage collection. but there is a cost in stack memory usage and "scoping" among multiple stack frames, CPU caching, etc.
-
Functions execute within the scope of frame boundaries that provide an individual memory space for each respective function. Each frame allows a function to operate within their own context and also provides flow control. A function has direct access to the memory inside its frame, through the frame pointer, but access to memory outside its frame requires indirect access. For a function to access memory outside of its frame, that memory must be shared with the function.
eg., shared via the "pointer" to an address in heap memory
-
- Feb 2020
-
journals.sagepub.com journals.sagepub.com
-
Discourses tend to be intertextual and interdiscursive (Reisigl and Wodak, 2001: 39). They interlink various texts, discourses and contexts. Social media data are therefore not independent from other media but tend to be multimodal and connected with texts in traditional media. An example is that many political tweets tend to link to articles in the online versions of mainstream newspapers. Studying social media therefore does not substitute the study of other media but often requires studying various media’s intercon-nection. Discourses are texts that stand in particular societal, political-economic, histori-cal, cultural contexts. Understanding them requires taking a holistic point of view, that is, to situate them in history and society.
-
- Jan 2020
-
en.wikipedia.org en.wikipedia.org
-
The plural for the small rodent is always "mice" in modern usage. The plural of a computer mouse is either "mouses" or "mice" according to most dictionaries, with "mice" being more common.[4] The first recorded plural usage is "mice"; the online Oxford Dictionaries cites a 1984 use, and earlier uses include J. C. R. Licklider's "The Computer as a Communication Device" of 1968.[5] The term computer mouses may be used informally in some cases. Although the plural of a mouse (small rodent) is mice, the two words have undergone a differentiation through usage.
-
plural mice
Tags
Annotators
URL
-
- Dec 2019
-
www.amazon.com www.amazon.com
- Nov 2019
-
trackmenot.io trackmenot.io
-
TrackMeNot is user-installed and user-managed, residing wholly on users' system and functions without the need for 3rd-party servers or services. Placing users in full control is an essential feature of TrackMeNot, whose purpose is to protect against the unilateral policies set by search companies in their handling of our personal information.
Tags
Annotators
URL
-
-
www.csplacement.com www.csplacement.com
-
Computer literacy is considered a very important skill to possess. Employers want their workers to have basic computer skills because their company becomes ever more dependent on computers
Learning the basic about computers is essential to employers.
-
-
elearningindustry.com elearningindustry.com
-
Author Mary Burns discusses the key elements of computer adaptive testing (CAT). CAT is defined as assessments that use algorithms to progressively adjust test difficulty based upon learner's correct or incorrect responses. The benefits of CAT include more immediate data and are often more reliable. Types of test items are also covered to illustrate how the test can meet various levels of cognition and measure expertise. An issue related to CAT is the intensive time needed to develop multiple test items at multiple levels of cognition. Rating: 8/10
-
- Oct 2019
-
www.lifewire.com www.lifewire.com
-
Best Overall: SanDisk Extreme PRO 128 GB Drive 3.5 Buy on Amazon The SanDisk PRO gives you blistering speeds, offering 420 MB/s on the reading front and 380 MB/s on the writing end, which is 3–4x faster than what a standard USB 3.0 drive will offer. The sleek, aluminum casing is both super durable and very eye-catching, so you can bring it with you to your business meetings and look professional as well. The onboard AES, 128-bit file encryption gives you top-of-the-line security for your sensitive files.
-
-
www.quora.com www.quora.com
- Jun 2019
-
-
EthereumEthereum is a distributed computer; each node in the network executes some bytecode (hint: Smart Contracts), and then stores the resulting state in a blockchain. Due to the properties of the blockchain representing application state, this results in “applications that run exactly as programmed without any possibility of downtime, censorship, fraud or third party interference”.
This is a decent little explanation for how smart contracts execute on blockchains. Author missed in "Due to the properties of the blockchain" to say that all nodes must also come to consensus about how the code was executed and therefore "applications that run exactly...". We will later discuss deterministic code execution in relation to this
-
- May 2019
-
www.gowitek.com www.gowitek.com
-
Go Programming Language publicly in 2009 they were also looking to solve certain challenges of the existing Computer languages. Of the many features that it demonstrated (we will get to those soon enough) it was also helpful in addressing the strange dilemma of hardware and software that was emerging.
Golang is a modern computing language, designed especially for modern computing needs.
-
-
intelligence.org intelligence.org
-
The first difficulty is that the robot’s utility function did not quite match our utility function. Our utility function is 1 if the cauldron is full, 0 if the cauldron is empty, −10 points to whatever the outcome was if the workshop has flooded, +0.2 points if it’s funny, −1,000 points (probably a bit more than that on this scale) if someone gets killed … and it just goes on and on and on.
But it is very difficult to fully express these utility functions in code. The goal is to literally turn our ethics into code -- to translate them into coherent data structures, algorithms, and decision trees. We want to deduce our moral intuitions and more.
-
- Jan 2019
-
urbigenous.net urbigenous.net
-
Automatic Sequence Computer
The Harvard Mark 1 was an ASCC or an Automated Sequence Controlled Calculator(https://en.wikipedia.org/wiki/Harvard_Mark_I) - so Clarke was using this term for what was possibly the most powerful computer during his time. Our smartphones now are more powerful than several of these ASCCs
-
-
dl.acm.org dl.acm.org
-
Reflective Design Strategies In addition shaping our principles or objectives, our foundational influences and case studies have also helped us articulate strategies for reflective design. The first three strategies identified here speak to characteristics of designs that encourage reflection by users. The second group of strategies provides ways for reflecting on the process of design.
verbatim from subheads in this section
1.Provide for interpretive flexibility.
2.Give users license to participate.
3.Provide dynamic feedback to users.
4.Inspire rich feedback from users.
5.Build technology as a probe.
6.Invert metaphors and cross boundaries.
-
Some Reflective Design Challenges
The reflective design strategies offer potential design interventions but lack advice on how to evaluate them against each other.
"Designing for appropriation requires recognizing that users already interact with technology not just on a superficial, task-centered level, but with an awareness of the larger social and cultural embeddedness of the activity."
-
Principles of Reflective Design
verbatim from subheads in this section
Designers should use reflection to uncover and alter the limitations of design practice
Designers should use reflection to re-understand their own role in the technology design process.
Designers should support users in reflecting on their lives.
Technology should support skepticism about and reinterpretation of its own working.
Reflection is not a separate activity from action but is folded into it as an integral part of experience
Dialogic engagement between designers and users through technology can enhance reflection.
-
Reflective design, like reflection-in-action, advocates practicing research and design concomitantly, and not only as separate disciplines. We also subscribe to a view of reflection as a fully engaged interaction and not a detached assessment. Finally, we draw from the observation that reflection is often triggered by an element of surprise, where someone moves from knowing-in-action, operating within the status quo, to reflection-in-action, puzzling out what to do next or why the status quo has been disrupted
Influences from reflection-in-action for reflective design values/methods.
-
In this effort, reflection-in-action provides a ground for uniting theory and practice; whereas theory presents a view of the world in general principles and abstract problem spaces, practice involves both building within these generalities and breaking them down.
A more improvisational, intuitive and visceral process of rethinking/challenging the initial design frame.
Popular with HCI and CSCW designers
-
CTP is a key method for reflective design, since it offers strategies to bring unconscious values to the fore by creating technical alternatives. In our work, we extend CTP in several ways that make it particularly appropriate for HCI and critical computing.
Ways in which Senger, et al., describe how to extend CTP for HCI needs:
• incorporate both designer/user reflection on technology use and its design
• integrate reflection into design even when there is no specific "technical impasse" or metaphor breakdown
• driven by critical concerns, not simply technical problems
-
CTP synthesizes critical reflection with technology production as a way of highlighting and altering unconsciously-held assumptions that are hindering progress in a technical field.
Definition of critical technical practice.
This approach is grounded in AI rather than HCI
(verbatim from the paper) "CTP consists of the following moves:
• identifying the core metaphors of the field
• noticing what, when working with those metaphors, remains marginalized
• inverting the dominant metaphors to bring that margin to the center
• embodying the alternative as a new technology
-
Ludic design promotes engagement in the exploration and production of meaning, providing for curiosity, exploration and reflection as key values. In other words, ludic design focuses on reflection and engagement through the experience of using the designed object.
Definition of ludic design.
Offers a more playful approach than critical design.
-
goal is to push design research beyond an agenda of reinforcing values of consumer culture and to instead embody cultural critique in designed artifacts. A critical designer designs objects not to do what users want and value, but to introduce both designers and users to new ways of looking at the world and the role that designed objects can play for them in it.
Definition of critical design.
This approach tends to be more art-based and intentionally provocative than a practical design method to inculcate a certain sensibility into the technology design process.
-
value-sensitive design method (VSD). VSD provides techniques to elucidate and answer values questions during the course of a system's design.
Definition of value-sensitive design.
(verbatim from the paper)
*"VSD employs three methods :
• conceptual investigations drawing on moral philosophy, which identify stakeholders, fundamental values, and trade-offs among values pertinent to the design
• empirical investigations using social-science methods to uncover how stakeholders think about and act with respect to the values involved in the system
• technical investigations which explore the links between specific technical decisions and the values and practices they aid and hinder" *
-
From participatory design, we draw several core principles, most notably the reflexive recognition of the politics of design practice and a desire to speak to the needs of multiple constituencies in the design process.
Description of participatory design which has a more political angle than user-centered design, with which it is often equated in HCI
-
PD strategies tend to be used to support existing practices identified collaboratively by users and designers as a design-worthy project. While values clashes between designers and different users can be elucidated in this collaboration, the values which users and designers share do not necessarily go examined. For reflective design to function as a design practice that opens new cultural possibilities, however, we need to question values which we may unconsciously hold in common. In addition, designers may need to introduce values issues which initially do not interest users or make them uncomfortabl
Differences between participatory design practices and reflective design
-
We define 'reflection' as referring tocritical reflection, orbringing unconscious aspects of experience to conscious awareness, thereby making them available for conscious choice. This critical reflection is crucial to both individual freedom and our quality of life in society as a whole, since without it, we unthinkingly adopt attitudes, practices, values, and identities we might not consciously espouse. Additionally, reflection is not a purely cognitive activity, but is folded into all our ways of seeing and experiencing the world.
Definition of critical reflection
-
Our perspective on reflection is grounded in critical theory, a Western tradition of critical reflection embodied in various intellectual strands including Marxism, feminism, racial and ethnic studies, media studies and psychoanalysis.
Definition of critical theory
-
ritical theory argues that our everyday values, practices, perspectives, and sense of agency and self are strongly shaped by forces and agendas of which we are normally unaware, such as the politics of race, gender, and economics. Critical reflection provides a means to gain some awareness of such forces as a first step toward possible change.
Critical theory in practice
-
We believe that, for those concerned about the social implications of the technologies we build, reflection itself should be a core technology design outcome for HCI. That is to say, technology design practices should support both designers and users in ongoing critical reflection about technology and its relationship to human life.
Critical reflection can/should support designers and users.
-
- Dec 2018
-
inst-fs-iad-prod.inscloudgate.net inst-fs-iad-prod.inscloudgate.net
-
Outliers : All data sets have an expected range of values, and any actual data set also has outliers that fall below or above the expected range. (Space precludes a detailed discussion of how to handle outliers for statistical analysis purposes, see: Barnett & Lewis, 1994 for details.) How to clean outliers strongly depends on the goals of the analysis and the nature of the data.
Outliers can be signals of unanticipated range of behavior or of errors.
-
Understanding the structure of the data : In order to clean log data properly, the researcher must understand the meaning of each record, its associated fi elds, and the interpretation of values. Contextual information about the system that produced the log should be associated with the fi le directly (e.g., “Logging system 3.2.33.2 recorded this fi le on 12-3-2012”) so that if necessary the specifi c code that gener-ated the log can be examined to answer questions about the meaning of the record before executing cleaning operations. The potential misinterpretations take many forms, which we illustrate with encoding of missing data and capped data values.
Context of the data collection and how it is structured is also a critical need.
Example, coding missing info as "0" risks misinterpretation rather than coding it as NIL, NDN or something distinguishable from other data
-
Data transformations : The goal of data-cleaning is to preserve the meaning with respect to an intended analysis. A concomitant lesson is that the data-cleaner must track all transformations performed on the data .
Changes to data during clean up should be annotated.
Incorporate meta data about the "chain of change" to accompany the written memo
-
Data Cleaning A basic axiom of log analysis is that the raw data cannot be assumed to correctly and completely represent the data being recorded. Validation is really the point of data cleaning: to understand any errors that might have entered into the data and to transform the data in a way that preserves the meaning while removing noise. Although we discuss web log cleaning in this section, it is important to note that these principles apply more broadly to all kinds of log analysis; small datasets often have similar cleaning issues as massive collections. In this section, we discuss the issues and how they can be addressed. How can logs possibly go wrong ? Logs suffer from a variety of data errors and distortions. The common sources of errors we have seen in practice include:
Common sources of errors:
• Missing events
• Dropped data
• Misplaced semantics (encoding log events differently)
-
In addition, real world events, such as the death of a major sports fi gure or a political event can often cause people to interact with a site differently. Again, be vigilant in sanity checking (e.g., look for an unusual number of visitors) and exclude data until things are back to normal.
Important consideration for temporal event RQs in refugee study -- whether external events influence use of natural disaster metaphors.
-
Recording accurate and consistent time is often a challenge. Web log fi les record many different timestamps during a search interaction: the time the query was sent from the client, the time it was received by the server, the time results were returned from the server, and the time results were received on the client. Server data is more robust but includes unknown network latencies. In both cases the researcher needs to normalize times and synchronize times across multiple machines. It is common to divide the log data up into “days,” but what counts as a day? Is it all the data from midnight to midnight at some common time reference point or is it all the data from midnight to midnight in the user’s local time zone? Is it important to know if people behave differently in the morning than in the evening? Then local time is important. Is it important to know everything that is happening at a given time? Then all the records should be converted to a common time zone.
Challenges of using time-based log data are similar to difficulties in the SBTF time study using Slack transcripts, social media, and Google Sheets
-
Log Studies collect the most natural observations of people as they use systems in whatever ways they typically do, uninfl uenced by experimenters or observers. As the amount of log data that can be collected increases, log studies include many different kinds of people, from all over the world, doing many different kinds of tasks. However, because of the way log data is gathered, much less is known about the people being observed, their intentions or goals, or the contexts in which the observed behaviors occur. Observational log studies allow researchers to form an abstract picture of behavior with an existing system, whereas experimental log stud-ies enable comparisons of two or more systems.
Benefits of log studies:
• Complement other types of lab/field studies
• Provide a portrait of uncensored behavior
• Easy to capture at scale
Disadvantages of log studies:
• Lack of demographic data
• Non-random sampling bias
• Provide info on what people are doing but not their "motivations, success or satisfaction"
• Can lack needed context (software version, what is displayed on screen, etc.)
Ways to mitigate: Collecting, Cleaning and Using Log Data section
-
Two common ways to partition log data are by time and by user. Partitioning by time is interesting because log data often contains signifi cant temporal features, such as periodicities (including consistent daily, weekly, and yearly patterns) and spikes in behavior during important events. It is often possible to get an up-to-the- minute picture of how people are behaving with a system from log data by compar-ing past and current behavior.
Bookmarked for time reference.
Mentions challenges of accounting for time zones in log data.
-
An important characteristic of log data is that it captures actual user behavior and not recalled behaviors or subjective impressions of interactions.
Logs can be captured on client-side (operating systems, applications, or special purpose logging software/hardware) or on server-side (web search engines or e-commerce)
-
Table 1 Different types of user data in HCI research
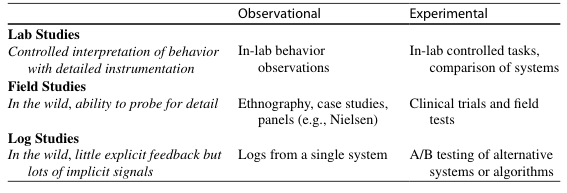
-
Large-scale log data has enabled HCI researchers to observe how information diffuses through social networks in near real-time during crisis situations (Starbird & Palen, 2010 ), characterize how people revisit web pages over time (Adar, Teevan, & Dumais, 2008 ), and compare how different interfaces for supporting email organi-zation infl uence initial uptake and sustained use (Dumais, Cutrell, Cadiz, Jancke, Sarin, & Robbins, 2003 ; Rodden & Leggett, 2010 ).
Wide variety of uses of log data
-
Behavioral logs are traces of human behavior seen through the lenses of sensors that capture and record user activity.
Definition of log data
-
-
wendynorris.com wendynorris.com
-
The distinct sorts of questions asked of science and design manifest the different kinds of accountability that apply to each - that is, the expectations of what activities must be defended and how, and by extension the ways narratives (accounts) are legitimately formed about each endeavour.science is defined by epistemological accountability, in which the essential requirement is to be able to explain and defend the basis of one’s claimed knowledge. Design, in contrast, works with aesthetic accountability, where ‘aesthetic’ refers to how satisfactory the composition of multiple design features are (as opposed to how ‘beautiful’ it might be). The requirement here is to be able to explain and defend – or, more typically, to demonstrate –that one’s design works.
Scientific accountability >> epistemological
Design accountability >> aesthetic
-
The issue of whether something ‘works’ goes beyond questions of technical or practical efficacy to address a host of social, cultural, aesthetic and ethical concerns.
Intent is the critical factor for design work, not its function.
-
To be sure, the topicality, novelty or potential benefits of a given line of research might help it attract notice and support, butscientific researchfundamentally stands or falls on the thoroughness with which activities and reasoning can be tied together. You just can’t get in the game without a solid methodology.
Methodology is the critical factor for scientific study, not the result.
-
-
www.creativitypost.com www.creativitypost.com
-
as societies become wealthier and more gender equal
are these two really related?
-
- Nov 2018
-
www.technologyreview.com www.technologyreview.com
-
The vast majority of machine-learning applications rely on supervised learning.
So then we know that most people will use supervised learning that requires less computational power and knowledge.
-
-
www.c3schools.org www.c3schools.org
-
English Teachers' Barriers to the Use of Computer-assisted Language Learning
This article discusses the use of Computer-assisted Language Learning (CALL) technologies to teach English. Each stage of learning aligns with a level of computer technology. There are also many barriers that impede the process of integrating the CALL into the classroom, which include financial, access to hardware and software, teacher training, technical knowledge, and acceptance of technology.
RATING: 8/10
-
-
files.eric.ed.gov files.eric.ed.gov
-
IMPACTS OF LEARNING STYLES AND COMPUTER SKILLS ON ADULT STUDENTS’ LEARNING ONLINE
This article explores how learning styles and computer skills impact student online learning. Further consideration is also given to course format and participants who were first time online learners. This is a complex study that investigates possible skills and abilities of first time online students. It would be interesting to conduct the same study, ten years latter to see if the changes in technology has improved the learners' computer skills and therefore the results of the study.
RATING: 7/10
-
- Oct 2018
-
mfeldstein.com mfeldstein.com
-
As a recap, Chegg discovered on September 19th a data breach dating back to April that "an unauthorized party" accessed a data base with access to "a Chegg user’s name, email address, shipping address, Chegg username, and hashed Chegg password" but no financial information or social security numbers. The company has not disclosed, or is unsure of, how many of the 40 million users had their personal information stolen.
-
-
towardsdatascience.com towardsdatascience.com
-
R-CNN, Fast R-CNN, Faster R-CNN, YOLO — Object Detection Algorithms
-
-
reallifemag.com reallifemag.com
-
Questions about the inclusivity of engineering and computer science departments have been going on for quite some time. Several current “innovations” coming out of these fields, many rooted in facial recognition, are indicative of how scientific racism has long been embedded in apparently neutral attempts to measure people — a “new” spin on age-old notions of phrenology and biological determinism, updated with digital capabilities.
-
- Sep 2018
-
www.mnemotext.com www.mnemotext.com
-
And its very likely that IA is a much easier road to the achievement of superhumanity than pure AI. In humans, the hardest development problems have already been solved. Building up from within ourselves ought to be easier than figuring out what we really are and then building machines that are all of that.
The authors of the text are proposing a radically different approach to the inevitable "singularity" event. They propose the research and development IA, or Intelligence Amplification, is developing computers with a symbiosis with humans. Noting that IA could be easier to develop than AI algorithms, since humanity had to probe what their true weaknesses and strengths are. In turn, developing an IA system that could cover humanities' weaknesses. This would summarily prevent an IA algorithm from getting over itself, which could potentially slow a point when we reach singularity.
-
- Aug 2018
-
-
Earlier communication tools enabled individuals to create a private list ofcontacts (for instance a buddy list on instant messaging), to establish a group of contactsthat were shared by others (such as a listserv membership list), or to publish a list ofrelated links (such as a blogroll), but SNSs extended the practice of creating a publiclyvisible, personally curated list of contacts and made it a mainstream practice.
Differences between SNS and CMC.
-
- Jun 2018
-
avisingh599.github.io avisingh599.github.io
-
Remember, the author made a more technical report on this topic. PDF here
-
if we ever find the translation is dominant in a direction other than forward, we simply ignore that motion.
Remember, this is just a heuristic
-
Most Computer Vision algorithms are not complete without a few heuristics thrown in
-
RANSAC. It is an iterative algorithm. At every iteration, it randomly samples five points from out set of correspondences, estimates the Essential Matrix, and then checks if the other points are inliers when using this essential matrix.
-
T his step compensates for this lens distortion.
-
For every pair of images, we need to find the rotation matrix RRR and the translation vector ttt, which describes the motion of the vehicle between the two frames.
-